- Release 15.4SY Supervisor Engine 2T Software Configuration Guide
- Preface
- Product Overview
- Command-Line Interfaces
- Smart Port Macros
- Virtual Switching Systems (VSS)
- Enhanced Fast Software Upgrade (eFSU)
- Fast Software Upgrades
- Stateful Switchover (SSO)
- Non-Stop Forwarding (NSF)
- RPR Supervisor Engine Redundancy
- Interface Configuration
- UniDirectional Link Detection (UDLD)
- Instant Access
- EnergyWise
- Power Management
- Environmental Monitoring
- Online Diagnostics
- Onboard Failure Logging (OBFL)
- Switch Fabric Functionality
- Cisco IP Phone Support
- Power over Ethernet
- Layer 2 LAN Port Configuration
- Flex Links
- EtherChannels
- IEEE 802.1ak MVRP and MRP
- VLAN Trunking Protocol (VTP)
- VLANs
- Private VLANs (PVLANs)
- Private Hosts
- IEEE 802.1Q Tunneling
- Layer 2 Protocol Tunneling
- Spanning Tree Protocols (STP, MST)
- Optional STP Features
- IP Unicast Layer 3 Switching
- Policy Based Routing (PBR)
- Layer 3 Interface Configuration
- Unidirectional Ethernet (UDE) and unidirectional link routing (UDLR)
- Multiprotocol Label Switching (MPLS)
- MPLS VPN Support
- Ethernet over MPLS (EoMPLS)
- Virtual Private LAN Services (VPLS)
- L2VPN Advanced VPLS (A-VPLS)
- Ethernet Virtual Connections (EVC)
- Layer 2 over Multipoint GRE (L2omGRE)
- Campus Fabric
- IPv4 Multicast Layer 3 Features
- IPv4 Multicast IGMP Snooping
- IPv4 PIM Snooping
- IPv4 Multicast VLAN Registration (MVR)
- IPv4 IGMP Filtering
- IPv4 Router Guard
- IPv4 Multicast VPN Support
- IPv6 Multicast Layer 3 Features
- IPv6 MLD Snooping
- NetFlow Hardware Support
- Call Home
- System Event Archive (SEA)
- Backplane Platform Monitoring
- Local SPAN, RSPAN, and ERSPAN
- SNMP IfIndex Persistence
- Top-N Reports
- Layer 2 Traceroute Utility
- Mini Protocol Analyzer
- PFC QoS Guidelines and Restrictions
- PFC QoS Overview
- PFC QoS Classification, Marking, and Policing
- PFC QoS Policy Based Queueing
- PFC QoS Global and Interface Options
- AutoQoS
- MPLS QoS
- PFC QoS Statistics Data Export
- Cisco IOS ACL Support
- Cisco TrustSec (CTS)
- AutoSecure
- MAC Address-Based Traffic Blocking
- Port ACLs (PACLs)
- VLAN ACLs (VACLs)
- Policy-Based Forwarding (PBF)
- Denial of Service (DoS) Protection
- Configuring IGMP Proxy
- Control Plane Policing (CoPP)
- Dynamic Host Configuration Protocol (DHCP) Snooping
- IP Source Guard
- Dynamic ARP Inspection (DAI)
- Traffic Storm Control
- Unknown Unicast Flood Control
- IEEE 802.1X Port-Based Authentication
- Configuring Web-Based Authentication
- Port Security
- Lawful Intercept
Release 15.5SY Supervisor Engine 2T Software Configuration Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- August 14, 2014
Chapter: Dynamic Host Configuration Protocol (DHCP) Snooping
- Prerequisites for DHCP Snooping
- Restrictions for DHCP Snooping
- Information About DHCP Snooping
- Default Configuration for DHCP Snooping
- How to Configure DHCP Snooping
- Enabling DHCP Snooping Globally
- Enabling DHCP Option-82 Data Insertion
- Enabling the DHCP Option-82 on Untrusted Port Feature
- Enabling DHCP Snooping MAC Address Verification
- Enabling DHCP Snooping on VLANs
- Configuring the DHCP Trust State on Layer 2 LAN Interfaces
- Configuring Spurious DHCP Server Detection
- Configuring DHCP Snooping Rate Limiting on Layer 2 LAN Interfaces
- Enabling VRF-Aware DHCP Option 82 with IANA Settings
- The DHCP Snooping Database Agent
- Displaying the DHCP Snooping Binding Table
Dynamic Host Configuration Protocol (DHCP) Snooping
- Prerequisites for DHCP Snooping
- Restrictions for DHCP Snooping
- Information About DHCP Snooping
- Default Configuration for DHCP Snooping
- How to Configure DHCP Snooping

Note ●![]() For complete syntax and usage information for the commands used in this chapter, see these publications:
For complete syntax and usage information for the commands used in this chapter, see these publications:
http://www.cisco.com/en/US/products/ps11846/prod_command_reference_list.html
- Cisco IOS Release 15.4SY supports only Ethernet interfaces. Cisco IOS Release 15.4SY does not support any WAN features or commands.
http://www.cisco.com/en/US/products/hw/switches/ps708/tsd_products_support_series_home.html
Participate in the Technical Documentation Ideas forum
Prerequisites for DHCP Snooping
Restrictions for DHCP Snooping
- DHCP Snooping Configuration Restrictions
- DHCP Snooping Configuration Guidelines
- Minimum DHCP Snooping Configuration
DHCP Snooping Configuration Restrictions
- The DHCP snooping database stores at least 12,000 bindings.
- When DHCP snooping is enabled, these Cisco IOS DHCP commands are not available on the switch:
–![]() ip dhcp relay information check global configuration command
ip dhcp relay information check global configuration command
–![]() ip dhcp relay information policy global configuration command
ip dhcp relay information policy global configuration command
–![]() ip dhcp relay information trust-all global configuration command
ip dhcp relay information trust-all global configuration command
–![]() ip dhcp relay information option global configuration command
ip dhcp relay information option global configuration command
–![]() ip dhcp relay information trusted interface configuration command
ip dhcp relay information trusted interface configuration command
If you enter these commands, the switch returns an error message, and the configuration is not applied.
DHCP Snooping Configuration Guidelines
- DHCP snooping is not active until you enable the feature on at least one VLAN, and enable DHCP globally on the switch.
- Before globally enabling DHCP snooping on the switch, make sure that the devices acting as the DHCP server and the DHCP relay agent are configured and enabled.
- For DHCP server configuration information, see this publication:
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dhcp/configuration/15-sy/dhcp-15-sy-book.html
- If a Layer 2 LAN port is connected to a DHCP server, configure the port as trusted by entering the ip dhcp snooping trust interface configuration command.
- If a Layer 2 LAN port is connected to a DHCP client, configure the port as untrusted by entering the no ip dhcp snooping trust interface configuration command.
- You can enable DHCP snooping on private VLANs:
–![]() If DHCP snooping is enabled, any primary VLAN configuration is propagated to its associated secondary VLANs.
If DHCP snooping is enabled, any primary VLAN configuration is propagated to its associated secondary VLANs.
–![]() If DHCP snooping is configured on the primary VLAN and you configure DHCP snooping with different settings on an associated secondary VLAN, the configuration on the secondary VLAN does not take effect.
If DHCP snooping is configured on the primary VLAN and you configure DHCP snooping with different settings on an associated secondary VLAN, the configuration on the secondary VLAN does not take effect.
–![]() If DHCP snooping is not configured on the primary VLAN and you configure DHCP snooping on a secondary VLAN, the configuration takes affect only on the secondary VLAN.
If DHCP snooping is not configured on the primary VLAN and you configure DHCP snooping on a secondary VLAN, the configuration takes affect only on the secondary VLAN.
–![]() When you manually configure DHCP snooping on a secondary VLAN, this message appears:
When you manually configure DHCP snooping on a secondary VLAN, this message appears:
–![]() The show ip dhcp snooping command displays all VLANs (both primary and secondary) that have DHCP snooping enabled.
The show ip dhcp snooping command displays all VLANs (both primary and secondary) that have DHCP snooping enabled.
Minimum DHCP Snooping Configuration
1.![]() Define and configure the DHCP server. See this publication:
Define and configure the DHCP server. See this publication:
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dhcp/configuration/15-sy/dhcp-15-sy-book.html
2.![]() Enable DHCP snooping on at least one VLAN.
Enable DHCP snooping on at least one VLAN.
By default, DHCP snooping is inactive on all VLANs. See the “Enabling DHCP Snooping on VLANs” section
3.![]() Ensure that DHCP server is connected through a trusted interface.
Ensure that DHCP server is connected through a trusted interface.
By default, the trust state of all interfaces is untrusted. See the “Configuring the DHCP Trust State on Layer 2 LAN Interfaces” section
4.![]() Configure the DHCP snooping database agent.
Configure the DHCP snooping database agent.
This step ensures that database entries are restored after a restart or switchover. See the “The DHCP Snooping Database Agent” section
5.![]() Enable DHCP snooping globally.
Enable DHCP snooping globally.
The feature is not active until you complete this step. See the “Enabling DHCP Snooping Globally” section
If you are configuring the switch for DHCP relay, the following additional steps are required:
1.![]() Define and configure the DHCP relay agent IP address.
Define and configure the DHCP relay agent IP address.
If the DHCP server is in a different subnet from the DHCP clients, configure the server IP address in the helper address field of the client side VLAN.
2.![]() Configure DHCP option-82 on untrusted port.
Configure DHCP option-82 on untrusted port.
See the “Enabling the DHCP Option-82 on Untrusted Port Feature” section
Information About DHCP Snooping
- Overview of DHCP Snooping
- Trusted and Untrusted Sources
- DHCP Snooping Binding Database
- Packet Validation
- DHCP Snooping Option-82 Data Insertion
- Overview of the DHCP Snooping Database Agent
- VRF-Aware DHCP Option 82
Overview of DHCP Snooping
DHCP snooping is a security feature that acts like a firewall between untrusted hosts and trusted DHCP servers. The DHCP snooping feature performs the following activities:
- Validates DHCP messages received from untrusted sources and filters out invalid messages.
- Rate-limits DHCP traffic from trusted and untrusted sources.
- Builds and maintains the DHCP snooping binding database, which contains information about untrusted hosts with leased IP addresses.
- Utilizes the DHCP snooping binding database to validate subsequent requests from untrusted hosts.
Other security features, such as dynamic ARP inspection (DAI), also use information stored in the DHCP snooping binding database.
DHCP snooping is enabled on a per-VLAN basis. By default, the feature is inactive on all VLANs. You can enable the feature on a single VLAN or a range of VLANs.
The DHCP snooping feature is implemented in software on the route processor (RP). Therefore, all DHCP messages for enabled VLANs are intercepted in the PFC and directed to the RP for processing.
Trusted and Untrusted Sources
The DHCP snooping feature determines whether traffic sources are trusted or untrusted. An untrusted source may initiate traffic attacks or other hostile actions. To prevent such attacks, the DHCP snooping feature filters messages and rate-limits traffic from untrusted sources.
In an enterprise network, devices under your administrative control are trusted sources. These devices include the switches, routers, and servers in your network. Any device beyond the firewall or outside your network is an untrusted source. Host ports and unknown DHCP servers are generally treated as untrusted sources.
A DHCP server that is on your network without your knowledge on an untrusted port is called a spurious DHCP server. A spurious DHCP server is any piece of equipment that is loaded with DHCP server enabled. Some examples are desktop systems and laptop systems that are loaded with DHCP server enabled, or wireless access points honoring DHCP requests on the wired side of your network. If spurious DHCP servers remain undetected, you will have difficulties troubleshooting a network outage. You can detect spurious DHCP servers by sending dummy DHCPDISCOVER packets out to all of the DHCP servers so that a response is sent back to the switch.
In a service provider environment, any device that is not in the service provider network is an untrusted source (such as a customer switch). Host ports are untrusted sources.
In the switch, you indicate that a source is trusted by configuring the trust state of its connecting interface.
The default trust state of all interfaces is untrusted. You must configure DHCP server interfaces as trusted. You can also configure other interfaces as trusted if they connect to devices (such as switches or routers) inside your network. You usually do not configure host port interfaces as trusted.

Note![]() For DHCP snooping to function properly, all DHCP servers must be connected to the switch through trusted interfaces, as untrusted DHCP messages will be forwarded only to trusted interfaces.
For DHCP snooping to function properly, all DHCP servers must be connected to the switch through trusted interfaces, as untrusted DHCP messages will be forwarded only to trusted interfaces.
DHCP Snooping Binding Database
The DHCP snooping binding database is also referred to as the DHCP snooping binding table.
The DHCP snooping feature dynamically builds and maintains the database using information extracted from intercepted DHCP messages. The database contains an entry for each untrusted host with a leased IP address if the host is associated with a VLAN that has DHCP snooping enabled. The database does not contain entries for hosts connected through trusted interfaces.
The DHCP snooping feature updates the database when the switch receives specific DHCP messages. For example, the feature adds an entry to the database when the switch receives a DHCPACK message from the server. The feature removes the entry in the database when the IP address lease expires or the switch receives a DHCPRELEASE message from the host.
Each entry in the DHCP snooping binding database includes the MAC address of the host, the leased IP address, the lease time, the binding type, and the VLAN number and interface information associated with the host.
Packet Validation
The switch validates DHCP packets received on the untrusted interfaces of VLANs with DHCP snooping enabled. The switch forwards the DHCP packet unless any of the following conditions occur (in which case the packet is dropped):
- The switch receives a packet (such as a DHCPOFFER, DHCPACK, DHCPNAK, or DHCPLEASEQUERY packet) from a DHCP server outside the network or firewall.
- The switch receives a packet on an untrusted interface, and the source MAC address and the DHCP client hardware address do not match. This check is performed only if the DHCP snooping MAC address verification option is turned on.
- The switch receives a DHCPRELEASE or DHCPDECLINE message from an untrusted host with an entry in the DHCP snooping binding table, and the interface information in the binding table does not match the interface on which the message was received.
- The switch receives a DHCP packet that includes a relay agent IP address that is not 0.0.0.0.
To support trusted edge switches that are connected to untrusted aggregation-switch ports, you can enable the DHCP option-82 on untrusted port feature, which enables untrusted aggregation-switch ports to accept DHCP packets that include option-82 information. Configure the port on the edge switch that connects to the aggregation switch as a trusted port.

Note![]() With the DHCP option-82 on untrusted port feature enabled, use dynamic ARP inspection on the aggregation switch to protect untrusted input interfaces.
With the DHCP option-82 on untrusted port feature enabled, use dynamic ARP inspection on the aggregation switch to protect untrusted input interfaces.
DHCP Snooping Option-82 Data Insertion
In residential, metropolitan Ethernet-access environments, DHCP can centrally manage the IP address assignments for a large number of subscribers. When the DHCP snooping option-82 feature is enabled on the switch, a subscriber device is identified by the switch port through which it connects to the network (in addition to its MAC address). Multiple hosts on the subscriber LAN can be connected to the same port on the access switch and are uniquely identified.
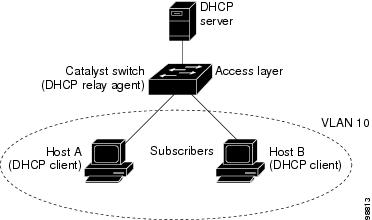
Figure 80-1 is an example of a metropolitan Ethernet network in which a centralized DHCP server assigns IP addresses to subscribers connected to the switch at the access layer. Because the DHCP clients and their associated DHCP server do not reside on the same IP network or subnet, a DHCP relay agent is configured with a helper address to enable broadcast forwarding and to transfer DHCP messages between the clients and the server.
Figure 80-1 DHCP Relay Agent in a Metropolitan Ethernet Network
When you enable the DHCP snooping information option-82 on the switch, this sequence of events occurs:
- The host (DHCP client) generates a DHCP request and broadcasts it on the network.
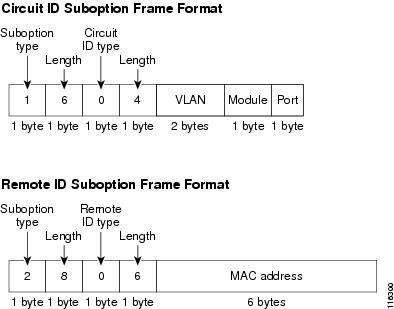
- When the switch receives the DHCP request, it adds the option-82 information in the packet. The option-82 information contains the switch MAC address (the remote ID suboption) and the port identifier, vlan-mod-port, from which the packet is received (the circuit ID suboption).
- If IEEE 802.1X port-based authentication is enabled, the switch will also add the host’s 802.1X authenticated user identity information (the RADIUS attributes suboption) to the packet. See the “802.1X Authentication with DHCP Snooping” section.
- If the IP address of the relay agent is configured, the switch adds the IP address in the DHCP packet.
- The switch forwards the DHCP request that includes the option-82 field to the DHCP server.
- The DHCP server receives the packet. If the server is option-82 capable, it can use the remote ID, or the circuit ID, or both to assign IP addresses and implement policies, such as restricting the number of IP addresses that can be assigned to a single remote ID or circuit ID. The DHCP server then echoes the option-82 field in the DHCP reply.
- The DHCP server unicasts the reply to the switch if the request was relayed to the server by the switch. When the client and server are on the same subnet, the server broadcasts the reply. The switch verifies that it originally inserted the option-82 data by inspecting the remote ID and possibly the circuit ID fields. The switch removes the option-82 field and forwards the packet to the switch port that connects to the DHCP client that sent the DHCP request.
When the previously described sequence of events occurs, the values in these fields in Figure 80-2 do not change:
–![]() Length of the suboption type
Length of the suboption type
–![]() Length of the circuit ID type
Length of the circuit ID type
–![]() Length of the suboption type
Length of the suboption type
–![]() Length of the circuit ID type
Length of the circuit ID type
Figure 80-2 shows the packet formats for the remote ID suboption and the circuit ID suboption. The switch uses the packet formats when DHCP snooping is globally enabled and when the ip dhcp snooping information option global configuration command is entered. For the circuit ID suboption, the module field is the slot number of the module.
Figure 80-2 Suboption Packet Formats
Overview of the DHCP Snooping Database Agent
To retain the bindings across reloads, you must use the DHCP snooping database agent. Without this agent, the bindings established by DHCP snooping are lost upon reload, and connectivity is lost as well.
The database agent stores the bindings in a file at a configured location. Upon reload, the switch reads the file to build the database for the bindings. The switch keeps the file current by writing to the file as the database changes.
The format of the file that contains the bindings is as follows:
Each entry in the file is tagged with a checksum that is used to validate the entries whenever the file is read. The <initial-checksum> entry on the first line helps distinguish entries associated with the latest write from entries that are associated with a previous write.
This is a sample bindings file:
Each entry holds an IP address, VLAN, MAC address, lease time (in hex), and the interface associated with a binding. At the end of each entry is a checksum that is based on all the bytes from the start of the file through all the bytes associated with the entry. Each entry consists of 72 bytes of data, followed by a space, followed by a checksum.
Upon bootup, when the calculated checksum equals the stored checksum, the switch reads entries from the file and adds the bindings to the DHCP snooping database. If the calculated checksum does not equal the stored checksum, the entry read from the file is ignored and so are all the entries following the failed entry. The switch also ignores all those entries from the file whose lease time has expired. (This is possible because the lease time might indicate an expired time.) An entry from the file is also ignored if the interface referred to in the entry no longer exists on the system, or if it is a router port or a DHCP snooping-trusted interface.
When the switch learns of new bindings or when it loses some bindings, the switch writes the modified set of entries from the snooping database to the file. The writes are performed with a configurable delay to batch as many changes as possible before the actual write happens. Associated with each transfer is a timeout after which a transfer is aborted if it is not completed. These timers are referred to as the write delay and abort timeout.
VRF-Aware DHCP Option 82
VRF-aware DHCP option 82 provides additional security when DHCP is used to allocate network addresses. It enables the device to act as a DHCP relay agent to prevent DHCP client requests from untrusted sources.
You must configure two VRFs on the Cisco Catalyst 6500 Series switch that functions as the DHCP relay agent. The first VRF receives the DHCP discover message from the DHCP client. The second VRF forwards the DHCP request to the DHCP server. The DHCP relay agent adds option 82 information to DHCP requests from clients, before forwarding the DHCP requests to the DHCP server. The DHCP server verifies this information and offers an IP address from the VRF IP address pool to the DHCP request. The DHCP relay agent forwards the offer to the DHCP client and establishes a connection between the DHCP client and DHCP server.
Starting with Cisco IOS Release 15.5(1)SY5, support for VRF-aware DHCP option 82 with IANA settings as sub-options was introduced.
See Enabling VRF-Aware DHCP Option 82 with IANA Settings section for more information on how to enable VRF-Aware DHCP Option 82 with IANA Settings.
Default Configuration for DHCP Snooping
|
|
|
|---|---|
How to Configure DHCP Snooping
- Enabling DHCP Snooping Globally
- Enabling DHCP Option-82 Data Insertion
- Enabling the DHCP Option-82 on Untrusted Port Feature
- Enabling DHCP Snooping MAC Address Verification
- Enabling DHCP Snooping on VLANs
- Configuring the DHCP Trust State on Layer 2 LAN Interfaces
- Configuring Spurious DHCP Server Detection
- Configuring DHCP Snooping Rate Limiting on Layer 2 LAN Interfaces
- Enabling VRF-Aware DHCP Option 82 with IANA Settings
- The DHCP Snooping Database Agent
- Configuration Examples for the Database Agent
- Displaying the DHCP Snooping Binding Table
Enabling DHCP Snooping Globally

Note![]() Configure this command as the last configuration step (or enable the DHCP feature during a scheduled maintenance period) because after you enable DHCP snooping globally, the switch drops DHCP requests until you configure the ports.
Configure this command as the last configuration step (or enable the DHCP feature during a scheduled maintenance period) because after you enable DHCP snooping globally, the switch drops DHCP requests until you configure the ports.
To enable DHCP snooping globally, perform this task:
|
|
|
|
|---|---|---|
This example shows how to enable DHCP snooping globally:

Note![]() When DHCP snooping is disabled and DAI is enabled, the switch shuts down all the hosts because all ARP entries in the ARP table will be checked against a nonexistent DHCP database. When DHCP snooping is disabled or in non-DHCP environments, use ARP ACLs to permit or to deny ARP packets.
When DHCP snooping is disabled and DAI is enabled, the switch shuts down all the hosts because all ARP entries in the ARP table will be checked against a nonexistent DHCP database. When DHCP snooping is disabled or in non-DHCP environments, use ARP ACLs to permit or to deny ARP packets.
Enabling DHCP Option-82 Data Insertion
To enable DHCP option-82 data insertion, perform this task:
|
|
|
|
|---|---|---|
This example shows how to disable DHCP option-82 data insertion:
This example shows how to enable DHCP option-82 data insertion:
Enabling the DHCP Option-82 on Untrusted Port Feature

Note![]() With the DHCP option-82 on untrusted port feature enabled, the switch does not drop DHCP packets that include option-82 information that are received on untrusted ports. Do not enter the ip dhcp snooping information option allowed-untrusted command on an aggregation switch to which any untrusted devices are connected.
With the DHCP option-82 on untrusted port feature enabled, the switch does not drop DHCP packets that include option-82 information that are received on untrusted ports. Do not enter the ip dhcp snooping information option allowed-untrusted command on an aggregation switch to which any untrusted devices are connected.
To enable untrusted ports to accept DHCP packets that include option-82 information, perform this task:
|
|
|
|
|---|---|---|
Router(config)# ip dhcp snooping information option allow-untrusted |
(Optional) Enables untrusted ports to accept incoming DHCP packets with option-82 information. |
|
This example shows how to enable the DHCP option-82 on untrusted port feature:
Enabling DHCP Snooping MAC Address Verification
With DHCP snooping MAC address verification enabled, DHCP snooping verifies that the source MAC address and the client hardware address match in DHCP packets that are received on untrusted ports. The source MAC address is a Layer 2 field associated with the packet, and the client hardware address is a Layer 3 field in the DHCP packet.
To enable DHCP snooping MAC address verification, perform this task:
|
|
|
|
|---|---|---|
This example shows how to disable DHCP snooping MAC address verification:
This example shows how to enable DHCP snooping MAC address verification:
Enabling DHCP Snooping on VLANs
By default, the DHCP snooping feature is inactive on all VLANs. You may enable the feature on a single VLAN or a range of VLANs.
When enabled on a VLAN, the DHCP snooping feature creates four entries in the VACL table in the MFC3. These entries cause the PFC or DFC to intercept all DHCP messages on this VLAN and send them to the RP. The DHCP snooping feature is implemented in software on the RP.
To enable DHCP snooping on VLANs, perform this task:
|
|
|
|
|---|---|---|
Router(config)# ip dhcp snooping vlan {{ vlan_ID [ vlan_ID ]} | { vlan_range } |
||
You can configure DHCP snooping for a single VLAN or a range of VLANs:
- To configure a single VLAN, enter a single VLAN number.
- To configure a range of VLANs, enter a beginning and an ending VLAN number or a dash-separated pair of VLAN numbers.
- You can enter a comma-separated list of VLAN numbers and dash-separated pairs of VLAN numbers.
This example shows how to enable DHCP snooping on VLANs 10 through 12:
This example shows another way to enable DHCP snooping on VLANs 10 through 12:
This example shows another way to enable DHCP snooping on VLANs 10 through 12:
This example shows how to enable DHCP snooping on VLANs 10 through 12 and VLAN 15:
This example shows how to verify the configuration:
Configuring the DHCP Trust State on Layer 2 LAN Interfaces
To configure DHCP trust state on a Layer 2 LAN interface, perform this task:
This example shows how to configure Gigabit Ethernet port 5/12 as trusted:
This example shows how to configure Gigabit Ethernet port 5/12 as untrusted:
Configuring Spurious DHCP Server Detection
To detect and locate spurious DHCP servers, perform this task:
|
|
|
|
|---|---|---|
Enables detection of spurious DHCP servers on a specified VLAN range. |
||
Router(config)# ip dhcp snooping detect spurious interval time |
||
This example shows how to configure DHCP spurious server detection on VLANs 20 to 25 and set the interval to 50 minutes:
Configuring DHCP Snooping Rate Limiting on Layer 2 LAN Interfaces
To configure DHCP snooping rate limiting on a Layer 2 LAN interface, perform this task:
When configuring DHCP snooping rate limiting on a Layer 2 LAN interface, note the following information:
- We recommend an untrusted rate limit of not more than 100 packets per second (pps).
- If you configure rate limiting for trusted interfaces, you might need to increase the rate limit on trunk ports carrying more than one VLAN on which DHCP snooping is enabled.
- DHCP snooping puts ports where the rate limit is exceeded into the error-disabled state.
This example shows how to configure DHCP packet rate limiting to 100 pps on Gigabit Ethernet port 5/12:
Enabling VRF-Aware DHCP Option 82 with IANA Settings
To enable VRF-aware DHCP option 82 on a DHCP relay agent with IANA settings, perform this task:
The DHCP Snooping Database Agent
Prerequisites for the DHCP Snooping Database Agent
Restrictions for the DHCP Snooping Database Agent
- The DHCP snooping database stores at least 8,000 bindings.
- Store the file on a TFTP server to avoid consuming storage space on the switch storage devices.
- When a switchover occurs, if the file is stored in a remote location accessible through TFTP, the newly active supervisor engine can use the binding list.
- Network-based URLs (such as TFTP and FTP) require that you create an empty file at the configured URL before the switch can write the set of bindings for the first time.
Default Settings for the DHCP Snooping Database Agent
How to Configure the DHCP Snooping Database Agent
To configure the DHCP snooping database agent, perform one or more of the following tasks:
Configuration Examples for the Database Agent
Example 1: Enabling the Database Agent
The following example shows how to configure the DHCP snooping database agent to store the bindings at a given location and to view the configuration and operating state:
The first three lines of output show the configured URL and related timer-configuration values. The next three lines show the operating state and the amount of time left for expiry of write delay and abort timers.
Among the statistics shown in the output, startup failures indicate the number of attempts to read or create the file that failed on bootup.

Note![]() Create a temporary file on the TFTP server with the touch command in the TFTP server daemon directory. With some UNIX implementations, the file should have full read and write access permissions (777).
Create a temporary file on the TFTP server with the touch command in the TFTP server daemon directory. With some UNIX implementations, the file should have full read and write access permissions (777).
DHCP snooping bindings are keyed on the MAC address and VLAN combination. If an entry in the remote file has an entry for a given MAC address and VLAN set for which the switch already has a binding, the entry from the remote file is ignored when the file is read. This condition is referred to as the binding collision.
An entry in a file may no longer be valid because the lease indicated by the entry may have expired by the time it is read. The expired leases counter indicates the number of bindings that are ignored because of this condition. The Invalid interfaces counter refers to the number of bindings that have been ignored when the interface referred by the entry either does not exist on the system or is a router or DHCP snooping trusted interface (if it exists) when the read happened. Unsupported VLANs refers to the number of entries that have been ignored because the indicated VLAN is not supported on the system. The Parse failures counter provides the number of entries that have been ignored when the switch is unable to interpret the meaning of the entries from the file.
The switch maintains two sets of counters for these ignored bindings. One provides the counters for a read that has at least one binding ignored by at least one of these conditions. These counters are shown as the “Last ignored bindings counters.” The total ignored bindings counters provides a sum of the number of bindings that have been ignored because of all the reads since the switch bootup. These two sets of counters are cleared by the clear command. The total counter set may indicate the number of bindings that have been ignored since the last clear.
Example 2: Reading Binding Entries from a TFTP File
To manually read the entries from a TFTP file, perform this task:
|
|
|
|
|---|---|---|
|
|
||
|
|
||
|
|
||
|
|
This is an example of how to manually read entries from the tftp://10.1.1.1/directory/file:
Example 3: Adding Information to the DHCP Snooping Database
To manually add a binding to the DHCP snooping database, perform this task:
|
|
|
|
|---|---|---|
|
|
||
|
|
||
|
|
This example shows how to manually add a binding to the DHCP snooping database:
Displaying the DHCP Snooping Binding Table
The DHCP snooping binding table for each switch contains binding entries that correspond to untrusted ports. The table does not contain information about hosts interconnected with a trusted port because each interconnected switch will have its own DHCP snooping binding table.
This example shows how to display the DHCP snooping binding information for a switch:
Table 80-1 describes the fields in the show ip dhcp snooping binding command output.
|
|
|
|---|---|
Binding type: dynamic binding learned by DHCP snooping or statically-configured binding |
|
http://www.cisco.com/en/US/products/hw/switches/ps708/tsd_products_support_series_home.html
Participate in the Technical Documentation Ideas forum
 Feedback
Feedback