Prerequisites for AVC with DNS-AS
-
You have the Cisco ONE for Access license to use AVC with DNS-AS.
-
You have enabled Multilayer Switch (MLS) Quality of Service (QoS).
-
You have maintained metadata in the authoritative DNS server and reachability exists - before you enable AVC with DNS-AS
-
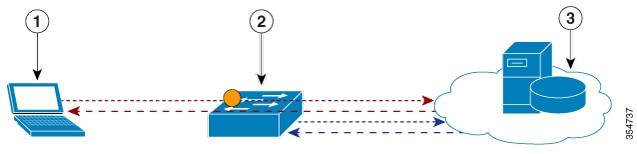
The DNS-AS client can snoop forward look-up requests originating from hosts.
-
To ensure DNS packet logging or snooping, you have attached the policy map to the interface, by using the service-policy input command.

 Feedback
Feedback