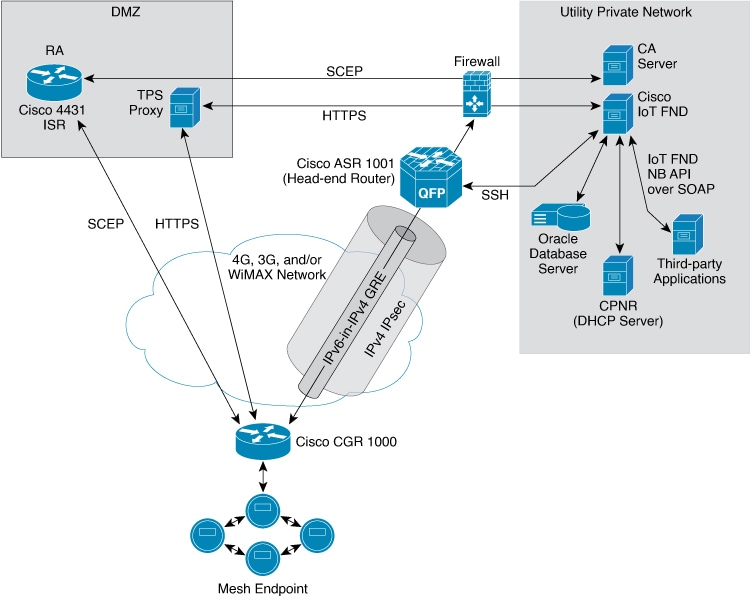
The TPS proxy logs all HTTPS inbound and outbound requests in the TPS proxy log file located at /opt/cgms-tpsproxy/log/tpsproxy.log
The following entry in the TPS proxy tpsproxy.log file defines inbound requests for a CGR:
73: cgr-centos57: May 21 2014 01:05:20.513 -0700: %CGMS-6-UNSPECIFIED:
%[ch=TpsProxyServlet-49dc423f][eid=CGR1240/K9+JAF1732ARCJ][ip=192.168.201.5]
[sev=INFO][tid=qtp46675819-29]: Inbound proxy request from [192.168.201.5]
with client certificate subject [CN=CGRJAF1732ARCJ.example.com,
SERIALNUMBER=PID:CGR1240/K9 SN:JAF1732ARCJ]
This message entry in the TPS proxy tpsproxy.log file indicates that the TPS successfully forwarded the message to IoT FND:
74: cgr-centos57: May 21 2014 01:05:20.564 -0700: %CGMS-6-UNSPECIFIED:
%[ch=TpsProxyServlet-49dc423f][sev=INFO]
[tid=com.cisco.cgms.tpsproxy.TpsProxyServlet-49dc423f-22]:
Completed inbound proxy request from [192.168.201.5]
with client certificate subject [CN=CGRJAF1732ARCJ.example.com,
SERIALNUMBER=PID:CGR1240/K9 SN:JAF1732ARCJ]
The following entry in the IoT FND server log file identifies the TPS proxy:
Request came from proxy
Using forwarded client subject (CN=cg-cgr-1, SERIALNUMBER=PID:CGR1240/K9 SN:JSJ15220047)
for authentication
The following entry in the TPS proxy tpsproxy.log file defines outbound requests:
%CGMS-6-UNSPECIFIED: %[ch=TpsProxyOutboundHandler][ip=192.168.205.5]
[sev=INFO][tid=qtp257798932-15]: Outbound proxy request from [192.168.205.5]
to [192.168.201.5:8443]
The following entry in the IoT FND server log file identifies the HTTPS connection:
Using proxy at 192.168.201.6:9122 to send to
https://192.168.201.4:8443/cgdm/mgmt commands:



 Feedback
Feedback