Maintenance Mode on the Expressway
Maintenance mode on the Expressway has been enhanced so that you can bring an MRA system down in a managed way.
When you engage maintenance mode, the Expressway stops accepting new calls or proxy (MRA) traffic. Existing calls and chat sessions are not affected.
As users end their sessions normally, the system comes to a point when it is not processing any traffic of a certain type, and then it shuts that service down.
If users try to make new calls or start new chat sessions while the Expressway is in maintenance mode, the clients will receive a service unavailable response, and they might then choose to use another peer (if they are capable). This fail-over behavior depends on the client, but restarting the client should resolve any connection issues if there are active peers in the cluster.
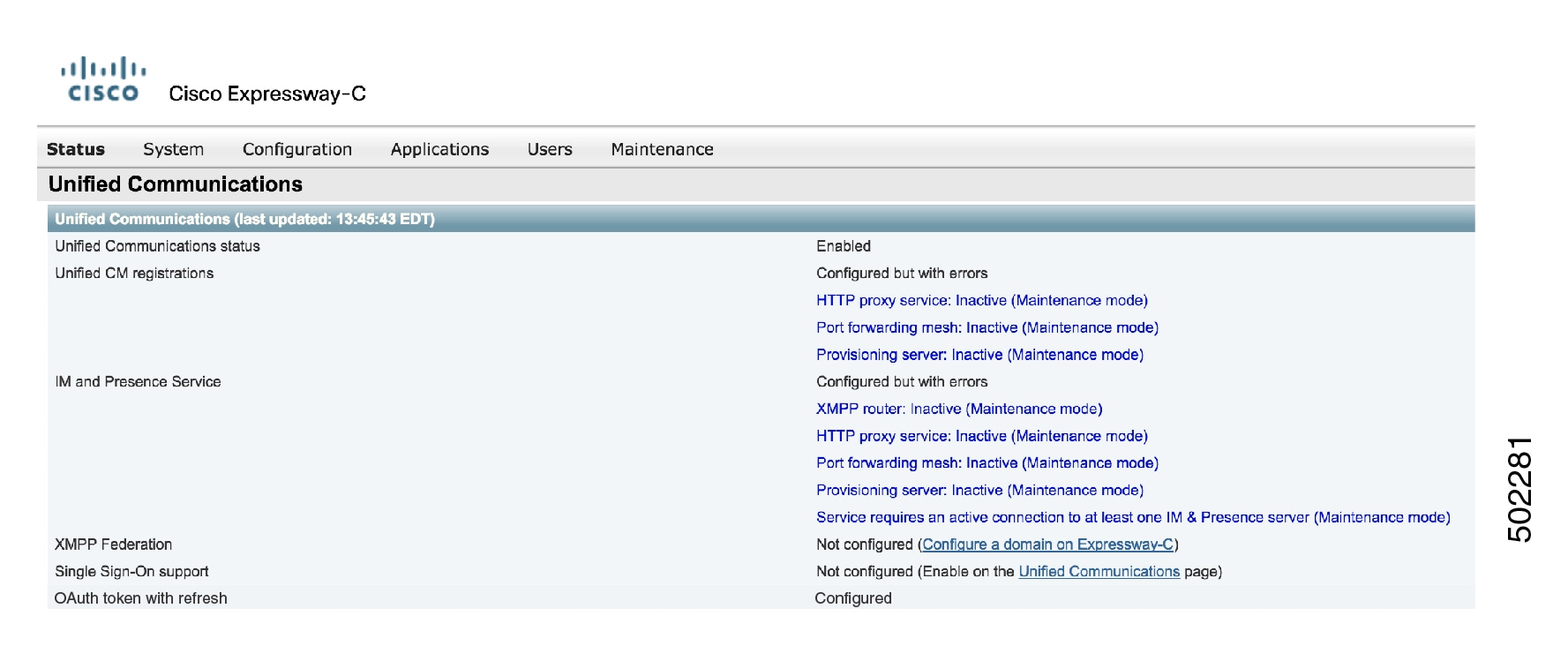
The Unified Communications status pages also show (Maintenance Mode) in any places where MRA services are affected.
Limitation for CE endpoints
Maintenance mode is not supported over MRA for endpoints running CE software. The Expressway drops MRA calls from these endpoints when you enable maintenance mode.

 Feedback
Feedback