- Overview of Cisco IoT Field Network Director
- Installing Cisco IoT FND
- Generating and Installing Certificates
- Managing User Access
- Managing System Settings
- Managing Devices
- Managing Firmware Upgrades
- Managing Tunnel Provisioning
- Monitoring System Activity
- Managing High Availability Installations
- Troubleshooting IoT FND
- Viewing Firmware Image Files in IoT FND
- Adding a Firmware Image to IoT FND
- Uploading a Firmware Image to a FAR Group
- Canceling FAR Firmware Image Upload
- Pausing and Resuming FAR Firmware Image Uploads
- Installing a Firmware Image
- Stopping Firmware Image Installation
- Pausing and Resuming FAR Firmware Image Installation
Managing Firmware Upgrades
This section describes managing firmware upgrade settings in IoT FND, and includes the following sections:
■![]() Configuring Firmware Group Settings
Configuring Firmware Group Settings
■![]() Working with FAR Firmware Images
Working with FAR Firmware Images
■![]() Working with Mesh Endpoint Firmware Images
Working with Mesh Endpoint Firmware Images
Use IoT FND to upgrade the firmware running on FARs (CGRs, C800s, IR800s, and AP800s) and MEs (CGEs and range extenders). IoT FND stores the firmware binaries in its database for later transfer to FARs in a firmware group through a IoT-DM file transfer, and to MEs using IoT FND.
Cisco provides the firmware bundles as a zip file. IoT FND automatically unzips the kickstart and system images included in the bundle. Firmware system images are large (approximately 130 MB); kickstart images are approximately 30 MB. Every firmware bundle includes a manifest file with metadata about the images in the bundle. You can pause, stop, or resume the upload process.
FAR Firmware Updates
IoT FND updates FAR firmware in two steps:
1.![]() Uploads the firmware image from IoT FND to the devices.
Uploads the firmware image from IoT FND to the devices.
Because of their large size, firmware-image uploads to FARs takes approximately 30 minutes, depending on interface speeds.
2.![]() Installs the firmware on the device and reloads it.
Installs the firmware on the device and reloads it.
Note: You must initiate the installation process. IoT FND does not start it automatically after the image upload.
When a FAR contacts IoT FND for the first time to register and request tunnel provisioning, IoT FND rolls the FAR back to the default factory configuration (ps-start-config) before uploading and installing the new firmware image.
Note: This rollback requires a second reload to update the boot parameters in ps-start-config and apply the latest configuration. This second reload adds an additional 10–15 minutes to the installation and reloading operation.
Upgrading Guest OS Images
Depending on CGR factory configuration, a Guest OS (GOS) may be present in the VM instance. You can install or upgrade Cisco IOS on the Config > Firmware Update page (see FAR Firmware Updates). The GOS, hypervisor, and Cisco IOS all upgrade when you perform a Cisco IOS image bundle installation or update.
After after any Cisco IOS install or upgrade, when IoT FND discovers a GOS, it checks if the initial communications setup is complete before it performs the required setup. The CGR must have a DHCP pool and GigabitEthernet 0/1 interface configured to provide an IP address and act as the gateway for the GOS. The new GOS image overwrites existing configurations. IoT FND has an internal backup and restore mechanism that ports existing apps to the upgraded Guest OS (see Managing a Guest OS).
See the Cisco 1000 Series Connected Grid Routers Configuration Guides documentation page for information on configuring the CGR.
Note: If IoT FND detects a non-Cisco OS installed on the VM, the firmware bundle will not upload and the Cisco reference GOS will not install.
Changing the CGR Timer
You can use the cgnms_preferences.sh script to set or retrieve the FAR timer expiration value in the IoT FND database:
■![]() set <pkg>actionExpirationTimeoutMins<value>
set <pkg>actionExpirationTimeoutMins<value>
–![]() <pkg> is the preference package (required for set and get operations).
<pkg> is the preference package (required for set and get operations).
–![]() actionExpirationTimeoutMins is the preference key (required for set and get operations).
actionExpirationTimeoutMins is the preference key (required for set and get operations).
–![]() <value> is the preferred value, in minutes (required for set and setCgrActionExpirationTimeout operations).
<value> is the preferred value, in minutes (required for set and setCgrActionExpirationTimeout operations).
■![]() setCgrActionExpirationTimeout <value>
setCgrActionExpirationTimeout <value>
■![]() get <pkg>actionExpirationTimeoutMins
get <pkg>actionExpirationTimeoutMins
■![]() getCgrActionExpirationTimeout
getCgrActionExpirationTimeout
In the following example, CGR timer value is retrieved, set, the current value retrieved again, the value removed, and a null value retrieved:
Mesh Endpoint Firmware Updates
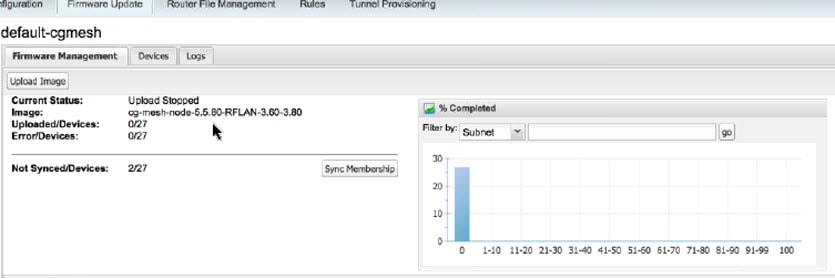
When you instruct IoT FND to upload a firmware image to the members of an ME firmware group or subnet, IoT FND pushes the image to the group members in the background and tracks the upload progress to ensure that the devices receive the image.
A mesh endpoint stores three firmware images:
■![]() Uploaded image: Image most recently uploaded.
Uploaded image: Image most recently uploaded.
■![]() Running image: Image that is currently operational.
Running image: Image that is currently operational.
■![]() Backup image: It serves as a golden (fallback) image for the endpoint if there is an issue with the running image.
Backup image: It serves as a golden (fallback) image for the endpoint if there is an issue with the running image.
Note: You can initiate up to 3 firmware downloads simultaneously.
Mesh Firmware Migration (CG-OS CG4 platforms only)
Note: Mesh Firmware Migration to Cisco Mesh is not supported for CGRs running CG-OS version CG4(4).
IoT FND allows you to update earlier versions of CGR firmware to allow Cisco mesh networking using the following IoT FND North Bound APIs:
■![]() startReprovisionByEidListAbridged
startReprovisionByEidListAbridged
■![]() startReprovisionByGroupAbridged
startReprovisionByGroupAbridged
See the Cisco Connected Grid NMS North Bound API Programming Guide for usage information.
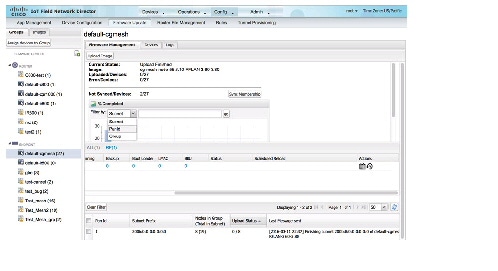
Configuring Firmware Group Settings
This section describes how to add, delete, and configure firmware groups, and includes the following topics:
■![]() Assigning Devices to a Firmware Group
Assigning Devices to a Firmware Group
Note: Upload operations only begin when you click the Resume button.
When you add FARs or MEs to IoT FND, the application sorts the devices into the corresponding default firmware group: default- <router> or default-cgmesh. Use these groups to upload and install firmware images on member devices. Add firmware groups to manage custom sets of devices. You can assign devices to firmware groups manually or in bulk. Before deleting a firmware group, you must move all devices in the group to another group. You cannot delete non-empty groups.
Note: When creating firmware groups note the following caveats:
■![]() CGRs, IR800s, and C800s can coexist on a network; however, for firmware management, they cannot belong to the same firmware group.
CGRs, IR800s, and C800s can coexist on a network; however, for firmware management, they cannot belong to the same firmware group.
■![]() IR500s and other mesh endpoint devices can coexist on a network; however, for firmware management, they cannot belong to the same group.
IR500s and other mesh endpoint devices can coexist on a network; however, for firmware management, they cannot belong to the same group.
The Groups tab on the Config > Firmware Update page displays various device metrics.
IoT FND displays this information about the image on the FARs in the selected firmware group:
|
|
|
|---|---|
| The name of the current image zip archive or the image being uploaded to group members. |
|
| The status of the image uploading. Possible statuses are: ■ ■ ■ |
|
| Specifies how many devices received or installed the image out of the total number of devices in the group. For example, 1/3 means that one device received the firmware image out of 3 devices in the group. |
|
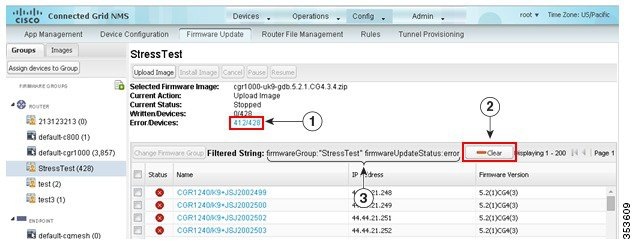
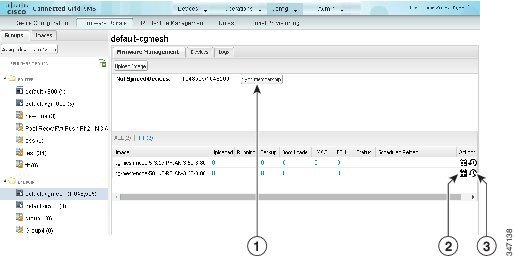
| Specifies how many devices failed to receive or install the image out of the total number of devices in the group. For example, 2/3 means that two out of the three devices in the group failed to install the image. Tip: Click the Error/Devices link (1 in Firmware Update Page – Errored Devices) to view the devices that are in the errored state. |
For every FAR in the group, IoT FND displays this information:
|
|
|
|---|---|
| Firmware image updating progress. A progress of 100% indicates that the image uploading is complete. |
|
Tip: Click the Error/Devices link (1 in Firmware Update Page – Errored Devices) to apply a filter (3). Click the Clear (2) button to revert to an unfiltered view of the selected device group.
Figure 1 Firmware Update Page – Errored Devices
Adding Firmware Groups
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select default-cgr1000, default-c800, default-ir500, default-ir800, or default-cgmesh.
In the FIRMWARE GROUPS pane, select default-cgr1000, default-c800, default-ir500, default-ir800, or default-cgmesh.
4.![]() Click Add Group (
Click Add Group ( ) at the top-right of the FIRMWARE GROUPS pane.
) at the top-right of the FIRMWARE GROUPS pane.
5.![]() In the Add Group dialog box, enter the name of the firmware group. Device Category is dependent on the device type you select in In the FIRMWARE GROUPS pane, select default-cgr1000, default-c800, default-ir500, default-ir800, or default-cgmesh..
In the Add Group dialog box, enter the name of the firmware group. Device Category is dependent on the device type you select in In the FIRMWARE GROUPS pane, select default-cgr1000, default-c800, default-ir500, default-ir800, or default-cgmesh..
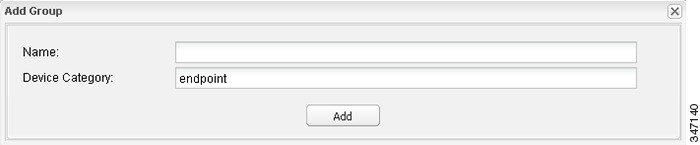
The new group label appears under the corresponding device type in the FIRMWARE GROUPS pane.
To assign devices to the new group, see Assigning Devices to a Firmware Group.
Assigning Devices to a Firmware Group
This section describes moving devices, and includes the following topics:
Moving Devices to Another Group Manually
To manually move devices to a group:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the desired firmware group based on device type.
In the FIRMWARE GROUPS pane, select the desired firmware group based on device type.
Note: If this is an ENDPOINT firmware group, click the Devices![]() tab above the main pane.
tab above the main pane.
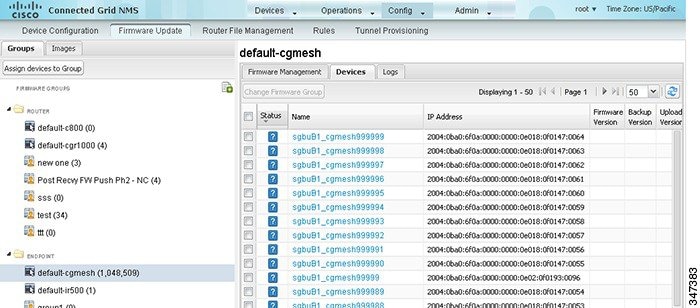
4.![]() Check the check boxes of the devices that you want to move.
Check the check boxes of the devices that you want to move.
5.![]() Click Change Firmware Group.
Click Change Firmware Group.
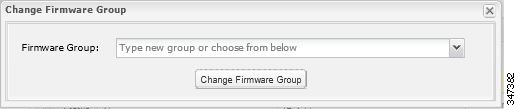
6.![]() From the Firmware Group drop-down menu, choose the firmware group to which you want to move the devices or enter a new group name.
From the Firmware Group drop-down menu, choose the firmware group to which you want to move the devices or enter a new group name.
Moving Devices to Another Group In Bulk
To move devices from one group to another in bulk:
1.![]() Create a CSV or XML file listing devices that you want to move using the format shown in the following examples:
Create a CSV or XML file listing devices that you want to move using the format shown in the following examples:
|
|
|
|
|
|
|
Note: Each file can only list one device type.
2.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
4.![]() Click Assign Devices to Group.
Click Assign Devices to Group.
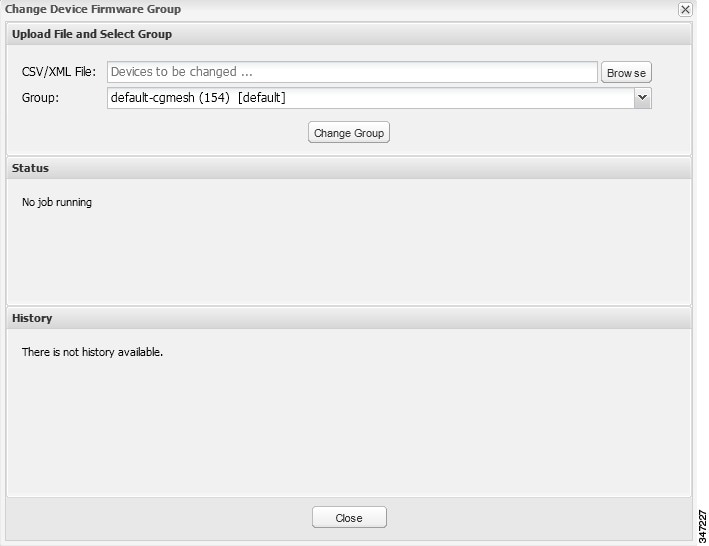
5.![]() Click Browse and locate the device list CSV or XML file.
Click Browse and locate the device list CSV or XML file.
6.![]() From the Group drop-down menu, choose the destination group.
From the Group drop-down menu, choose the destination group.
IoT FND moves the devices listed in the file from their current group to the destination group.
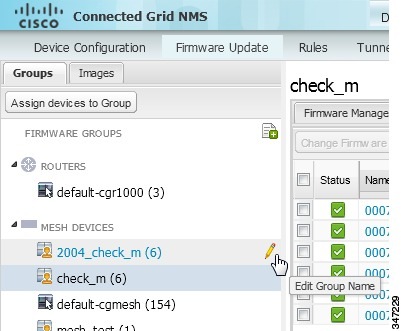
Renaming a Firmware Group
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the firmware group to rename.
In the FIRMWARE GROUPS pane, select the firmware group to rename.
4.![]() Move the cursor over the group and click the Edit Group Name pencil icon.
Move the cursor over the group and click the Edit Group Name pencil icon.
5.![]() In the Rename Group window, enter the new name and then click OK.
In the Rename Group window, enter the new name and then click OK.
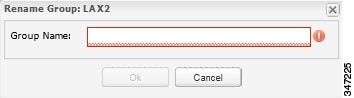
Note: As shown above, when you enter an invalid character entry (such as, @, #, !, or +) within a field, IoT FND displays a red alert icon, highlights the field in red, and disables the OK![]() button.
button.
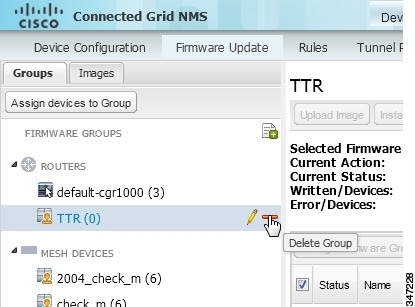
Deleting Firmware Groups
Note: Before deleting a firmware group, you must move all devices in the group to another group. You cannot delete non-empty groups.
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the firmware group to delete.
In the FIRMWARE GROUPS pane, select the firmware group to delete.
4.![]() Move the cursor over the group and click Delete Group (
Move the cursor over the group and click Delete Group ( ).
).
Working with FAR Firmware Images
This section describes how to add FAR firmware images to IoT FND and how to upload and install the images on FARs, and includes the following topics:
■![]() Viewing Firmware Image Files in IoT FND
Viewing Firmware Image Files in IoT FND
■![]() Adding a Firmware Image to IoT FND
Adding a Firmware Image to IoT FND
■![]() Uploading a Firmware Image to a FAR Group
Uploading a Firmware Image to a FAR Group
■![]() Canceling FAR Firmware Image Upload
Canceling FAR Firmware Image Upload
■![]() Pausing and Resuming FAR Firmware Image Uploads
Pausing and Resuming FAR Firmware Image Uploads
■![]() Stopping Firmware Image Installation
Stopping Firmware Image Installation
■![]() Pausing and Resuming FAR Firmware Image Installation
Pausing and Resuming FAR Firmware Image Installation
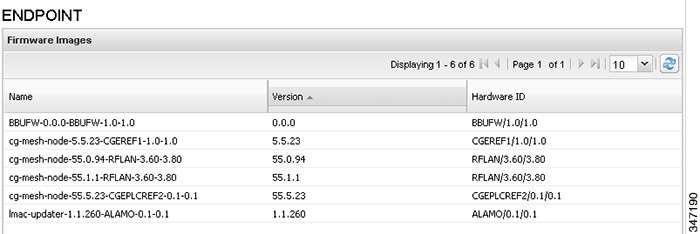
Viewing Firmware Image Files in IoT FND
You can display firmware image information from the Images pane in the Config > Firmware Update page. Select ROUTER or ENDPOINT to display all firmware images for those devices in the IoT FND database. Select the firmware image type to refine the display. For example, Config > Firmware Update Images Pane shows that selecting ENDPOINT > BBU displays the available BBU firmware image file name and version, and supported Hardware ID.
Figure 2 Config > Firmware Update Images Pane
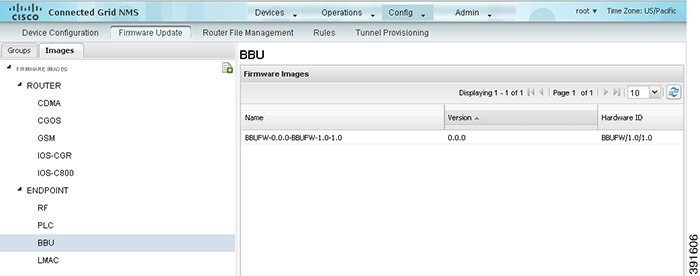
For every image in the list, IoT FND provides this information:
|
|
|
|---|---|
Adding a Firmware Image to IoT FND
Before you can upload and install a firmware image on a device, add the image file (as a zip archive) to IoT FND. IoT FND stores the image in its database.
Note: Do not unzip the image file. IoT FND unzips the file.
To add a firmware image to IoT FND:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
2.![]() Click the Images tab (Config > Firmware Update Images Pane).
Click the Images tab (Config > Firmware Update Images Pane).
3.![]() In the Firmware Images pane, select ROUTER or ENDPOINT, and the type of device group.
In the Firmware Images pane, select ROUTER or ENDPOINT, and the type of device group.
5.![]() Click Browse to locate the firmware image. Select the image, then click Choose.
Click Browse to locate the firmware image. Select the image, then click Choose.
The image appears in the Firmware Images pane.
| ■ |
| Firmware images with a download in progress (with Yes in the Active Download? column) cannot be deleted. |
| ■ |
Uploading a Firmware Image to a FAR Group
When you upload a firmware image to FAR firmware group members, IoT FND pushes the image to the group members in the background and tracks the upload progress to ensure that the devices receive the image.
On FARs, firmware image upload and installation requires 200 MB of free disk space. IoT FND stores image files in the.../managed/images directory on the FAR.
Note: If there is not enough disk space on the FAR for the firmware image, the IoT FND initiates disk cleanup process on the FAR and removes the following files, sequentially, until there is enough disk space to upload the new image:
■![]() Unused files in the.../managed/images directory that are not currently running or referenced in the before-tunnel-config, before-registration-config, express-setup-config, and factory-config files for IOS CGRs; golden-config, ps-start-config, express-setup-config, or factory-config for CG-OS CGRs
Unused files in the.../managed/images directory that are not currently running or referenced in the before-tunnel-config, before-registration-config, express-setup-config, and factory-config files for IOS CGRs; golden-config, ps-start-config, express-setup-config, or factory-config for CG-OS CGRs
■![]() Unused.gbin and.bin files from the bootflash directory in CG-OS CGRs
Unused.gbin and.bin files from the bootflash directory in CG-OS CGRs
If there is still not enough space, you must manually delete unused files on the FAR.
To upload a firmware image to FAR group members:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the firmware group to update.
In the FIRMWARE GROUPS pane, select the firmware group to update.
Note: CGR groups can include devices running Cisco IOS and CG-OS. Therefore, Cisco IOS software images only upload to devices running Cisco IOS (IR800s, ISR800s, CGRs); only CGRs accept CG-OS images.
IoT FND displays the firmware image type applicable the router:
|
|
|
|
|---|---|---|
5.![]() From the Select Type: drop-down menu, choose the firmware type for your device.
From the Select Type: drop-down menu, choose the firmware type for your device.
6.![]() From the Select an Image: drop-down menu, choose the firmware bundle to upload.
From the Select an Image: drop-down menu, choose the firmware bundle to upload.
IoT FND starts the upload process. After the image uploads, install the image as described in Installing a Firmware Image.
Canceling FAR Firmware Image Upload
You can stop the image upload process to firmware router groups at any time. Stopping the upload can take a few minutes. When you cancel the image upload, the image upload process immediately stops currently running tasks, and blocks all queued tasks.
Note: Running tasks do not complete, leaving partial files on the disk and sets the firmware group status to CANCELING until you complete the upload operation.
To stop firmware image uploading to a group:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
Pausing and Resuming FAR Firmware Image Uploads
You can pause the image upload process to FAR firmware groups at any time, and resume it later.
Note: The image upload process does not immediately pause; all queued (but not running) operations pause, but currently running tasks complete. The status changes to PAUSING until the active operations complete.
To pause firmware image upload:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the firmware group.
In the FIRMWARE GROUPS pane, select the firmware group.
The Status column displays PAUSING until the active upload operations complete. No new upload operations start until you click the Resume button.
To resume the upload process, click Resume.
Note: If a IoT FND server goes down while the firmware image is being uploaded to devices, the server resumes the upload process for the scheduled devices after the server comes up. For IoT FND server clusters, if one server goes down during the upload process, another server in the cluster resumes the process.
Installing a Firmware Image
To install an image on devices in a router firmware group:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the firmware group.
In the FIRMWARE GROUPS pane, select the firmware group.
Note: IoT FND recognizes devices as firmware-specific, and uploads the proper image to selected devices. Select a device subgroup in the Images pane to refine the display to those device types.
IoT FND sends commands to the FARs in the group to install the uploaded image and reload the FAR to ensure that the new image is operational.
IoT FND starts the installation or reloading process.
Note: If you restart IoT FND during the image installation process, IoT FND restarts the firmware installation operations that were running prior to IoT FND going offline.
You can pause or stop the installation operation as described in:
■![]() Stopping Firmware Image Installation
Stopping Firmware Image Installation
■![]() Pausing and Resuming FAR Firmware Image Installation.
Pausing and Resuming FAR Firmware Image Installation.
Note: The firmware installation operation can time out on some routers. If routers are not heard from for more than an hour, IoT FND logs error messages.
Stopping Firmware Image Installation
You can stop firmware image installation at any time. When you stop image installation, the running version of the firmware remains in place.
Note: Stopping the installation cancels all queued tasks. Currently running tasks complete.
To stop firmware image installation to devices in a firmware group:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
Pausing and Resuming FAR Firmware Image Installation
You can pause the firmware image installation process at any time.
Note: Pausing the installation pauses all queued tasks. Currently running tasks complete.
To pause firmware image installation to devices in a firmware group:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
Performing OS Migrations
You can upgrade CGRs from CG-OS to IOS in bulk or by device. The migration package is in the IoT Field Network Director installation package, and is available in the Select IOS Image menu.
Note: The Migration to IOS button is disabled if all CGRs in the group are IOS.
For CG-OS CGRs that you are migrating, modify the device configuration properties CSV or XML file to include the following IOS properties (see Changing Device Configuration Properties):
This example preserves tunnels during migration:
Note: You can only migrate from CG4(3) to the minimum IOS image for that device. Refer to Table 1 for minimum IOS image requirements.
To add CGR IOS images to IoT Field Network Director and upload and install the migration image on CGRs:
1.![]() Select Config > Firmware Update, and click the Migration to IOS tab.
Select Config > Firmware Update, and click the Migration to IOS tab.

2.![]() In the ROUTERS pane, select a CGR group.
In the ROUTERS pane, select a CGR group.
3.![]() Select the check box at the top of the devices list for group migration or individual CGRs, and click Upload Image.
Select the check box at the top of the devices list for group migration or individual CGRs, and click Upload Image.
4.![]() From the Select IOS Image drop-down menu, choose the desired image, and click Upload Image.
From the Select IOS Image drop-down menu, choose the desired image, and click Upload Image.

5.![]() Click OK to begin the upload.
Click OK to begin the upload.

Upload progress appears in the device list.
6.![]() Upload the following properties files (see Installing Cisco IoT FND):
Upload the following properties files (see Installing Cisco IoT FND):
7.![]() Click the Migrate To IOS button.
Click the Migrate To IOS button.

8.![]() Click Yes to confirm and begin the migration process.
Click Yes to confirm and begin the migration process.
You can follow the update progress in the devices list. Error messages also appear in the devices list. You can cancel, pause, and resume the migration process.
Tip: If any routers fail to upgrade, restart migration on the group. IoT Field Network Director skips upgraded routers.
Interface Names After Migration
IoT Field Network Director preserves metrics for the various interfaces and associated properties during migration. CG-OS-to-IOS Interface Migration Map maps CG-OS interfaces to the corresponding IOS interfaces to preserve metrics.
CG-OS Interface |
Corresponding IOS Interface |
|---|---|
Working with Mesh Endpoint Firmware Images
This section describes how to add ME firmware images to IoT FND, and how to upload and install the images on FARs, and includes the following topics:
■![]() Uploading a Firmware Image to a Mesh Endpoint Group
Uploading a Firmware Image to a Mesh Endpoint Group
■![]() Viewing Mesh Device Firmware Image Upload Logs
Viewing Mesh Device Firmware Image Upload Logs
■![]() Viewing Mesh Endpoint Firmware Update Information
Viewing Mesh Endpoint Firmware Update Information
Note: IR500s and other mesh endpoint devices can coexist on a network; however, for firmware management they cannot belong to the same group.
Note: ENDPOINT devices can report BL/Boot Loader image types to IoT FND, but IoT FND cannot upload boot loader images to devices.
Uploading a Firmware Image to a Mesh Endpoint Group
To upload a firmware image to ME group members:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the firmware group to update.
In the FIRMWARE GROUPS pane, select the firmware group to update.
6.![]() From the Select Type: drop-down menu, choose the firmware type for your device.
From the Select Type: drop-down menu, choose the firmware type for your device.
IoT FND can upload these image types to ENDPOINT devices.
|
|
|
|---|---|
7.![]() From the Select an Image: drop-down menu, choose the firmware bundle to upload.
From the Select an Image: drop-down menu, choose the firmware bundle to upload.
IoT FND adds the image to the list of images in the Firmware Management pane and starts the upload process in the background.
|
|
|
|
|
|
|
|
For every image in the list, IoT FND displays the following information:
Setting the Installation Schedule
To set the installation schedule:
1.![]() Click the Schedule Install and Reload button (2).
Click the Schedule Install and Reload button (2).
2.![]() Specify the date and time for the installation of the image and the rebooting of the device.
Specify the date and time for the installation of the image and the rebooting of the device.
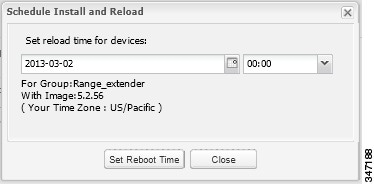
| ■ |
| ■ |
Viewing Mesh Device Firmware Image Upload Logs
To view the firmware image upload logs for mesh devices:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select the mesh device firmware group.
In the FIRMWARE GROUPS pane, select the mesh device firmware group.
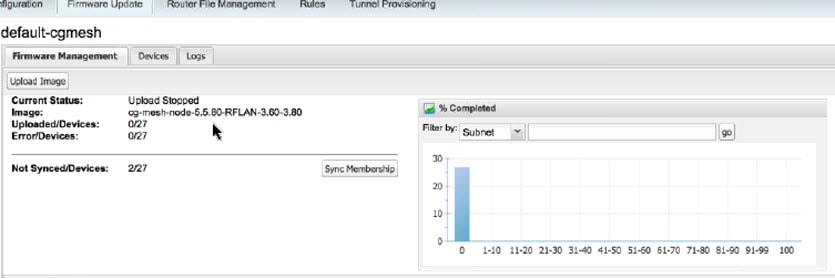
Viewing Mesh Endpoint Firmware Update Information
You can view the endpoint firmware update process down to the subnet level for greater visibility.
To view details of firmware updates for mesh endpoint devices (by subnet) during the upgrade process or after the firmware upgrade completes in a tabular and graphical manner (histogram):
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select a MESH DEVICES group.
In the FIRMWARE GROUPS pane, select a MESH DEVICES group.
4.![]() Click the Firmware Management tab.
Click the Firmware Management tab.
Viewing Mesh Device Firmware Information
To view the firmware information for mesh devices:
1.![]() Choose Config > Firmware Update.
Choose Config > Firmware Update.
3.![]() In the FIRMWARE GROUPS pane, select a MESH DEVICES group.
In the FIRMWARE GROUPS pane, select a MESH DEVICES group.
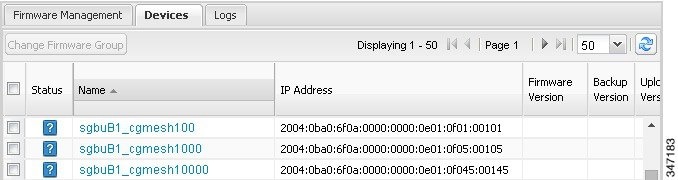
For every device in the group, IoT FND displays this information:
|
|
|
|---|---|
| Firmware image upload progress. An update progress of 100% indicates that the upload is complete. |
|
 Feedback
Feedback