About User Identity Sources
The following table provides a brief overview of the user identity sources supported by the Firepower System. Each identity source provides a store of users for user awareness. These users can then be controlled with identity and access control policies.
|
User Identity Source |
Policy |
Server Requirements |
Type |
Authentication Type |
User Awareness? |
User Control? |
For more information, see... |
|---|---|---|---|---|---|---|---|
|
User Agent |
Identity |
Microsoft Active Directory |
Authoritative logins |
Passive |
Yes |
Yes |
|
|
ISE/ISE-PIC |
Identity |
Microsoft Active Directory |
Authoritative logins |
Passive |
Yes |
Yes |
|
|
TS Agent |
Identity |
Microsoft Windows Terminal Server |
Authoritative logins |
Passive |
Yes |
Yes |
|
|
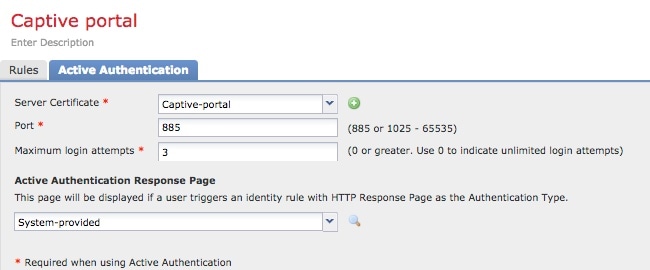
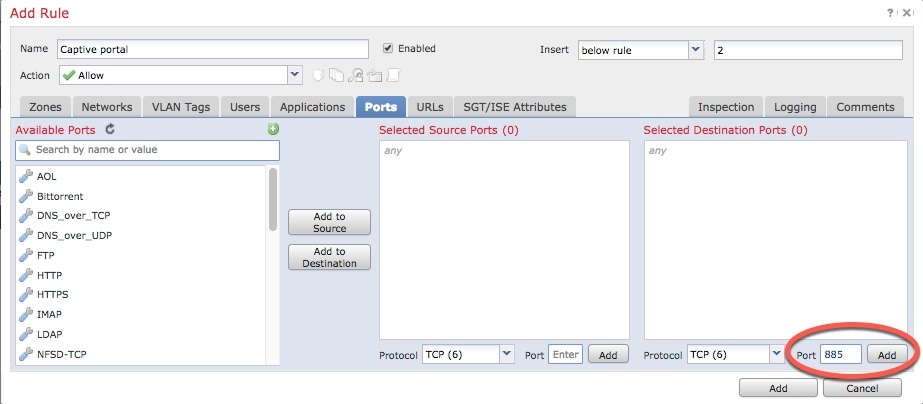
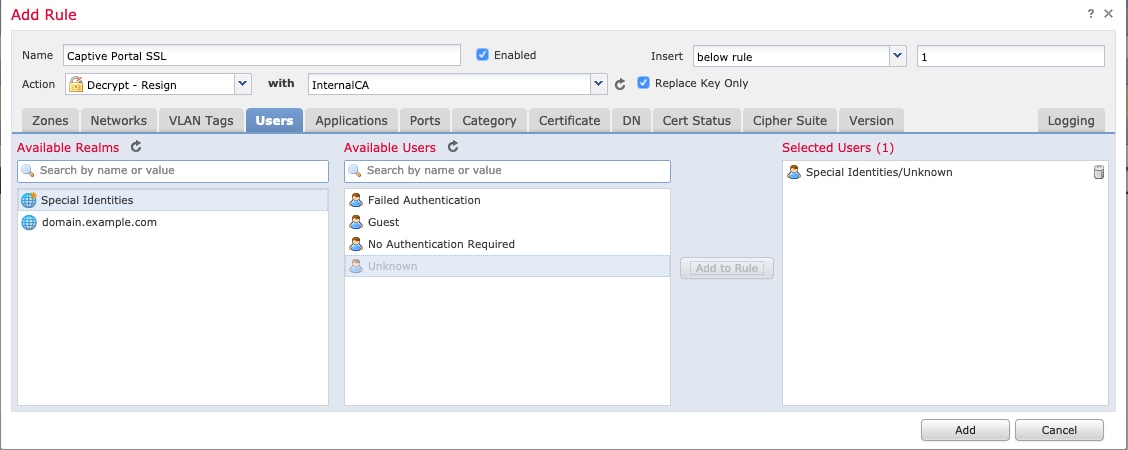
Captive portal |
Identity |
Microsoft Active Directory |
Authoritative logins |
Active |
Yes |
Yes |
|
| Remote Access VPN | Identity | OpenLDAP or Microsoft Active Directory |
Authoritative logins |
Active |
Yes |
Yes |
|
|
Identity |
RADIUS |
Authoritative logins |
Active |
Yes |
No |
||
|
Traffic-based detection |
Network discovery |
n/a |
Non-authoritative logins |
n/a |
Yes |
No |
Consider the following when selecting identity sources to deploy:
-
You must use traffic-based detection for non-LDAP user logins. For example, if you are using only user agents to detect user activity, restricting non-LDAP logins has no effect.
-
You must use traffic-based detection or captive portal to record failed login or authentication activity. A failed login or authentication attempt does not add a new user to the list of users in the database.
-
The captive portal identity source requires a managed device with a routed interface. You cannot use an inline (also referred to as tap mode) interface with captive portal.
Data from those identity sources is stored in the Firepower Management Center's users database and the user activity database. You can configure Firepower Management Center-server user downloads to automatically and regularly download new user data to your databases.
After you configure identity rules using the desired identity source, you must associate each rule with an access control policy and deploy the policy to managed devices for the policy to have any effect. For more information about access control policies and deployment, see User, Realm, and ISE Attribute Conditions (User Control).
For general information about user identity in the Firepower System, see About User Identity.
Video icon YouTube videos for configuring identity sources.


 )
) )
)
 )
)
 )
) )
) )
) Feedback
Feedback