- SIP Features Roadmap
- Overview of SIP
- Basic SIP Configuration
- Achieving SIP RFC Compliance
- Configuring SIP Call-Transfer Features
- Configuring SIP Message, Timer, and Response Features
- Configuring SIP AAA Features
- Configuring SIP Connection-Oriented Media, Forking, and MLPP Features
- Configuring SIP Bind Features
- Configuring SIP DTMF Features
- Configuring SIP Support for SRTP
- Configuring SIP Support for Hookflash
- Configuring SIP ISDN Support Features
- Transparent Tunneling of QSIG and Q.931 over SIP TDM Gateways and SIP-SIP Cisco Unified Border Elements
- Configuring SIP RSVP Features
- Configuring SIP QoS Features
- Configuring SIP MWI Features
- Verifying and Troubleshooting SIP Features
- Contents
- Prerequisites for SIP AAA
- Restrictions for SIP AAA
- Information About SIP AAA
Configuring SIP AAA Features
This chapter describes how to configure the following SIP AAA features:
•![]() Configurable Screening Indicator (handled in this document as a subset of SIP - Enhanced Billing Support for Gateways)
Configurable Screening Indicator (handled in this document as a subset of SIP - Enhanced Billing Support for Gateways)
•![]() RADIUS Pre-authentication for Voice Calls
RADIUS Pre-authentication for Voice Calls
•![]() SIP - Enhanced Billing Support for Gateways
SIP - Enhanced Billing Support for Gateways
•![]() SIP: Gateway HTTP Authentication Digest
SIP: Gateway HTTP Authentication Digest
Feature History for Configurable Screening Indicator1
|
|
|
12.2(2)XB |
This feature was introduced. |
12.2(8)T |
This feature was integrated into this release. |
Feature History for RADIUS Pre-authentication for Voice Calls
|
|
|
12.2(11)T |
This feature was introduced. |
Feature History for SIP - Enhanced Billing Support for SIP Gateways
|
|
|
12.2(2)XB |
This feature was introduced. |
12.2(8)T |
This feature was integrated into this release. |
12.2(11)T |
This feature was implemented on additional platforms. |
Feature History for SIP: Gateway HTTP Authentication Digest
|
|
|
12.3(8)T |
This feature was introduced. |
Finding Support Information for Platforms and Cisco Software Images
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•![]() How to Configure SIP AAA Features
How to Configure SIP AAA Features
•![]() Configuration Examples for SIP AAA Features
Configuration Examples for SIP AAA Features
Prerequisites for SIP AAA
All SIP AAA Features
•![]() Establish a working IP network. For information about configuring IP, see Cisco IOS IP Command Reference, Release 12.3
Establish a working IP network. For information about configuring IP, see Cisco IOS IP Command Reference, Release 12.3
•![]() Configure VoIP. For information about configuring VoIP, see the following:
Configure VoIP. For information about configuring VoIP, see the following:
–![]() Cisco IOS Voice Configuration Library, Release 12.4T
Cisco IOS Voice Configuration Library, Release 12.4T
–![]() Cisco IOS Voice Command Reference
Cisco IOS Voice Command Reference
–![]() Enhancements to the Session Initiation Protocol for VoIP on Cisco Access Platforms
Enhancements to the Session Initiation Protocol for VoIP on Cisco Access Platforms
•![]() Ensure that the gateway has voice functionality configured for SIP.
Ensure that the gateway has voice functionality configured for SIP.
RADIUS Pre-authentication for Voice Calls Feature
•![]() Ensure that you have an application that supports preauthentication.
Ensure that you have an application that supports preauthentication.
•![]() Set up preauthentication profiles and have them running on a RADIUS-based PPM server in your network.
Set up preauthentication profiles and have them running on a RADIUS-based PPM server in your network.
•![]() Enable gateway accounting using the gw-accounting command. All call-accounting information must be forwarded to the server that is performing preauthentication. Accounting stop packets must be sent to this server so that call billing is ended when calls are disconnected from the gateway. In addition, authentication and accounting start packets are needed to enable other features, such as virtual private dialup network (VPDN).
Enable gateway accounting using the gw-accounting command. All call-accounting information must be forwarded to the server that is performing preauthentication. Accounting stop packets must be sent to this server so that call billing is ended when calls are disconnected from the gateway. In addition, authentication and accounting start packets are needed to enable other features, such as virtual private dialup network (VPDN).

Note ![]() For information on setting up the preauthentication profiles, see the Cisco IOS Security Command Reference.
For information on setting up the preauthentication profiles, see the Cisco IOS Security Command Reference.
For information on Cisco RPMS, see the Cisco Resource Policy Management System 2.0.
For standards supporting RADIUS-based PPM servers, see RFC 2865, Remote Authentication Dial In User Service (RADIUS).
SIP: Gateway HTTP Authentication Digest Feature
•![]() Implement a Cisco IOS SIP gateway that supports SIP.
Implement a Cisco IOS SIP gateway that supports SIP.
•![]() Implement a configuration that supports SIP.
Implement a configuration that supports SIP.
•![]() Implement an authentication configuration for the gateway to respond to authentication challenges for requests that it originates.
Implement an authentication configuration for the gateway to respond to authentication challenges for requests that it originates.
Restrictions for SIP AAA
All SIP AAA Features
•![]() If Cisco Resource Policy Management System (RPMS) is used as the RADIUS-based PPM server, it must be Version 2.0 or a later release.
If Cisco Resource Policy Management System (RPMS) is used as the RADIUS-based PPM server, it must be Version 2.0 or a later release.
•![]() In SIP environments, if you want the Cisco SIP proxy server to generate preauthentication queries, you must run Cisco SPS 2.0 or a later version.
In SIP environments, if you want the Cisco SIP proxy server to generate preauthentication queries, you must run Cisco SPS 2.0 or a later version.
SIP: Gateway HTTP Authentication Digest Via SIP UA Feature
•![]() SIP Register is supported only on platforms with digital trunk type ports.
SIP Register is supported only on platforms with digital trunk type ports.
Information About SIP AAA
AAA features for SIP provide the following benefits:
•![]() RADIUS preauthentication allows wholesalers to accept or reject calls to enforce SLAs before calls are connected, thereby conserving gateway resources.
RADIUS preauthentication allows wholesalers to accept or reject calls to enforce SLAs before calls are connected, thereby conserving gateway resources.
•![]() Call admission control prevents call connections when resources are unavailable.
Call admission control prevents call connections when resources are unavailable.
•![]() Extended dial plan features enable the call service type to be determined from preauthentication request data, simplifying dial plan entries.
Extended dial plan features enable the call service type to be determined from preauthentication request data, simplifying dial plan entries.
•![]() Universal gateways provide other specific benefits:
Universal gateways provide other specific benefits:
–![]() Flexibility in deploying new services and adapting to changes in the business environment
Flexibility in deploying new services and adapting to changes in the business environment
–![]() Cost savings through reduction of total number of ports required to provide different services
Cost savings through reduction of total number of ports required to provide different services
–![]() Optimized utilization of access infrastructure by supporting more services during off-peak hours
Optimized utilization of access infrastructure by supporting more services during off-peak hours
–![]() Flexibility in access network engineering by leveraging dial infrastructure to handle both dial and voice
Flexibility in access network engineering by leveraging dial infrastructure to handle both dial and voice
To configure AAA features for SIP, you should understand the following concepts:
•![]() RADIUS Pre-authentication for Voice Calls
RADIUS Pre-authentication for Voice Calls
•![]() SIP - Enhanced Billing Support for Gateways
SIP - Enhanced Billing Support for Gateways
•![]() SIP: Gateway HTTP Authentication Digest
SIP: Gateway HTTP Authentication Digest
RADIUS Pre-authentication for Voice Calls
This section explains how to configure the AAA RADIUS communication link between a universal gateway and a RADIUS-based PPM server for RADIUS preauthentication.
Information about an incoming call is relayed through the gateway to the RADIUS-based PPM server in the network before the call is connected. The RADIUS-based PPM server provides port policy management and preauthentication by evaluating the call information against contracted parameter levels in SLAs. If the call falls within SLA limits, the server preauthenticates the call and the universal gateway accepts it. If the server does not authorize the call, the universal gateway sends a disconnect message to the public network switch to reject the call. The available call information includes one or more of the following:
•![]() DNIS number, also referred to as the called number.
DNIS number, also referred to as the called number.
•![]() CLID number (calling line identification number), also referred to as the calling number.
CLID number (calling line identification number), also referred to as the calling number.
•![]() Call type, also referred to as the bearer capability.
Call type, also referred to as the bearer capability.
•![]() IP address of the originating domain.
IP address of the originating domain.
•![]() Interzone ClearToken (IZCT) information, which contains the origination gatekeeper zone name for intradomain calls or the origination domain border gatekeeper zone name for interdomain calls. Whenever IZCT information is available, it is used to preauthenticate leg-3 H.323 VoIP calls.
Interzone ClearToken (IZCT) information, which contains the origination gatekeeper zone name for intradomain calls or the origination domain border gatekeeper zone name for interdomain calls. Whenever IZCT information is available, it is used to preauthenticate leg-3 H.323 VoIP calls.

Note ![]() To enable IZCT, use the security izct password command on the gatekeeper. For multiple gatekeeper zones, use the lrq forward-queries command.
To enable IZCT, use the security izct password command on the gatekeeper. For multiple gatekeeper zones, use the lrq forward-queries command.
For information on IZCT configuration, see Inter-Domain Gatekeeper Security Enhancement, Release 12.2(4)T.
A timer monitors the preauthentication query in case the RADIUS-based PPM server application is unavailable or slow to respond. If the timer expires before an acceptance or rejection is provided, the universal gateway rejects the call.
The RADIUS Pre-authentication for Voice Calls feature supports the use of RADIUS attributes that are configured in RADIUS preauthentication profiles to specify preauthentication behavior. These attributes can also be used, for instance, to specify whether subsequent authentication should occur and, if so, what authentication method should be used.
The commands in this section are used for both leg 1 calls (calls from a PSTN that enter an incoming, or originating, gateway) and leg 3 calls (calls that exit the IP network to an outgoing, or terminating, gateway). The use of optional commands depends on individual network factors.

Note ![]() Before configuring AAA preauthentication, you must make sure that the supporting preauthentication application is running on a RADIUS-based PPM server in your network, such as a Cisco RPMS. You must also set up preauthentication profiles on the RADIUS-based PPM server. For full information on AAA, see the Cisco IOS Security Configuration Guide.
Before configuring AAA preauthentication, you must make sure that the supporting preauthentication application is running on a RADIUS-based PPM server in your network, such as a Cisco RPMS. You must also set up preauthentication profiles on the RADIUS-based PPM server. For full information on AAA, see the Cisco IOS Security Configuration Guide.
The RADIUS Pre-authentication for Voice Calls feature provides the means to evaluate and accept or reject call setup requests for both voice and dial calls received at universal gateways. This process is known as preauthentication. The feature also optionally allows voice calls to bypass this evaluation.
With universal gateways, voice customers and dial customers contend for the same gateway resources. This competition can present problems for IP service wholesalers who lease their IP services to various customers such as Internet service providers (ISPs), Internet telephony service providers (ITSPs), and telephony application service providers (T-ASPs). Wholesalers need a way to implement and enforce with these customers service-level agreements (SLAs) that describe the levels of connectivity, performance, and availability that they guarantee to provide. The RADIUS Pre-authentication for Voice Calls feature allows a wholesaler to determine whether a call is within SLA limits before gateway resources are dedicated to terminating the call.
With RADIUS preauthentication enabled, end customers from over-subscribed service providers are prevented from consuming ports that exceed the number allotted to their service provider in its SLA. If the call is accepted in the preauthentication step, it proceeds to full dial authentication and authorization or to voice dial-peer matching and voice session application authentication and authorization.
RADIUS preauthentication uses a RADIUS-based port-policy management (PPM) server, such as the Cisco Resource Policy Management System (RPMS), to interpret and enforce universal PPM and preauthentication SLAs. RADIUS provides the communication link between the PPM server and universal gateways.
Customer profiles are defined in the PPM server with information from the SLA. Then, when a call is received at the universal gateway, the server determines which specific customer SLA policy to apply to the call on the basis of information associated with the call. For example, calls can be identified as either dial or voice on the basis of the called number (also called the dialed number identification service number or DNIS). Then the PPM server might be set up to allow only a certain number of dial calls. When a new dial call is received, it is rejected if adding it to the count makes the count exceed the number of dial calls stipulated in the SLA.
Calls that are accepted by the PPM server continue with their normal call setup sequences after preauthentication. The response from the PPM server is returned to the calling entity—such as an ISDN or SIP call signaling interface—which then proceeds with the regular call flow. Calls that are rejected by the PPM server follow the given call model and apply the error codes or rejection reasons that are specified by the signaling entity.
SIP-Based Voice Termination
In Figure 62, a voice call from a SIP telephone or SIP terminal is sent from an ITSP to a wholesaler.The Cisco SIP proxy server (Cisco SPS) chooses the appropriate universal gateway to which the SIP INVITE is forwarded, on the basis of its own routing mechanism. In Step 3, Cisco SPS makes a preauthentication query to the RPMS-based PPM server. Cisco SPS locks out calls that are rejected by the RPMS-based PPM server. In Step 5, the universal gateway makes a preauthentication reservation request to the RPMS-based PPM server, which locks in the resources to handle the call.

Note ![]() This scenario requires Cisco SPS 2.0.
This scenario requires Cisco SPS 2.0.
Figure 62 SIP-Based Voice Termination
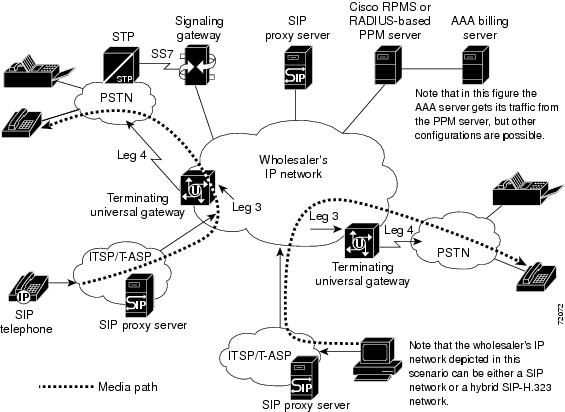
The call flow is as follows:
1. ![]() A SIP INVITE is sent from an end user's PC to an ITSP SIP proxy server.
A SIP INVITE is sent from an end user's PC to an ITSP SIP proxy server.
2. ![]() The ITSP's SIP proxy server forwards the SIP INVITE to a Cisco SPS at a wholesaler or ISP.
The ITSP's SIP proxy server forwards the SIP INVITE to a Cisco SPS at a wholesaler or ISP.
3. ![]() Preauthentication—The Cisco SPS sends a preauthentication query to the RADIUS-based PPM server, which locates the appropriate SLA and makes sure that the call is within the SLA limits. If the call is outside the limits, the call is rejected and Cisco SPS responds to the sender with an "Error code 480 - Temporarily not available" message. Cisco SPS interaction with the RADIUS-based PPM server is optional and requires Cisco SPS version 2.0 or a later release. If you are not using Cisco SPS 2.0, the gateway makes the preauthentication query to the RADIUS-based PPM server if it has been configured to do so.
Preauthentication—The Cisco SPS sends a preauthentication query to the RADIUS-based PPM server, which locates the appropriate SLA and makes sure that the call is within the SLA limits. If the call is outside the limits, the call is rejected and Cisco SPS responds to the sender with an "Error code 480 - Temporarily not available" message. Cisco SPS interaction with the RADIUS-based PPM server is optional and requires Cisco SPS version 2.0 or a later release. If you are not using Cisco SPS 2.0, the gateway makes the preauthentication query to the RADIUS-based PPM server if it has been configured to do so.
4. ![]() Gateway selection—If the preauthentication request is accepted, the Cisco SPS uses its routing logic to determine the appropriate terminating universal gateway to which it should forward the INVITE.
Gateway selection—If the preauthentication request is accepted, the Cisco SPS uses its routing logic to determine the appropriate terminating universal gateway to which it should forward the INVITE.
5. ![]() Call admission control—If the preauthentication request is accepted, the terminating universal gateway checks its configured call admission control limits. If the call is outside the limits, the call is rejected.
Call admission control—If the preauthentication request is accepted, the terminating universal gateway checks its configured call admission control limits. If the call is outside the limits, the call is rejected.
6. ![]() Authentication and authorization—The universal gateway reserves a port and sends an authentication, authorization, and accounting (AAA) accounting start packet to the RADIUS-based PPM server.
Authentication and authorization—The universal gateway reserves a port and sends an authentication, authorization, and accounting (AAA) accounting start packet to the RADIUS-based PPM server.
7. ![]() The connection between the caller and the universal gateway is completed (call leg 3).
The connection between the caller and the universal gateway is completed (call leg 3).
8. ![]() The caller is connected to the PSTN (call leg 4).
The caller is connected to the PSTN (call leg 4).
9. ![]() Accounting stop—After the caller hangs up or is otherwise disconnected, the terminating universal gateway issues an accounting stop packet to the RADIUS-based PPM server. The PPM server uses the accounting stop packet to clear out the count for that call against the SLA.
Accounting stop—After the caller hangs up or is otherwise disconnected, the terminating universal gateway issues an accounting stop packet to the RADIUS-based PPM server. The PPM server uses the accounting stop packet to clear out the count for that call against the SLA.
SIP - Enhanced Billing Support for Gateways
This section describes the SIP - Enhanced Billing Support for Gateways feature. The feature describes the changes to authentication, authorization, and accounting (AAA) records and the Remote Authentication Dial-In User Service (RADIUS) implementations on Cisco SIP gateways. These changes were introduced to provide customers and partners the ability to effectively bill for traffic transported over SIP networks.
This section discusses the following topics:
Username Attribute
The username attribute is included in all AAA records and is the primary means for the billing system to identify an end user. The password attribute is included in authentication and authorization messages of inbound VoIP call legs.
For most implementations, the SIP gateway populates the username attribute in the SIP INVITE request with the calling number from the FROM: header, and the password attribute with null or with data from an IVR script. If a Proxy-Authorization header exists, it is ignored. The aaa username command determines the information with which to populate the username attribute.
Within the Microsoft Passport authentication service that authenticates and identifies users, the passport user ID (PUID) is used. The PUID and a password are passed from a Microsoft network to the Internet telephony service provider (ITSP) network in the Proxy-Authorization header of a SIP INVITE request as a single, base-64 encoded string. For example,
Proxy-Authorization: basic MDAwMzAwMDA4MDM5MzJlNjou
The aaa username command enables parsing of the Proxy-Authorization header; decoding of the PUID and password; and populating of the PUID into the username attribute, and the decoded password into the password attribute. The decoded password is generally a "." because a Microsoft Network (MSN) authenticates users prior to this point. For example,
Username = "123456789012345"
Password = "Z\335\304\326KU\037\301\261\326GS\255\242\002\202"
The password in the example above is an encrypted "." and is the same for all users.
SIP Call ID
From the Call ID header of the SIP INVITE request, the SIP Call ID is extracted and populated in Cisco vendor-specific attributes (VSA) as an attribute value pair call-id=string. The value pair can be used to correlate RADIUS records from Cisco SIP gateways with RADIUS records from other SIP network elements for example, proxies.

Note ![]() For complete information on this attribute value pair, see the RADIUS Vendor-Specific Attributes Voice Implementation Guide.
For complete information on this attribute value pair, see the RADIUS Vendor-Specific Attributes Voice Implementation Guide.
Session Protocol
Session Protocol is another attribute value pair that indicates whether the call is using SIP or H.323 as the signaling protocol.

Note ![]() For complete information on this attribute value pair, see the RADIUS Vendor-Specific Attributes Voice Implementation Guide.
For complete information on this attribute value pair, see the RADIUS Vendor-Specific Attributes Voice Implementation Guide.
Silent Authentication Script
As part of the SIP - Enhanced Billing Support for SIP Gateways feature, a Tool Command Language (Tcl) Interactive Voice Response (IVR) 2.0 Silent Authorization script has been developed. The Silent Authorization script allows users to be authorized without having to separately enter a username or password into the system. The script automatically extracts the passport user ID (PUID) and password from the SIP INVITE request, and then authenticates that information through RADIUS authentication and authorization records. The script is referred to as silent since neither the caller or called party hears any prompts.

Note![]() •
•![]() You can upgrade to the latest script version through the CCO Software Center. You can download the app_passport_silent.2.0.0.0.tcl script from http://www.cisco.com/cgi-bin/tablebuild.pl/tclware. You must be a registered CCO user to log in and access these files.
You can upgrade to the latest script version through the CCO Software Center. You can download the app_passport_silent.2.0.0.0.tcl script from http://www.cisco.com/cgi-bin/tablebuild.pl/tclware. You must be a registered CCO user to log in and access these files.
•![]() For information regarding Tcl IVR API 2.0, see the Tcl IVR API Version 2.0 Programmer's Guide.
For information regarding Tcl IVR API 2.0, see the Tcl IVR API Version 2.0 Programmer's Guide.
Developers using the Tcl Silent Authorization script may be interested in joining the Cisco Developer Support Program. This program provides you with a consistent level of support that you can depend on while leveraging Cisco interfaces in your development projects. It also provides an easy process to open, update, and track issues through Cisco.com. The Cisco web-site is a key communication vehicle for using the Cisco Online Case tracking tool. A signed Developer Support Agreement is required to participate in this program. For more details, and access to this agreement, please visit us at http://www.cisco.com/en/US/products/svcs/ps3034/ps5408/ps5418/serv_home.html or contact developer-support@cisco.com.
Configurable Screening Indicator
Screening Indicator (SI) is a signaling-related information element found in octet 3a of the ISDN SETUP message that can be used as an authorization mechanism for incoming calls. The Tcl IVR 2.0 command set allows SIP terminating gateways to assign a specific value to the screening indicator through the use of Tcl scripts.
The screening indicator can contain four possible values:
•![]() User provided, not screened
User provided, not screened
•![]() User provided, verified and passed
User provided, verified and passed
•![]() User provided, verified and failed
User provided, verified and failed
•![]() Network provided
Network provided

Note![]() •
•![]() In all scenarios, gateway accounting must be enabled, and all call-accounting information must be forwarded to the server that is performing preauthentication. Accounting stop packets must be sent to this server so that call billing is ended when calls are disconnected from the gateway. In addition, authentication and accounting start packets are needed to enable other features, such as virtual private dial-up network (VPDN).
In all scenarios, gateway accounting must be enabled, and all call-accounting information must be forwarded to the server that is performing preauthentication. Accounting stop packets must be sent to this server so that call billing is ended when calls are disconnected from the gateway. In addition, authentication and accounting start packets are needed to enable other features, such as virtual private dial-up network (VPDN).
•![]() For information on using Tcl IVR scripts to set and retrieve screening indicators, see the Tcl IVR API Version 2.0 Programmer's Guide.
For information on using Tcl IVR scripts to set and retrieve screening indicators, see the Tcl IVR API Version 2.0 Programmer's Guide.
SIP: Gateway HTTP Authentication Digest
The SIP: Gateway HTTP Authentication Digest feature implements authentication using the digest access on the client side of a common SIP stack. The gateway responds to authentication challenges from an authenticating server, proxy server, or user-agent server (UAS). This feature also maintains parity between the Cisco gateways, proxy servers, and SIP phones that already support authentication.
Feature benefits include the following:
•![]() A SIP gateway is able to respond to authentication challenges from authenticating proxy servers or user-agent servers (UASs). The authentication method supported is digest authentication. Although digest authentication is not the best method, it provides a basic level of security.
A SIP gateway is able to respond to authentication challenges from authenticating proxy servers or user-agent servers (UASs). The authentication method supported is digest authentication. Although digest authentication is not the best method, it provides a basic level of security.

Note ![]() The UAS challenges with a 401 response and the proxy server with a 407 response. It tries to find authentication credentials appropriate to the realm issuing the challenge and response. A gateway can handle authentication challenges from both the proxy server and UAS.
The UAS challenges with a 401 response and the proxy server with a 407 response. It tries to find authentication credentials appropriate to the realm issuing the challenge and response. A gateway can handle authentication challenges from both the proxy server and UAS.
•![]() Registration of the destination patterns on POTS dial peers extends to all PSTN interfaces.
Registration of the destination patterns on POTS dial peers extends to all PSTN interfaces.

Note ![]() The proxy server previously performed authentication only with the SIP phones.
The proxy server previously performed authentication only with the SIP phones.
The SIP Survivable Remote Site Telephony (SRST) feature in an earlier release added support to register E.164 numbers for foreign exchange stations (FXSs) (analog telephone voice ports) and extended foreign exchange stations (IP phone virtual voice ports) to an external SIP registrar. This feature extends that functionality for the gateway to register numbers configured on PSTN trunks such as PRI pipes.
This section contains the following information:
•![]() Proxy-Server-to-UA Authentication
Proxy-Server-to-UA Authentication
•![]() Extending SIP Register Support on Gateway
Extending SIP Register Support on Gateway
Digest Access Authentication
SIP provides a stateless challenge-response mechanism for authentication based on digest access. A UAS or proxy server receiving a request challenges the initiator of the request to provide its identity. The user-agent client (UAC) generates a response by performing a message digest 5 (MD5) checksum on the challenge and its password. The response is passed back to the challenger in a subsequent request.
There are two modes of authentication:
•![]() Proxy-server authentication
Proxy-server authentication
•![]() UAS authentication
UAS authentication
This feature also supports multiple proxy authentication on the gateway. The gateway can respond to up to five different authentication challenges in the signaling path between gateway as UAC and a UAS.
UAC-to-UAS Authentication
When the UAS receives a request without credentials from a UAC, it challenges the originator to provide credentials by rejecting the request with a "401 Unauthorized" response that includes a WWW-Authenticate header. The header field value consists of arguments applicable to digest scheme, as follows:
•![]() realm—A string to be displayed to users so they know which username and password to use.
realm—A string to be displayed to users so they know which username and password to use.
•![]() nonce—A server-specified data string that should be uniquely generated each time a 401 response is made.
nonce—A server-specified data string that should be uniquely generated each time a 401 response is made.
In addition, the header field may contain the following optional arguments:
•![]() opaque—A string of data, specified by the server, that should be returned by the client unchanged in the Authentication header of subsequent requests with URIs in the same protection space.
opaque—A string of data, specified by the server, that should be returned by the client unchanged in the Authentication header of subsequent requests with URIs in the same protection space.
•![]() stale—A flag, indicating that the previous request from the client was rejected because the nonce value was stale.
stale—A flag, indicating that the previous request from the client was rejected because the nonce value was stale.
•![]() algorithm—A string indicating a pair of algorithms used to produce the digest and a checksum.
algorithm—A string indicating a pair of algorithms used to produce the digest and a checksum.
•![]() qop-options—A string of one or more tokens indicating the "quality of protection" values supported by the server.
qop-options—A string of one or more tokens indicating the "quality of protection" values supported by the server.
•![]() auth-param—Directive that allows for future extensions.
auth-param—Directive that allows for future extensions.
The UAC reoriginates the request with proper credentials in the Authorization header field. The Authorization header field value consists of authentication information and arguments:
•![]() username—User's name in specified realm. This value is taken from the configuration, either at the dial-peer or the global level.
username—User's name in specified realm. This value is taken from the configuration, either at the dial-peer or the global level.
•![]() digest-uri—Same as request uri of the request.
digest-uri—Same as request uri of the request.
•![]() realm, nonce— From WWW-Authenticate header.
realm, nonce— From WWW-Authenticate header.
Message digest 5 (MD5) is computed as follows:
MD5(concat(MD5(A1),(unquoted)nonce-value":"nc-value":"
(unquoted)cnonce-value ":"(unquoted)qop-value":"MD5(A2)))
where A1 = (unquoted) username-value ":" (unquoted) realm-value ":" password
A2 = Method ":" request-uri if qop is "auth"
& A2 = Method ":" request-uri ":" MD5(entity-body) if qop is "auth-int".
•![]() The nc-value is the hexadecimal count of the number of requests (including the current request that the client has sent with the nonce value in this request.
The nc-value is the hexadecimal count of the number of requests (including the current request that the client has sent with the nonce value in this request.
•![]() The cnonce-value is an opaque string provided by client for mutual authentication between client and server.
The cnonce-value is an opaque string provided by client for mutual authentication between client and server.
•![]() The qop-value is quality of protection directive, "auth" or "auth-int".
The qop-value is quality of protection directive, "auth" or "auth-int".
UAC-to-UAS Call Flow with Register Message
In this call flow (see Figure 63), the UA sends a Register message request without the Authorization header and receives a 401 status code message response challenge from the SIP server. The UA then resends the request including the proper credentials in the Authorization header.
Figure 63 UA-to-UAS Call Flow with Register Message
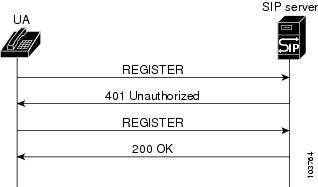
The UA sends a Register message request to the SIP server with the CSeq initialized to 1:
REGISTER sip:172.18.193.187:5060 SIP/2.0
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK200B
From: "36602" <sip:36602@172.18.193.120>;tag=98AS-87RT
To: <sip:36602@172.18.193.187>
Call-ID: A9EEC728-495E11D6-8003AD63-F55A9C4
User-Agent: Cisco-SIPGateway/IOS-12.x
CSeq: 1 REGISTER
Contact: <sip:36602@172.18.193.120:5060>;user=phone
Expires: 60
Content-Length: 0
The SIP server responds with a 401 Unauthorized challenge response to the UA:
SIP/2.0 401 Unauthorized
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK200B
From: "36602" <sip:36602@172.18.193.120>;tag=98AS-87RT
To: <sip:36602@172.18.193.187>;tag=3046583040568302
Call-ID: A9EEC728-495E11D6-8003AD63-F55A9C4
CSeq: 1 REGISTER
WWW-Authenticate: Digest realm="example.com", qop="auth", nonce="ea9c8e88df84f1cec4341ae6cbe5a359", opaque="", stale=FALSE, algorithm=MD5
Content-Length: 0
The UA resends a Register message request to the SIP server that includes the authorization and increments the CSeq:
REGISTER sip:172.18.193.187:5060 SIP/2.0
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK1DEA
From: "36602" <sip:36602@172.18.193.120>;tag=98AS-89FD
To: <sip:36602@172.18.193.187>
Call-ID: A9EEC728-495E11D6-8003AD63-F55A9C4
User-Agent: Cisco-SIPGateway/IOS-12.x
Authorization: Digest username="36602", realm="example.com", nonce="ea9c8e88df84f1cec4341ae6cbe5a359", opaque="", uri="sip:172.18.193.187", response="dfe56131d1958046689d83306477ecc"
CSeq: 2 REGISTER
Contact: <sip:36602@172.18.193.120:5060>;user=phone
Expires: 60
Content-Length: 0
The SIP server responds with a 200 OK message response to the UA:
SIP/2.0 200 OK
Via: SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK1DEA
Call-ID: A9EEC728-495E11D6-8003AD63-F55A9C4
From: "36602" <sip:36602@172.18.193.120>;tag=98AS-89FD
To: <sip:36602@172.18.193.187>;tag=1q92461294
CSeq: 2 REGISTER
Contact: <sip:36602@172.18.193.120:5060>;expires="Wed, 02 Jul 2003 18:18:26 GMT"
Expires: 60
Content-Length: 0

Note ![]() A SIP server can challenge any request except ACK and CANCEL request messages, because an ACK message request does not take any response and a CANCEL message request cannot be resubmitted. The UA uses the same credentials in an ACK message request as in an INVITE message request.
A SIP server can challenge any request except ACK and CANCEL request messages, because an ACK message request does not take any response and a CANCEL message request cannot be resubmitted. The UA uses the same credentials in an ACK message request as in an INVITE message request.
UAC-to-UAS Call Flow with INVITE Message
In this call flow (see Figure 64), the UAC sends an INVITE message request to a UAS without proper credentials and is challenged with a 401 Unauthorized message response. A new INVITE message request is then sent, containing the correct credentials. Finally, the call is completed.
Figure 64 UAC-to-UAS Call Flow with INVITE Message
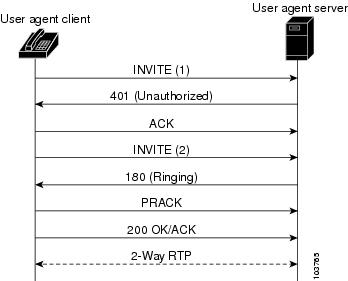
The UAS challenges the UAC to provide user credentials by issuing a 401 Unauthorized message response:
SIP/2.0 401 Unauthorized
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK45TGN
From: "36602" <sip:36602@172.18.193.120>;tag=98AS-87RT
To: <sip:36602@172.18.193.187>;tag=3046583040568302
Call-ID: A9EEC728-495E11D6-8003AD63-F55A9C4
CSeq: 101 INVITE
WWW-Authenticate: Digest realm="example.com", qop="auth", nonce="ea9c8e8809345gf1cec4341ae6cgh5a359", opaque=""
Content-Length: 0
The UAC resubmits the request with proper credentials in the Authorization header:
INVITE sip:36601@172.18.193.187:5060 SIP/2.0
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK8DF8H
From: "36602"<sip:36602@172.18.193.120>;tag=50EB48-383
To: <sip:36601@172.18.193.187>
Call-ID: A9EEC728-495E11D6-8003AD63-F55A9C4
CSeq: 102 INVITE
Authorization: Digest username="36602", realm="example.com", nonce="ea9c8e8809345gf1cec4341ae6cgh5a359", opaque="", uri="sip:36601@172.18.193.187", response="42ce3cef44b22f50c02350g6071bc8"
.
.
.
The UAC uses the same credentials in subsequent requests in that dialog:
PRACK sip:36601@172.18.193.187:5060 SIP/2.0
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK8YH5790
From: "36602"<sip:36602@172.18.193.120>;tag=50EB48-383
To: <sip:36601@172.18.193.187>;tag=AG09-92315
Call-ID: A9EEC728-495E11D6-8003AD63-F55A9C4
CSeq: 103 PRACK
Authorization: Digest username="36602", realm="example.com", nonce="ea9c8e8809345gf1cec4341ae6cgh5a359", opaque="", uri="sip:36601@172.18.193.187", response="42ce3cef44b22f50c02350g6071bc9"
Content-Length: 0
Proxy-Server-to-UA Authentication
When a UA submits a request to a proxy server without proper credentials, the proxy server authenticates the originator by rejecting the request with a 407 message response (Proxy Authentication Required) and includes a Proxy-Authenticate header field value applicable to the proxy server for the requested resource. The UAC follows the same procedure mentioned in the "UAC-to-UAS Authentication" section to get proper credentials for the realm and resubmits the request with the credentials in the Proxy-Authorization header.

Note ![]() realm—A string to be displayed to users so they know which username and password to use.
realm—A string to be displayed to users so they know which username and password to use.
Proxy Server to UA Authentication Call Flow
In this call flow the UAC completes a call to user a UAS by using two proxy servers (PS 1 or PS 2, (see Figure 65). The UAC has valid credentials in both domains. Because the initial INVITE message request does not contain the Authorization credentials proxy server 1 requires, a 407 Proxy Authorization message response containing the challenge information is sent. A new INVITE message request containing the correct credentials is then sent and the call proceeds after proxy server 2 challenges and receives valid credentials.
Figure 65 Proxy-Server-to-UA Call Flow
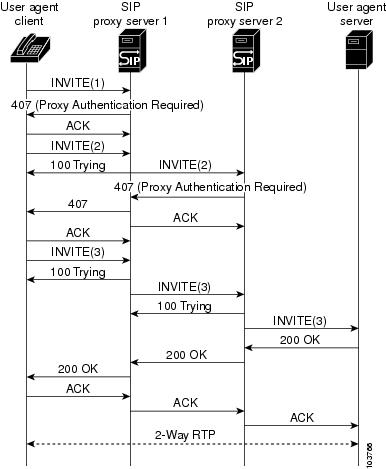
Proxy server 1 challenges the UAC for authentication:
SIP/2.0 407 Proxy Authorization Required
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK207H
From: <sip:36602@172.18.193.120>;tag=50EB48-383
To: <sip:36601@172.18.193.187>;tag=929523858000835
Call-ID: D61E40D3-496A11D6-80070030-9426ED30@172.18.193.120
CSeq: 101 INVITE
Proxy-Authenticate: Digest realm="proxy1.example.com", qop="auth",
nonce="wf84f1cczx41ae6cbeaea9ce88d359", opaque="", stale=FALSE, algorithm=MD5
Content-Length: 0
The UAC responds by resending the INVITE message request with authentication credentials. The same Call-ID is used, so the CSeq is increased.
INVITE sip:36601@172.18.193.187:5060 SIP/2.0
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bKEE1
From: <sip:36602@172.18.193.120>;tag=50EB48-383
To: <sip:36601@172.18.193.187>
Call-ID: D61E40D3-496A11D6-80070030-9426ED30@172.18.193.120
CSeq: 102 INVITE
Proxy-Authorization: Digest username="36602", realm="proxy1.example.com", nonce="wf84f1ceczx41ae6cbe5aea9c8e88d359", opaque="", uri="sip:36601@172.18.193.187", response="42ce3cef44b22f50c6a6071bc8"
Contact: <sip:172.18.193.120:5060>
.
.
.
The proxy server 2 challenges the UAC INVITE message request for authentication which is the 407 authentication message response that is forwarded to the UAC by proxy server 1.
SIP/2.0 407 Proxy Authorization Required
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bKEE1
From: <sip:36602@172.18.193.120>;tag=50EB48-383
To: <sip:36601@172.18.193.187>;tag=083250982545745
Call-ID: D61E40D3-496A11D6-80070030-9426ED30@172.18.193.120
Proxy-Authenticate: Digest realm="proxy2.example.com", qop="auth", nonce="c1e22c41ae6cbe5ae983a9c8e88d359", opaque="", stale=FALSE, algorithm=MD5
Content-Length: 0
The UAC responds by resending the INVITE message request with authentication credentials for proxy server 1 and proxy server 2.
INVITE sip:36601@172.18.193.187:5060 SIP/2.0
Via: SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK8GY
From: <sip:36602@172.18.193.120>;tag=50EB48-383
To: <sip:36601@172.18.193.187>
Call-ID: D61E40D3-496A11D6-80070030-9426ED30@172.18.193.120
CSeq: 103 INVITE
Proxy-Authorization: Digest username="36602", realm="proxy1.example.com", nonce="wf84f1ceczx41ae6cbe5aea9c8e88d359", opaque="", uri="sip:36601@172.18.193.187", response="42ce3cef44b22f50c6a6071bc8"
Proxy-Authorization: Digest username="36602", realm="proxy2.example.com", nonce="c1e22c41ae6cbe5ae983a9c8e88d359", opaque="", uri="sip:36601@172.18.193.187", response="f44ab22f150c6a56071bce8"
.
.
.
Extending SIP Register Support on Gateway
The SIP: Gateway HTTP Authentication Digest feature enhances functionality for Cisco IOS SIP gateway to Register all addresses specified by destination patterns in operational POTS dial-peers for all ports. This provides customer flexibility to register and authenticate users behind a private branch exchange (PBX) connected to the gateway through a PRI interface. There is no change in the way the gateway with foreign-exchange-station (FXS) ports registers individual E.164 addresses.
This feature leverages dial peers to create granularity for registration and authentication. However, the dial peers can be created with wildcards (for example: .919T, where terminator [T] makes the gateway wait until the full dial-string is received.) and a range of numbers (for example: .919392..., where ... indicates numbers in the range 0000 to 9999). Such destination patterns are registered with a single character wildcard in the user portion of To and Contact headers. Table 36 shows how the various types of gateway dial plans map to its registration.
|
|
|
|---|---|
dial-peer voice 919 pots destination-pattern 919....... port 0:D |
REGISTER sip:proxy.example.com SIP/2.0 To: <sip:919.......@172.18.193.120> From: <sip:172.18.192.120>;tag=ABCD Contact: <sip:919.......@172.18.193.120>;user=phone |
dial-peer voice 555 pots destination-pattern 555T port 0:D |
REGISTER sip:proxy.example.com SIP/2.0 To: <sip:555*@172.18.193.120> From: <sip:172.18.192.120>;tag=ABCD Contact: <sip:555*@172.18.193.120>;user=phone |
dial-peer voice 5550100 pots destination-pattern 5550100 port 0:D |
REGISTER sip:proxy.example.com SIP/2.0 To: <sip:5550100@172.18.193.120> From: <sip:5550100@172.18.192.120>;tag=ABCD Contact: <sip:5550100@172.18.193.120>;user=phone |
1 You need to modify the proxy/registrar behavior to correctly route calls for wildcard patterns or destination pattern with a range. Proxy server or registrars that do not match a wildcard patterns or destination pattern with a range should be ignored for that specific request. |
How to Configure SIP AAA Features
This section contains the following procedures:
•![]() Configuring RADIUS Pre-authentication for Voice Calls
Configuring RADIUS Pre-authentication for Voice Calls
•![]() Configuring SIP - Enhanced Billing Support for Gateways
Configuring SIP - Enhanced Billing Support for Gateways
•![]() Configuring SIP: Gateway HTTP Authentication Digest
Configuring SIP: Gateway HTTP Authentication Digest
•![]() Verifying AAA Features for SIP
Verifying AAA Features for SIP
Configuring RADIUS Pre-authentication for Voice Calls
This section includes the following procedures:
•![]() Configure a RADIUS Group Server
Configure a RADIUS Group Server
•![]() Configure Access and Authentication
Configure Access and Authentication
•![]() Configure RADIUS Communications
Configure RADIUS Communications
Configure a RADIUS Group Server
To configure a a RADIUS group server, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa new-model
aaa new-model
4. ![]() aaa group server radius groupname
aaa group server radius groupname
5. ![]() server ip-address [auth-port port] [acct-port port]
server ip-address [auth-port port] [acct-port port]
6. ![]() exit
exit
DETAILED STEPS
Configure Access and Authentication
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa authentication login h323 group groupname
aaa authentication login h323 group groupname
4. ![]() aaa authentication ppp default group groupname
aaa authentication ppp default group groupname
5. ![]() aaa authorization exec list-name group groupname
aaa authorization exec list-name group groupname
6. ![]() aaa authorization network default group {radius | rpms} if-authenticated
aaa authorization network default group {radius | rpms} if-authenticated
7. ![]() aaa authorization reverse-access default local
aaa authorization reverse-access default local
8. ![]() aaa accounting suppress null-user-name
aaa accounting suppress null-user-name
9. ![]() aaa accounting send stop-record authentication failure
aaa accounting send stop-record authentication failure
10. ![]() exit
exit
DETAILED STEPS
Configure Accounting

Note ![]() For a complete explanation of the aaa accounting command, see the Cisco IOS Security Command Reference.
For a complete explanation of the aaa accounting command, see the Cisco IOS Security Command Reference.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa accounting delay-start
aaa accounting delay-start
4. ![]() aaa accounting update [periodic number]
aaa accounting update [periodic number]
5. ![]() aaa accounting exec default start-stop group groupname
aaa accounting exec default start-stop group groupname
6. ![]() aaa accounting exec list-name start-stop group groupname
aaa accounting exec list-name start-stop group groupname
7. ![]() aaa accounting network default start-stop group groupname
aaa accounting network default start-stop group groupname
8. ![]() aaa accounting connection h323 start-stop group groupname
aaa accounting connection h323 start-stop group groupname
9. ![]() aaa accounting system default start-stop group groupname
aaa accounting system default start-stop group groupname
10. ![]() aaa accounting resource default start-stop-failure group groupname
aaa accounting resource default start-stop-failure group groupname
11. ![]() gw-accounting aaa
gw-accounting aaa
12. ![]() exit
exit
DETAILED STEPS
Configure Preauthentication
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa preauth
aaa preauth
4. ![]() group {radius | groupname}
group {radius | groupname}
5. ![]() clid [if-avail | required] [accept-stop] [password string]
clid [if-avail | required] [accept-stop] [password string]
6. ![]() ctype [if-avail | required] [accept-stop] [password string]
ctype [if-avail | required] [accept-stop] [password string]
7. ![]() dnis [if-avail | required] [accept-stop] [password string]
dnis [if-avail | required] [accept-stop] [password string]
8. ![]() dnis bypass {dnis-groupname}
dnis bypass {dnis-groupname}
9. ![]() filter voice
filter voice
10. ![]() timeout leg3 time
timeout leg3 time
11. ![]() service-type call-check
service-type call-check
12. ![]() exit
exit
DETAILED STEPS
Configure RADIUS Communications
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() radius-server host {hostname | ip-address} [auth-port port-number] [acct-port port-number] [timeout seconds] [retransmit retries] [key string] [alias {hostname | ip-address}]
radius-server host {hostname | ip-address} [auth-port port-number] [acct-port port-number] [timeout seconds] [retransmit retries] [key string] [alias {hostname | ip-address}]
4. ![]() radius-server retransmit retries
radius-server retransmit retries
5. ![]() radius-server attribute 6 support-multiple
radius-server attribute 6 support-multiple
6. ![]() radius-server attribute 44 include-in-access-req
radius-server attribute 44 include-in-access-req
7. ![]() radius-server attribute nas-port format c
radius-server attribute nas-port format c
8. ![]() radius-server key {0 string | 7 string | string}
radius-server key {0 string | 7 string | string}
9. ![]() radius-server vsa send accounting
radius-server vsa send accounting
10. ![]() radius-server vsa send authentication
radius-server vsa send authentication
11. ![]() exit
exit
DETAILED STEPS
|
|
|
|
|---|---|---|
Step 1 |
enable Router> enable |
Enables privileged EXEC mode. Enter your password if prompted. |
Step 2 |
configure terminal Router# configure terminal |
Enters global configuration mode. |
Step 3 |
radius-server host {hostname | ip-address} [auth-port port-number] [acct-port port-number] [timeout seconds] [retransmit retries] [key string] [alias {hostname | ip-address}] radius-server host jimname |
Specifies a RADIUS server host. Keywords and arguments are as follows: • • • • • • • The key is a text string that must match the encryption key used on the RADIUS server. Always configure the key as the last item in the radius-server host command syntax. This is because leading spaces are ignored, but spaces within and at the end of the key are used. If you use spaces in the key, do not enclose the key in quotation marks unless the quotation marks themselves are part of the key. • |
Step 4 |
radius-server retransmit retries Router(config)# radius-server retransmit 1 |
(Optional) Specifies the number of times the Cisco IOS software searches the list of RADIUS server hosts before giving up. The argument is as follows: • |
Step 5 |
radius-server attribute 6 support-multiple Router(config)# radius-server attribute 6 support-multiple |
(Optional) Sets an option for RADIUS Attribute 6 (Service-Type) values in a RADIUS profile. The keyword is as follows: • |
Step 6 |
radius-server attribute 44 include-in-access-req Router(config)# radius-server attribute 44 include-in-access-req |
Sends RADIUS attribute 44 (Accounting Session ID) in access request packets before user authentication (including requests for preauthentication). Note |
Step 7 |
radius-server attribute nas-port format c Router(config)# radius-server attribute nas-port format c |
(Required if using Cisco RPMS) Selects the NAS-Port format used for RADIUS accounting features. |
Step 8 |
radius-server key {0 string | 7 string | string} Router(config)# radius-server key ncmmekweisnaowkakskiiw |
(Optional) Sets the authentication and encryption key for all RADIUS communications between the router and the RADIUS daemon. Keywords and arguments are as follows: • • • |
Step 9 |
radius-server vsa send accounting Router(config)# radius-server vsa send accounting |
(Optional) Configures the network access server to recognize and use vendor-specific attributes. |
Step 10 |
radius-server vsa send authentication Router(config)# radius-server vsa send authentication |
(Optional) Configures the network access server to recognize and use vendor-specific attributes. |
Step 11 |
exit Router(config)# exit |
Exits the current mode. |
Configuring SIP - Enhanced Billing Support for Gateways
To configure the SIP - Enhanced Billing Support for Gateways feature, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() sip-ua
sip-ua
4. ![]() aaa username {calling-name | proxy-auth}
aaa username {calling-name | proxy-auth}
5. ![]() exit
exit
DETAILED STEPS
Configuring SIP: Gateway HTTP Authentication Digest
This section contains the following procedures:
•![]() Configure SIP: Gateway HTTP Authentication Digest Via Dial-Peer (required)
Configure SIP: Gateway HTTP Authentication Digest Via Dial-Peer (required)
•![]() Configure SIP: Gateway HTTP Authentication Digest Via SIP UA (required)
Configure SIP: Gateway HTTP Authentication Digest Via SIP UA (required)
Configure SIP: Gateway HTTP Authentication Digest Via Dial-Peer
To configure the SIP: Gateway HTTP Authentication Digest Via Dial-Peer feature, perform the following steps.

Note![]() •
•![]() This configuration sets up the feature as defined under the POTS dial peer.
This configuration sets up the feature as defined under the POTS dial peer.
•![]() This feature is configured at the POTS dial peer and SIP user agent, with configuration at the dial peer taking precedence over that at the SIP user agent.
This feature is configured at the POTS dial peer and SIP user agent, with configuration at the dial peer taking precedence over that at the SIP user agent.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() dial-peer voice tag pots
dial-peer voice tag pots
4. ![]() authentication username username password password [realm realm]
authentication username username password password [realm realm]
5. ![]() exit
exit
DETAILED STEPS
Configure SIP: Gateway HTTP Authentication Digest Via SIP UA
To configure the SIP: Gateway HTTP Authentication Digest Via SIP UA feature, perform the following steps.

Note ![]() You can configure this feature for a dial peer or globally, for all POTS dial peers, in SIP user-agent configuration mode. If authentication is configured in SIP user-agent configuration mode and on individual dial peers, the individual dial-peer configuration takes precedence.
You can configure this feature for a dial peer or globally, for all POTS dial peers, in SIP user-agent configuration mode. If authentication is configured in SIP user-agent configuration mode and on individual dial peers, the individual dial-peer configuration takes precedence.
Restrictions
•![]() SIP Register is supported only on platforms with digital trunk type ports.
SIP Register is supported only on platforms with digital trunk type ports.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() sip-ua
sip-ua
4. ![]() registrar {dns:address | ipv4:destination-address} expires seconds [tcp] [secondary]
registrar {dns:address | ipv4:destination-address} expires seconds [tcp] [secondary]
5. ![]() authentication username username password password [realm realm]
authentication username username password password [realm realm]
6. ![]() exit
exit
DETAILED STEPS
Verifying AAA Features for SIP
To verify AAA-feature configuration, perform the following steps as appropriate (commands are listed in alphabetical order).
SUMMARY STEPS
1. ![]() show call active voice
show call active voice
2. ![]() show radius statistics
show radius statistics
3. ![]() show running-config
show running-config
4. ![]() show sip-ua register status
show sip-ua register status
DETAILED STEPS
Step 1 ![]() show call active voice
show call active voice
Use this command to display call information for active voice calls. You can thus verify the username attribute.
The following sample output shows that the proxy-auth parameter is selected.
Router# show call active voice
Total call-legs: 2
GENERIC:
SetupTime=1551144 ms
.
. (snip)
.
ReceiveBytes=63006
VOIP:
ConnectionId[0x220A95B7 0x6B3611D5 0x801DBD53 0x8F65BA34]
.
. (snip)
.
CallerName=
CallerIDBlocked=False
Username=1234567890123456 <-- PUID from Proxy-Auth header
The following sample output shows that the calling-number parameter is selected.
Router# show call active voice
Total call-legs: 2
GENERIC:
SetupTime=1587000 ms
.
. (snip)
.
ReceiveBytes=22762
VOIP:
ConnectionId[0xF7C22E07 0x6B3611D5 0x8022BD53 0x8F65BA34]
.
. (snip)
.
CallerName=
CallerIDBlocked=False
Username=1234 <-- calling-number
Step 2 ![]() show radius statistics
show radius statistics
Use this command to display RADIUS statistics for accounting and authentication packets.
Step 3 ![]() show rpms-proc counters
show rpms-proc counters
Use this command to display the number of leg 3 preauthentication requests, successes, and rejects.

Note ![]() Use the clear rpms-proc counters command to reset the counters that record the statistics that the show rpms-proc counters command displays.
Use the clear rpms-proc counters command to reset the counters that record the statistics that the show rpms-proc counters command displays.
Step 4 ![]() show running-config
show running-config
Use this command to display the current configuration.
Step 5 ![]() show sip-ua register status
show sip-ua register status
Use this command to verify SIP user-agent register status.
Router# show sip-ua register status
Line peer expires(sec) registered
4001 20001 596 no
4002 20002 596 no
5100 1 596 no
9998 2 596 no
where:
line=phone number to register
peer=registration destination number
expires (sec)=amount of time, in seconds, until registration expires
registered=registration status
Troubleshooting Tips

Note ![]() For general troubleshooting tips and a list of important debug commands, see the "General Troubleshooting Tips" section on page 18.
For general troubleshooting tips and a list of important debug commands, see the "General Troubleshooting Tips" section on page 18.
•![]() Make sure that you can make a voice call.
Make sure that you can make a voice call.
•![]() If the gateway does not respond to the authentication challenge, make sure that the user credentials for the appropriate domain have been configured.
If the gateway does not respond to the authentication challenge, make sure that the user credentials for the appropriate domain have been configured.
•![]() For the gateway to register destination patterns on the POTS dial peer, make sure that a registrar has been configured.
For the gateway to register destination patterns on the POTS dial peer, make sure that a registrar has been configured.
•![]() Use the debug aaa authentication command to display high-level diagnostics related to AAA logins.
Use the debug aaa authentication command to display high-level diagnostics related to AAA logins.
•![]() Use the debug cch323 preauth command to enable debug tracing on the H.323 SPI for preauthentication.
Use the debug cch323 preauth command to enable debug tracing on the H.323 SPI for preauthentication.
•![]() Use the debug ccsip family of commands to enable SIP debugging capabilities. In particular, use the following:
Use the debug ccsip family of commands to enable SIP debugging capabilities. In particular, use the following:
–![]() Use the debug ccsip all and debug ccsip events commands to display output specific to the SIP - Enhanced Billing Support for Gateways feature.
Use the debug ccsip all and debug ccsip events commands to display output specific to the SIP - Enhanced Billing Support for Gateways feature.
–![]() Use the debug ccsip preauth command to enable debug tracing on the SIP service provider interface (SPI) for preauthentication.
Use the debug ccsip preauth command to enable debug tracing on the SIP service provider interface (SPI) for preauthentication.
•![]() Use the debug radius command to enable debug tracing of RADIUS attributes.
Use the debug radius command to enable debug tracing of RADIUS attributes.
•![]() Use the debug rpms-proc preauth command to enable debug tracing on the RPMS process for H.323 calls, SIP calls, or both H.323 and SIP calls.
Use the debug rpms-proc preauth command to enable debug tracing on the RPMS process for H.323 calls, SIP calls, or both H.323 and SIP calls.
Following is sample output for some of these commands:
•![]() Sample Output for the debug ccsip Command
Sample Output for the debug ccsip Command
•![]() Sample Output of the debug ccsip events Command
Sample Output of the debug ccsip events Command
•![]() Sample Output for the debug radius Command
Sample Output for the debug radius Command
Sample Output for the debug ccsip Command
Router# debug ccsip messages
*Oct 11 21:40:26.175://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Sent:
INVITE sip:5550123@172.18.193.187:5060 SIP/2.0 ! Invite request message (command sequence
101)
Via:SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK6ED
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>
Date:Fri, 11 Oct 2002 21:40:26 GMT
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
Supported:100rel,timer
Min-SE: 1800
Cisco-Guid:3787171507-3700953558-2147913662-199702180
User-Agent:Cisco-SIPGateway/IOS-12.x
Allow:INVITE, OPTIONS, BYE, CANCEL, ACK, PRACK, COMET, REFER, SUBSCRIBE, NOTIFY, INFO, UPDATE, REGISTER
CSeq:101 INVITE
Max-Forwards:70
Remote-Party-ID:"36602" <sip:36602@172.18.193.120>;party=calling;screen=no;privacy=off
Timestamp:1034372426
Contact:<sip:36602@172.18.193.120:5060>
Expires:180
Allow-Events:telephone-event
Content-Type:application/sdp
Content-Length:244
v=0
o=CiscoSystemsSIP-GW-UserAgent 6603 1568 IN IP4 172.18.193.120
s=SIP Call
c=IN IP4 172.18.193.120
t=0 0
m=audio 17978 RTP/AVP 18 19
c=IN IP4 172.18.193.120
a=rtpmap:18 G729/8000
a=fmtp:18 annexb=no
a=rtpmap:19 CN/8000
a=ptime:20
*Oct 11 21:40:26.179://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Received:
SIP/2.0 100 Trying ! 100 Trying response message (command sequence 101)
Via:SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK6ED
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>
CSeq:101 INVITE
Content-Length:0
*Oct 11 21:40:26.179://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Received:
SIP/2.0 407 Proxy Authentication Required ! 407 proxy authentication required response
message (command sequence 101)
Via:SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK6ED
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=214b-70c4
CSeq:101 INVITE
Proxy-Authenticate:DIGEST realm="example.com", nonce="405729fe", qop="auth", algorithm=MD5
Content-Length:0
*Oct 11 21:40:26.183://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Sent:
ACK sip:5550123@172.18.193.187:5060 SIP/2.0 ! ACK request message (command sequence 101)
Via:SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK6ED
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=214b-70c4
Date:Fri, 11 Oct 2002 21:40:26 GMT
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
Max-Forwards:70
CSeq:101 ACK
Content-Length:0
*Oct 11 21:40:26.183://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Sent:
INVITE sip:5550123@172.18.193.187:5060 SIP/2.0 ! Invite message request (command sequence
102)
Via:SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK8BA
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>
Date:Fri, 11 Oct 2002 21:40:26 GMT
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
Supported:100rel,timer
Min-SE: 1800
Cisco-Guid:3787171507-3700953558-2147913662-199702180
User-Agent:Cisco-SIPGateway/IOS-12.x
Allow:INVITE, OPTIONS, BYE, CANCEL, ACK, PRACK, COMET, REFER, SUBSCRIBE, NOTIFY, INFO, UPDATE, REGISTER
CSeq:102 INVITE
Max-Forwards:70
Remote-Party-ID:"36602" <sip:36602@172.18.193.120>;party=calling;screen=no;privacy=off
Timestamp:1034372426
Contact:<sip:36602@172.18.193.120:5060>
Expires:180
Allow-Events:telephone-event
Proxy-Authorization:Digest username="36602",realm="example.com",uri="sip:172.18.193.187",response="404feee07cc7d3081d 04b977260efef5",nonce="405729fe",cnonce="AD7E41C1",qop=auth,algorithm=MD5,nc=00000001
Content-Type:application/sdp
Content-Length:244
v=0
o=CiscoSystemsSIP-GW-UserAgent 6603 1568 IN IP4 172.18.193.120
s=SIP Call
c=IN IP4 172.18.193.120
t=0 0
m=audio 17978 RTP/AVP 18 19
c=IN IP4 172.18.193.120
a=rtpmap:18 G729/8000
a=fmtp:18 annexb=no
a=rtpmap:19 CN/8000
a=ptime:20
*Oct 11 21:40:26.187://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Received:
SIP/2.0 100 Trying ! 100 Trying response message (command sequence 102)
Via:SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK8BA
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>
CSeq:102 INVITE
Content-Length:0
*Oct 11 21:40:26.439://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Received:
SIP/2.0 180 Ringing ! 180 Ringing response message (command sequence 102)
Via:SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK8BA
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=003094c2e56a035d4326b6a1-292418c6
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
CSeq:102 INVITE
Server:CSCO/4
Contact:<sip:5550123@172.18.197.182:5060>
Record-Route:<sip:5550123@172.18.193.187:5060;maddr=172.18.193.187>
Content-Length:0
*Oct 11 21:40:28.795://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Received:
SIP/2.0 200 OK ! 200 OK response message (command sequence 102)
Via:SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK8BA
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=003094c2e56a035d4326b6a1-292418c6
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
CSeq:102 INVITE
Server:CSCO/4
Contact:<sip:5550123@172.18.197.182:5060>
Record-Route:<sip:5550123@172.18.193.187:5060;maddr=172.18.193.187>
Content-Type:application/sdp
Content-Length:146
v=0
o=Cisco-SIPUA 21297 9644 IN IP4 172.18.197.182
s=SIP Call
c=IN IP4 172.18.197.182
t=0 0
m=audio 28290 RTP/AVP 18
a=rtpmap:18 G729/8000
*Oct 11 21:40:28.799://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Sent:
ACK sip:5550123@172.18.193.187:5060;maddr=172.18.193.187 SIP/2.0 ! ACK request message
(command sequence 102)
Via:SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK20A5
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=003094c2e56a035d4326b6a1-292418c6
Date:Fri, 11 Oct 2002 21:40:26 GMT
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
Route:<sip:5550123@172.18.197.182:5060>
Max-Forwards:70
CSeq:102 ACK
Proxy-Authorization:Digest username="36602",realm="example.com",uri="sip:172.18.193.187",response="cc865e13d766426fb6 5f362c4f569334",nonce="405729fe",cnonce="9495DEBD",qop=auth,algorithm=MD5,nc=00000002
Content-Length:0
*Oct 11 21:40:32.891://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Sent:
BYE sip:5550123@172.18.193.187:5060;maddr=172.18.193.187 SIP/2.0 ! BYE request message
(command sequence 103)
Via:SIP/2.0/UDP 172.18.193.120:5060;branch=z9hG4bK6AF
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=003094c2e56a035d4326b6a1-292418c6
Date:Fri, 11 Oct 2002 21:40:26 GMT
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
User-Agent:Cisco-SIPGateway/IOS-12.x
Max-Forwards:70
Route:<sip:5550123@172.18.197.182:5060>
Timestamp:1034372432
CSeq:103 BYE
Reason:Q.850;cause=16
Proxy-Authorization:Digest username="36602",realm="example.com",uri="sip:172.18.193.187",response="9b4d617d59782aeaf8 3cd49d932d12dd",nonce="405729fe",cnonce="22EB1F32",qop=auth,algorithm=MD5,nc=00000003
Content-Length:0
*Oct 11 21:40:32.895://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Received:
SIP/2.0 100 Trying ! 100 Trying response message (command sequence 103)
Via:SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK6AF
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=003094c2e56a035d4326b6a1-292418c6
CSeq:103 BYE
Content-Length:0
*Oct 11 21:40:32.963://-1/xxxxxxxxxxxx/SIP/Msg/ccsipDisplayMsg:
Received:
SIP/2.0 200 OK ! 200 OK response message (command sequence 103)
Via:SIP/2.0/UDP 172.18.193.120:5060;received=172.18.193.120;branch=z9hG4bK6AF
From:"36602" <sip:36602@172.18.193.120>;tag=3E948-4C5
To:<sip:5550123@172.18.193.187>;tag=003094c2e56a035d4326b6a1-292418c6
Call-ID:E35DBEB1-DC9811D6-80098FBE-BE736A4@172.18.193.120
CSeq:103 BYE
Server:CSCO/4
Content-Length:0
Sample Output of the debug ccsip events Command
The example shows how the Proxy-Authorization header is broken down into a decoded username and password.
Router# debug ccsip events
CCSIP SPI: SIP Call Events tracing is enabled
21:03:21: sippmh_parse_proxy_auth: Challenge is 'Basic'.
21:03:21: sippmh_parse_proxy_auth: Base64 user-pass string is 'MTIzNDU2Nzg5MDEyMzQ1Njou'.
21:03:21: sip_process_proxy_auth: Decoded user-pass string is '1234567890123456:.'.
21:03:21: sip_process_proxy_auth: Username is '1234567890123456'.
21:03:21: sip_process_proxy_auth: Pass is '.'.
21:03:21: sipSPIAddBillingInfoToCcb: sipCallId for billing records =
10872472-173611CC-81E9C73D-F836C2B6@172.18.192.19421:03:21: ****Adding to UAS Request table
Sample Output for the debug radius Command
Router# debug radius
Radius protocol debugging is on
Radius protocol brief debugging is off
Radius packet hex dump debugging is off
Radius packet protocol debugging is on
Radius packet retransmission debugging is off
Radius server fail-over debugging is off
Jan 23 14:30:25.421:RADIUS/ENCODE(00071EBF):acct_session_id:742769
Jan 23 14:30:25.421:RADIUS(00071EBF):sending
Jan 23 14:30:25.421:RADIUS:Send to unknown id 25 192.168.41.57:1812, Access-Request, len 179
Jan 23 14:30:25.421:RADIUS: authenticator 88 94 AC 32 89 84 73 6D - 71 00 50 6C D0 F8 FD 11
Jan 23 14:30:25.421:RADIUS: User-Name [1] 9 "2210001"
Jan 23 14:30:25.421:RADIUS: User-Password [2] 18 *
Jan 23 14:30:25.421:RADIUS: Vendor, Cisco [26] 32
Jan 23 14:30:25.421:RADIUS: Cisco AVpair [1] 26 "resource-service=reserve"
Jan 23 14:30:25.421:RADIUS: Service-Type [6] 6 Call Check [10]
Jan 23 14:30:25.421:RADIUS: Vendor, Cisco [26] 19
Jan 23 14:30:25.421:RADIUS: cisco-nas-port [2] 13 "Serial6/0:0"
Jan 23 14:30:25.425:RADIUS: NAS-Port [5] 6 6144
Jan 23 14:30:25.425:RADIUS: Vendor, Cisco [26] 29
Jan 23 14:30:25.425:RADIUS: Cisco AVpair [1] 23 "interface=Serial6/0:0"
Jan 23 14:30:25.425:RADIUS: Called-Station-Id [30] 9 "2210001"
Jan 23 14:30:25.425:RADIUS: Calling-Station-Id [31] 9 "1110001"
Jan 23 14:30:25.425:RADIUS: NAS-Port-Type [61] 6 Async [0]
Jan 23 14:30:25.425:RADIUS: NAS-IP-Address [4] 6 192.168.81.101
Jan 23 14:30:25.425:RADIUS: Acct-Session-Id [44] 10 "000B5571"
Jan 23 14:30:25.429:RADIUS:Received from id 25 192.168.41.57:1812, Access-Accept, len 20
Jan 23 14:30:25.429:RADIUS: authenticator 2C 16 63 18 36 56 18 B2 - 76 EB A5 EF 11 45 BE F4
Jan 23 14:30:25.429:RADIUS:Received from id 71EBF
Jan 23 14:30:25.429:RADIUS/DECODE:parse response short packet; IGNORE
Jan 23 14:30:25.433:RADIUS/ENCODE(00071EBF):Unsupported AAA attribute start_time
Jan 23 14:30:25.433:RADIUS/ENCODE(00071EBF):Unsupported AAA attribute timezone
Jan 23 14:30:25.433:RADIUS/ENCODE:format unknown; PASS
Jan 23 14:30:25.433:RADIUS(00071EBF):sending
Jan 23 14:30:25.433:RADIUS:Send to unknown id 26 192.168.41.57:1813, Accounting-Request, len 443
Jan 23 14:30:25.433:RADIUS: authenticator DA 1B 03 83 20 90 11 39 - F3 4F 70 F0 F5 8C CC 75
Jan 23 14:30:25.433:RADIUS: Acct-Session-Id [44] 10 "000B5571"
Jan 23 14:30:25.433:RADIUS: Vendor, Cisco [26] 56
Jan 23 14:30:25.433:RADIUS: h323-setup-time [25] 50 "h323-setup-time=14:30:25.429 GMT Wed Jan 23 2002"
Jan 23 14:30:25.433:RADIUS: Vendor, Cisco [26] 26
Jan 23 14:30:25.433:RADIUS: h323-gw-id [33] 20 "h323-gw-id=OrigGW."
Jan 23 14:30:25.433:RADIUS: Vendor, Cisco [26] 56
Jan 23 14:30:25.433:RADIUS: Conf-Id [24] 50 "h323-conf-id=931C146B 0F4411D6 AB5591F0 CBF3D765"
Jan 23 14:30:25.433:RADIUS: Vendor, Cisco [26] 31
Jan 23 14:30:25.437:RADIUS: h323-call-origin [26] 25 "h323-call-origin=answer"
Jan 23 14:30:25.437:RADIUS: Vendor, Cisco [26] 32
Jan 23 14:30:25.437:RADIUS: h323-call-type [27] 26 "h323-call-type=Telephony"
Jan 23 14:30:25.437:RADIUS: Vendor, Cisco [26] 65
Jan 23 14:30:25.437:RADIUS: Cisco AVpair [1] 59 "h323-incoming-conf-id=931C146B 0F4411D6 AB5591F0 CBF3D765"
Jan 23 14:30:25.437:RADIUS: Vendor, Cisco [26] 30
Jan 23 14:30:25.437:RADIUS: Cisco AVpair [1] 24 "subscriber=RegularLine"
Jan 23 14:30:25.437:RADIUS: User-Name [1] 9 "1110001"
Jan 23 14:30:25.437:RADIUS: Acct-Status-Type [40] 6 Start [1]
Jan 23 14:30:25.437:RADIUS: Vendor, Cisco [26] 19
Jan 23 14:30:25.437:RADIUS: cisco-nas-port [2] 13 "Serial6/0:0"
Jan 23 14:30:25.437:RADIUS: NAS-Port [5] 6 0
Jan 23 14:30:25.437:RADIUS: Vendor, Cisco [26] 29
Jan 23 14:30:25.437:RADIUS: Cisco AVpair [1] 23 "interface=Serial6/0:0"
Jan 23 14:30:25.437:RADIUS: Called-Station-Id [30] 9 "2210001"
Jan 23 14:30:25.437:RADIUS: Calling-Station-Id [31] 9 "1110001"
Jan 23 14:30:25.437:RADIUS: NAS-Port-Type [61] 6 Async [0]
Jan 23 14:30:25.437:RADIUS: Service-Type [6] 6 Login [1]
Jan 23 14:30:25.437:RADIUS: NAS-IP-Address [4] 6 192.168.81.101
Jan 23 14:30:25.437:RADIUS: Event-Timestamp [55] 6 1011796225
Jan 23 14:30:25.437:RADIUS: Delay-Time [41] 6 0
Jan 23 14:30:25.441:RADIUS/ENCODE(00071EC0):Unsupported AAA attribute start_time
Jan 23 14:30:25.441:RADIUS/ENCODE(00071EC0):Unsupported AAA attribute timezone
Jan 23 14:30:25.441:RADIUS(00071EC0):sending
Jan 23 14:30:25.441:RADIUS:Send to unknown id 27 192.168.41.57:1813, Accounting-Request, len 411
Jan 23 14:30:25.441:RADIUS: authenticator 15 83 23 D8 0B B2 3A C2 - 1D 8C EF B4 18 0F 1C 65
Jan 23 14:30:25.441:RADIUS: Acct-Session-Id [44] 10 "000B5572"
Jan 23 14:30:25.441:RADIUS: Vendor, Cisco [26] 56
Jan 23 14:30:25.441:RADIUS: h323-setup-time [25] 50 "h323-setup-time=14:30:25.441 GMT Wed Jan 23 2002"
Jan 23 14:30:25.441:RADIUS: Vendor, Cisco [26] 26
Jan 23 14:30:25.441:RADIUS: h323-gw-id [33] 20 "h323-gw-id=OrigGW."
Jan 23 14:30:25.441:RADIUS: Vendor, Cisco [26] 56
Jan 23 14:30:25.441:RADIUS: Conf-Id [24] 50 "h323-conf-id=931C146B 0F4411D6 AB5591F0 CBF3D765"
Jan 23 14:30:25.441:RADIUS: Vendor, Cisco [26] 34
Jan 23 14:30:25.441:RADIUS: h323-call-origin [26] 28 "h323-call-origin=originate"
Jan 23 14:30:25.441:RADIUS: Vendor, Cisco [26] 27
Jan 23 14:30:25.441:RADIUS: h323-call-type [27] 21 "h323-call-type=VoIP"
Jan 23 14:30:25.441:RADIUS: Vendor, Cisco [26] 65
Configuration Examples for SIP AAA Features
This section provides the following configuration examples:
•![]() SIP - Enhanced Billing Support for Gateways: Examples
SIP - Enhanced Billing Support for Gateways: Examples
•![]() SIP: Gateway HTTP Authentication Digest: Examples
SIP: Gateway HTTP Authentication Digest: Examples
SIP - Enhanced Billing Support for Gateways: Examples
The following configuration example highlights the minimal configuration options that are necessary to carry out the full feature. After you configure the aaa username command described in this document, the gateway uses the information received in the SIP Authorization header and makes it available to AAA and Tcl IVR services. Typically, if you expect to use the full functionality of this feature, AAA and Tcl IVR have been configured previously.
Router# show running-config
Building configuration...
Current configuration : 4017 bytes
!
version 12.3
no service single-slot-reload-enable
service timestamps debug datetime msec
service timestamps log uptime
no service password-encryption
!
hostname 3640-1
!
logging rate-limit console 10 except errors
! Need the following aaa line
aaa new-model
!
! Need the following four aaa lines
aaa authentication login h323 group radius
aaa authorization exec h323 group radius
aaa accounting connection h323 start-stop group radius
aaa session-id common
enable password lab
!
memory-size iomem 15
clock timezone GMT 0
voice-card 2
!
ip subnet-zero!
ip domain-name example.sip.com
ip name-server 172.18.192.154
ip name-server 10.10.1.5
!
no ip dhcp-client network-discovery
isdn switch-type primary-5ess
isdn voice-call-failure 0
!
voice service voip
sip
rel1xx disable
!
fax interface-type fax-mail
mta receive maximum-recipients 0
call-history-mib retain-timer 500
!
controller E1 1/0
!
controller E1 1/1
!
controller T1 2/0
framing esf
linecode b8zs
pri-group timeslots 1-24
!
controller T1 2/1
framing sf
linecode ami
!
! Need the following three lines
gw-accounting h323
gw-accounting h323 vsa
gw-accounting voip
!
interface Ethernet0/0
ip address 10.10.1.4 255.255.255.0
half-duplex
ip rsvp bandwidth 7500 7500
!
interface Ethernet0/1
no ip address
shutdown
half-duplex
!
interface Ethernet0/2
no ip address
shutdown
half-duplex
!
interface Ethernet0/3
no ip address
shutdown
half-duplex
!
interface FastEthernet1/0
ip address 172.18.192.197 255.255.255.0
duplex auto
speed auto
ip rsvp bandwidth 75000 75000
!
interface Serial2/0:23
no ip address
no logging event link-status
isdn switch-type primary-5ess
isdn incoming-voice modem
isdn T306 200000
isdn T310 200000
no cdp enable
!
ip classless
ip route 10.0.0.0 255.0.0.0 172.18.192.1
ip route 172.18.0.0 255.255.0.0 172.18.192.1
no ip http server
!
ip radius source-interface FastEthernet1/0
logging source-interface FastEthernet1/0
!
! Need the following radius-server lines for accounting/authentication
radius-server host 172.18.192.154 auth-port 1645 acct-port 1646
radius-server retransmit 1
radius-server key lab
radius-server vsa send accounting
radius-server vsa send authentication
call rsvp-sync
!
! Need the following call application lines in order to enable
! tcl scripting feature.
call application voice voice_billing tftp://172.18.207.15/app_passport_silent.2.0.0.0.tcl
!
voice-port 2/0:23
!
voice-port 3/0/0
!
voice-port 3/0/1
!
voice-port 3/1/0
!
voice-port 3/1/1
!
mgcp profile default
dial-peer cor custom
!
dial-peer voice 3640110 pots
destination-pattern 3640110
port 3/0/0
!
dial-peer voice 3640120 pots
destination-pattern 3640120
port 3/0/1
!
dial-peer voice 3660110 voip
destination-pattern 3660110
session protocol sipv2
session target ipv4:172.18.192.194
codec g711ulaw
!
dial-peer voice 3660120 voip
destination-pattern 3660120
session protocol sipv2
session target ipv4:172.18.192.194
codec g711ulaw
!
dial-peer voice 222 pots
huntstop
application session
destination-pattern 222
no digit-strip
direct-inward-dial
port 2/0:23
!
! Need to add the application line below to enable the tcl script
dial-peer voice 999 voip
application voice_billing
destination-pattern ...
session protocol sipv2
session target ipv4:10.10.1.2:5061
codec g711ulaw
!
! Need to add the aaa line below in order to enable proxy-authorization
! header processing
sip-ua
aaa username proxy-auth
!
line con 0
exec-timeout 0 0
length 0
line aux 0
line vty 0 4
!
!end
SIP: Gateway HTTP Authentication Digest: Examples
This section provides the following configuration examples:
•![]() SIP: Gateway HTTP Authentication Digest Feature Disabled
SIP: Gateway HTTP Authentication Digest Feature Disabled
•![]() SIP: Gateway HTTP Authentication Digest Feature Enabled
SIP: Gateway HTTP Authentication Digest Feature Enabled
SIP: Gateway HTTP Authentication Digest Feature Disabled
Router# show running-config
Building configuration...
Current configuration :4903 bytes
!
version 12.3
no parser cache
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
service internal
!
hostname Router
!
boot-start-marker
boot-end-marker
!
enable secret 5 $1$Fyay$DfmV/uLXX.X94CoaRy569.
enable password lab
!
voice-card 3
!
aaa new-model
!
aaa authentication login h323 group radius
aaa authorization exec h323 group radius
aaa accounting connection h323 start-stop group radius
aaa session-id common
ip subnet-zero
ip tcp path-mtu-discovery
!
ip cef
ip domain name example.sip.com
ip name-server 172.18.192.48
!
ip dhcp pool 1
host 172.18.193.173 255.255.255.0
client-identifier 0030.94c2.5d00
option 150 ip 172.18.193.120
default-router 172.18.193.120
!
voice call carrier capacity active
!
voice service pots
!
voice service voip
sip
rel1xx disable
!
voice class codec 1
codec preference 1 g729r8
codec preference 2 g711ulaw
codec preference 5 g726r16
codec preference 6 g726r24
codec preference 7 g726r32
codec preference 8 g723ar53
codec preference 9 g723ar63
!
voice class codec 2
codec preference 1 g711ulaw
codec preference 2 g729r8
codec preference 5 g726r16
codec preference 6 g726r24
!
fax interface-type fax-mail
!
translation-rule 100
!
interface FastEthernet0/0
ip address 172.18.193.120 255.255.255.0
ip mtu 900
duplex auto
speed auto
no cdp enable
ip rsvp bandwidth 75000 75000
!
interface FastEthernet0/1
no ip address
no ip mroute-cache
shutdown
duplex auto
speed auto
no cdp enable
!
ip http server
ip classless
ip route 0.0.0.0 0.0.0.0 FastEthernet0/0
ip route 10.0.0.0 255.0.0.0 172.18.193.1
ip route 172.18.0.0 255.255.0.0 172.18.193.1
!
ip radius source-interface FastEthernet0/0
logging source-interface FastEthernet0/0
dialer-list 1 protocol ip permit
snmp-server engineID local 00000009020000309426F6D0
snmp-server community public RO
snmp-server community private RW
snmp-server packetsize 4096
snmp-server enable traps tty
!
tftp-server flash:XMLDefault.cnf.xml
!
radius-server host 172.18.192.108 auth-port 1645 acct-port 1646
radius-server retransmit 1
radius-server key lab
radius-server vsa send accounting
radius-server vsa send authentication
!
control-plane
!
voice-port 1/0/0
!
voice-port 1/0/1
!
voice-port 1/1/0
!
voice-port 1/1/1
!
voice-port 2/0/0
station-id name 36602
station-id number 36602
!
voice-port 2/0/1
!
mgcp
mgcp sdp simple
!
dial-peer cor custom
!
dial-peer voice 1 pots
application session
destination-pattern 36602
port 2/0/0
!
dial-peer voice 5 voip
application session
destination-pattern 5550123
session protocol sipv2
session target ipv4:172.18.193.187
!
dial-peer voice 81 voip
application session
destination-pattern 3100801
session protocol sipv2
session target ipv4:172.18.193.100
req-qos controlled-load
acc-qos controlled-load
!
dial-peer voice 41 voip
application session
destination-pattern 333
session protocol sipv2
session target ipv4:10.102.17.80
dtmf-relay rtp-nte
!
dial-peer voice 7 voip
application session
destination-pattern 999
session protocol sipv2
session target ipv4:172.18.193.98
incoming called-number 888
!
dial-peer voice 38 voip
application session
destination-pattern 3100802
voice-class codec 1
session protocol sipv2
session target ipv4:172.18.193.99
!
dial-peer voice 88 voip
preference 1
destination-pattern 888
session protocol sipv2
session target ipv4:172.18.193.187
!
dial-peer voice 123 voip
destination-pattern 222
session protocol sipv2
session target ipv4:10.102.17.80
!
dial-peer voice 6 voip
destination-pattern 36601
session protocol sipv2
session target ipv4:172.18.193.98
session transport udp
incoming called-number 36602
!
gateway
timer receive-rtp 1200
!
sip-ua
retry invite 1
retry bye 2
timers expires 60000
!
rtr responder
!
line con 0
exec-timeout 0 0
transport preferred all
transport output all
line aux 0
transport preferred all
transport output all
line vty 0 4
password lab
transport preferred all
transport input all
transport output all
!
end
SIP: Gateway HTTP Authentication Digest Feature Enabled
Router# show running-config
Building configuration...
Current configuration :5087 bytes
!
version 12.3
no parser cache
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
service internal
!
hostname Router
!
boot-start-marker
boot-end-marker
!
enable secret 5 $1$Fyay$DfmV/uLXX.X94CoaRy569.
enable password lab
!
voice-card 3
!
aaa new-model
!
aaa authentication login h323 group radius
aaa authorization exec h323 group radius
aaa accounting connection h323 start-stop group radius
aaa session-id common
ip subnet-zero
ip tcp path-mtu-discovery
!
ip cef
ip domain name example.sip.com
ip name-server 172.18.192.48
!
ip dhcp pool 1
host 172.18.193.173 255.255.255.0
client-identifier 0030.94c2.5d00
option 150 ip 172.18.193.120
default-router 172.18.193.120
!
voice call carrier capacity active
!
voice service pots
!
voice service voip
sip
rel1xx disable
!
voice class codec 1
codec preference 1 g729r8
codec preference 2 g711ulaw
codec preference 5 g726r16
codec preference 6 g726r24
codec preference 7 g726r32
codec preference 8 g723ar53
codec preference 9 g723ar63
!
voice class codec 2
codec preference 1 g711ulaw
codec preference 2 g729r8
codec preference 5 g726r16
codec preference 6 g726r24
!
fax interface-type fax-mail
!
translation-rule 100
!
interface FastEthernet0/0
ip address 172.18.193.120 255.255.255.0
ip mtu 900
duplex auto
speed auto
no cdp enable
ip rsvp bandwidth 75000 75000
!
interface FastEthernet0/1
no ip address
no ip mroute-cache
shutdown
duplex auto
speed auto
no cdp enable
!
ip http server
ip classless
ip route 0.0.0.0 0.0.0.0 FastEthernet0/0
ip route 10.0.0.0 255.0.0.0 172.18.193.1
ip route 172.18.0.0 255.255.0.0 172.18.193.1
!
ip radius source-interface FastEthernet0/0
logging source-interface FastEthernet0/0
dialer-list 1 protocol ip permit
snmp-server engineID local 00000009020000309426F6D0
snmp-server community public RO
snmp-server community private RW
snmp-server packetsize 4096
snmp-server enable traps tty
!
tftp-server flash:XMLDefault.cnf.xml
!
radius-server host 172.18.192.108 auth-port 1645 acct-port 1646
radius-server retransmit 1
radius-server key lab
radius-server vsa send accounting
radius-server vsa send authentication
!
control-plane
!
voice-port 1/0/0
!
voice-port 1/0/1
!
voice-port 1/1/0
!
voice-port 1/1/1
!
voice-port 2/0/0
station-id name 36602
station-id number 36602
!
voice-port 2/0/1
!
mgcp
mgcp sdp simple
!
dial-peer cor custom
!
dial-peer voice 1 pots
application session
destination-pattern 36602
port 2/0/0
authentication username user1 password password1 realm example1.com ! authentication
xample 1
authentication username user2 password password2 realm example2.com ! authentication
xample 2
!
dial-peer voice 5 voip
application session
destination-pattern 5550123
session protocol sipv2
session target ipv4:172.18.193.187
!
dial-peer voice 81 voip
application session
destination-pattern 3100801
session protocol sipv2
session target ipv4:172.18.193.100
req-qos controlled-load
acc-qos controlled-load
!
dial-peer voice 41 voip
application session
destination-pattern 333
session protocol sipv2
session target ipv4:10.102.17.80
dtmf-relay rtp-nte
!
dial-peer voice 7 voip
application session
destination-pattern 999
session protocol sipv2
session target ipv4:172.18.193.98
incoming called-number 888
!
dial-peer voice 38 voip
application session
destination-pattern 3100802
voice-class codec 1
session protocol sipv2
session target ipv4:172.18.193.99
!
dial-peer voice 88 voip
preference 1
destination-pattern 888
session protocol sipv2
session target ipv4:172.18.193.187
!
dial-peer voice 123 voip
destination-pattern 222
session protocol sipv2
session target ipv4:10.102.17.80
!
dial-peer voice 6 voip
destination-pattern 36601
session protocol sipv2
session target ipv4:172.18.193.98
session transport udp
incoming called-number 36602
!
gateway
timer receive-rtp 1200
!
sip-ua
authentication username user3 password password3 ! authentication example 3
retry invite 1
retry bye 2
timers expires 60000
registrar ipv4:172.18.193.187 expires 100 ! registrar example
!
rtr responder
!
line con 0
exec-timeout 0 0
transport preferred all
transport output all
line aux 0
transport preferred all
transport output all
line vty 0 4
password lab
transport preferred all
transport input all
transport output all
!
end
Additional References
General SIP References
•![]() "SIP Features Roadmap" on page 1—Describes how to access Cisco Feature Navigator; also lists and describes, by Cisco IOS release, SIP features for that release.
"SIP Features Roadmap" on page 1—Describes how to access Cisco Feature Navigator; also lists and describes, by Cisco IOS release, SIP features for that release.
•![]() "Overview of SIP" on page 1—Describes underlying SIP technology; also lists related documents, standards, MIBs, RFCs, and how to obtain technical assistance.
"Overview of SIP" on page 1—Describes underlying SIP technology; also lists related documents, standards, MIBs, RFCs, and how to obtain technical assistance.
References Mentioned in This Chapter (Listed Alphabetically)
•![]() Cisco IOS Security Command Reference at
Cisco IOS Security Command Reference at
http://www.cisco.com/en/US/docs/ios/security/command/reference/sec_book.html
•![]() Cisco IOS Security Configuration Guide, Release 12.4T at http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/12_4T/sec_securing_user_services_12.4t_book.html
Cisco IOS Security Configuration Guide, Release 12.4T at http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/12_4T/sec_securing_user_services_12.4t_book.html
•![]() Cisco IOS SIP Configuration Guide, Release 12.4T at http://www.cisco.com/en/US/docs/ios/voice/sip/configuration/guide/12_4t/sip_12_4t_book.html
Cisco IOS SIP Configuration Guide, Release 12.4T at http://www.cisco.com/en/US/docs/ios/voice/sip/configuration/guide/12_4t/sip_12_4t_book.html
•![]() Cisco IOS Tcl IVR and VoiceXML Application Guide at http://www.cisco.com/en/US/docs/ios/voice/ivr/configuration/guide/tcl_c.html
Cisco IOS Tcl IVR and VoiceXML Application Guide at http://www.cisco.com/en/US/docs/ios/voice/ivr/configuration/guide/tcl_c.html
•![]() Cisco Resource Policy Management System 2.0 at http://www.cisco.com/en/US/products/sw/netmgtsw/ps2074/tsd_products_support_eol_series_home.html
Cisco Resource Policy Management System 2.0 at http://www.cisco.com/en/US/products/sw/netmgtsw/ps2074/tsd_products_support_eol_series_home.html
•![]() Cisco Tcl IVR API Programmer's Guide at http://www.cisco.com/en/US/docs/ios/voice/tcl/developer/guide/tclivrv2.html
Cisco Tcl IVR API Programmer's Guide at http://www.cisco.com/en/US/docs/ios/voice/tcl/developer/guide/tclivrv2.html
•![]() Enhancements to the Session Initiation Protocol for VoIP on Cisco Access Platforms at http://www.cisco.com/en/US/docs/ios/12_2t/12_2t11/feature/guide/ftsipgv1.html
Enhancements to the Session Initiation Protocol for VoIP on Cisco Access Platforms at http://www.cisco.com/en/US/docs/ios/12_2t/12_2t11/feature/guide/ftsipgv1.html
•![]() Inter-Domain Gatekeeper Security Enhancement, Cisco IOS Release 12.2(4)T at http://www.cisco.com/en/US/docs/ios/12_2/12_2x/12_2xa/feature/guide/ft_ctoke.html
Inter-Domain Gatekeeper Security Enhancement, Cisco IOS Release 12.2(4)T at http://www.cisco.com/en/US/docs/ios/12_2/12_2x/12_2xa/feature/guide/ft_ctoke.html
•![]() RADIUS Vendor-Specific Attributes Voice Implementation Guide at http://noc.hsdn.org/files/univercd/cc/td/doc/product/access/acs_serv/vapp_dev/vsaig3.htm
RADIUS Vendor-Specific Attributes Voice Implementation Guide at http://noc.hsdn.org/files/univercd/cc/td/doc/product/access/acs_serv/vapp_dev/vsaig3.htm

Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincidental.
© 2007 Cisco Systems, Inc. All rights reserved.
1 Introduced as part of the SIP Gateway Support of RSVP and TEL URL feature.
 Feedback
Feedback