Why network security matters
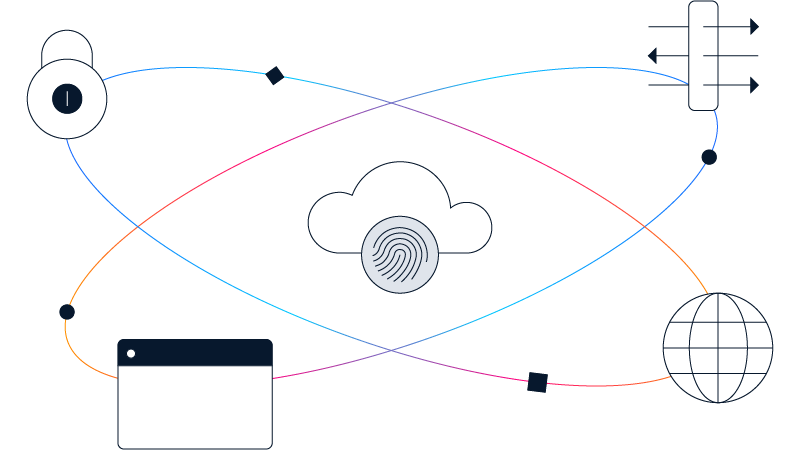
Enterprise networks support critical business operations and connect users, devices, applications, and data across on-premises infrastructure, cloud environments, and remote locations. At the same time, threat activity continues to evolve, and attackers increasingly target the network layer to move laterally, disrupt services, or exfiltrate data.
Network security plays a central role in three areas:
- Threat and risk prevention, by reducing exposure and limiting the impact of attacks
- Compliance and governance, by enforcing access controls, monitoring activity, and supporting audit requirements
- Operational resilience, by helping organizations maintain availability and recover quickly during incidents
Together, these outcomes allow organizations to operate securely while meeting regulatory obligations and business performance expectations.