|
Data Center
|
VMware. See Installation Requirements in VMware vCenter.
Amazon EC2. See Installation Requirements in AWS EC2.
|
|
Interfaces
|
Minimum: 1
Maximum: 3
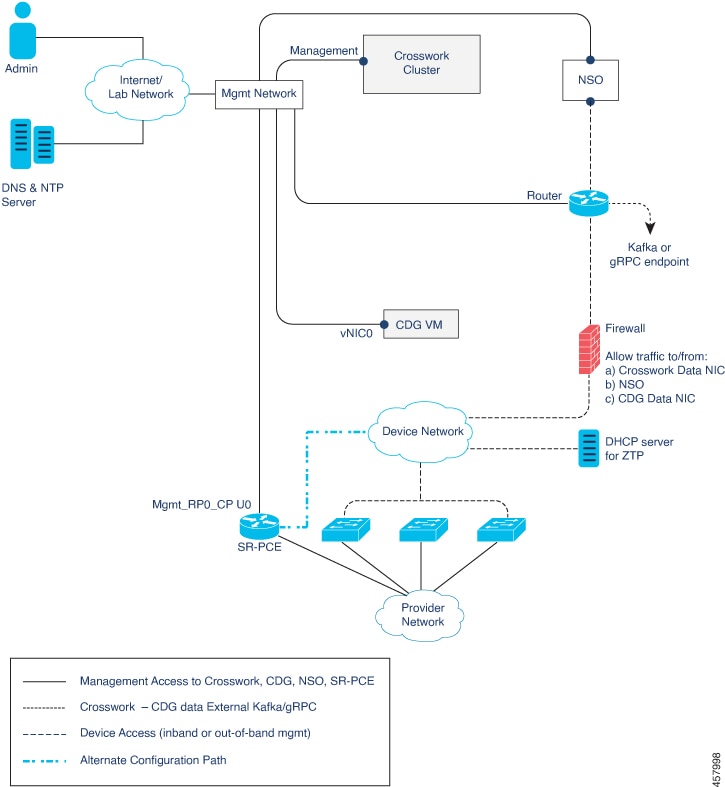
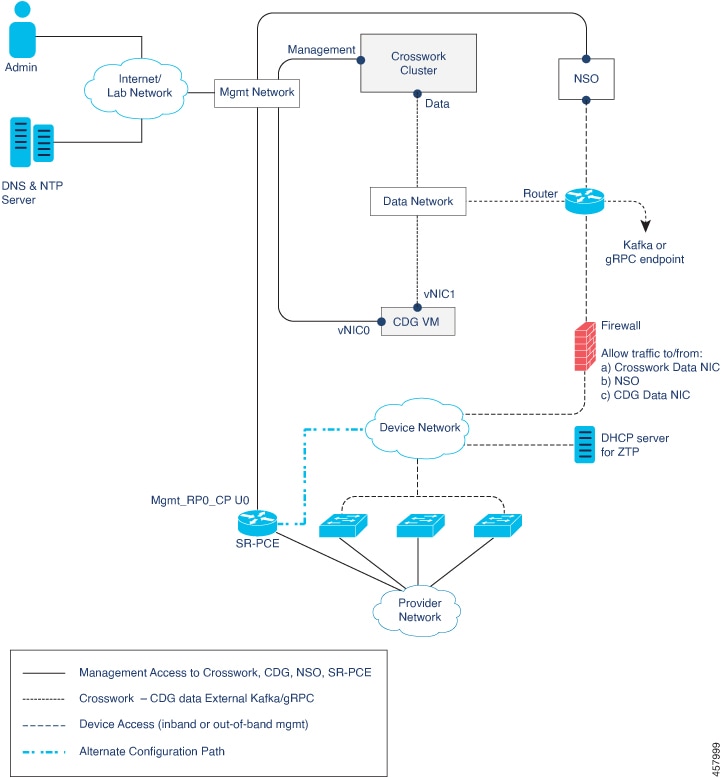
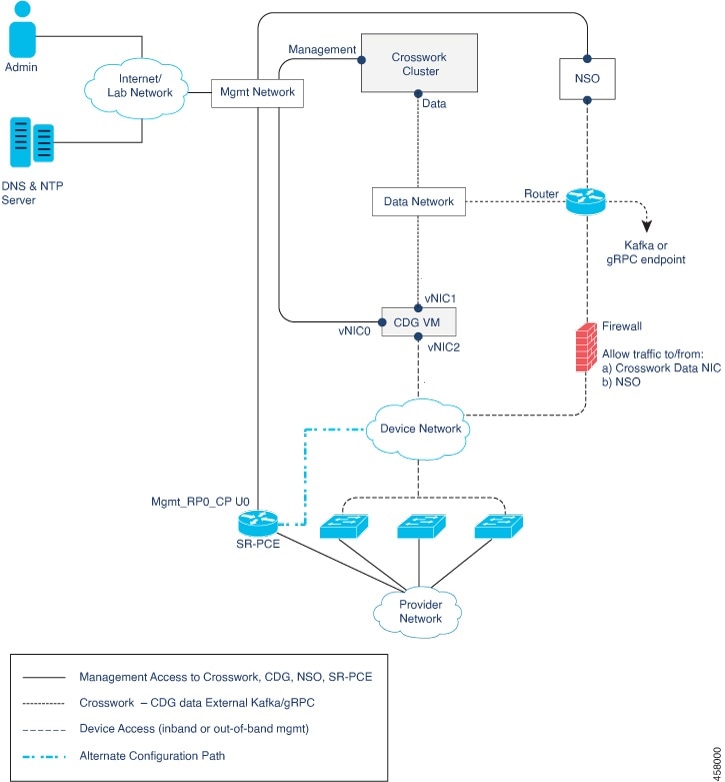
Cisco Crosswork Data Gateway can be deployed with either 1, 2, or 3 interfaces as per the combinations below:
|
Note
|
If you use one interface on your Crosswork cluster, you must use only one interface on the Crosswork Data Gateway. If you
use two interfaces on your Crosswork Cluster, then you can use two or three interfaces on the Crosswork Data Gateway as per
your network requirements.
|
|
|
No. of NICs
|
vNIC0
|
vNIC1
|
vNIC2
|
| 1 |
-
Management Traffic
-
Control/Data Traffic
-
Device Access Traffic
|
—
|
—
|
| 2 |
|
-
Control/Data Traffic
-
Device Access Traffic
|
—
|
| 3 |
|
|
|
-
Management traffic: for accessing the Interactive Console and passing the Control/Data information between servers (for example,
a Crosswork application to Crosswork Data Gateway).
-
Control/Data traffic: for data and configuration transfer between Cisco Crosswork Data Gateway and Crosswork applications and other external data destinations.
-
Device access traffic: for device access and data collection.
|
Note
|
Due to security policies, traffic from subnets of a vNIC received on other vNICs is dropped. For example, in a 3 vNIC model
setup, all device traffic (incoming and outgoing) must be routed through vNIC2. Crosswork Data Gateway drops device traffic
received over vNIC0 and vNIC1.
|
|
|
IP Addresses
|
1 or 2 IPv4 or IPv6 addresses based on the number of interfaces you choose to use. Including one additional IP address to
be used as the Virtual IP (VIP) address. For more information, refer to the Interfaces section in the Table 1 table.
|
Note
|
Crosswork does not support dual stack configurations. Therefore, ALL addresses for the environment must be either IPv4 or
IPv6.
In a 3- NIC deployment, you will need to provide an IP address for Management interface (vNIC0) and Control/Data interface
(vNIC1) only during installation. A virtual IP address for Device Access Traffic (vNIC2) is assigned when you create a Crosswork
Data Gateway pool as explained in the Section: Create a Crosswork Data Gateway Pool in the Cisco Crosswork Infrastructure 4.4 and Applications Administration Guide.
|
|
|
NTP Servers
|
The IPv4 or IPv6 addresses or host names of the NTP servers you plan to use. If you want to enter multiple NTP servers, separate
them with spaces. These should be the same NTP servers you use to synchronize devices, clients, and servers across your network.
Verify that the NTP IP address or host name is reachable on the network or installation will fail.
Also, the ESXi hosts that will run the Crosswork application and Cisco Crosswork Data Gateway VM must have NTP configured, or the initial handshake may fail with "certificate not valid" errors.
|
|
DNS Servers
|
The IPv4 or IPv6 addresses of the DNS servers you plan to use. These should be the same DNS servers you use to resolve host
names across your network. Confirm that the DNS servers are reachable on the network before attempting installation. The installation
will fail if the servers cannot be reached.
|
|
DNS Search Domain
|
The search domain you want to use with the DNS servers, for example, cisco.com. You can have only one search domain.
|
| (optional) Proxy Server |
URL of an optional management network proxy server if your environment.
If your environment requires an HTTP or HTTPS proxy in order to access URLs on the public Internet, you must configure a proxy
server in order for the Cisco Crosswork Data Gateway to successfully connect to Cisco Crosswork
|
|
(optional) Syslog Sever
|
The hostname or IPv4 or IPv6 address of an external syslog server.
|
|
(optional) Auditd Server
|
The hostname or IPv4 or IPv6 address of an external auditd server.
|

 Feedback
Feedback