What Are Converged Access Workflows?
The Converged Access workflow simplifies, automates and optimizes deployment of various enterprise-class next generation wireless deployment models for campus and branch networks. Cisco Prime Infrastructurecan automate the converged access deployment of wireless networks using converged access components such as Catalyst 3650, 3850, 4500 SUP 8-E switches, and Cisco 5760 Wireless LAN controller (WLC). The catalyst switches can be deployed as Mobility Agent (MA), Mobility Controller (MC), and Guest Anchor controller (GA).
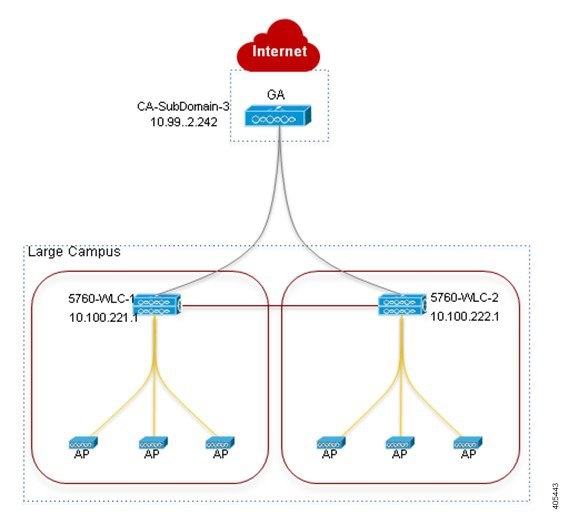
The following figure illustrates the wireless converged access deployment mode.
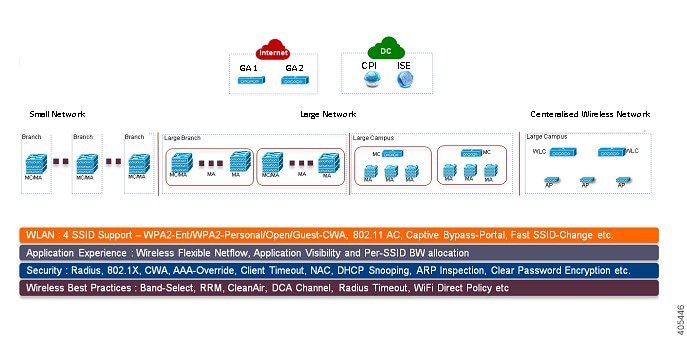
Single-Switch Small Network Deployment Model
This deployment model assumes single Catalyst 3650, 3850 or 4500 SUP 8-E switch deployed in Access layer in combined MA and MC roles. The Catalyst switches can be deployed in individual standalone system mode or in stackwise redundant supervisor mode.
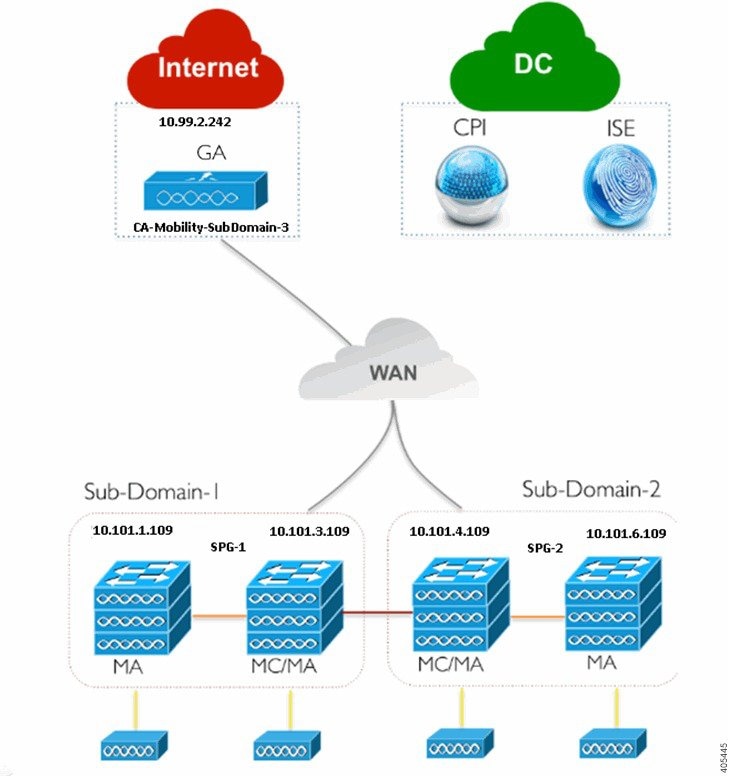
Controller-Less Single/Multi-Domain Deployment Model
This deployment model consists of multiple sub-domains and allows inter-domain MC peering for end-to-end seamless roaming across sub-domains. The MA switches are deployed in Access layer while the MC switches can be placed in Distribution layer.
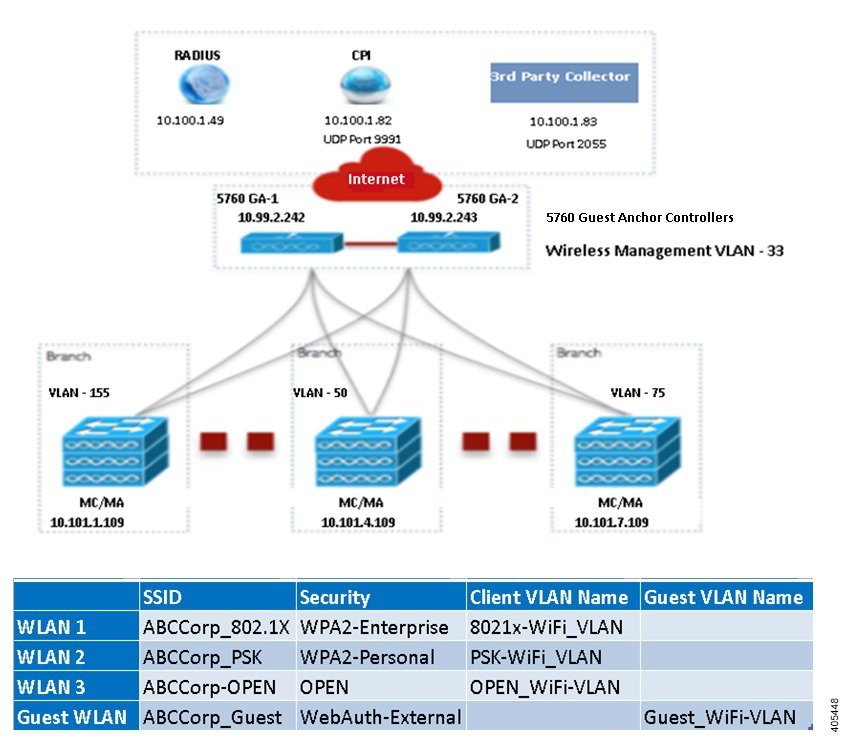
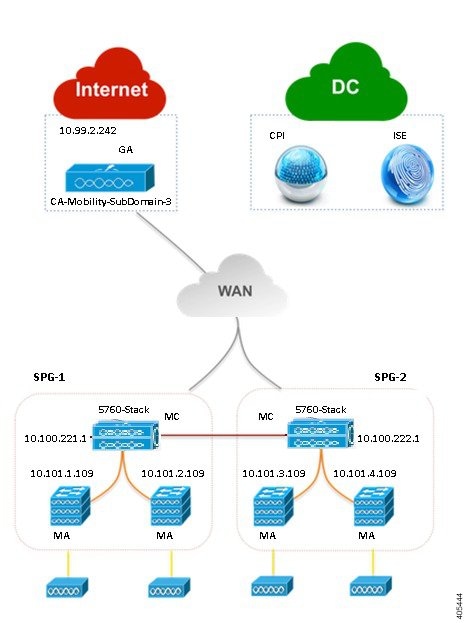
Controller-Based Single/Multi-Domain Deployment Model
A large scale converged access campus building is deployed with external 5760 WLC as MC. The Access layer switches are deployed as MA across multiple buildings with centralized 5760 MC. In such large network, multiple 5760 WLCs may co-exist for better load balancing and redundancy. Depending on the roaming requirement across different buildings, the inter-domain mobility peering between 5760 WLCs can be established.
Centralized Wireless Campus Deployment Model
In this deployment model, the switches in Access layer remain in traditional switching mode and wireless communication between Access Point (AP) and WLC is built as overlay network. In large scale campus deployments, multiple 5760 WLCs can be deployed for better load balancing and redundancy. To provide seamless large mobility domains, the inter-domain mobility peering 5760 WLCs can be established.
Key Benefits
- Simple Automated Deployment—Simplifies the converged access deployment by automating the device configuration process. Requires only a few deployment specific inputs from the network administrator and pushes the complete converged access configurations to the network devices.
- Error Free Deployment—The template-based configuration used by Cisco Prime Infrastructure avoids manual misconfigurations, making it easier to build/maintain enterprise-wide standardized configurations that are well understood by the network administrator.
- Optimized Deployment—The configuration templates used by Cisco Prime Infrastructure incorporates a large number of Cisco best practice guidelines, improving the deployment quality. Some of the best practice wireless technologies/features that are automatically included in the template are Band-Select, Radio Resource Management (RRM), Fast SSID-Change, CleanAir, and Wireless QoS.
- High Scalability—Supports large enterprises with thousands of branches. It not only reduces efforts to deploy greenfield branches, but also simplifies large scale conversion of traditional Ethernet based branch networks to converged access branches in an error-free way.

 Feedback
Feedback