Recommended Policy and Rule Settings
We recommend the following policy settings:
-
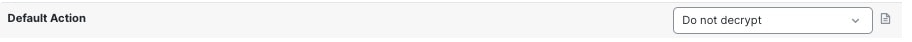
SSL policy:
-
Default action Do Not Decrypt.
-
Enable logging.
-
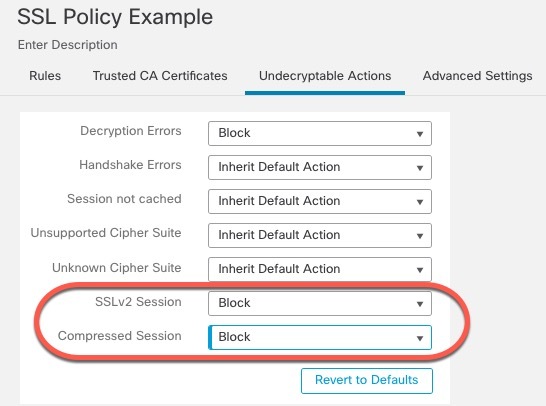
Set Undecryptable Actions to Block for both SSL v2 Session and Compressed Session.
-
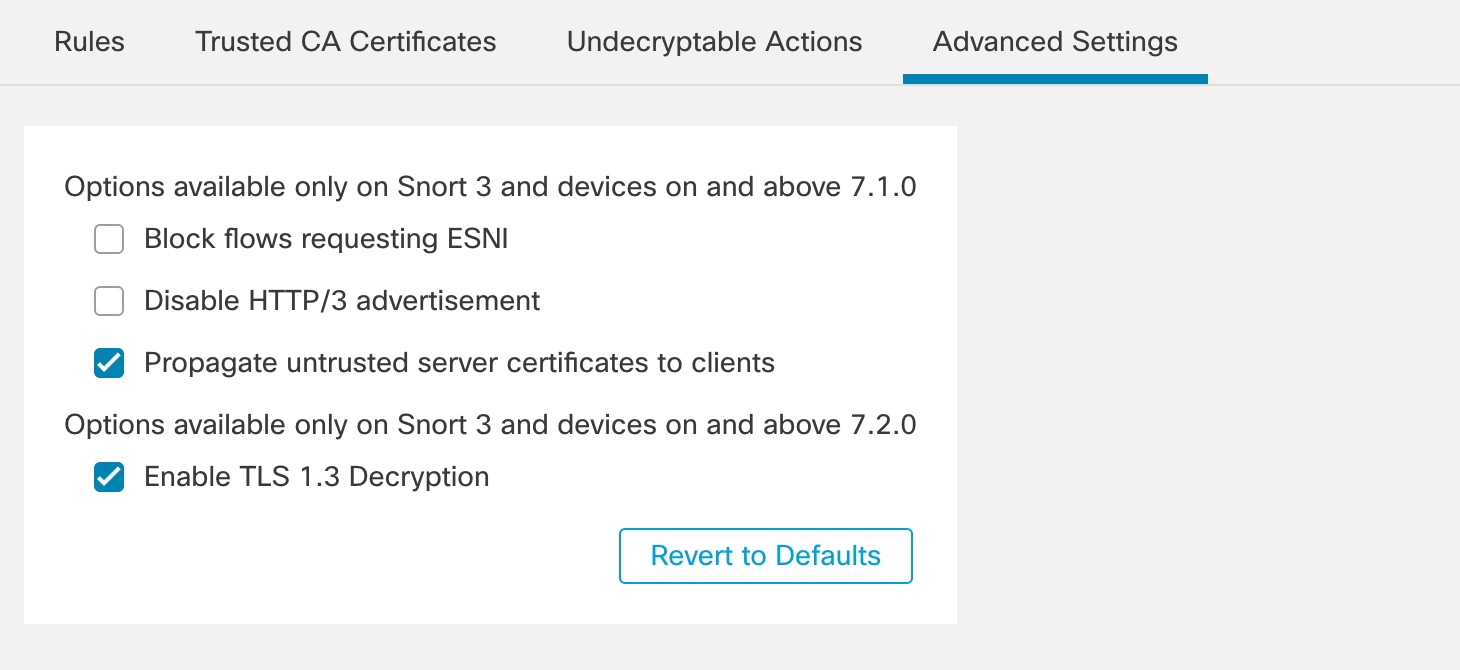
Enable TLS 1.3 decryption in the policy's advanced settings.
-
-
TLS/SSL rule: Enable logging for every rule except those with a Do Not Decrypt rule action. (It's up to you; if you want to see information about traffic that isn't decrypted, enable logging for those rules also.)
-
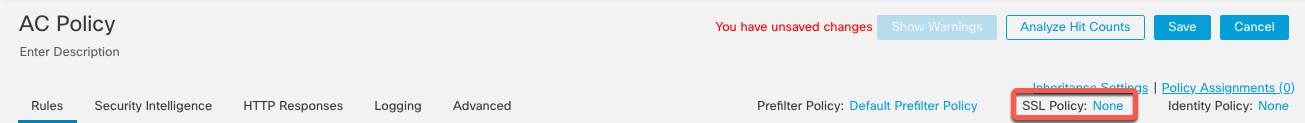
Access control policy:
-
Associate your SSL policy with an access control policy. (If you fail to do this, your SSL policy and rules have no effect.)
-
Set the default policy action to Intrusion Prevention: Balanced Security and Connectivity.
-
Enable logging.
-
 )
)
 )
)


 )
) Feedback
Feedback