- Release 15.4SY Supervisor Engine 2T Software Configuration Guide
- Preface
- Product Overview
- Command-Line Interfaces
- Smart Port Macros
- Virtual Switching Systems (VSS)
- Enhanced Fast Software Upgrade (eFSU)
- Fast Software Upgrades
- Stateful Switchover (SSO)
- Non-Stop Forwarding (NSF)
- RPR Supervisor Engine Redundancy
- Interface Configuration
- UniDirectional Link Detection (UDLD)
- Instant Access
- EnergyWise
- Power Management
- Environmental Monitoring
- Online Diagnostics
- Onboard Failure Logging (OBFL)
- Switch Fabric Functionality
- Cisco IP Phone Support
- Power over Ethernet
- Layer 2 LAN Port Configuration
- Flex Links
- EtherChannels
- IEEE 802.1ak MVRP and MRP
- VLAN Trunking Protocol (VTP)
- VLANs
- Private VLANs (PVLANs)
- Private Hosts
- IEEE 802.1Q Tunneling
- Layer 2 Protocol Tunneling
- Spanning Tree Protocols (STP, MST)
- Optional STP Features
- IP Unicast Layer 3 Switching
- Policy Based Routing (PBR)
- Layer 3 Interface Configuration
- Unidirectional Ethernet (UDE) and unidirectional link routing (UDLR)
- Multiprotocol Label Switching (MPLS)
- MPLS VPN Support
- Ethernet over MPLS (EoMPLS)
- Virtual Private LAN Services (VPLS)
- L2VPN Advanced VPLS (A-VPLS)
- Ethernet Virtual Connections (EVC)
- Layer 2 over Multipoint GRE (L2omGRE)
- Campus Fabric
- IPv4 Multicast Layer 3 Features
- IPv4 Multicast IGMP Snooping
- IPv4 PIM Snooping
- IPv4 Multicast VLAN Registration (MVR)
- IPv4 IGMP Filtering
- IPv4 Router Guard
- IPv4 Multicast VPN Support
- IPv6 Multicast Layer 3 Features
- IPv6 MLD Snooping
- NetFlow Hardware Support
- Call Home
- System Event Archive (SEA)
- Backplane Platform Monitoring
- Local SPAN, RSPAN, and ERSPAN
- SNMP IfIndex Persistence
- Top-N Reports
- Layer 2 Traceroute Utility
- Mini Protocol Analyzer
- PFC QoS Guidelines and Restrictions
- PFC QoS Overview
- PFC QoS Classification, Marking, and Policing
- PFC QoS Policy Based Queueing
- PFC QoS Global and Interface Options
- AutoQoS
- MPLS QoS
- PFC QoS Statistics Data Export
- Cisco IOS ACL Support
- Cisco TrustSec (CTS)
- AutoSecure
- MAC Address-Based Traffic Blocking
- Port ACLs (PACLs)
- VLAN ACLs (VACLs)
- Policy-Based Forwarding (PBF)
- Denial of Service (DoS) Protection
- Configuring IGMP Proxy
- Control Plane Policing (CoPP)
- Dynamic Host Configuration Protocol (DHCP) Snooping
- IP Source Guard
- Dynamic ARP Inspection (DAI)
- Traffic Storm Control
- Unknown Unicast Flood Control
- IEEE 802.1X Port-Based Authentication
- Configuring Web-Based Authentication
- Port Security
- Lawful Intercept
Release 15.5SY Supervisor Engine 2T Software Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 14, 2014
Chapter: Configuring Web-Based Authentication
- Prerequisites for Web-based Authentication
- Restrictions for Web-based Authentication
- Information About Web-Based Authentication
- Web-based Authentication Configuration Task List
- Configuring the Authentication Rule and Interfaces
- Configuring AAA Authentication
- Configuring Switch-to-RADIUS-Server Communication
- Configuring the HTTP Server
- Configuring an AAA Fail Policy
- Configuring the Web-based Authentication Parameters
- Removing Web-based Authentication Cache Entries
Web-Based Authentication
- Prerequisites for Web-based Authentication
- Restrictions for Web-based Authentication
- Information About Web-Based Authentication
- Default Web-Based Authentication Configuration
- How to Configure Web-Based Authentication
- Displaying Web-Based Authentication Status

Note ●![]() For complete syntax and usage information for the commands used in this chapter, see these publications:
For complete syntax and usage information for the commands used in this chapter, see these publications:
http://www.cisco.com/en/US/products/ps11846/prod_command_reference_list.html
- Cisco IOS Release 15.4SY supports only Ethernet interfaces. Cisco IOS Release 15.4SY does not support any WAN features or commands.
http://www.cisco.com/en/US/products/hw/switches/ps708/tsd_products_support_series_home.html
Participate in the Technical Documentation Ideas forum
Prerequisites for Web-based Authentication
Restrictions for Web-based Authentication
- Web-based authentication is an ingress-only feature.
- You can configure web-based authentication only on access ports. Web-based authentication is not supported on trunk ports, EtherChannel member ports, or dynamic trunk ports.
- You must configure the default ACL on the interface before configuring web-based authentication. Configure a port ACL for a Layer 2 interface, or a Cisco IOS ACL for a Layer 3 interface.
- On Layer 2 interfaces, you cannot authenticate hosts with static ARP cache assignment. These hosts are not detected by the web-based authentication feature, because they do not send ARP messages.
- By default, the IP device tracking feature is disabled on a switch. You must enable the IP device tracking feature to use web-based authentication.
- You must configure at least one IP address to run the HTTP server on the switch. You must also configure routes to reach each host IP address. The HTTP server sends the HTTP login page to the host.
- Hosts that are more than one hop away may experience traffic disruption if an STP topology change results in the host traffic arriving on a different port. This is because ARP and DHCP updates may not be sent after a Layer 2 (STP) topology change.
- Web-based authentication does not support VLAN assignment as a downloadable host policy.
- Cisco IOS Release 15.4SY support downloadable ACLs (DACLs) from the RADIUS server.
- Web-based authentication is not supported for IPv6 traffic.
Information About Web-Based Authentication
- Web-Based Authentication Overview
- Device Roles
- Host Detection
- Session Creation
- Authentication Process
- AAA Fail Policy
- Customization of the Authentication Proxy Web Pages
- Web-based Authentication Interactions with Other Features
Web-Based Authentication Overview
The web-based authentication feature implements web-based authentication (also known as Web Authentication Proxy), which can function as part of the authentication, authorization, and accounting (AAA) system.
You can use the web-based authentication feature to authenticate end users on host systems that do not run the IEEE 802.1X supplicant. You can configure the web-based authentication feature on Layer 2 and Layer 3 interfaces.
When a user initiates an HTTP session, the web-based authentication feature intercepts ingress HTTP packets from the host and sends an HTML login page to the user. The user keys in their credentials, which the web-based authentication feature sends to the AAA server for authentication. If the authentication succeeds, web-based authentication sends a Login-Successful HTML page to the host and applies the access policies returned by the AAA server.
If the authentication fails, web-based authentication feature sends a Login-Fail HTML page to the user, which prompts the user to retry the login attempt. If the user exceeds the maximum number of failed login attempts, web-based authentication sends a Login-Expired HTML page to the host and the user is placed on a watch list for a waiting period.
Device Roles
With web-based authentication, the devices in the network have specific roles as shown in Figure 86-1.
Figure 86-1 Web-based Authentication Device Roles
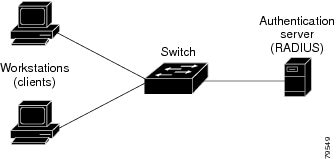
The specific roles shown in Figure 86-1 are as follows:
- Client —The device (workstation) that requests access to the LAN and switch services and responds to requests from the switch. The workstation must be running an HTML browser with Java Script enabled.
- Authentication server —Performs the actual authentication of the client. The authentication server validates the identity of the client and notifies the switch whether or not the client is authorized to access the LAN and switch services.
- Switch —Controls the physical access to the network based on the authentication status of the client. The switch acts as an intermediary (proxy) between the client and the authentication server, requesting identity information from the client, verifying that information with the authentication server, and relaying a response to the client.
Host Detection
The switch maintains an IP device tracking table to store information about detected hosts.

Note![]() By default, the IP device tracking feature is disabled on a switch. You must enable the IP device tracking feature to use web-based authentication.
By default, the IP device tracking feature is disabled on a switch. You must enable the IP device tracking feature to use web-based authentication.
For Layer 3 interfaces, web-based authentication sets an HTTP intercept ACL when the feature is configured on the interface (or when the interface is put in service).
For Layer 2 interfaces, web-based authentication detects IP hosts using the following mechanisms:
Session Creation
When web-based authentication detects a new host, it creates a session as follows:
If the host IP is included in the exception list, the policy from the exception list entry is applied, and the session is considered to be established.
If the host IP is not on the exception list, web-based authentication sends a nonresponsive host (NRH) request to the server.
If the server response is Access Accepted, authorization is bypassed for this host. The session is considered to be established.
If the server response to the NRH request is Access Rejected, the HTTP intercept ACL is activated and the session waits for HTTP traffic from the host.
Authentication Process
When web-based authentication is enabled, the following events occur:
- The user initiates an HTTP session.
- The HTTP traffic is intercepted, and authorization is initiated. The switch sends the login page to the user. The user enters a username and password on the login page, and the switch sends the entries to the authentication server.
- If the client identity is valid and the authentication succeeds, the switch downloads and activates the user’s access policy from the authentication server. The login success page is sent to the user.
- If the authentication fails, the switch sends the login fail page. The user retries the login, but if the maximum number of attempts fail, the switch sends the login expired page and the host is placed in a watch list. After a watch list timeout, the user can retry the authentication process.
- If the authentication server does not respond to the switch, and if an AAA fail policy is configured, the switch will apply the failure access policy to the host. The login success page is sent to the user.
The switch reauthenticates a client when the host does not respond to an ARP probe on a Layer 2 interface, or the host does not send any traffic within the idle timeout on a Layer 3 interface.
- The feature applies the downloaded timeout or the locally configured session timeout.
- If the terminate action is RADIUS, the feature sends a nonresponsive host (NRH) request to the server. The terminate action is included in the response from the server.
- If the terminate action is default, the session is dismantled and the applied policy is removed.
AAA Fail Policy
The AAA fail policy is a method for allowing a user to connect or to remain connected to the network if the AAA server is not available. If the AAA server cannot be reached when web-based authentication of a client is needed, instead of rejecting the user (that is, not providing the access to the network), an administrator can configure a default AAA fail policy that can be applied to the user.
This policy is advantageous for the following reasons:
- While AAA is unavailable, the user will still have connectivity to the network, although access may be restricted.
- When the AAA server is again available, a user can be revalidated, and the user’s normal access policies can be downloaded from the AAA server.

Note![]() When the AAA server is down, the AAA fail policy is applied only if there is no existing policy associated with the user. Typically, if the AAA server is unavailable when a user session requires reauthentication, the policies currently in effect for the user are retained.
When the AAA server is down, the AAA fail policy is applied only if there is no existing policy associated with the user. Typically, if the AAA server is unavailable when a user session requires reauthentication, the policies currently in effect for the user are retained.
While the AAA fail policy is in effect, the session state is maintained as AAA Down.
Customization of the Authentication Proxy Web Pages
The switch’s internal HTTP server hosts four HTML pages for delivery to an authenticating client during the web-based authentication process. The four pages allow the server to notify the user of the following four states of the authentication process:
- Login—The user’s credentials are requested
- Success—The login was successful
- Fail—The login has failed
- Expire—The login session has expired due to excessive login failures
You can substitute your custom HTML pages for the four default internal HTML pages, or you can specify a URL to which the user will be redirected upon successful authentication, effectively replacing the internal Success page.
Web-based Authentication Interactions with Other Features
Port Security
You can configure web-based authentication and port security on the same port. (You configure port security on the port by using the switchport port-security interface configuration command.) When you enable port security and web-based authentication on a port, web-based authentication authenticates the port, and port security manages network access for all MAC addresses, including that of the client. You can then limit the number or group of clients that can access the network through the port.
For more information about enabling port security, see the “How to Configure Port Security” section.
Gateway IP
You cannot configure Gateway IP on a Layer 3 VLAN interface if web-based authentication is configured on any of the switch ports in the VLAN.
You can configure web-based authentication on the same Layer 3 interface as Gateway IP. The host policies for both features are applied in software. The GWIP policy overrides the web-based authentication host policy.
ACLs
If you configure a VLAN ACL or Cisco IOS ACL on an interface, the ACL is applied to the host traffic only after the web-based authentication host policy is applied.
For Layer 2 web-based authentication, you must configure a port ACL (PACL) as the default access policy for ingress traffic from hosts connected to the port. After authentication, the web-based authentication host policy overrides the PACL.
You cannot configure a MAC ACL and web-based authentication on the same interface.
You cannot configure web-based authentication on a port whose access VLAN has VACL capture configured.
IP Source Guard
Configuring IP Source Guard and web-based authentication on the same interface is not supported.
You can configure IP Source Guard and web-based authentication on the same interface. If DHCP snooping is also enabled on the access VLAN, you must enter the platform acl tcam override dynamic dhcp-snooping command in global configuration mode to avoid conflict between the two features. Other VLAN-based features are not supported when IP Source Guard and web-based authentication are combined.
EtherChannel
You can configure web-based authentication on a Layer 2 EtherChannel interface. The web-based authentication configuration applies to all member channels.
Switchover
In RPR redundancy mode, information about currently authenticated hosts is maintained during a switchover. Users will not need to reauthenticate.
Default Web-Based Authentication Configuration
|
|
|
|---|---|
How to Configure Web-Based Authentication
- Default Web-Based Authentication Configuration
- Web-based Authentication Configuration Task List
- Configuring the Authentication Rule and Interfaces
- Configuring AAA Authentication
- Configuring Switch-to-RADIUS-Server Communication
- Configuring the HTTP Server
- Configuring the Web-based Authentication Parameters
- Removing Web-based Authentication Cache Entries
Web-based Authentication Configuration Task List
Configuring the Authentication Rule and Interfaces
To configure web-based authentication, perform this task:
This example shows how to enable web-based authentication, while disabling 802.1X or MAB authentication, on port 5/1:
This example shows how to verify the configuration:
Configuring AAA Authentication
To enable web-based authentication, you must enable AAA and specify the authentication method. perform this task:
|
|
|
|
|---|---|---|
Router(config)# aaa authentication login default group { tacacs+ | radius } |
||
Router(config)# aaa authorization auth-proxy default group { tacacs+ | radius } |
Creates an authorization method list for web-based authorization. |
|
Router(config)# tacacs-server host { hostname | ip_address } |
Specifies an AAA server. For Radius servers, see the section “Configuring Switch-to-RADIUS-Server Communication” section. |
|
Configures the authorization and encryption key used between the switch and the TACACS server. |
This example shows how to enable AAA:
Configuring Switch-to-RADIUS-Server Communication
RADIUS security servers are identified by any of the following:
- Host name
- Host IP address
- Host name and specific UDP port numbers
- IP address and specific UDP port numbers
The combination of the IP address and UDP port number creates a unique identifier, which enables RADIUS requests to be sent to multiple UDP ports on a server at the same IP address. If two different host entries on the same RADIUS server are configured for the same service (for example, authentication) the second host entry that is configured functions as the failover backup to the first one. The RADIUS host entries are chosen in the order that they were configured.
To configure the RADIUS server parameters, perform this task:
- Specify the key string on a separate command line.
- For key string , specify the authentication and encryption key used between the switch and the RADIUS daemon running on the RADIUS server. The key is a text string that must match the encryption key used on the RADIUS server.
- When you specify the key string, spaces within and at the end of the key are used. If you use spaces in the key, do not enclose the key in quotation marks unless the quotation marks are part of the key. This key must match the encryption used on the RADIUS daemon.
- You can globally configure the timeout, retransmission, and encryption key values for all RADIUS servers by using the radius-server host global configuration command. If you want to configure these options on a per-server basis, use the radius-server timeout, radius-server retransmit, and the radius-server key global configuration commands.

Note![]() You also need to configure some settings on the RADIUS server. These settings include the IP address of the switch, the key string to be shared by both the server and the switch, and the downloadable ACL. For more information, see the RADIUS server documentation.
You also need to configure some settings on the RADIUS server. These settings include the IP address of the switch, the key string to be shared by both the server and the switch, and the downloadable ACL. For more information, see the RADIUS server documentation.
This example shows how to configure the RADIUS server parameters on the switch:
Configuring the HTTP Server
To use web-based authentication, you must enable the HTTP server within the switch. You can enable the server for either HTTP or HTTPS. To enable the server, perform one of these tasks in global configuration mode:
|
|
|
|
|---|---|---|
Enables the HTTP server. The web-based authentication feature uses the HTTP server to communicate with the hosts for user authentication. |
||
You can optionally configure custom authentication proxy web pages or specify a redirection URL for successful login, as described in the following sections:
Customizing the Authentication Proxy Web Pages
You have the option to provide four substitute HTML pages to be displayed to the user in place of the switch’s internal default HTML pages during web-based authentication.
To specify the use of your custom authentication proxy web pages, first store your custom HTML files on the switch’s internal disk or flash memory, then perform this task in global configuration mode:
- To enable the custom web pages feature, you must specify all four custom HTML files. If fewer than four files are specified, the internal default HTML pages will be used.
- The four custom HTML files must be present on the disk or flash of the switch.
- An image file has a size limit of 256 KB.
- All image files must have a filename that begins with “web_auth_” (like “web_auth_logo.jpg” instead of “logo.jpg”).
- All image file names must be less than 33 characters.
- Any images on the custom pages must be located on an accessible HTTP server. An intercept ACL must be configured within the admission rule to allow access to the HTTP server.
- Any external link from a custom page will require configuration of an intercept ACL within the admission rule.
- Any name resolution required for external links or images will require configuration of an intercept ACL within the admission rule to access a valid DNS server.
- If the custom web pages feature is enabled, a configured auth-proxy-banner will not be used.
- If the custom web pages feature is enabled, the redirection URL for successful login feature will not be available.
- To remove the specification of a custom file, use the no form of the command.
Because the custom login page is a public web form, consider the following guidelines for this page:
- The login form must accept user input for the username and password and must POST the data as uname and pwd.
- The custom login page should follow best practices for a web form, such as page timeout, hidden password, and prevention of redundant submissions.
The following example shows how to configure custom authentication proxy web pages:
The following example shows how to verify the configuration of custom authentication proxy web pages:
Specifying a Redirection URL for Successful Login
You have the option to specify a URL to which the user will be redirected upon successful authentication, effectively replacing the internal Success HTML page.
To specify a redirection URL for successful login, perform this task in global configuration mode:
|
|
|
|
|---|---|---|
Router(config)# ip admission proxy http success redirect url-string |
Specifies a URL for redirection of the user in place of the default login success page. |
When configuring a redirection URL for successful login, consider the following guidelines:
- If the custom authentication proxy web pages feature is enabled, the redirection URL feature is disabled and will not be available in the CLI. You can perform redirection in the custom login success page.
- If the redirection URL feature is enabled, a configured auth-proxy-banner will not be used.
- To remove the specification of a redirection URL, use the no form of the command.
The following example shows how to configure a redirection URL for successful login:
The following example shows how to verify the redirection URL for successful login:
Configuring an AAA Fail Policy
To configure an AAA fail policy, perform this task in global configuration mode:
The following example shows how to apply an AAA fail policy:
The following example shows how to determine whether any hosts are connected in the AAA Down state:
The following example shows how to view detailed information about a particular session based on the host IP address:
Configuring the Web-based Authentication Parameters
You can configure the maximum number of failed login attempts before the client is placed in a watch list for a waiting period.
To configure the web-based authentication parameters, perform this task:
|
|
|
|
|---|---|---|
Sets the maximum number of failed login attempts. The range is 1 to 2147483647 attempts; the default is 5. |
||
This example shows how to set the maximum number of failed login attempts to 10:
Removing Web-based Authentication Cache Entries
To delete existing session entries, perform either of these tasks:
This example shows how to remove the web-based authentication session for the client at a specific IP address:
Displaying Web-Based Authentication Status
To display the web-based authentication settings for all interfaces or for specific ports, perform this task:
This example shows how to view only the global web-based authentication status:
This example shows how to view the web-based authentication settings for interface GigabitEthernet 3/27:
http://www.cisco.com/en/US/products/hw/switches/ps708/tsd_products_support_series_home.html
Participate in the Technical Documentation Ideas forum
 Feedback
Feedback