Preparing FND for IXM ZTD
Follow these steps to prepare FND for IXM ZTD:
Procedure
|
Step 1 |
If you are using PSK authentication for tunneloing, add the userPropertyTypes.xml file to the FND server under /opt/cgms/server/cgms/conf. Restart the FND service after adding the following. If you are using RSA, ignore this step. 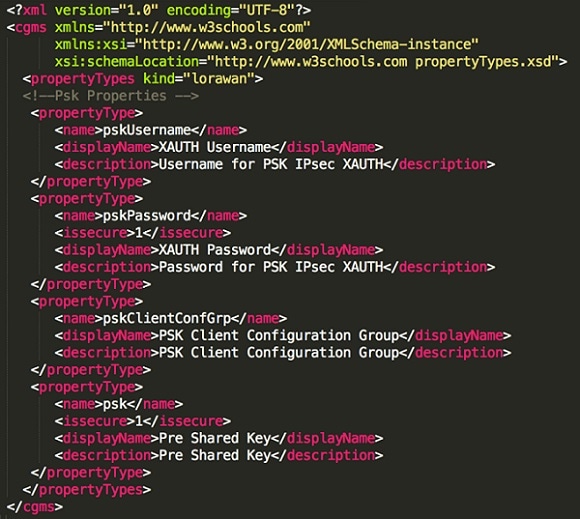 |
|
Step 2 |
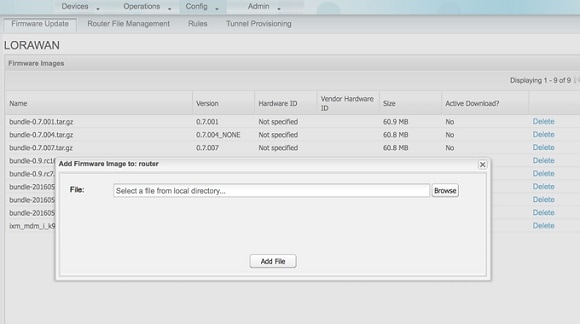
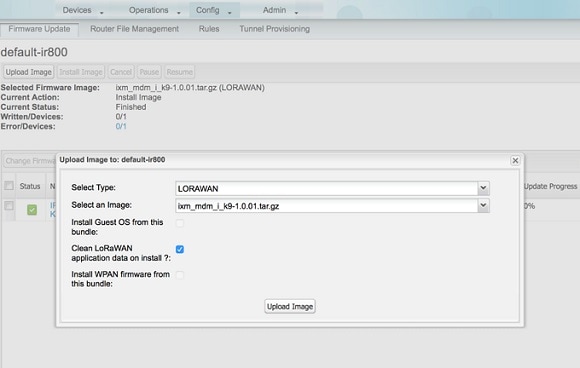
Add the Actility LRR and public key to FND by clicking the import button on the File Management page. 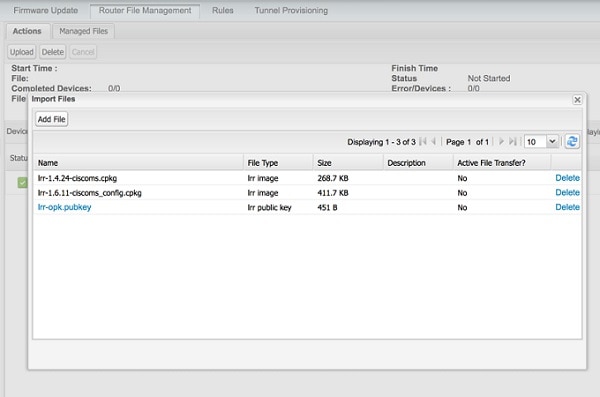 |
|
Step 3 |
Update the Tunnel Configuration group with the following parameters and save the changes. The following figure shows an example for PSK. 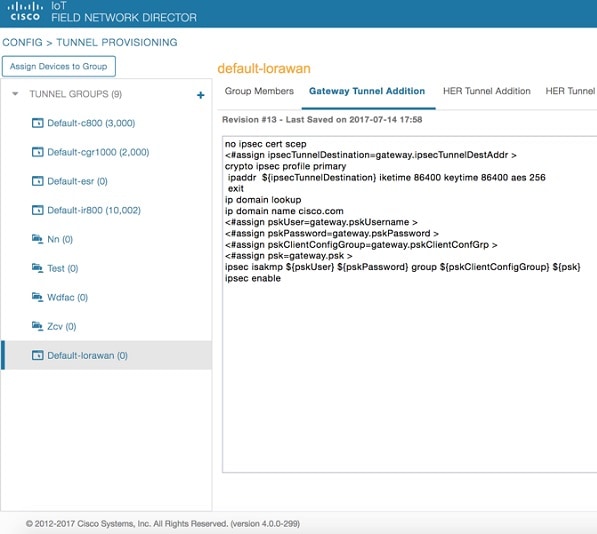 |
|
Step 4 |
Update the Device Configuration group with the following parameters and save the changes. The following figure shows a sample configuration. 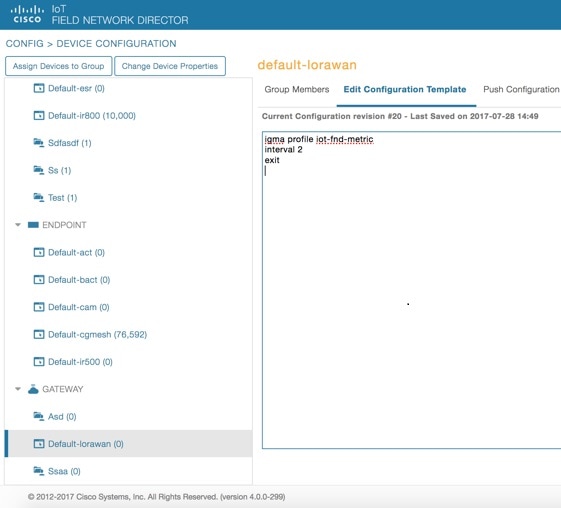 Update the Device Configuration Group properties with the following parameters and save the changes. 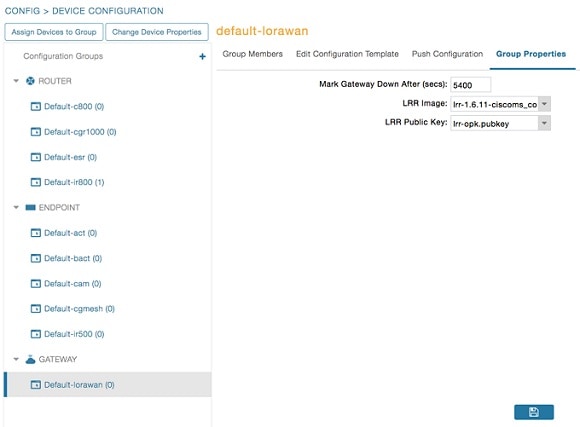 The Tunnel Provisioning settings page will have the FND common name populated as the following figure shows. 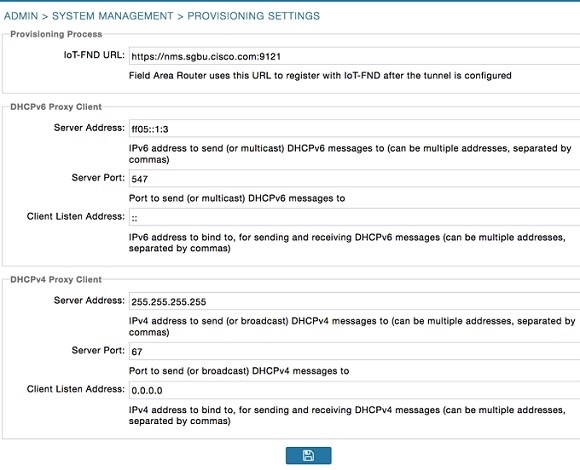 |
|
Step 5 |
Make sure you have obtained certificates from the CA (the same ones used to issue certs for FND). Execute the show ipsec certs command to verify. Make sure the firewall allows ports 9120, 9121, 9122, and all the SSH, telnet, and DHCP ports. Make sure the TPS name is pingable. Then execute the copy running express-setup-config command. You need to add the HER configuration manually, for example, the tunnel crypto profiles and transform sets. The following easyVPN example uses PSK as authentication. 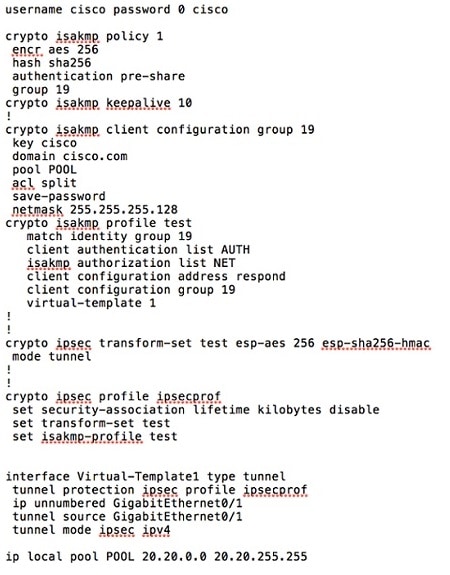 |
|
Step 6 |
Encrypt the PSK passwords using the signature-tool under /opt/cgms-tools/bin. Add the encrypted passwords in the CSV file and prepare it for upload. Add the modem to FND as the following sample CSV shows. Add ISR4K using the following CSV. |
|
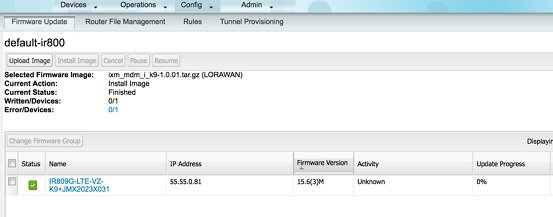
Step 7 |
Once the Modem is registered, the IXM will show as up in the FND. Please check the following events if there are issues during ZTD. 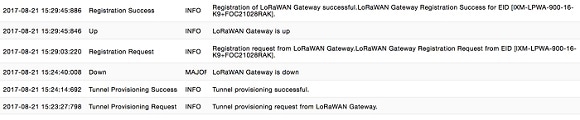 |
|
Step 8 |
Detailed IXM modem information can be viewed by clicking on the modem link. 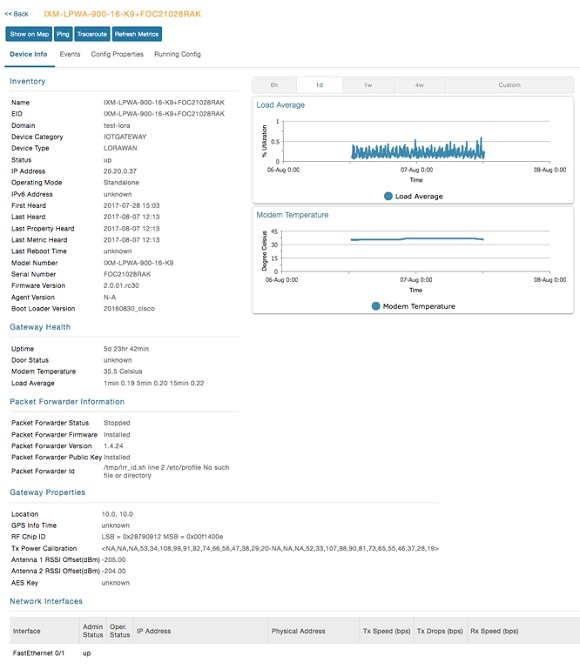 |
|
Step 9 |
If configuration update is required or a new modem is added to the router, follow the same procefure from Step 1. But in this case you invoke a configuration push. 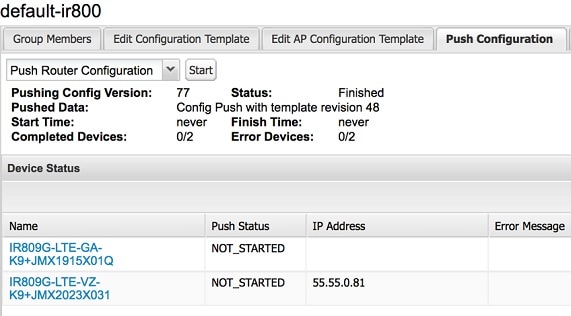 |
 Feedback
Feedback