- Index
- Preface
- Overview
- Using the Command-Line Interface
- Assigning the Switch IP Address and Default Gateway
- Configuring Cisco IOS Configuration Engine
- Managing Switch Stacks
- Clustering Switches
- Administering the Switch
- Configuring SDM Templates
- Managing Catalyst 3750-X Stack Power
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Web-Based Authentication
- Configuring Interface Characteristics
- Configuring Auto Smartports Macros
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLANs
- Configuring Private VLANs
- Configuring IEEE 802.1Q and Layer 2 Protocol Tunneling
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Flex Links
- Configuring DHCP Features and IP Source Guard
- Configuring Dynamic ARP Inspection
- Configuring IGMP Snooping and MVR
- Configuring IPv6 MLD Snooping
- Configuring Port-Based Traffic Control
- Configuring CDP
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring UDLD
- Configuring SPAN and RSPAN
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Embedded Event Manager
- Configuring Network Security with ACLs
- Configuring IPv6 ACLs
- Configuring QoS
- Configuring EtherChannels
- Configuring TelePresence E911 IP Phone Support
- Configuring IP Unicast Routing
- Configuring IPv6 Unicast Routing
- Configuring HSRP
- Configuring Cisco IOS IP SLAs Operations
- Configuring Enhanced Object Tracking
- Configuring WCCP
- Configuring IP Multicast Routing
- Configuring MSDP
- Configuring Fallback Bridging
- Troubleshooting
- Configuring Online Diagnostics
- Supported MIBs
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Unsupported Commands in Cisco IOS Release 12.2(53)SE
- Understanding Auto Smartports and Static Smartports Macros
- Configuring Auto Smartports
- Default Auto Smartports Configuration
- Auto Smartports Configuration Guidelines
- Enabling Auto Smartports
- Configuring Auto Smartports Default Parameter Values
- Configuring Auto Smartports MAC-Address Groups
- Configuring Auto Smartports Macro Persistent
- Configuring Auto Smartports Built-In Macro Options
- Creating User-Defined Event Triggers
- Configuring Auto Smartports User-Defined Macros
- Configuring Static Smartports Macros
- Displaying Auto Smartports and Static Smartports Macros
Configuring Auto Smartports Macros
This chapter describes how to configure and apply Auto Smartports and static Smartports macros on the Catalyst 3750-X or 3560-X switch.

Note![]() For complete syntax and usage information for the commands used in this chapter, see the command reference for this release.
For complete syntax and usage information for the commands used in this chapter, see the command reference for this release.
Understanding Auto Smartports and Static Smartports Macros
Auto Smartports macros dynamically configure ports based on the device type detected on the port. When the switch detects a new device on a port it applies the appropriate Auto Smartports macro on the port. When there is a link-down event on the port, the switch removes the macro. For example, when you connect a Cisco IP phone to a port, Auto Smartports automatically applies the IP phone macro. The IP phone macro enables quality of service (QoS), security features, and a dedicated voice VLAN to ensure proper treatment of delay-sensitive voice traffic. Auto Smartports uses event triggers to map devices to macros.
The Auto Smartports macros embedded in the switch software are groups of CLI commands. The CISCO_PHONE event detected on a port triggers the switch to apply the commands in the CISCO_PHONE_AUTO_SMARTPORT macro. You can also create user-defined macros by using the Cisco IOS Shell scripting capability, which is a BASH-like language syntax for command automation and variable replacement.
Auto Smartports macros differ from static Smartports macros because static Smartports macros provide port configuration that you manually apply based on the device connected to the port. When you apply a static Smartports macro the CLI commands within the macro are added to the existing port configuration. When there is a link-down event on the port, the switch does not remove the static macro configuration.
Auto Smartports uses events to map macros to the source port of the event. The most common event triggers are based on Cisco Discovery Protocol (CDP) messages received from a connected device. The detection of a device invokes a CDP event trigger: Cisco IP Phone, Cisco Wireless Access Point including Autonomous and Lightweight Access Points, Cisco switch, Cisco router, and Cisco IP Video Surveillance Camera.
Additional event triggers for Cisco and third-party devices are user-defined MAC-address groups, MAC authentication bypass (MAB) messages, 802.1x authentication messages, and Link Layer Discovery Protocol (LLDP) messages.
LLDP supports a set of attributes that it uses to discover neighbor devices. These attributes contain type, length, and value descriptions and are referred to as TLVs. LLDP-supported devices use TLVs to receive and send information. This protocol advertises details such as configuration information, device capabilities, and device identity. Auto Smartports uses the LLDP system capabilities TLV as the event trigger. For more information about configuring the LLDP system capabilities TLV attributes for Auto Smartports, see Chapter30, “Configuring LLDP, LLDP-MED, and Wired Location Service”
For devices that do not support CDP, MAB, or 802.1x authentication, such as network printers, LLDP, or legacy Cisco Digital Media Players, you can configure a MAC-address group with a MAC operationally unique identifier (OUI)-based trigger. You map the MAC-address to a built-in or user-defined macro containing the desired configuration.
You can designate a remote server location for user-defined macro files. You can then update and maintain one set of Auto Smartport macro files for use by multiple switches across the network.
The Auto Smartports macro persistent feature enables macro configurations to remain applied on the switch ports regardless of a detected linkdown event. You can use this feature to make the Auto Smartport macros configurations static on the switch. This can eliminate multiple system log and configuration change notification events when the switch has linkup and linkdown events or is a participating entity in an EnergyWise-configured network.
Auto Smartports and Cisco Medianet
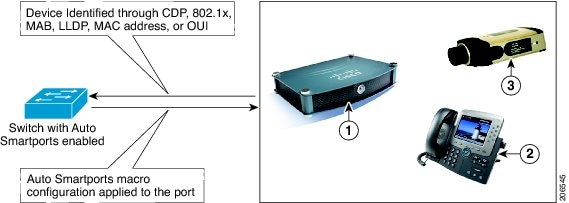
Cisco Medianet enables intelligent services in the network infrastructure for a wide variety of video applications. One of the services of Medianet is auto provisioning for Cisco Digital Media Players and Cisco IP Video Surveillance cameras through Auto Smartports. The switch identifies Cisco and third-party video devices by using CDP, 802.1x, MAB, LLDP, and MAC addresses (Figure 14-1). The switch applies the applicable Auto Smartports macro to enable the appropriate VLAN and QoS settings for the device. The switch also uses a built-in MAC-address group to detect the legacy Cisco DMP, based on an OUI of of4400 or 23ac00. You can also create custom user-defined macros for any video device.
Figure 14-1 Cisco Medianet Deployment Example
Configuring Auto Smartports
- Default Auto Smartports Configuration
- Auto Smartports Configuration Guidelines
- Enabling Auto Smartports
- Configuring Auto Smartports Default Parameter Values
- Configuring Auto Smartports MAC-Address Groups
- Configuring Auto Smartports Macro Persistent
- Configuring Auto Smartports Built-In Macro Options
- Creating User-Defined Event Triggers
- Configuring Auto Smartports User-Defined Macros
Default Auto Smartports Configuration
- Auto Smartports is disabled globally and enabled per interface.
- CDP fallback is disabled globally and enabled per interface.
- Cisco IOS shell is enabled.
- Auto Smartports macros are used by default when ASP is enabled for the devices shown in Table 14-1 .
Auto Smartports Configuration Guidelines
- The built-in macros cannot be deleted or changed. However, you can override a built-in macro by creating a user-defined macro with the same name. To restore the original built-in macro, delete the user-defined macro.
- If you enable both the macro auto device and the macro auto execute global configuration commands, the parameters specified in the command last executed will be applied to the switch. Only one command is active on the switch.
- To avoid system conflicts when Auto Smartports macros are applied, remove all port configuration except for 802.1x authentication.
- Do not configure port security when enabling Auto Smartports on the switch.
- If the macro conflicts with the original configuration, the macro will not apply some of the original configuration commands, or the antimacro will not remove them. (The antimacro is the portion of the applied macro that removes the macro at a link-down event.)
For example, if 802.1x authentication is enabled, you cannot remove switchport-mode access configuration. Remove the 802.1x authentication before removing the switchport mode configuration.
- A port cannot be a member of an EtherChannel when you apply Auto Smartports macros. If you use EtherChannels, disable Auto Smartports on interfaces that are members of the EtherChannels by using the no macro auto processing interface configuration command.
- The built-in macro default data VLAN is VLAN 1. The built-in macro default voice VLAN is VLAN 2. (VLAN 1 is the default data VLAN for all macros. VLAN 2 is the default voice VLAN for all macros.) If your switch uses different access, native, or voice VLANs, use the macro auto device or the macro auto execute global configuration commands to configure the desired nondefault values.
- Use the show macro auto device privileged EXEC command to display the default macros with the default parameter values, current values, and the configurable parameter list for each macro. You can also use the show shell functions privileged EXEC command to view the built-in macro default values.
- For 802.1x authentication or MAB, configure the RADIUS server to support the Cisco attribute-value (av) pair auto-smart-port=event trigger to detect non-Cisco devices.
- For stationary devices that do not support CDP, MAB, or 802.1x authentication, such as network printers, you can configure a MAC-address group with a MAC OUI-based trigger and map it to a user-defined macro containing the desired configuration.
- The switch supports Auto Smartport macros only on directly connected devices. Multiple device connections, such as hubs, are not supported. If multiple devices are connected, the macro applied is the one associated with the first device that is detected.
- If authentication is enabled on a port, the switch ignores a MAC-address trigger if authentication fails.
- The order of CLI commands within the macro and the corresponding antimacro can be different.
- Auto SmartPorts does not perform any global configuration. If the interface level Auto Smartport macros require any global configuration, you must manually add the global configuration.
Enabling Auto Smartports
Follow this procedure to enable Auto Smartports macros globally on the switch. This procedure is required. To disable Auto Smartports macros on a specific port, use the no auto global processing interface configuration command.
Beginning in privileged EXEC mode:
|
|
|
|
|---|---|---|
To return to the default setting, use the no macro auto global processing global configuration command.
You can use the show macro auto device, the show shell functions, and the show shell triggers privileged EXEC commands to display the event triggers, the built-in macros, and the built-in macro default values.
This example shows how to enable Auto Smartports on the switch and how to disable the feature on a specific interface:
Configuring Auto Smartports Default Parameter Values
The switch automatically maps from event triggers to built-in macros. You can follow this procedure to replace Auto Smartports macro default parameter values with values that are specific to your switch. This procedure is optional.
Beginning in privileged EXEC mode:
To return to the default setting, use the no macro auto device {macro name} parameter=value global configuration command.
This example shows how to view the IP phone macro parameter values and how to change the default voice VLAN to 20. When you change the default values, they are not applied on interfaces that already have applied macros. The configured values are applied at the next link-up event. Note that the exact text string was used for VOICE_VLAN. The entry is case sensitive.
Configuring Auto Smartports MAC-Address Groups
For devices such as printers that do not support neighbor discovery protocols such as CDP or LLDP, use the MAC-address-based trigger configurations for Auto Smartports. This procedure is optional and requires these steps:
- Configure a MAC-address-based trigger by using the macro auto mac-address global configuration command.
- Associate the MAC-address trigger to a built-in or a user-defined macro by using the macro auto execute global configuration command.
Beginning in privileged EXEC mode:
To delete an address group, use the no macro auto mac-address-group name global configuration command. Enter no macro auto mac-address-group name to remove the macro trigger and any associated trigger mapping to a macro defined by using the macro auto execute global configuration command. Entering no macro auto execute mac-address-group only removes the mapping of the trigger to the macro.
This example shows how to create a MAC-address-group event trigger called address_trigger and how to verify your entries:
Configuring Auto Smartports Macro Persistent
When you enable Auto Smartports on the switch, the default is that the macro configuration is applied at a link-up event and removed at a link-down event. When you enable the macro persistent feature, the configuration is applied at link-up and is not removed at link-down. The applied configuration remains, regardless of link-up or link-down events on the switch. The macro persistent feature remains configured through a reboot if the running configuration file is saved.
Follow this procedure to enable Auto Smartports macros to remain active on the switch after a link-down event. This procedure is optional.
Beginning in privileged EXEC mode:
|
|
|
|
|---|---|---|
Enable Auto Smartport macro configurations to remain on the interface on a link-down event. |
||
To disable the Auto Smartports macro persistent feature, use the no macro auto sticky global configuration command.
This example shows how to enable the Auto Smartports auto-sticky feature on the switch:
Configuring Auto Smartports Built-In Macro Options
Use this procedure to map event triggers to built-in macros and to replace the built-in macro default parameter values with values that are specific to your switch. If you need to replace default parameters values in a macro, use the macro auto device global configuration command. All commands in this procedure are optional.
Beginning in privileged EXEC mode:
This example shows how to use two built-in Auto Smartports macros for connecting Cisco switches and Cisco IP phones to the switch. This example modifies the default voice VLAN, access VLAN, and native VLAN for the trunk interface:
This example shows how to configure the remote macro with the setting for native VLAN 5.
a.![]() Configure the remote macro in the macro.txt file.
Configure the remote macro in the macro.txt file.
b.![]() Use the macro auto execute configuration command to specify the remote location for the macro file.
Use the macro auto execute configuration command to specify the remote location for the macro file.
Creating User-Defined Event Triggers
When using MAB or 802.1x authentication to trigger Auto Smartports macros, you need to create an event trigger that corresponds to the Cisco attribute-value pair (auto-smart-port=event trigger) sent by the RADIUS server. This procedure is optional.
Beginning in privileged EXEC mode:
|
|
|
|
|---|---|---|
Specify the event trigger identifier and description. The identifier should have no spaces or hyphens between words. |
||
Use the no shell trigger identifier global configuration command to delete the event trigger.
This example shows how to map a user-defined event trigger called RADIUS_MAB_EVENT to the built-in macro CISCO_AP AUTO_SMARTPORT, replace the default VLAN with VLAN 10, and how to verify the entries.
a.![]() Connect the device to a MAB-enabled switch port.
Connect the device to a MAB-enabled switch port.
b.![]() On the RADIUS server, set the attribute-value pair to auto-smart-port =RADIUS_MAB_EVENT.
On the RADIUS server, set the attribute-value pair to auto-smart-port =RADIUS_MAB_EVENT.
c.![]() On the switch, create the event trigger RADIUS_MAB_EVENT.
On the switch, create the event trigger RADIUS_MAB_EVENT.
d.![]() The switch recognizes the attribute-value pair=RADIUS_MAB_EVENT response from the RADIUS server and applies the macro CISCO_AP_AUTO_SMARTPORT.
The switch recognizes the attribute-value pair=RADIUS_MAB_EVENT response from the RADIUS server and applies the macro CISCO_AP_AUTO_SMARTPORT.
This example shows how to use the show shell triggers privileged EXEC command to view the event triggers in the switch software:
This example shows how to use the show shell functions privileged EXEC command to view the built-in macros in the switch software:
Configuring Auto Smartports User-Defined Macros
The Cisco IOS shell provides basic scripting capabilities for configuring the user-defined Auto Smartports macros. These macros can contain multiple lines and can include any CLI command. You can also define variable substitution, conditionals, functions, and triggers within the macro. This procedure is optional.
Beginning in privileged EXEC mode, follow these steps to map a user-defined event trigger to a user-defined macro.
This example shows how to map a user-defined event trigger called media player to a user-defined macro.
a.![]() Connect the media player to an 802.1x- or MAB-enabled switch port.
Connect the media player to an 802.1x- or MAB-enabled switch port.
b.![]() On the RADIUS server, set the attribute-value pair to auto-smart-port =MP_EVENT.
On the RADIUS server, set the attribute-value pair to auto-smart-port =MP_EVENT.
c.![]() On the switch, create the event trigger MP_EVENT, and enter the user-defined macro commands shown below.
On the switch, create the event trigger MP_EVENT, and enter the user-defined macro commands shown below.
d.![]() The switch recognizes the attribute-value pair=MP_EVENT response from the RADIUS server and applies the macro associated with this event trigger.
The switch recognizes the attribute-value pair=MP_EVENT response from the RADIUS server and applies the macro associated with this event trigger.
|
|
|
|---|---|
Variables that begin with the $ character are replaced with a parameter value. |
|
|
|
|
|---|---|
Configuring Static Smartports Macros
- Default Static Smartports Configuration
- Static Smartports Configuration Guidelines
- Applying Static Smartports Macros
Default Static Smartports Configuration
There are no static Smartports macros enabled on the switch.
|
|
|
|---|---|
Use this global configuration macro to enable rapid PVST+, loop guard, and dynamic port error recovery for link state failures. |
|
Use this interface configuration macro for increased network security and reliability when connecting a desktop device, such as a PC, to a switch port. |
|
Use this interface configuration macro when connecting a desktop device such as a PC with a Cisco IP Phone to a switch port. This macro is an extension of the cisco-desktop macro and provides the same security and resiliency features, but with the addition of dedicated voice VLANs to ensure proper treatment of delay-sensitive voice traffic. |
|
Use this interface configuration macro when connecting an access switch and a distribution switch or between access switches connected by using small form-factor pluggable (SFP) modules. |
|
Use this interface configuration macro when connecting the switch and a WAN router. |
|
Use this interface configuration macro when connecting the switch and a wireless access point. |
|
1.Cisco-default Smartports macros vary, depending on the software version running on your switch. |
Static Smartports Configuration Guidelines
- When a macro is applied globally to a switch or to a switch interface, all existing configuration on the interface is retained. This is helpful when applying an incremental configuration.
- If a command fails because of a syntax or a configuration error, the macro continues to apply the remaining commands. You can use the macro global trace macro-name global configuration command or the macro trace macro-name interface configuration command to apply and debug a macro to find any syntax or configuration errors.
- Some CLI commands are specific to certain interface types. If you apply a macro to an interface that does not accept the configuration, the macro fails the syntax or the configuration check, and the switch returns an error message.
- Applying a macro to an interface range is the same as applying a macro to a single interface. When you use an interface range, the macro is applied sequentially to each interface within the range. If a macro command fails on one interface, it is still applied to the remaining interfaces.
- When you apply a macro to a switch or a switch interface, the macro name is automatically added to the switch or interface. You can display the applied commands and macro names by using the show running-config user EXEC command.
Applying Static Smartports Macros
Beginning in privileged EXEC mode, follow these steps to apply a static Smartports macro:
You can only delete a global macro-applied configuration on a switch by entering the no version of each command in the macro. You can delete a macro-applied configuration on a port by entering the default interface interface-id interface configuration command.
This example shows how to display the cisco-desktop macro, to apply the macro and to set the access VLAN ID to 25 on an interface:
Displaying Auto Smartports and Static Smartports Macros
To display the Auto Smartports and static Smartports macros, use one or more of the privileged EXEC commands in Table 14-5 .
 Feedback
Feedback