Information about High Availability
A method for deploying two Cisco CSR 1000v in a redundant pair with failover between them, is summarized below. Also see How to Configure High Availability for further details.
Configuring High Availability: Summary
-
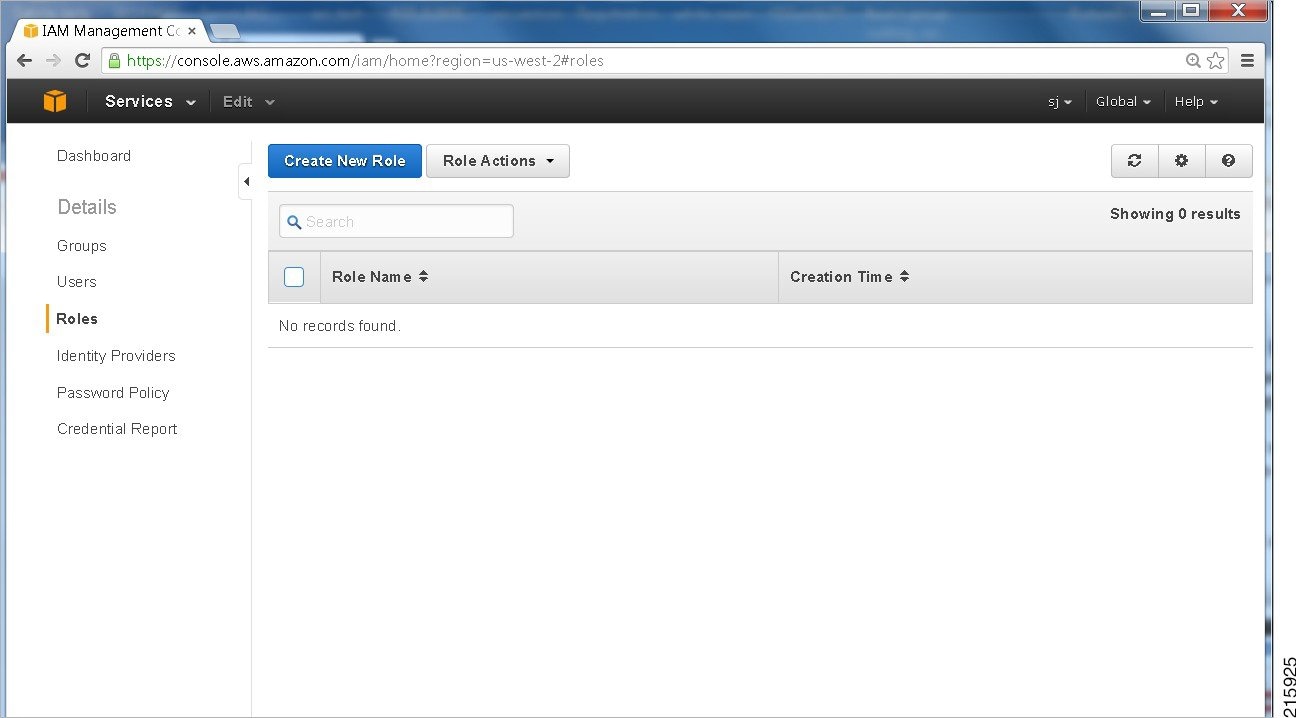
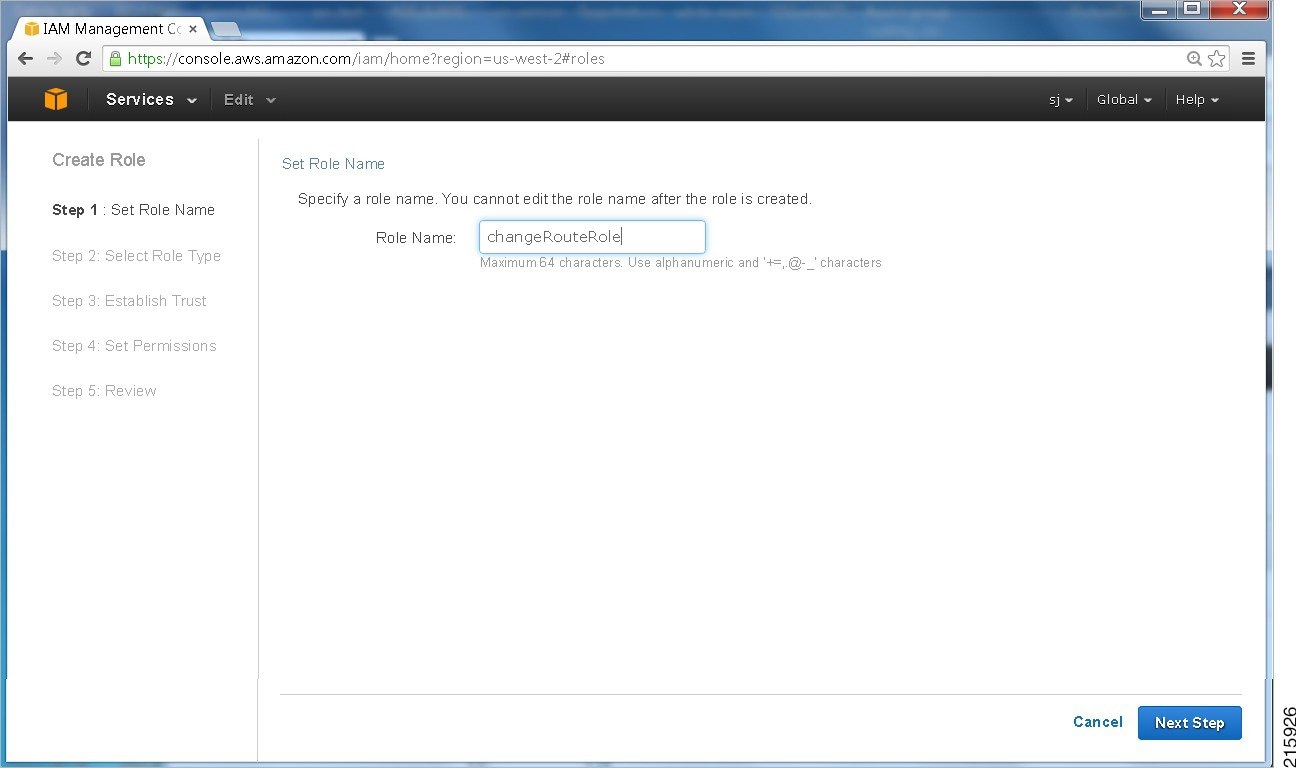
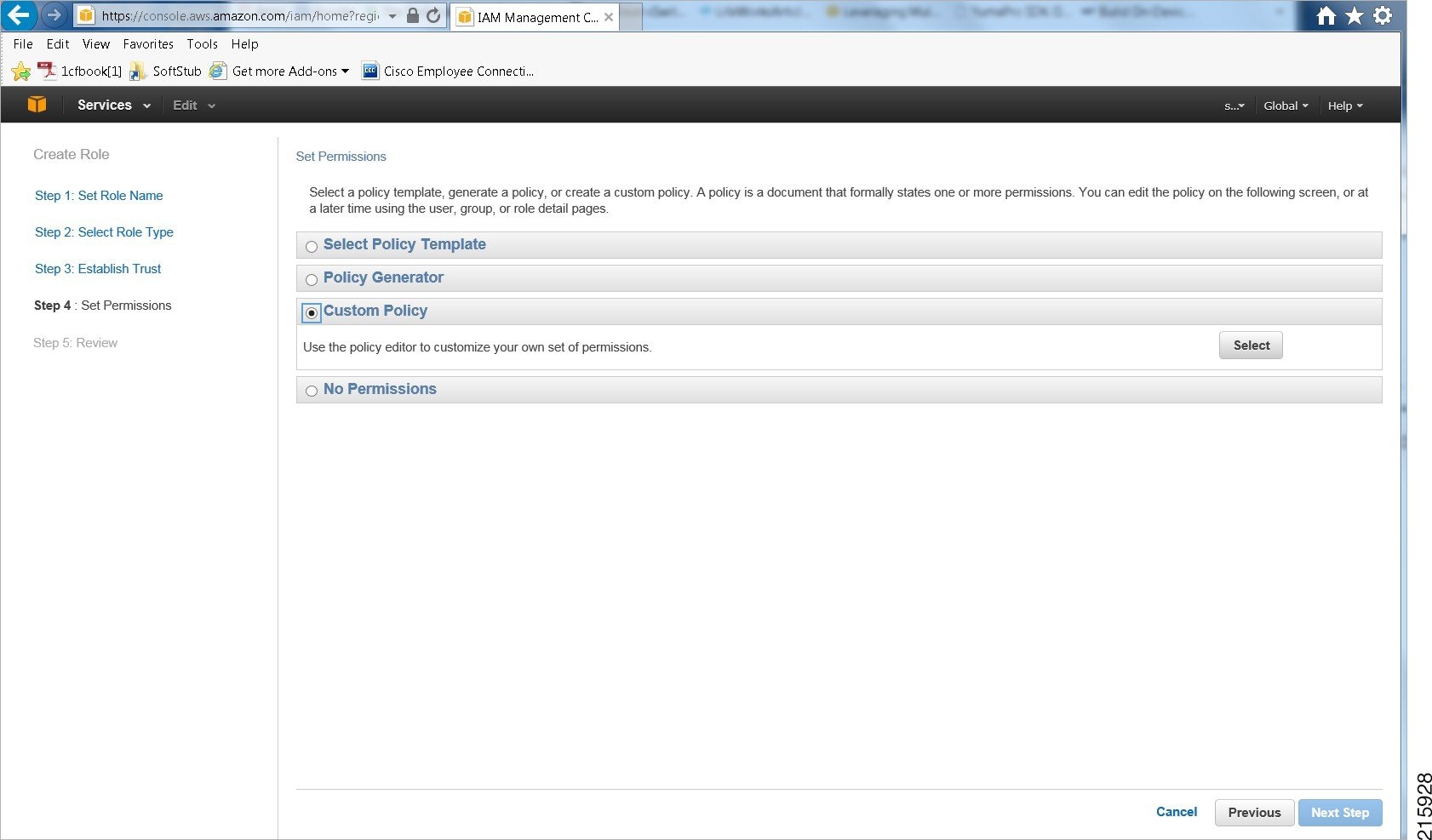
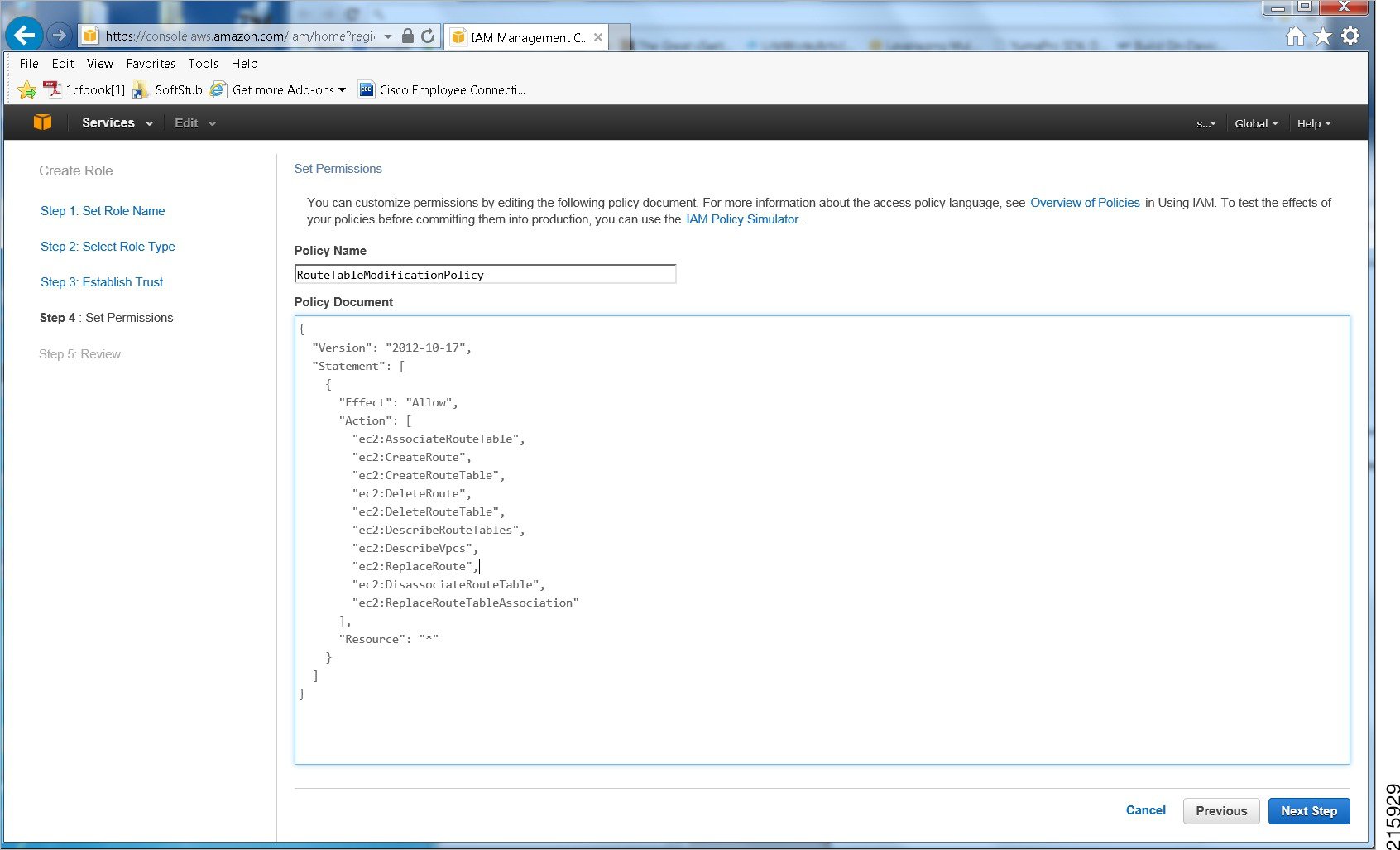
Create an AWS Identity and Access Management (IAM) role to be able to access the AWS APIs.
-
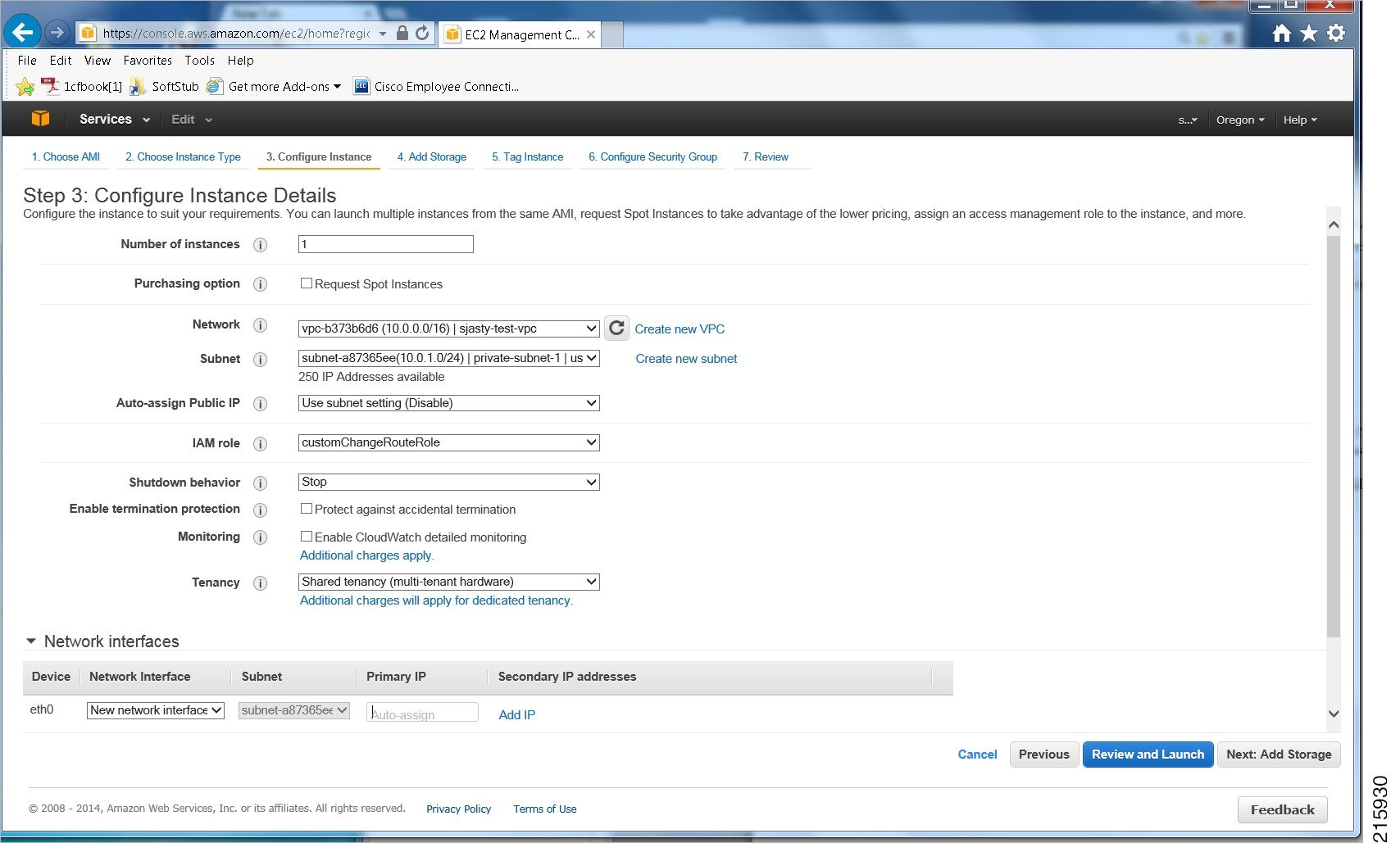
Create an AWS VPC and launch each Cisco CSR1000V into the VPC with an Amazon EC2 IAM role.
-
(Cisco IOS XE Everest 16.6.1 or later) Enable the AX or SEC license, using BFD.
(Cisco IOS XE Everest 16.5.1 or earlier) Enable the AX license, using BFD.
-
Configure the CSRs to reach the internet and access EC2 AWS API servers.
-
Configure a GRE tunnel between the CSR1000V instances and enable Bi-directional Forwarding Detection (BFD) and a routing protocol (EIGRP or BGP) on the GRE tunnel between the routers, for peer failure detection.
-
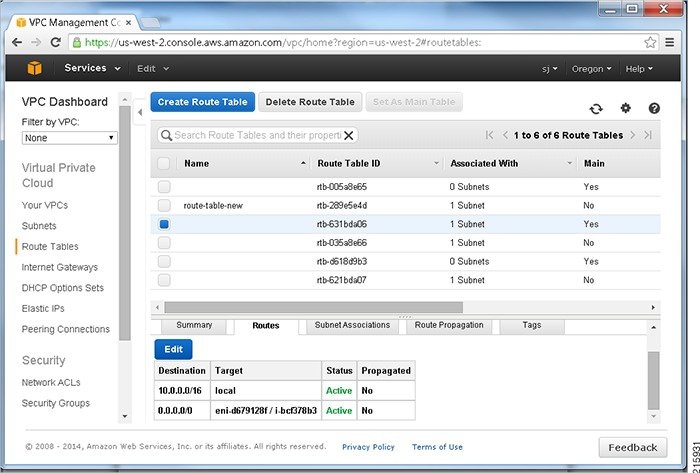
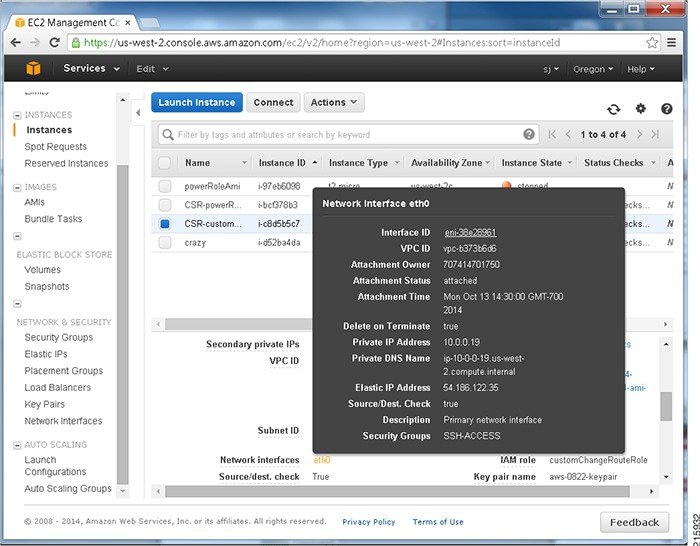
Note the route table ID and network interface ID.
-
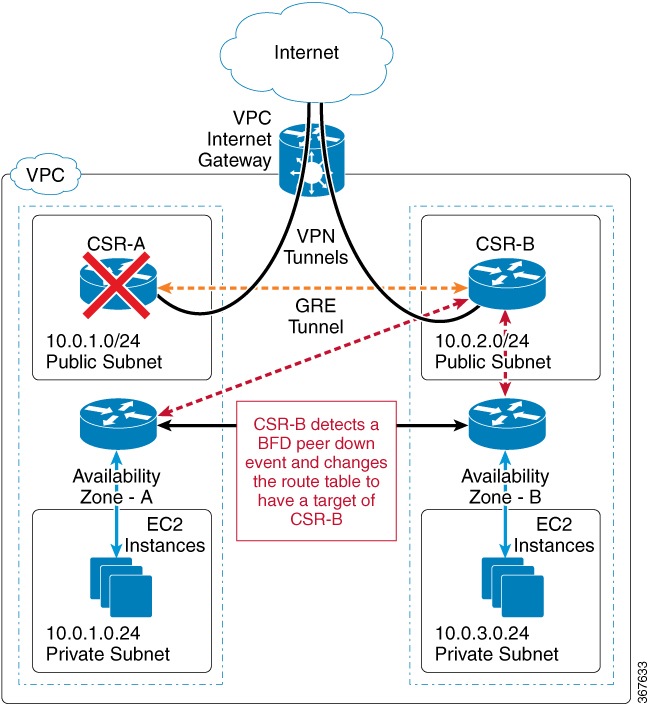
(Cisco IOS XE 3.16 or earlier) Monitor AWS HA errors such as BFD peer down events and specify the routing changes parameters: Route-table-id, Network-interface-id and CIDR range, by configuring each CSR1000V with an Embedded Event Manager (EEM) applet. When a BFD peer down event is detected, the applet uses the AWS EC2 VPC API to modify the VPC route table to redirect traffic around the failure.

Note
For private subnets, do not use the IP address 10.0.3.0/24—this is used internally on the Cisco CSR1000V for High Availability. The Cisco CSR1000V needs to have public internet accessibility to make REST API calls that change the AWS route table.
-
(Cisco IOS XE Denali16.3.1a or later) Monitor AWS HA errors such as BFD peer down events and specify the routing changes to Route-table-id, Network-interface-id and CIDR by configuring each CSR1000V using the cloud provider aws command. When a BFD peer down event is detected, routing changes are made to the Route-table-id, Network-interface-id and CIDR range and the VPC route table is modified to redirect traffic around the failure.
Further Information
For futher information about configuring HA for CSR1000V on AWS, see CSR1000V HA Redundancy Deployment Guide on Amazon AWS.
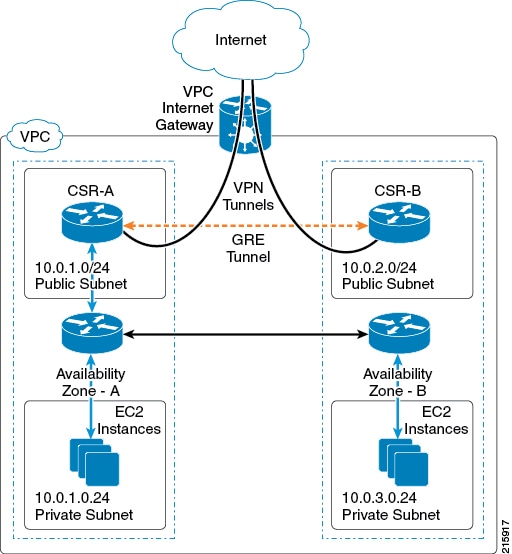
Initial Topology
The initial topology and traffic flow are shown in the following figure, before performing the procedure: How to Configure High Availability.
 Note |
The procedure How to Configure High Availability shows how to configure high availability (VPC Gateway Redundancy) for a VPN gateway configuration in a single availability zone. For further examples, see the Deploying the Cisco Cloud Services Router 1000V Series in Amazon Web Services, Design and Implementation Guide . |
Ingress and egress traffic is initially forwarded through CSR-A.
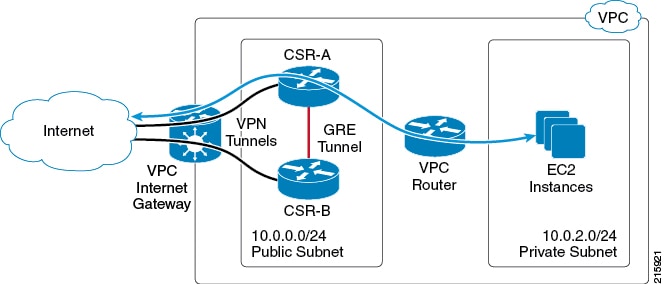
Each CSR has a primary Ethernet interface (GigabitEthernet1) that is assigned to the public subnet. The public subnet has a VPC route table with a default route target of the Internet gateway. Both CSR-A and CSR-B are launched in the same public subnet.
Each CSR also has a VPN tunnel to the Internet. These tunnels typically terminate at another VPN device located on the enterprise network or another VPC.
To support high availability , a GRE tunnel is configured between the local CSRs, which allows the CSRs to exchange BFD control packets that are used for peer failure detection.
The EC2 instances reside in a private subnet, Private Subnet (10.0.2.0/24), in the topology diagram. If the CSR is not directly connected to this private subnet, it is recommended to add a static route for the private subnet to each CSR. This static route points to the address of the VPC router on the public subnet. This address will always be the first usable address of a subnet. For example, the VPC router address for the subnet 10.0.0.0/24 will be 10.0.0.1.
EIGRP is used as the routing protocol, though other routing protocols could be used. The primary purpose of the routing protocol is to register as a BFD client. BFD requires at least one client protocol before it will initiate neighbor discovery. An additional benefit of the GRE tunnel and the routing protocol is that they can be used to establish a back-up path in case of VPN tunnel failures.
The EC2 private subnet has its own VPC route table. The default route for this subnet will have a target of the public subnet network interface (GigabitEthernet1) of one of the CSRs. Because the VPC route table only allows for one active target per route, only one CSR is in the egress traffic path for the subnet. Ingress traffic flow over the VPN tunnels is determined by the remote VPN devices. This means that CSR-B may be the active ingress path or that load sharing is performed between CSR-A and CSR-B.
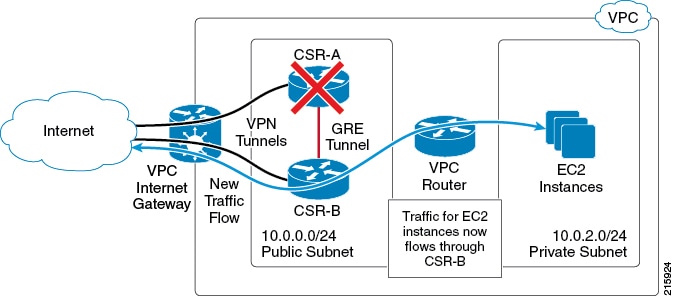
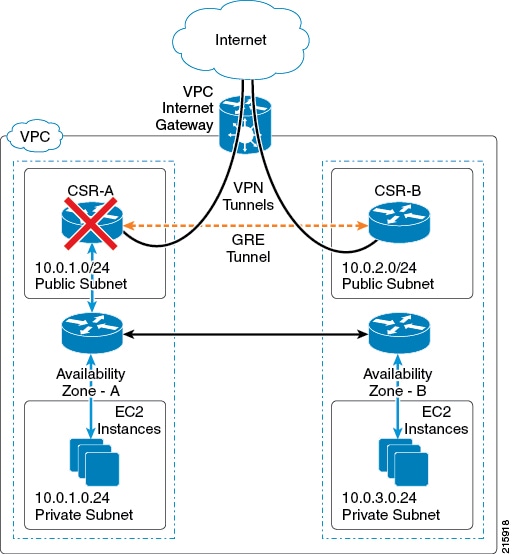
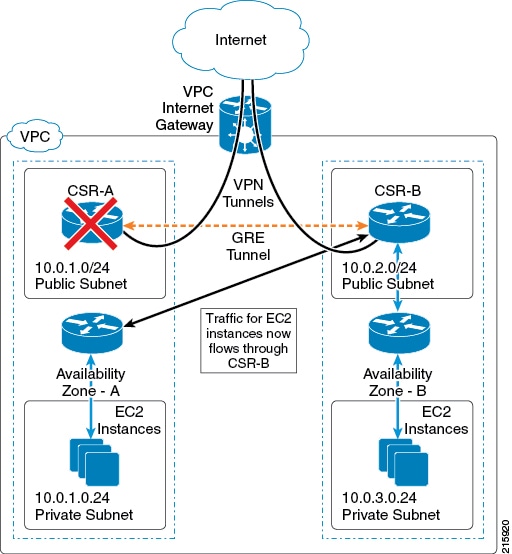
The next figure shows the new traffic flow that occurs after you have configured the steps shown in the procedure How to Configure High Availability and after a BFD peer down event. The modified VPC route table causes traffic to egress through CSR-B.
 Feedback
Feedback