- Overview to Prime Performance Manager
- Managing Gateways and Units Using the CLI
- Managing the Web Interface
- Importing Devices From Other Cisco Prime Applications
- Discovering Devices With Prime Performance Manager
- Managing Users and Security
- Managing Reports, Dashboards, and Views
- Setting Up Reports for Specialized Technologies
- Managing Devices
- Managing Network Alarms and Events
- Creating and Managing Thresholds
- Displaying System Properties, Statuses, Messages, and Logs
- Managing Gateways and Units
- Managing High Availability
- Configuring Prime Performance Manager for Firewalls
- Managing Multi-Tenant Services
- Pushing Prime Performance Manager Data to Other Applications
- Backing Up and Restoring Prime Performance Manager
- Prime Performance Manager and IPv6
- Prime Performance Manager Commands
- Predefined Thresholds
- Compliance
Cisco Prime Performance Manager User Guide, 1.7
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- September 28, 2015
Chapter: Configuring Prime Performance Manager for Firewalls
Configuring Prime Performance Manager for Firewalls
The following topics tell you how to configure Prime Performance Manager for firewalls:
Gateway-to-Unit Connectivity
Prime Performance Manager runs on standard IP-connected networks and has the flexibility to adapt to different network environments including firewalls and Secure Sockets Layer (SSL) connectivity. Prime Performance Manager can run in each of these environments individually, or in any combination of networking environments.
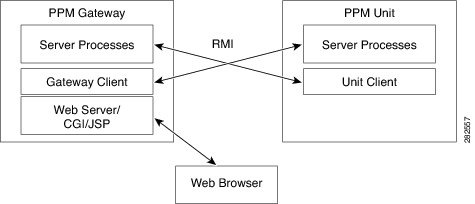
Figure 15-1 shows the communication elements between the Prime Performance Manager gateway and units. Communication elements include:
- Two-way Remote Method Invocation (RMI) between gateway and unit processes. The gateway and unit send requests and receive responses to and from each other. Each can send unsolicited notifications. For example, if a unit detects a change in a device state, it sends a notification to the gateway, and the gateway updates its database.
- One-way HTTP communication between a web browser and the gateway embedded web server, using the request/response model.
Figure 15-1 Prime Performance Manager Communication
|
|
|
||
|
|
|
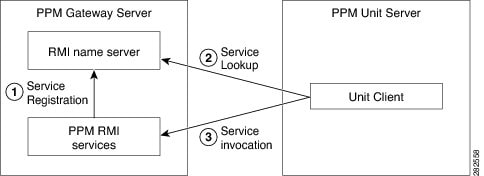
RMI is a Java-based technology that allows one Java application to communicate with another Java application (usually residing on different hosts) using remote method invocation. RMI manages method parameters and return values using Java object serialization. RMI uses TCP as the default communication mechanism.
The following RMI components run on Prime Performance Manager gateways and units:
When the Prime Performance Manager gateway starts, the RMI services register with the RMI name server. These registered RMI services have one single published IP address.
When the Prime Performance Manager unit starts, it establishes a TCP connection to the RMI name server and performs a service lookup. The RMI name server returns the published IP address for the Prime Performance Manager RMI services. The unit then establishes another TCP connection to the published IP address of Prime Performance Manager RMI services for unit client and server communication.
Configuring Gateways and Units for Firewalls
Configuring Prime Performance Manager for firewalls includes communication through firewalls between:
Configurations for each are provided in the following topics:
- Configuring Web Client and Gateway Communication
- Configuring Gateway and Unit Communication
- Configuring Unit and Device Communication
Configuring Web Client and Gateway Communication
If a gateway and unit are installed on the same server and you only want to enable communication from web clients to the gateway, open the firewall WEB_PORT port. No additional changes are needed. By default, WEB_PORT is 4440. To change it to a different port, you can use the ppm jspport command. See ppm javaver, for more information.
Configuring Gateway and Unit Communication
To enable the Prime Performance Manager gateway to communicate with units through a firewall, provision the firewall to allow Prime Performance Manager packets to pass through it. Ports used by Prime Performance Manager are configured in the System.properties file. System.properties is located in /opt/CSCOppm-gw/properties or /opt/CSCOppm-unit/properties. If you installed Prime Performance Manager in a different directory, the file resides in that directory.
Table 15-1 lists the Prime Performance Manager ports and firewall requirements.
|
|
|
|---|---|
The port on which the RMI naming server listens. You must specify a port number; 0 is not allowed. |
|
The port on which the data service listens. If you specify 0, Prime Performance Manager uses a random available port, 1024 and above. Prime Performance Manager maintains the chosen port until the next server restart. 45751 and 55751 are good alternate ports for gateways and units respectively. |
|
The port on which the log in service listens. If you specify 0, Prime Performance Manager uses a random available port, 1024 and above. Prime Performance Manager maintains the chosen port until the next server restart. 45752 and 55752 are good alternate ports for gateways and units respectively. |
|
The port on which the Prime Performance Manager gateway listens. You must specify a port number; 0 is not allowed. To change it to a different port, you can use the ppm webport command. See ppm javaver, for more information. |
|
| The port on which the Prime Performance Manager server listens for RMI callbacks (unsolicited notifications):
Because a gateway server can connect to multiple units, specify a range if more than one unit is defined in the deployment. Because a unit connects to only one gateway, you only need to specify a single port. |
|
To provision the firewall for gateway and unit communications:
Step 1![]() Identify the TCP ports that you want to use for two-way TCP connections between the gateway and unit and gateway and web client. See Table 15-1 .
Identify the TCP ports that you want to use for two-way TCP connections between the gateway and unit and gateway and web client. See Table 15-1 .
Step 3![]() Navigate to the directory containing the System.properties file.
Navigate to the directory containing the System.properties file.
If you installed Prime Performance Manager in the default directory, System.properties is located in the /opt/CSCOppm-gw/properties or /opt/CSCOppm-unit/properties directory.
If you installed Prime Performance Manager in a different location, specify the path where you installed Prime Performance Manager in place of the default (/opt) path.
Step 4![]() Back up the System.properties file.
Back up the System.properties file.

Step 5![]() Use a text editor to modify the DATASERVER_PORT, LOGINSERVER_PORT, and CLIENT_PORT gateway and unit ports as indicated below. See Table 15-1 for port descriptions and values.
Use a text editor to modify the DATASERVER_PORT, LOGINSERVER_PORT, and CLIENT_PORT gateway and unit ports as indicated below. See Table 15-1 for port descriptions and values.
Gateway modified for firewall:
Step 6![]() Modify the device configuration files with the selected port numbers.
Modify the device configuration files with the selected port numbers.
On Cisco devices, you can use extended access lists to allow the chosen TCP port numbers to pass between the appropriate interface(s). Assuming a single device separates the Prime Performance Manager gateway and unit servers, you can use the following extended access list:
These entries allow data to flow between the gateway and unit that initiated the session. Without these entries, units cannot access the gateway server.
Here is an access list entry to allow the unit and web browser connections to the gateway:
Here is an access list to allow gateway connections to the unit:
Step 7![]() Restart the gateway to use the new TCP ports. As the root user, enter:
Restart the gateway to use the new TCP ports. As the root user, enter:
The gateway and collocated unit processes restart using the new ports.
Step 8![]() If the unit properties changed, restart the units:
If the unit properties changed, restart the units:
Both access list examples allow established TCP connections. When a unit or gateway establishes a TCP connection to the other end, it uses a fixed destination port. However, the source port from the initiating party is random. The established keyword allows a returning TCP packet to go back to the random initiating source port.
Configuring Unit and Device Communication
For units to communicate to devices through a firewall, ports used by the connection protocol used to connect to the device must be open. Table 15-2 lists the default ports. However, other ports might be assigned when you configure the credential. For information about adding device credentials, see Managing Device Credentials.
|
|
|
|---|---|
 Feedback
Feedback