Introduction
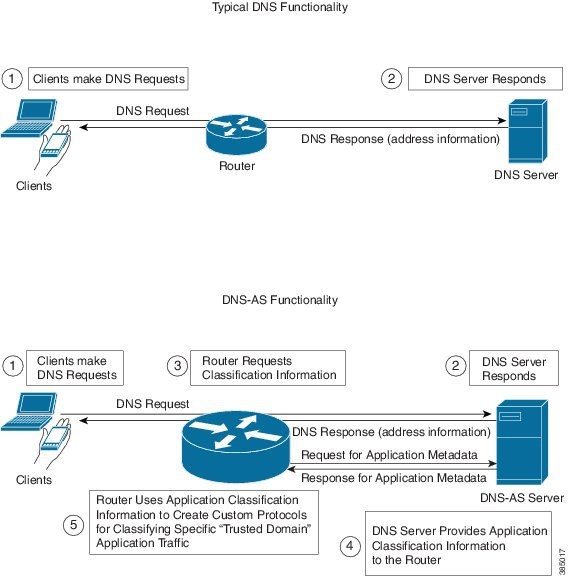
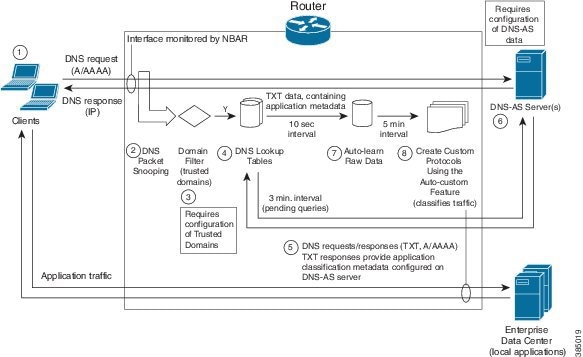
Working together with Cisco NBAR2, "DNS as Authoritative Source," DNS-AS, provides centralized control of custom application classification information. Classification information (metadata such as application name, ID, traffic class, business relevance, and so on) is used by NBAR2 to recognize the network traffic of specific applications, and to classify the traffic by assigning parameters useful both in reporting and in applying network traffic policy.
Classification Metadata Reflects Organizational Needs, Policy Intent
Different enterprises have different requirements for reporting and shaping traffic through network traffic policy. This is partly because they use different local applications internal to the organization, and partly because widely used applications may have a different business relevance to different organizations.
Consequently, it is often helpful to customize application classification information to determine how network traffic is reported and shaped by traffic policy.
Leveraging DNS Infrastructure
DNS-AS leverages the universally available DNS query/response infrastructure to enable local DNS servers within an organization to propagate application classification information to routers in an enterprise network. The local DNS servers function as "authoritative source" for both DNS data and custom classification data.
Through its flexibility and simplicity, DNS-AS unlocks traffic reporting and shaping functionality that may otherwise be difficult to configure.
DNS-AS In Use
Setup
DNS-AS setup includes configuration steps on the local DNS server(s) and routers within the enterprise network.
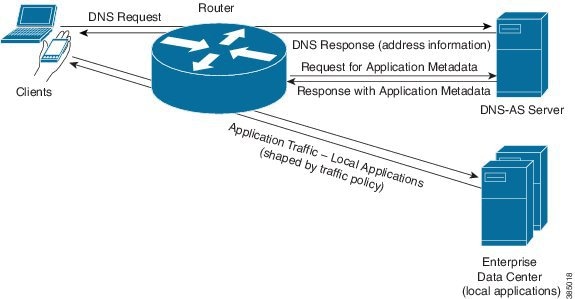
Local DNS servers are configured with the classification information for specific "trusted domain" sites/applications. This enables a network administrator to control how a network handles traffic for these local, server-based applications - for example, those used in an enterprise intranet.
Routers are configured to detect DNS traffic for the "trusted domains" (sites/applications) controlled by DNS-AS.
Propagating Classification Information
When configuration is complete, the DNS servers can provide classification information for the "trusted domain" applications.
When a client in the network makes a DNS request, the DNS response is sent as usual. If the request relates to a "trusted domain" application, the router then queries the local DNS server about the application. The DNS server sends the router the network address data and the relevant classification information.
Using the Classification Information
On the routers that receive the information, NBAR2 uses the information to automatically create custom protocols that classify the traffic.
Traffic classification affects application visibility functions, such as reporting of traffic, and it affects application control, such as the use of QoS traffic-shaping policy.
Priority
Custom application protocols have priority over standard Cisco NBAR2 Protocol Pack protocols, so it is possible to override Protocol Pack protocols by configuring application classification metadata using DNS-AS.
Predefined Protocols and Customized Protocols
For most network traffic, the predefined protocols in the NBAR2 Protocol Pack are sufficient to identify and classify traffic.
For local applications not covered by the Protocol Pack, such as the sites and applications in an enterprise's intranet, DNS-AS provides a centralized mechanism for controlling traffic.
Classification and Traffic Policy
Application classification and traffic policy are related but distinct. DNS-AS provides classification information, but does not directly control traffic policy.
Classification of applications may be controlled by:
-
Cisco-provided Protocol Pack
-
User-defined protocols
-
Automatically-generated custom protocols
-
DNS-AS-specified application metadata that indirectly creates custom protocols
Traffic policy may be defined by:
-
Direct configuration of policy on the router
-
Network controller, such as SDN, providing traffic policy
The following table clarifies the different types of protocols that can control classification of applications.
|
Protocol Type |
Source |
|---|---|
|
NBAR2 Protocol Pack protocols |
Cisco-provided |
|
Custom protocols defined manually |
User-defined on router |
|
Custom protocols defined automatically using DNS-AS |
User-defined
|
Efficient, Centralized Configuration
An advantage to using DNS-AS is efficiency of configuration. DNS-AS helps to control application classification over the entire enterprise network, but most of its configuration tasks are handled on the local DNS-AS server(s) operating within the network.
Configuration tasks include:
-
Configuring application metadata: Defining the metadata for each “trusted domain” application during DNS-AS server setup; modifying the metadata at any time.
-
Configuring trusted domains: Trusted domains are configured on the individual routers within the network.
Adaptability
Centralized configuration makes it easier to adapt to changes in the local applications. For example, if the IP addresses of the servers handling a local application change, or if the metadata attributes (application-class, business-relevance, and so on) for an application change, you can configure the changes on the local DNS-AS server(s) and the updates are propagated to the routers throughout the entire network.
DNS-AS vs. SDN Controller Functionality
DNS-AS and SDN controllers, when used, both operate broadly on the network. While an SDN controller provides traffic policy to devices in the network, DNS-AS provides application-match metadata.
NBAR2 Responding to Evolving Networks and Network Traffic
Applications Using End-to-End Encryption
Many of today's network applications operate in clear text over common transports such as HTTP. These applications can be identified using Deep Packet Inspection (DPI), a resource-intensive method. However, more and more network applications are communicating with end-to-end encryption, preventing identification by DPI.
Enterprise Networking Moving to the Cloud
A trend in enterprise networks is moving to the cloud. Instead of operating their own full-scale enterprise network, organizations are opting to move network infrastructure to cloud service providers. Their downsized internal network may have to control a variety of network devices located anywhere in the world. Those devices, managed by the cloud services provider, may not be under their direct administrative control.
NBAR Flexibility, Agility
Cisco NBAR2 features, such as DNS-AS, are evolving to address the changing trends in enterprise networking. While end-to-end encryption and migration to the cloud complicate the task of providing application visibility and control, NBAR continues to aim for:
-
Simplicity in network configuration
-
Agility at scale
Comparison with the Custom Protocol Feature
The DNS-AS configuration process is similar in some ways to using the NBAR2 custom protocol feature to create a protocol for a specific application relevant to the organization, but DNS-AS does not operate router-by-router for each individual application.
DNS-AS also provides an easier method of reconfiguring how numerous devices within the network handle custom applications.
-
When using the custom protocol feature, if any attributes of a custom application change, or if the server hosting the application changes, then updates to the custom application protocol must be made on each router in the network, one by one. In a network containing hundreds of routers, this process is impractical.
-
When using DNS-AS, the single reconfiguration on the DNS server propagates information to all routers in the network.

 Feedback
Feedback