Security operations simplified
Disrupt sophisticated threats with network-led defense
Instantly verify threats and execute tailored investigation plans with agentic AI across network, endpoint, email, cloud, and identity—powered by built‑in network detection.
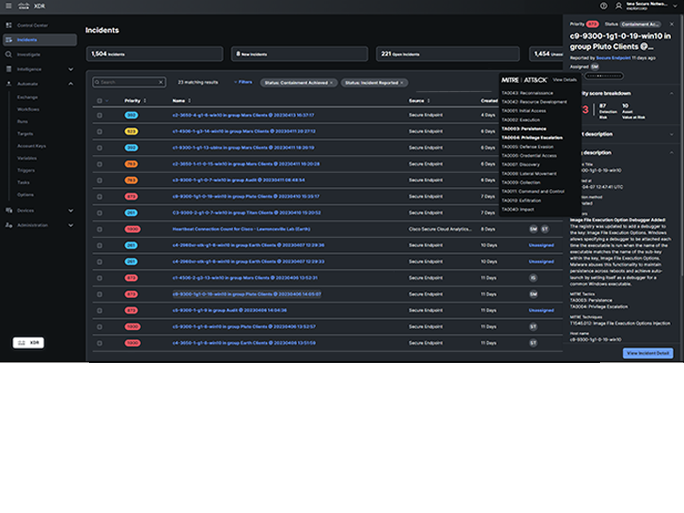
Take decisive action on prioritized incidents
Autonomously contain critical alerts, stop lateral movement, and follow guidance through prioritized incident workflows for fast, confident remediation.
Elevate productivity with AI assistance and automation
Empower analysts with guided, step‑by‑step automation and AI‑driven prioritization to level up the performance and effectiveness of your security operations team.
Built for SecOps pros by SecOps pros
Detect, investigate, and prioritize
Make defenders more effective and efficient by uncovering sophisticated attacks and using AI to prioritize incidents across multiple security controls. It's one of the fastest, easiest ways to achieve unified threat detection, investigation, and response (TDIR) in your security posture.
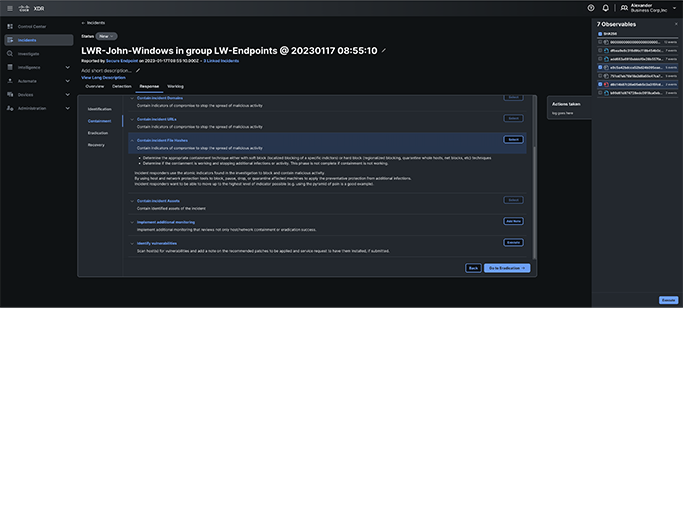
Command every response and action
Streamline incident response by simplifying preparation, detection, analysis, containment, eradication, and recovery, which can involve anything from adding a worknote to implementing an automated action to recovering from ransomware by restoring the last known good snapshot.
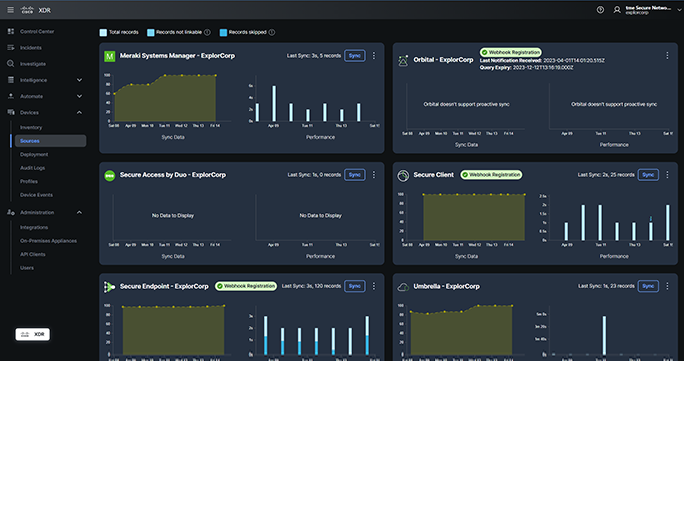
Gain visibility into users and devices
Get a comprehensive user and device inventory for contextual awareness that simplifies investigations and identifies gaps, while tracking user behaviors and devices to assess your security posture and stop threats before problems occur.
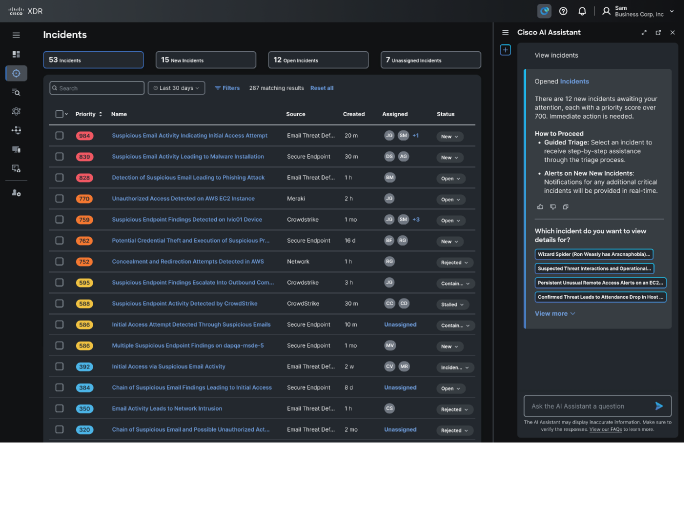
Accelerate, streamline, and strengthen
Reduce complexity and increase efficiency with the Cisco AI Assistant in XDR. Make faster, more consistent decisions and eliminate errors while easily monitoring ransomware, endpoint compromises, and more. And strengthen your security posture with MITRE ATT&CK coverage mapping.
Bring your security stack together with Cisco XDR




Endpoint telemetry and response integrations
Seamlessly integrate popular endpoint detection and response tools to extend security investments.
Cloud and network telemetry and response integrations
Easily connect cloud, network, and firewall security tools to gain insights across your environment.
Email telemetry and response integrations
Effortlessly integrate email and applications data from leading solutions to deliver secure access.
Integrate Cisco security tools to unlock more value
Cisco Secure Endpoint
Stay ahead of the latest threats with simplified, automated endpoint security.
Cisco Secure Email Threat Defense
Protect against damaging and costly email threats that can compromise your brand and operations.
Cisco Secure Network Analytics
Achieve powerful network visibility to find sophisticated, covert threats and suspicious behavior.
Cisco Breach Protection Suite
Accelerate response across the most prominent attack vectors—network, email, cloud, and endpoint—unified by Cisco XDR.
Flexible licensing options for every business
Cisco XDR
Essentials
Built by practitioners for practitioners with built-in integrations across the Cisco security portfolio so analysts can detect and respond to the most sophisticated threats.
Cisco XDR
Advantage
Includes all features in Essentials plus commercially supported and curated integrations with select third-party tools to rapidly respond to threats regardless of vector or vendor.
Cisco XDR
Premier
Offers XDR as a managed service provided by Cisco security experts. Includes security validation through penetration testing and select Cisco Talos Incident Response services.





