Cisco Crosswork Data Gateway Installation Workflow
Cisco Crosswork Data Gateway is installed as a VM called Base VM (containing only enough software to register itself with Cisco Crosswork). Use this procedure to install the first Cisco Crosswork Data Gateway VM or for adding additional Cisco Crosswork Data Gateway VMs.
 Note |
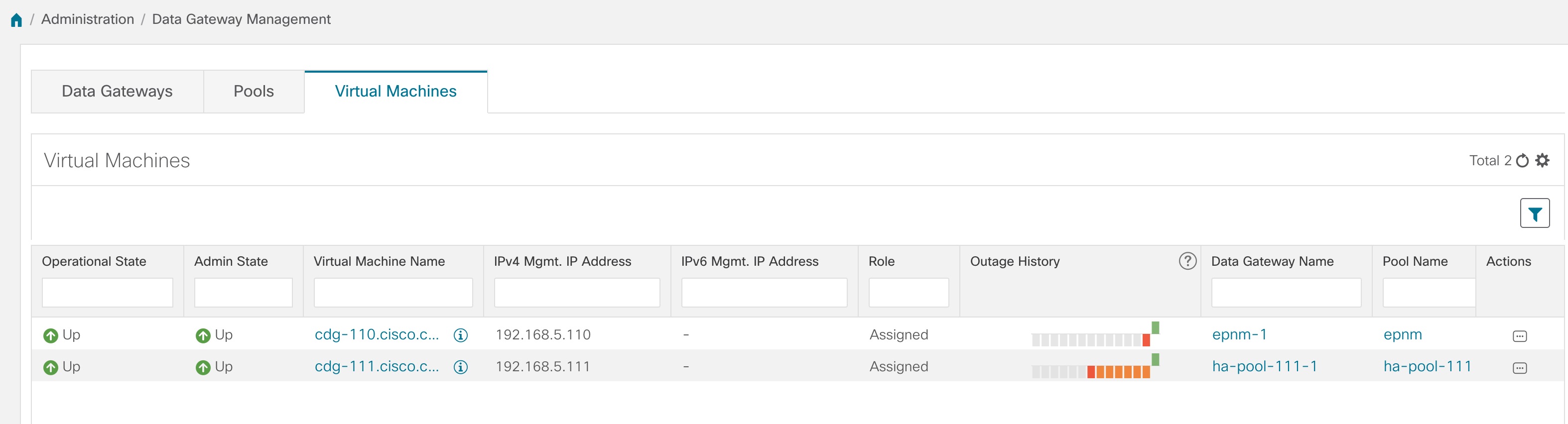
If you are redeploying the same Cisco Crosswork Data Gateway with Cisco Crosswork, delete the previous Crosswork Data Gateway entry from the Virtual Machine table under Data Gateway Management. For information on how to delete a Crosswork Data Gateway VM, see Delete Crosswork Data Gateway VM from Cisco Crosswork. |
To install Crosswork Data Gateway VM for use with Cisco Crosswork, follow these steps:
-
Choose the deployment profile for the Crosswork Data Gateway VM. See Crosswork Data Gateway VM Requirements.
-
Install Cisco Crosswork Data Gateway on your preferred platform:
Table 1. Crosswork Data Gateway installation options VMware
Install Cisco Crosswork Data Gateway Using vCenter vSphere Client
Amazon EC2
-
Complete the post-installation tasks mentioned in the section Crosswork Data Gateway Post-installation Tasks
-
Verify that the Crosswork Data Gateway VM has enrolled successfully with Cisco Crosswork. See Cisco Crosswork Data Gateway Authentication and Enrollment.
After verifying that the Crosswork Data Gateway VM has enrolled successfully with Cisco Crosswork, set up the Crosswork Data Gateway for collection by creating a Crosswork Data Gateway pool. See Section: Create a Crosswork Data Gateway Pool in the Cisco Crosswork Infrastructure 4.4 and Applications Administration Guide.
 Note |
If you plan to install multiple Cisco Crosswork Data Gateway VMs due to load or scale requirements or you wish to leverage Cisco Data Gateway High Availability, we recommend that you install all the Crosswork Data Gateway VMs first and then proceed with adding them to a Data Gateway pool. |
Cisco Crosswork Data Gateway Parameters and Deployment Scenarios
Before you begin installing the Crosswork Data Gateway, go through this section to read about the deployment parameters and possible deployment scenarios.
Crosswork Data Gateway supports either IPv4 or IPv6 addresses for all interfaces. Cisco Crosswork does not support dual stack configurations. Therefore, plan ALL addresses for the environment as either IPv4 or IPv6.
During installation, Cisco Crosswork Data Gateway creates two user accounts:
-
Cisco Crosswork Data Gateway administrator, with the username, dg-admin and the password set during installation. The administrator uses this ID to log in and troubleshoot Cisco Crosswork Data Gateway.
-
Cisco Crosswork Data Gateway operator, with the username, dg-oper and the password set during installation. The dg-oper user has permissions to perform all ‘read’ operations and limited ‘action’ commands.
To know what operations an admin and operator can perform, see Section Supported User Roles in the Cisco Crosswork Infrastructure 4.4 and Applications Administration Guide.
The dg-admin and dg-oper user accounts are reserved usernames and cannot be changed. You can change the password in the console for both the accounts. See Section Change Passphrase Cisco Crosswork Infrastructure 4.4 and Applications Administration Guide. In case of lost or forgotten passwords, destroy the current VM, you have to create a new VM, and reenroll the new VM with Cisco Crosswork.
In the following table:
* Denotes the mandatory parameters. Parameters without this mark are optional. You can choose them based on your deployment scenario. Deployment scenarios are explained (wherever applicable) in the Additional Information column.
** Denotes parameters that you can enter during install or address later using additional procedures.
|
Name |
Parameter |
Description |
Additional Information |
||
|---|---|---|---|---|---|
|
Host Information |
|||||
|
Hostname* |
Hostname |
Name of the Cisco Crosswork Data Gateway VM specified as a fully qualified domain name (FQDN).
|
|||
|
Description* |
Description |
A detailed description of the Cisco Crosswork Data Gateway. |
|||
|
Label |
Label |
Label used by Cisco Crosswork to categorize and group multiple Cisco Crosswork Data Gateway VMs. |
|||
|
Deployment |
|
Parameter that conveys the type of controller application that CDG is deployed with. For an on-premise installation, choose either:
onpremise-standard.
|
You need to specify this value for OVF tool installation. |
||
|
Active vNICs* |
ActiveVnics |
Number of vNICs to use for sending traffic. The default number of interfaces for the deployment options—Standard, Standard Plus, and Extended are 3. |
You can choose to use either 1, 2, or 3 vNICs as per the following combinations:
|
||
|
AllowRFC8190* |
AllowRFC8190 |
Choose how to validate interface addresses that fall in a usable RFC 8190 range. Options are The default value is |
|||
|
Private Key URI |
DGCertKey |
SCP URI to private key file for session key signing. You can retrieve this using SCP ( |
Cisco Crosswork uses self-signed certificates for handshake with Cisco Crosswork Data Gateway. These certificates are generated at installation. However, if you want to use third party or your own certificate files, then enter these parameters. Certificate chains override any preset or generated certificates in the Cisco Crosswork Data Gateway VM and are given as an SCP URI (user:host:/path/to/file).
|
||
|
Certificate File and Key Passphrase |
DGCertChainPwd |
Passphrase of SCP user to retrieve the Cisco Crosswork Data Gateway PEM formatted certificate file and private key. |
|||
|
Data Disk Size |
DGAppdataDisk |
Size in GB of a second data disk. Default value of this parameter in each profile is:
|
|||
|
AwsIamRole |
|
AWS IAM role name for EC2 installation. |
A role created in Identity and Access Management (IAM) in the AWS environment with relevant permissions. |
||
|
Passphrase |
|||||
|
dg-admin Passphrase* |
dg-adminPassword |
The password you have chosen for the dg-admin user. Password must be 8-64 characters. |
|||
|
dg-oper Passphrase* |
dg-operPassword |
The password you have chosen for the dg-oper user. Password must be 8-64 characters. |
|||
|
Interfaces In a 3-NIC deployment, you need to provide IP address for Management Traffic (vNIC0) and Control/Data Traffic (vNIC1) only. IP address for Device Access Traffic (vNIC2) is assigned during Crosswork Data Gateway pool creation as explained in the Section: Create a Crosswork Data Gateway Pool in the Cisco Crosswork Infrastructure 4.4 and Applications Administration Guide.
|
|||||
|
vNIC IPv4 Address |
|||||
|
vNIC IPv4 Method* For example, the parameter name for vNIC0 is vNIC0 IPv4 Method. |
|
Method in which the interface is assigned an IPv4 address - The default value is |
If you have selected Method as:
|
||
|
vNIC IPv4 Address |
|
IPv4 address of the interface. |
|||
|
vNIC IPv4 Netmask |
|
IPv4 netmask of the interface in dotted quad format. |
|||
|
vNIC IPv4 Skip Gateway |
|
The default value is Setting this to |
|||
|
vNIC IPv4 Gateway |
|
IPv4 address of the vNIC gateway. |
|||
|
vNIC IPv6 Address |
|||||
|
vNIC IPv6 Method* |
|
Method in which the vNIC interface is assigned an IPv6 address - The default value is |
If you have selected Method as:
|
||
|
vNIC IPv6 Address |
|
IPv6 address of the interface. |
|||
|
vNIC IPv6 Netmask |
|
IPv6 prefix of the interface. |
|||
|
vNIC IPv6 Skip Gateway |
|
Options are Selecting |
|||
|
vNIC IPv6 Gateway |
|
IPv6 address of the vNIC gateway. |
|||
|
DNS Servers |
|||||
|
DNS Address* |
DNS |
Space delimited list of IPv4 or IPv6 addresses of the DNS servers accessible from the management interface. |
|||
|
DNS Search Domain* |
Domain |
DNS search domain |
|||
|
DNS Security Extensions * |
DNSSEC |
Options are The default value is Select |
|||
|
DNS over TLS* |
DNSTLS |
Options are The default value is Select |
|||
|
Multicast DNS* |
mDNS |
Options are The default value is |
If you choose Resolve, only resolution support is enabled. Responding is disabled. |
||
|
Link-Local Multicast Name Resolution* |
LLMNR |
Options are The default value is Select |
If you choose Resolve, only resolution support is enabled. Responding is disabled. |
||
|
NTPv4 Servers |
|||||
|
NTPv4 Servers* |
NTP |
Space-delimited list of IPv4, IPv6 addresses, or hostnames of the NTPv4 servers accessible in the management interface. |
You must enter a value here, such as pool.ntp.org. NTP server is critical for time synchronization between Crosswork Data Gateway VM, Crosswork, and devices. Using a nonfunctional or dummy address may cause issues when Cisco Crosswork and Crosswork Data Gateway try to communicate with each other. If you are not using an NTP server, ensure that time gap between Crosswork Data Gateway and Crosswork is not more than 10 minutes. Else, Crosswork Data Gateway fails to connect. |
||
|
Use NTPv4 Authentication |
NTPAuth |
Select The default value is |
|||
|
NTPv4 Keys |
NTPKey |
Key IDs to map to the server list. Enter space-delimited list of Key IDs. |
|||
|
NTPv4 Key File URI |
NTPKeyFile |
SCP URI to the chrony key file. |
|||
|
NTPv4 Key File Passphrase |
NTPKeyFilePwd |
Password of SCP URI to the chrony key file. |
|||
|
Remote Syslog Server |
|||||
| Use Remote Syslog Server* | UseRemoteSyslog |
Options are True and False. Select True to send syslog messages to a remote host.The default value is |
Configuring an external syslog server sends service events (CLI/MDT/SNMP/gNMI) to the external syslog server. Otherwise, they are logged only to the Cisco Crosswork Data Gateway VM. If you want to use an external syslog server, specify the following settings:
|
||
|
Syslog Server Address |
|
Hostname, IPv4, or IPv6 address of a syslog server accessible in the management interface.
|
|||
|
Syslog Server Port |
SyslogPort |
Port number of the syslog server. The default port number is 514. |
|||
|
Syslog Server Protocol |
SyslogProtocol |
Options are The default value is |
|||
|
Use Syslog over TLS? |
SyslogTLS |
Select The default value is |
|||
|
Syslog TLS Peer Name |
SyslogPeerName |
Syslog server hostname exactly as entered in the server certificate SubjectAltName or subject common name. |
|||
|
Syslog Root Certificate File URI |
|
PEM formatted root cert of syslog server retrieved using SCP. |
|||
|
Syslog Certificate File Passphrase |
|
Password of SCP user to retrieve Syslog certificate chain. |
|||
|
Remote Auditd Server |
|||||
|
Use Remote Auditd Server* |
UseRemoteAuditd |
Options are True and False. The default value is False.. Select True to send auditd messages to a remote host. |
If desired, you can configure an external remote auditd server to send Cisco Crosswork Data Gateway VM change audit notifications. Specify these three settings to use an external Auditd server. |
||
|
Auditd Server Address |
AuditdAddress |
Hostname, IPv4, or IPv6 address of an optional Auditd server. |
|||
|
Auditd Server Port |
AuditdPort |
Port number of an optional Auditd server. The default port is 60. |
|||
|
Controller and Proxy Settings |
|||||
|
Crosswork Controller IP* |
ControllerIP |
The Virtual IP address or the hostname of Cisco Crosswork Cluster.
|
This is required if you are providing a controller signing certificate file URI. |
||
|
Crosswork Controller Port* |
ControllerPort |
Port of the Cisco Crosswork controller. The default port is 30607. |
|||
|
Controller Signing Certificate File URI* |
ControllerSignCertChain |
PEM formatted root cert of Cisco Crosswork to validate signing certs retrieved using SCP. Cisco Crosswork generates the PEM file and is available at the following location:
|
Crosswork Data Gateway requires the Controller Signing Certificate File to enroll automatically with Cisco Crosswork. If you specify these parameters during the installation, the certificate file is imported once Crosswork Data Gateway boots up for the first time. If you do not specify these parameters during installation, then import the certificate file manually by following the procedure Import Controller Signing Certificate File. |
||
|
Controller SSL/TLS Certificate File URI |
ControllerTlsCertChain |
Cisco Crosswork Controller PEM formatted SSL/TLS certificate file retrieved using SCP. |
|||
|
Controller Certificate File Passphrase* |
ControllerCertChainPwd |
Password of SCP user (cw-admin) to retrieve Cisco Crosswork certificate chain. |
|||
|
Proxy Server URL |
|
URL of the HTTP proxy server.
|
Crosswork Data Gateway must connect to the Internet via TLS, and a proxy server may be required if it is not present in your environment. If you want to use a proxy server, specify these parameters. |
||
|
Proxy Server Bypass List |
ProxyBypass |
Comma-delimited list of addresses and hostnames that will not use the proxy server.
|
|||
|
Authenticated Proxy Username |
ProxyUsername |
Username for authenticated proxy servers.
|
|||
|
Authenticated Proxy Passphrase |
ProxyPassphrase |
Passphrase for authenticated proxy servers.
|
|||
|
HTTPS Proxy SSL/TLS Certificate File URI |
ProxyCertChain |
HTTPS proxy PEM formatted SSL/TLS certificate file retrieved using SCP.
|
|||
|
HTTPS Proxy SSL/TLS Certificate File Passphrase |
ProxyCertChainPwd |
Password of SCP user to retrieve proxy certificate chain.
|
|||
 Note |
If you are not using the default SCP port 22, you can specify the port as a part of the SCP command. For example, Where 55 is a custom port. |
Install Cisco Crosswork Data Gateway Using vCenter vSphere Client
 Note |
We have included sample images of Cisco Crosswork Data Gateway on-premise Standard deployment in the procedure. |
Procedure
|
Step 1 |
Download the Cisco Crosswork Data Gateway 4.1 image file from cisco.com (*.ova).
|
||
|
Step 2 |
Connect to vCenter vSphere Client. Then select Actions > Deploy OVF Template |
||
|
Step 3 |
The VMware Deploy OVF Template wizard appears and highlights the first step, 1 Select template. |
||
|
Step 4 |
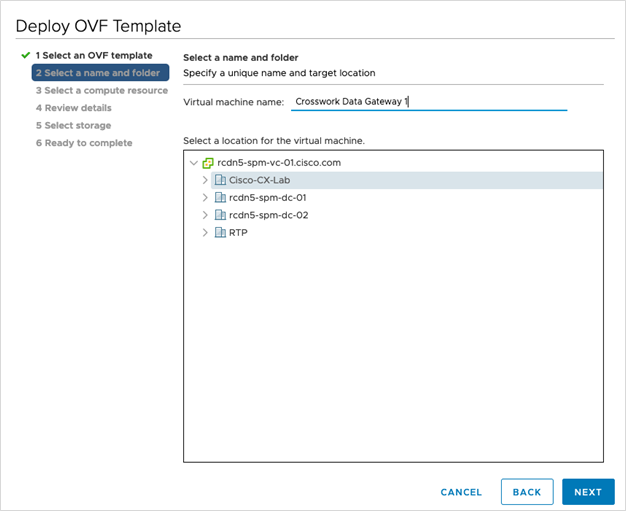
Click Next to go to 2 Select name and location, as shown in the following figure. |
||
|
Step 5 |
Click Next to go to 3 Select a resource. Choose the VM’s host. |
||
|
Step 6 |
Click Next. The VMware vCenter Server validates the OVA. Network speed will determine how long validation takes. When the validation is complete, the wizard moves to 4 Review details. Review the OVA’s information and then click Next. Take a moment to review the OVF template you are deploying.
|
||
|
Step 7 |
Click Next to go to 5 accept license agreements. Review the End User License Agreement and click Accept. |
||
|
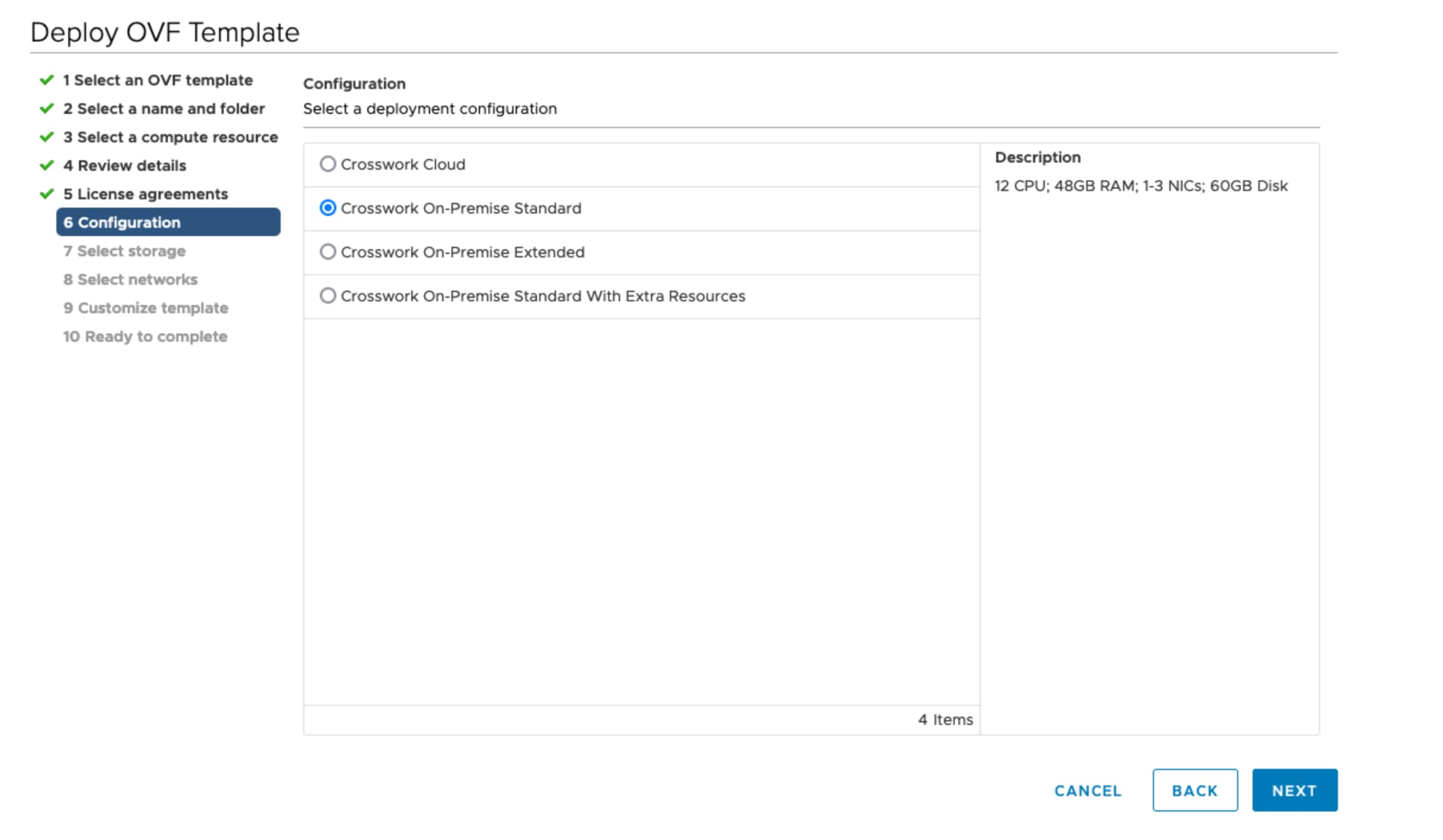
Step 8 |
Click Next to go to 6 Select configuration, as shown in the following figure. Select the type of configuration from Crosswork On-Premise Standard and Crosswork On-Premise Extended. See Mandatory deployment type for Crosswork Data Gateway for more information.
 |
||
|
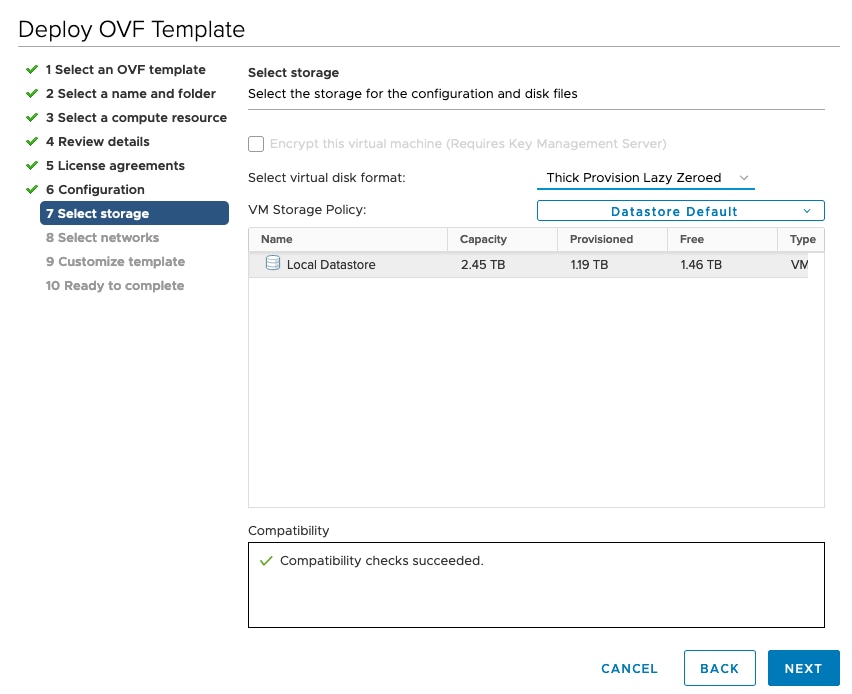
Step 9 |
Click Next to go to 7 Select storage, as shown in the following figure.
|
||
|
Step 10 |
Click Next to go to 8 Select networks, as shown in the following figure. In the drop-down table at the top of the page, choose the appropriate destination network for each source network, vNIC2, vNIC1, and vNIC0 respectively.
|
||
|
Step 11 |
Click Next to go to 9 Customize template, with the Host Information Settings already expanded. Enter the information for the parameters as explained in Table: Table 1. 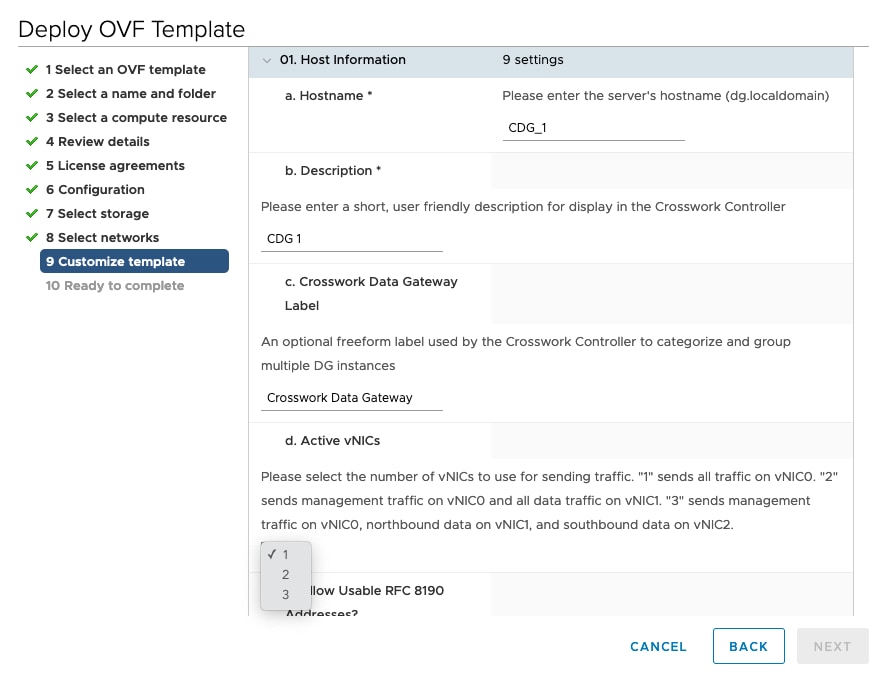 |
||
|
Step 12 |
Click Next to go to 10 Ready to complete. Review your settings and then click Finish if you are ready to begin deployment. |
||
|
Step 13 |
Wait for the deployment to finish before continuing. To check the deployment status:
Wait for the deployment status to become 100%. You can now proceed to power on the VM. |
||
|
Step 14 |
Once the deployment status is 100%, power on the VM to complete the deployment process. Expand the host’s entry so you can click the VM and then choose Actions > Power > Power On, as shown in the following figure: 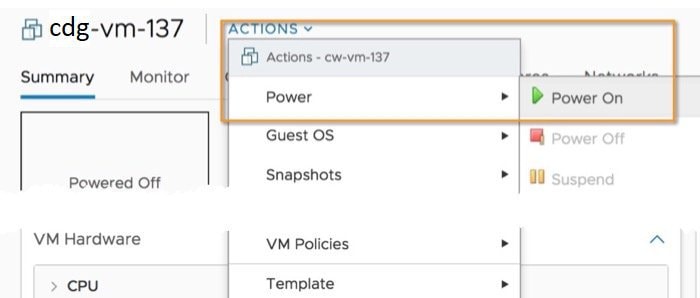 Wait for at least 5 minutes for the VM to come up and then log in via vCenter or SSH as explained below.
|
What to do next
Log in to Cisco Crosswork Data Gateway VM Via vCenter:
-
Locate the VM in vCenter and then right click and select Open Console.
-
Enter user name (
dg-adminordg-operas per the role assigned to you) and the corresponding password (the one that you created during installation process) and press Enter.
After you log in, the Crosswork Data Gateway should present you with the welcome screen and options menu indicating that the installation completed successfully. Log out and proceed with the post-installation tasks explained in the next section.
Install Cisco Crosswork Data Gateway Via OVF Tool
You can modify the list of mandatory and optional parameters in the command/script as per your requirement and run the OVF Tool. Refer to the Table: Table 1 for the list of installation parameters and their default values.
 Note |
Ensure that you specify all the required mandatory and optional parameters with the desired values when you build the script. Parameters that are not included in the script will be considered with their default values for deployment. |
Below is a sample if you plan to run the OVF tool with a script:
#!/usr/bin/env bash
VM_NAME='VM_NAME'
DM='thin'
DS='Datastore name'
Vcenter='Vcenter IP'
Host='Vcenter Host IP'
DC='DC Name'
CwIpv4Mgmt='CW IP'
ManagementIPv4Address='CDG IP'
ManagementIPv4Netmask='Netmask address'
ManagementIPv4Gateway='Management Gateway IP'
NorthDataIPv4Address='Northbound IP'
NorthDataIPv4Netmask='Netmask address'
NorthDataIPv4Gateway='Data Gateway IP'
DNSv4='DNS IP'
NTP='NTP FQDN'
Domain='Domain name'
CtrlerCertChainPwd='Controller Password'
DgAdminPwd='Admin user password'
DgOperPwd='Oper user password'
CdgDomain='CDG hostname'
MgmtNetwork='Standard Network'
SouthDataNetwork='Southbound port group name'
NorthDataNetwork='Northbound port group name'
DeploymentOption='Deployment Option'
VcenterUser='Vcenter username'
VcenterPwd='Vcenter password'
ImageFilePath='CDG Image Path'
ovftool --version
ovftool --acceptAllEulas --skipManifestCheck --X:injectOvfEnv --overwrite --powerOffTarget --powerOn --noSSLVerify --allowExtraConfig \
-ds=$DS \
--deploymentOption="${DeploymentOption}" \
--diskMode=$DM \
--name="${VM_NAME}" \
--prop:"ControllerIP=${CwIpv4Mgmt}" \
--prop:"ControllerPort=30607" \
--prop:"ControllerSignCertChain=cw-admin@${CwIpv4Mgmt}:/home/cw-admin/controller.pem" \
--prop:"ControllerCertChainPwd=${CtrlerCertChainPwd}" \
--prop:"Hostname=${CdgDomain}" \
--prop:"Description=CDG Base VM for Automation" \
--prop:"Vnic0IPv4Method=Static" \
--prop:"Vnic0IPv4Address=${ManagementIPv4Address}" \
--prop:"Vnic0IPv4Netmask=${ManagementIPv4Netmask}" \
--prop:"Vnic0IPv4Gateway=${ManagementIPv4Gateway}" \
--prop:"Vnic1IPv4Method=Static" \
--prop:"Vnic1IPv4Address=${NorthDataIPv4Address}" \
--prop:"Vnic1IPv4Netmask=${NorthDataIPv4Netmask}" \
--prop:"Vnic1IPv4Gateway=${NorthDataIPv4Gateway}" \
--prop:"dg-adminPassword=${DgAdminPwd}" \
--prop:"dg-operPassword=${DgOperPwd}" \
--prop:"DNS=${DNSv4}" \
--prop:"NTP=${NTP}" \
--prop:"Domain=${Domain}" \
--net:"vNIC0=${MgmtNetwork}" \
--net:"vNIC1=${NorthDataNetwork}" \
--net:"vNIC2=${SouthDataNetwork}" \
$ImageFilePath \
vi://$VcenterUser:$VcenterPwd@$Vcenter/$DC/host/$HostProcedure
|
Step 1 |
Open a command prompt. |
|
Step 2 |
Navigate to the location where you installed the OVF Tool. |
|
Step 3 |
Install the VM by executing the script that you created containing the command and arguments. For example, |
Once the VM powers up, log into the VM. See Login into Crosswork Data Gateway VM. After you log in, the Crosswork Data Gateway should present you with the welcome screen and options menu indicating that the installation completed successfully. Log out and proceed with the post-installation tasks explained in the next section.
Install Crosswork Data Gateway on Amazon EC2
You can install the Crosswork Data Gateway on Amazon EC2 in one of the following ways:
Install Crosswork Data Gateway on Amazon EC2 using CloudFormation Template
Installing Crosswork Data Gateway on EC2 using CloudFormation (CF) templates involves creating a template (YAML formatted text file) which describes the VM resources and their properties. Whenever you create a stack, CloudFormation provisions the resources that are described in your template and installs the VMs.
A sample CF template is attached here for your reference.
Before you begin
-
Ensure that you have met the requirements specified in the section AWS EC2 Settings.
-
All the Cisco Crosswork VMs have been installed.
Procedure
|
Step 1 |
Log in to AWS and search for the CloudFormation service. The CloudFormation dashboard opens. |
||
|
Step 2 |
Click Stacks from the side menu. All existing stacks in the environment are displayed here. |
||
|
Step 3 |
In Step 1 - Specify template, select the following settings:
|
||
|
Step 4 |
In Step 2 - Specify stack details, enter relevant values for the stack name and each parameter field, and click Next.
|
||
|
Step 5 |
In Step 3 - Configure stack options, enter the relevant values for the settings based on your production preferences. Click Next to continue. |
||
|
Step 6 |
In Step 4 - Review, review the settings you have configured. |
||
|
Step 7 |
Select the acknowledgment checkbox, and click Create stack to start the VM installation. |
-
In the CloudFormation dashboard, click Stacks from the side menu to view the list of stacks.
-
Select the stack you installed. The stack details are displayed on the right. Click on each tab in this window to view details of the stack creation.
The status of the stack in the Events tab will be CREATE_IN_PROGRESS
-
After the stack has been created:
-
The status of the stack changes to CREATE_COMPLETE and the Logical ID displays the stack name.
-
The Resources tab displays details of the all the resources that the CF template has created, including the physical IDs.
-
The Output tab has details of the VM's interface IP addresses.
-
-
Click the Physical ID of the VM instance in your stack.
Doing this will open the Instances window in the EC2 dashboard with details of the selected VM instance.
-
Click Connect (top right corner).
-
In the Connect to instance window that appears, click the EC2 Serial Control tab and click Connect.
-
Click on the EC2 serial console tab. Click Connect to connect to the console of the VM.
-
Log in to the VM as a
dg-adminordg-operuser using the password you configured.The Interactive Console of the VM is displayed on successful login.
Install Crosswork Data Gateway on Amazon EC2 Manually
Follow these steps to install Crosswork Data Gateway on EC2.
 Note |
|
Before you begin
Ensure that you have the following information ready before deploying the Crosswork Data Gateway VMs :
-
Ensure that you have met the requirements specified in AWS EC2 Settings.
-
All the Cisco Crosswork VMs have been installed.
-
Decide the number of Crosswork Data Gateway VM instances to install.
-
Have the Crosswork Data Gateway AMI image saved in a location accessible to your AWS.
Procedure
|
Step 1 |
Prepare the user data for the Crosswork Data Gateway VMs. |
|
Step 2 |
Install the Crosswork Data Gateway VM. |
|
Step 3 |
Click Launch Instance. AWS EC2 initiates the installation of the VM. |
|
Step 4 |
Repeat steps 2 to 4 to install the remaining VMs. |
-
In the EC2 dashboard, click Instances from the menu on the left to view the VMs that were deployed. You can search for the VMs using the name, attributes or tags.
Wait for about 20 minutes for the VMs to be deployed.
-
After the VMs are launched successfully, they have the Instance State as Running.
-
To verify that the VMs were installed successfully, select a VM and click Connect (top right corner).
-
In the Connect to instance window that appears, click the EC2 Serial Control tab and click Connect.
-
Log in to the VM as a
dg-adminordg-operuser using the password you configured in the user data.The Interactive Console of the VM is displayed on successful login.
 Feedback
Feedback