Update AWS VPC Connection Credentials
If you create a new access key and secret access key to connect to the AWS VPC, you must update the connection credentials in Security Cloud Control. To do this, first update the credentials in the AWS console. Next, update the credentials in the Security Cloud Control console by using this procedure. For more information, refer to Managing Access Keys for IAM Users (https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_access-keys.html) or Creating, Disabling, and Deleting Access Keys for Your AWS Account Root User (https://docs.aws.amazon.com/general/latest/gr/managing-aws-access-keys.html).
You cannot change the access key or secret access key from Security Cloud Control. You must manually manage the connection credentials using the AWS console or the AWS CLI console.
 Note |
If multiple AWS VPCs are onboarded to your Security Cloud Control tenant, you must update the credentials for one device at a time. |
Procedure
|
Step 1 |
Choose . |
||
|
Step 2 |
Click the Devices tab, and then click AWS VPC. |
||
|
Step 3 |
Select the AWS VPC whose connection credentials you want to update. Use the filter and search functionalities to find the required device. |
||
|
Step 4 |
Under Device Actions, click Update Credentials. |
||
|
Step 5 |
Enter the new Access Key and Secret Access Key, which you want to use to connect to the AWS VPC. |
||
|
Step 6 |
Click Update.
|
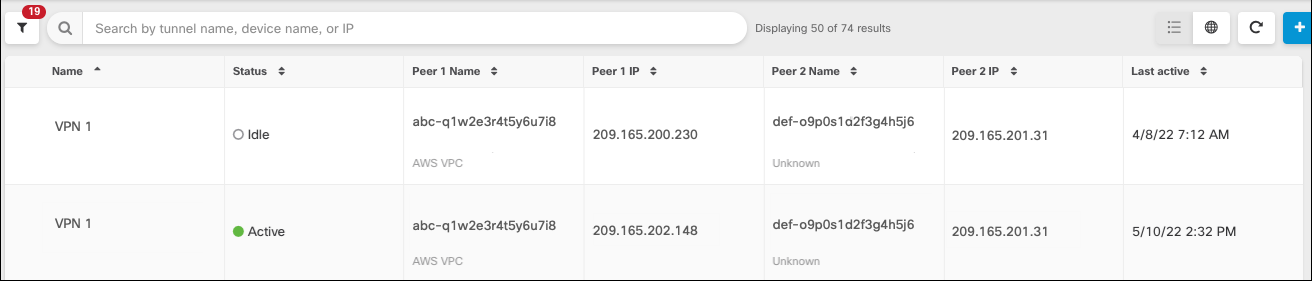
 in combination with the search field to focus your search of VPN tunnels presented in the VPN tunnel diagram.
in combination with the search field to focus your search of VPN tunnels presented in the VPN tunnel diagram.



 in the
in the  in the
in the  Feedback
Feedback