- Preface
- Cisco 800M Series Integrated Services Routers Overview
- Basic Router Configuration
- Configuring 3G Wireless WAN
- Configuring the Serial Interface
- Configuring Ethernet Switch Ports
- Configuring Security Features
- Configuring QoS
- Configuring Network Management Features
- Configuring IP Addressing and IP Services Features
- Configuring Authentication, Authorization, and Accounting
- Configuring Access Lists
- Configuring Cisco IOS IPS
- Configuring VPN
Configuring Security Features
The Cisco 800M Series ISR provides the following security features:
- Configuring Authentication, Authorization, and Accounting
- Configuring Access Lists
- Configuring Cisco IOS IPS
- Configuring VPN
- Configuring Dynamic Multipoint VPN
- Configuring Group Encrypted Transport VPN
- Configuring SSL VPN
- Configuring FlexVPN
- Configuring Zone-Based Policy Firewall
- Configuring VRF-Aware Cisco Firewall
- Configuring Subscription-Based Cisco IOS Content Filtering
- Configuring On-Device Management for Security Features
- Related Documents
Configuring Authentication, Authorization, and Accounting
Authentication, Authorization, and Accounting (AAA) network security services provide the primary framework through which you set up access control on your router. Authentication provides the method of identifying users, including login and password dialog, challenge and response, messaging support, and encryption depending on the security protocol you choose. Authorization provides the method for remote access control, including one-time authorization or authorization for each service, per-user account list and profile, user group support, and support of IP, Internetwork Packet Exchange (IPX), AppleTalk Remote Access (ARA), and Telnet. Accounting provides the method for collecting and sending security server information used for billing, auditing, and reporting, such as user identities, start and stop times, executed commands (such as PPP), number of packets, and number of bytes.
AAA uses protocols such as Remote Authentication Dial-In User Service (RADIUS), Terminal Access Controller Access Control System Plus (TACACS+), or Kerberos to administer its security functions. If your router is acting as a network access server, AAA is the means through which you establish communication between your network access server and your RADIUS, TACACS+, or Kerberos security server.
For information about configuring AAA services and supported security protocols, see the following guide:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_usr_aaa/configuration/15-mt/sec-usr-aaa-15-mt-book.html
Configuring Access Lists
Access lists permit or deny network traffic over an interface, based on source IP address, destination IP address, or protocol. Access lists are configured as standard or extended. A standard access list either permits or denies passage of packets from a designated source. An extended access list allows designation of both the destination and the source, and it allows designation of individual protocols to be permitted or denied passage.
An access list is a series of commands with a common tag to bind them together. The tag is either a number or a name. Table 6-1 lists the commands used to configure access lists.
For more complete information on creating access lists, see the following web link: http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_data_acl/configuration/15-mt/sec-data-acl-15-mt-book.html
Access Groups
An access group is a sequence of access list definitions bound together with a common name or number. An access group is enabled for an interface during interface configuration. Use the following guidelines when creating access groups:
- The order of access list definitions is significant. A packet is compared against the first access list in the sequence. If there is no match (that is, if neither a permit nor a deny occurs), the packet is compared with the next access list, and so on.
- All parameters must match the access list before the packet is permitted or denied.
- There is an implicit “deny all” at the end of all sequences.
For information on configuring and managing access groups, see the following link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_data_acl/configuration/15-mt/sec-data-acl-15-mt-book/sec-create-ip-al-filter.html
Configuring Cisco IOS IPS
The Cisco IOS Intrusion Prevention System (IPS) acts as an in-line intrusion detection sensor, watching packets and sessions as they flow through the router and scanning each packet to match any of the Cisco IOS IPS signatures. When Cisco IOS IPS detects suspicious activity, it responds before network security can be compromised and logs the event through Cisco IOS syslog messages or Security Device Event Exchange (SDEE). The network administrator can configure Cisco IOS IPS to choose the appropriate response to various threats. When packets in a session match a signature, Cisco IOS IPS can take any of the following actions, as appropriate:
- Send an alarm to a syslog server or a centralized management interface
- Drop the packet
- Reset the connection
- Deny traffic from the source IP address of the attacker for a specified amount of time
- Deny traffic on the connection for which the signature was seen for a specified amount of time
For more information about configuring Cisco IOS IPS see the following web link:
http://www.cisco.com/c/en/us/td/docs/ios/sec_data_plane/configuration/guide/convert/sec_data_ios_ips_15_1_book/sec_cfg_ips.html
Configuring VPN
A Virtual Private Network (VPN) connection provides a secure connection between two networks over a public network such as the Internet. Cisco 800M Series ISRs support two types of VPNs: site-to-site and remote access. Remote access VPNs are used by remote clients to log in to a corporate network. Site-to-site VPNs connect branch offices to corporate offices. This section gives examples for site-to-site and remote access VPNs.
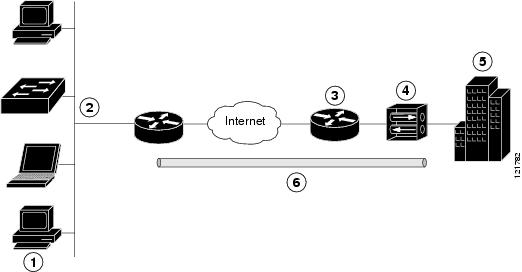
The configuration of a remote access VPN uses Cisco Easy VPN and an IP Security (IPSec) tunnel to configure and secure the connection between the remote client and the corporate network. Figure 6-1 shows a typical deployment scenario.
Figure 6-1 Remote Access VPN Using IPSec Tunnel
|
|
|
|
|
|
|
|
|
|
|
VPN server—Easy VPN server; for example, a Cisco VPN 3000 concentrator with outside interface address 210.110.101.1 |
|
|
|
|
|
The Cisco Easy VPN client feature eliminates much of the tedious configuration work by implementing the Cisco Unity Client protocol. This protocol allows most VPN parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, Windows Internet Naming Service (WINS) server addresses, and split-tunneling flags, to be defined at a VPN server, such as a Cisco VPN 3000 series concentrator that is acting as an IPSec server.
A Cisco Easy VPN server–enabled device can terminate VPN tunnels initiated by mobile and remote workers who are running Cisco Easy VPN Remote software on PCs. Cisco Easy VPN server–enabled devices allow remote routers to act as Cisco Easy VPN Remote nodes.
The Cisco Easy VPN client feature can be configured in one of two modes—client mode or network extension mode. Client mode is the default configuration and allows only devices at the client site to access resources at the central site. Resources at the client site are unavailable to the central site. Network extension mode allows users at the central site (where the Cisco VPN 3000 series concentrator is located) to access network resources on the client site.
After the IPSec server has been configured, a VPN connection can be created with minimal configuration on an IPSec client. When the IPSec client initiates the VPN tunnel connection, the IPSec server pushes the IPSec policies to the IPSec client and creates the corresponding VPN tunnel connection.

Note![]() The Cisco Easy VPN client feature supports configuration of only one destination peer. If your application requires creation of multiple VPN tunnels, you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on both the client and the server.
The Cisco Easy VPN client feature supports configuration of only one destination peer. If your application requires creation of multiple VPN tunnels, you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on both the client and the server.
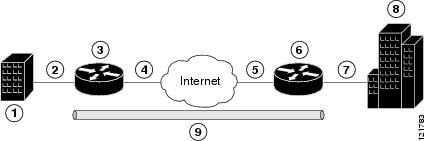
The configuration of a site-to-site VPN uses IPSec and the generic routing encapsulation (GRE) protocol to secure the connection between the branch office and the corporate network. Figure 6-2 shows a typical deployment scenario.
Figure 6-2 Site-to-Site VPN Using an IPSec Tunnel and GRE
For more information about IPSec and GRE configuration, see the following link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_vpnips/configuration/15-mt/sec-sec-for-vpns-w-ipsec-15-mt-book/sec-cfg-vpn-ipsec.html
Each example configures a VPN over an IPSec tunnel, using the procedure given in the “Configure a VPN over an IPSec Tunnel” section. Then, the specific procedure for a remote access configuration is given, followed by the specific procedure for a site-to-site configuration.
The examples shown in this chapter apply only to the endpoint configuration on the Cisco 800M Series ISRs. Any VPN connection requires both endpoints to be properly configured in order to function. See the software configuration documentation as needed to configure VPN for other router models.
VPN configuration information must be configured on both endpoints. You must specify parameters such as internal IP addresses, internal subnet masks, DHCP server addresses, and Network Address Translation (NAT).
- “Configure a VPN over an IPSec Tunnel” section
- “Create a Cisco Easy VPN Remote Configuration” section
- “Configure a Site-to-Site GRE Tunnel” section
Configure a VPN over an IPSec Tunnel
Perform the following tasks to configure a VPN over an IPSec tunnel:
Configure the IKE Policy
To configure the Internet Key Exchange (IKE) policy, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
1.![]() crypto isakmp policy priority
crypto isakmp policy priority
2.![]() encryption { des | 3des | aes | aes 192 | aes 256}
encryption { des | 3des | aes | aes 192 | aes 256}
DETAILED STEPS
|
|
|
|
|---|---|---|
|
|
Creates an IKE policy that is used during IKE negotiation. The priority is a number from 1 to 10000, with 1 being the highest. Also enters the ISAKMP1 policy configuration mode. |
|
encryption { des | 3des | aes | aes 192 | aes 256} |
Specifies the encryption algorithm used in the IKE policy. The example specifies 168-bit DES2. |
|
|
|
Specifies the hash algorithm used in the IKE policy. The example specifies the MD53 algorithm. The default is SHA-14. |
|
authentication { rsa-sig | rsa-encr | pre-share } |
||
|
|
Specifies the Diffie-Hellman group to be used in an IKE policy. |
|
|
|
Specifies the lifetime, from 60 to 86400 seconds, for an IKE SA5. |
|
|
|
Exits IKE policy configuration mode and enters global configuration mode. |
|
1.ISAKMP = Internet Security Association Key and Management Protocol |
Configure Group Policy Information
To configure the group policy, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
1.![]() crypto isakmp client configuration group { group-name | default }
crypto isakmp client configuration group { group-name | default }
6.![]() ip local pool { default | poolname } [ low-ip-address [ high-ip-address ]]
ip local pool { default | poolname } [ low-ip-address [ high-ip-address ]]
DETAILED STEPS
|
|
|
|
|---|---|---|
crypto isakmp client configuration group { group-name | default } Router(config)# crypto isakmp client configuration group rtr-remote |
Creates an IKE policy group containing attributes to be downloaded to the remote client. |
|
|
|
||
|
|
Specifies the primary DNS6 server for the group. You may also want to specify WINS7 servers for the group by using the wins command. |
|
|
|
||
|
|
Exits IKE group policy configuration mode and enters global configuration mode. |
|
ip local pool { default | poolname } [ low-ip-address [ high-ip-address ]] Router(config)# ip local pool dynpool 30.30.30.20 30.30.30.30 |
Specifies a local address pool for the group. For details about this command and additional parameters that can be set, see Cisco IOS Dial Technologies Command Reference. |
|
|
Apply Mode Configuration to the Crypto Map
To apply mode configuration to the crypto map, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
1.![]() crypto map map-name isakmp authorization list list-name
crypto map map-name isakmp authorization list list-name
2.![]() crypto map tag client configuration address [ initiate | respond ]
crypto map tag client configuration address [ initiate | respond ]
DETAILED STEPS
Enable Policy Lookup
To enable policy lookup through AAA, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
2.![]() aaa authentication login { default | list-name } method1 [ method2... ]
aaa authentication login { default | list-name } method1 [ method2... ]
3.![]() aaa authorization {network | exec | commands level | reverse-access | configuration } { default | list-name } [ method1 [ method2... ]]
aaa authorization {network | exec | commands level | reverse-access | configuration } { default | list-name } [ method1 [ method2... ]]
4.![]() username name {nopassword | password password | password encryption-type encrypted-password }
username name {nopassword | password password | password encryption-type encrypted-password }
DETAILED STEPS
|
|
|
|
|---|---|---|
|
|
||
aaa authentication login { default | list-name } method1 [ method2... ] |
Specifies AAA authentication of selected users at login, and specifies the method used. This example uses a local authentication database. You could also use a RADIUS server for this. For details, see Cisco IOS Security Configuration Guide: Securing User Services, Release 15M&T and Cisco IOS Security Command Reference. |
|
aaa authorization {network | exec | commands level | reverse-access | configuration } { default | list-name } [ method1 [ method2... ]] |
Specifies AAA authorization of all network-related service requests, including PPP, and specifies the method of authorization. |
|
username name {nopassword | password password | password encryption-type encrypted-password } |
Configure IPSec Transforms and Protocols
A transform set represents a certain combination of security protocols and algorithms. During IKE negotiation, the peers agree to use a particular transform set for protecting data flow.
During IKE negotiations, the peers search multiple transform sets for a transform that is the same at both peers. When a transform set is found that contains such a transform, it is selected and applied to the protected traffic as a part of both peers’ configurations.
To specify the IPSec transform set and protocols, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
1.![]() crypto ipsec profile profile-name
crypto ipsec profile profile-name
2.![]() crypto ipsec transform-set transform-set-name
crypto ipsec transform-set transform-set-name
3.![]() crypto ipsec security-association lifetime { seconds seconds | kilobytes kilobytes }
crypto ipsec security-association lifetime { seconds seconds | kilobytes kilobytes }
DETAILED STEPS
|
|
|
|
|---|---|---|
crypto ipsec profile profile-name |
Configures an IPSec profile to apply protection on the tunnel for encryption. |
|
crypto ipsec transform-set transform-set-name transform1 [ transform2 ] [ transform3 ] [ transform4 ] Router(config)# crypto ipsec transform-set vpn1 esp-3des esp-sha-hmac |
Defines a transform set—an acceptable combination of IPSec security protocols and algorithms. See Cisco IOS Security Command Reference for detail about the valid transforms and combinations. |
|
crypto ipsec security-association lifetime { seconds seconds | kilobytes kilobytes } Router(config)# crypto ipsec security-association lifetime seconds 86400 |
Specifies global lifetime values used when IPSec security associations are negotiated. |
Configure the IPSec Crypto Method and Parameters
A dynamic crypto map policy processes negotiation requests for new security associations from remote IPSec peers, even if the router does not know all the crypto map parameters (for example, IP address).
To configure the IPSec crypto method, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
1.![]() crypto dynamic-map dynamic-map-name dynamic-seq-num
crypto dynamic-map dynamic-map-name dynamic-seq-num
2.![]() set transform-set transform-set-name [ transform-set-name2...transform-set-name6 ]
set transform-set transform-set-name [ transform-set-name2...transform-set-name6 ]
5.![]() crypto map map-name seq-num [ ipsec-isakmp ] [ dynamic dynamic-map-name ] [ discover ] [ profile profile-name ]
crypto map map-name seq-num [ ipsec-isakmp ] [ dynamic dynamic-map-name ] [ discover ] [ profile profile-name ]
DETAILED STEPS
|
|
|
|
|---|---|---|
crypto dynamic-map dynamic-map-name dynamic-seq-num |
Creates a dynamic crypto map entry and enters crypto map configuration mode. See Cisco IOS Security Command Reference for more detail about this command. |
|
set transform-set transform-set-name [ transform-set-name2...transform-set-name6 ] |
Specifies which transform sets can be used with the crypto map entry. |
|
|
|
||
|
|
||
crypto map map-name seq-num [ ipsec-isakmp ] [ dynamic dynamic-map-name ] [ discover ] [ profile profile-name ] Router(config)# crypto map static-map 1 ipsec-isakmp dynamic dynmap |
Apply the Crypto Map to the Physical Interface
The crypto maps must be applied to each interface through which IPSec traffic flows. Applying the crypto map to the physical interface instructs the router to evaluate all the traffic against the security associations database. With the default configurations, the router provides secure connectivity by encrypting the traffic sent between remote sites. However, the public interface still allows the rest of the traffic to pass and provides connectivity to the Internet.
To apply a crypto map to an interface, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
DETAILED STEPS
|
|
|
|
|---|---|---|
|
|
Enters the interface configuration mode for the interface to which you are applying the crypto map. |
|
|
|
||
|
|
Where to Go Next
If you are creating a Cisco Easy VPN remote configuration, go to the “Create a Cisco Easy VPN Remote Configuration” section.
If you are creating a site-to-site VPN using IPSec tunnels and GRE, go to the “Configure a Site-to-Site GRE Tunnel” section.
Create a Cisco Easy VPN Remote Configuration
The router that is acting as the Cisco Easy VPN client must create a Cisco Easy VPN remote configuration and assign it to the outgoing interface.
To create the remote configuration, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
1.![]() crypto ipsec client ezvpn name
crypto ipsec client ezvpn name
2.![]() group group-name key group-key
group group-name key group-key
3.![]() peer { ipaddress | hostname }
peer { ipaddress | hostname }
4.![]() mode { client | network-extension | network extension plus }
mode { client | network-extension | network extension plus }
6.![]() crypto isakmp keepalive seconds
crypto isakmp keepalive seconds
DETAILED STEPS
|
|
|
|
|---|---|---|
crypto ipsec client ezvpn name |
Creates a Cisco Easy VPN remote configuration, and enters Cisco Easy VPN remote configuration mode. |
|
group group-name key group-key Router(config-crypto-ezvpn)# group ezvpnclient key secret-password |
Specifies the IPSec group and IPSec key value for the VPN connection. |
|
Specifies the peer IP address or hostname for the VPN connection. Note A hostname can be specified only when the router has a DNS server available for hostname resolution. Note Use this command to configure multiple peers for use as backup. If one peer goes down, the Easy VPN tunnel is established with the second available peer. When the primary peer comes up again, the tunnel is reestablished with the primary peer. |
||
mode { client | network-extension | network extension plus } |
||
|
|
||
crypto isakmp keepalive seconds |
Enables dead peer detection messages. Time between messages is given in seconds, with a range of 10 to 3600. |
|
|
|
Enters the interface configuration mode for the interface to which you are applying the Cisco Easy VPN remote configuration. |
|
crypto ipsec client ezvpn name [ outside | inside ] Router(config-if)# crypto ipsec client ezvpn ezvpnclient outside |
Assigns the Cisco Easy VPN remote configuration to the WAN interface which causes the router to automatically create the NAT or PAT8 and the access list configuration needed for the VPN connection. |
|
|
|
|
|
Configuration Example
The following configuration example shows the EasyVPN client configuration.
Configure a Site-to-Site GRE Tunnel
To configure a site-to-site GRE tunnel, follow these steps, beginning in global configuration mode.
SUMMARY STEPS
3.![]() tunnel source interface-type number
tunnel source interface-type number
4.![]() tunnel destination default-gateway-ip-address
tunnel destination default-gateway-ip-address
7.![]() ip access-list { standard | extended } access-list-name
ip access-list { standard | extended } access-list-name
8.![]() permit protocol source source-wildcard destination destination-wildcard
permit protocol source source-wildcard destination destination-wildcard
DETAILED STEPS
|
|
|
|
|---|---|---|
|
|
Creates a tunnel interface and enters interface configuration mode. |
|
|
|
||
tunnel source interface-type number |
Specifies the source endpoint of the router for the GRE tunnel. |
|
tunnel destination default-gateway-ip-address |
Specifies the destination endpoint of the router for the GRE tunnel. |
|
|
|
Assigns a crypto map to the tunnel. Note Dynamic routing or static routes to the tunnel interface must be configured to establish connectivity between the sites.. |
|
|
|
Exits interface configuration mode and returns to global configuration mode. |
|
ip access-list { standard | extended } access-list-name |
Enters ACL9 configuration mode for the named ACL that the crypto map uses. |
|
permit protocol source source-wildcard destination destination-wildcard Router(config-acl)# permit gre host 192.168.100.1 host 192.168.101.1 |
Specifies that only GRE traffic is permitted on the outbound interface. |
|
|
|
|
|
Configuration Example
The following configuration example shows a portion of the configuration file for a site-to-site VPN using a GRE tunnel as described in the preceding sections.
Configuring Dynamic Multipoint VPN
The Dynamic Multipoint VPN (DMVPN) feature is a simplified solution to deploy large and small IP Security (IPsec) VPNs by combining GRE tunnels, IPsec encryption, and Next Hop Resolution Protocol (NHRP). DMVPN simplifies the configuration tasks in a large scale VPN deployment and reduces the administrative overhead.
DMVPN is useful in a scenario, when one central router at the head office acts as a hub and other branch routers act as spoke and connected to the hub router to access the company's resources. DMVPN is also useful for spoke to spoke deployment and can be used for branch-to-branch interconnections
See the Example: DMVPN Configuration for a typical DMVPN configuration for a hub and spoke deployment. For additional information about configuring DMVPN, see the following link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_dmvpn/configuration/15-mt/sec-conn-dmvpn-15-mt-book/sec-conn-dmvpn-dmvpn.html
Example: DMVPN Configuration
The following configuration example shows the configuration for DMVPN hub and spoke deployment model. In this example, Cisco 800M series ISR is configured as spoke and Cisco 2900 Series ISR is configured as hub. For readability some part of the configuration is removed.
This configuration section shows the configuration of 800M Series ISR as a spoke.
800M_spoke# show running-config
This configuration section shows the configuraton of 2900 Series ISR as hub.
Configuring Group Encrypted Transport VPN
Group Encrypted Transport VPN (GETVPN) is a tunnel-less VPN technology that provides end-to-end security for network traffic in a native mode and maintain the mesh topology. GET VPN combines the keying protocol Group Domain of Interpretation (GDOI) with IPsec encryption to provide users with an efficient method of securing IP multicast traffic or unicast traffic. GET VPN enables the router to apply encryption to tunnel-less (native) IP multicast and unicast packets and eliminates the requirement to configure tunnels to protect multicast and unicast traffic.
By removing the need for point-to-point tunnels, meshed networks can scale higher while maintaining network-intelligence features that are critical to voice and video quality, such as QoS, routing, and multicast. GET VPN offers a new standards-based IP security (IPsec) security model that is based on the concept of “trusted” group members. Trusted member routers use a common security methodology that is independent of any point-to-point IPsec tunnel relationship.
A GETVPN deployment has primarily three components, Key Server (KS), Group Member (GM), and Group Domain of Interpretation (GDOI) protocol. GMs encrypt or decrypt the traffic and KS distributes the encryption key to all the group members. The KS decides on one single data encryption key for a given life time. Since all GMs use the same key, any GM can decrypt the traffic encrypted by any other GM. GDOI protocol is used between the GM and KS for group key and group SA management. Minimum one KS is required for a GETVPN deployment.
Unlike traditional IPSec encryption solutions, GET VPN uses the concept of group security association (SA). All members in the GETVPN group can communicate with each other using a common encryption policy and a shared SA and therefore no need to negotiate IPSec between GMs on a peer to peer basis; thereby reducing the resource load on the GM routers.
See the Example: GETVPN Configuration for a sample GETVPN deployment configuration.
For additional information about configuring GET VPN, see the following link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_getvpn/configuration/15-mt/sec-get-vpn-15-mt-book/sec-get-vpn.html
Example: GETVPN Configuration
The following configuration example shows the configuration for GETVPN deployment. In this example, a Cisco 800M series ISR is configured as GM and the Cisco 1900 Series ISR is configured as KS.
This configuration section shows the configuration of 800M Series ISR as GM.
This configuration section shows the configuration of Cisco 1900 Series ISR as KS.
Configuring SSL VPN
The Secure Socket Layer Virtual Private Network (SSL VPN) feature provides support for remote user access to enterprise networks from anywhere on the Internet. Remote access is provided through a SSL–enabled SSL VPN gateway. The SSL VPN gateway allows remote users to establish a secure VPN tunnel using a web browser. This feature provides a comprehensive solution that allows easy access to a broad range of web resources and web-enabled applications using native HTTP over SSL (HTTPS) browser support. SSL VPN delivers three modes of SSL VPN access: clientless, thin-client, and full-tunnel client support.
See the “Example: SSL VPN Configuration” section for a sample SSL VPN gateway configuration.
For additional information about configuring SSL VPN, see the following link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_sslvpn/configuration/15-mt/sec-conn-sslvpn-15-mt-book/sec-conn-sslvpn-ssl-vpn.html
Example: SSL VPN Configuration
This configuration example shows the configuration for SSL VPN gateway using Cisco 800M Series ISR.
Configuring FlexVPN
FlexVPN is Cisco's implementation of the IKEv2 standard featuring a unified paradigm and CLI that combines site to site, remote access, hub and spoke topologies and partial meshes (spoke to spoke direct). FlexVPN offers a simple but modular framework that extensively uses the tunnel interface paradigm while remaining compatible with legacy VPN implementations using crypto maps.
See the “Example: FlexVPN Configuration” section for a sample FlexVPN hub and spoke configuration.
For additional information about configuring FlexVPN, see the following link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_ike2vpn/configuration/15-mt/sec-flex-vpn-15-mt-book/sec-intro-ikev2-flex.html
Example: FlexVPN Configuration
The following configuration example shows the configuration for FlexVPN hub and spoke deployment model. In this example, Cisco 800M series ISR is configured as a spoke and Cisco 3900 Series ISR is configured as the hub.
This configuration section shows the configuration of 800M Series ISR as a spoke.
This configuration section shows the configuration of 800M Series ISR as a spoke.
Configuring Zone-Based Policy Firewall
Zone-Based Policy Firewall (also known as Zone-Policy Firewall, or ZFW) changes the firewall configuration from the interface-based model to a more flexible, more easily understood zone-based model. Interfaces are assigned to zones, and inspection policy is applied to traffic moving between the zones. Inter-zone policies offer considerable flexibility and granularity, so different inspection policies can be applied to multiple host groups connected to the same router interface.
For more information about configuring zone-based policy firewall, see the following weblink:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_data_zbf/configuration/15-mt/sec-data-zbf-15-mt-book/sec-zone-pol-fw.html
Configuring VRF-Aware Cisco Firewall
VRF-Aware Cisco Firewall applies Cisco Firewall functionality to Virtual Routing and Forwarding (VRF) interfaces when the firewall is configured on a service provider (SP) or large enterprise edge device. SPs can provide managed services to small and medium business markets.
For more information about configuring VRF-aware Cisco Firewall, see the following web link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_data_zbf/configuration/15-mt/sec-data-zbf-15-mt-book/sec-cbac-vrf-fw.html
Configuring Subscription-Based Cisco IOS Content Filtering
The Subscription-based Cisco IOS Content Filtering feature interacts with the Trend Micro URL filtering service so that HTTP requests can be allowed or blocked, and logged, based on a content filtering policy. The content filtering policy specifies how to handle items such as web categories, reputations (or security ratings), trusted domains, untrusted domains, and keywords. URLs are cached on the router, so that subsequent requests for the same URL do not require a lookup request, thus improving performance.
For more information about configuring subscription-based Cisco IOS content filtering see the following web link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_data_zbf/configuration/15-mt/sec-data-zbf-15-mt-book/subscrip-cont-filter.html
Configuring On-Device Management for Security Features
The On-Device Management for Security Features provides an intuitive and simple management interface, the Cisco Configuration Professional Express, to deploy a variety of security features. You can deploy security features including zone-based firewalls, VPN, Intrusion Detection System (IDS) and URL filtering through the Cisco Configuration Professional Express.
The Cisco Configuration Professional Express uses existing zone-based firewall CLIs in conjunction with Network-Based Application Recognition 2 (NBAR2) CLIs to determine the application category, and position NBAR2 protocols supported by the firewall into the relevant application category.
Fro more information about enabling NBAR2 for zone-based firewalls, see the following web link:
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_data_zbf/configuration/15-mt/sec-data-zbf-15-mt-book/on-device-mgmt.html
 Feedback
Feedback