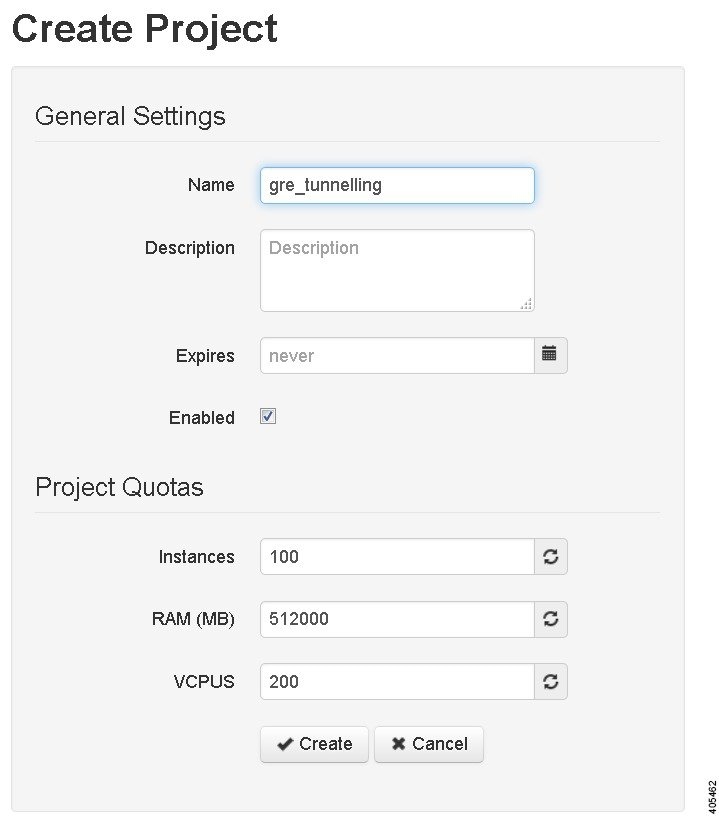
Build a Configuration Overview
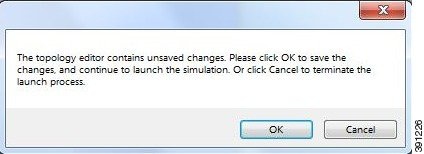
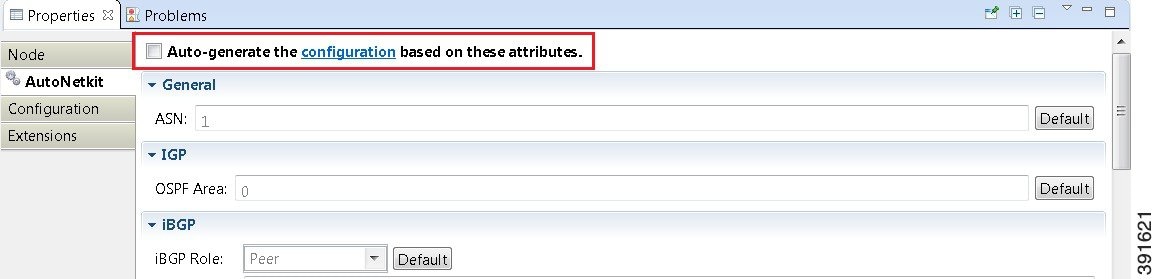
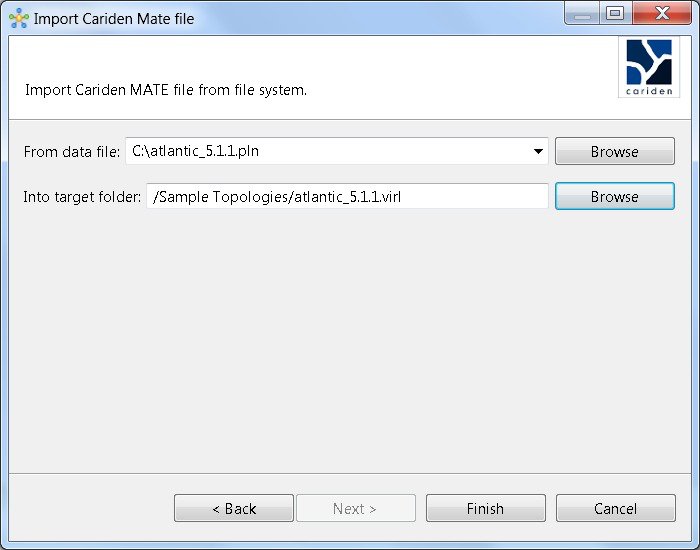
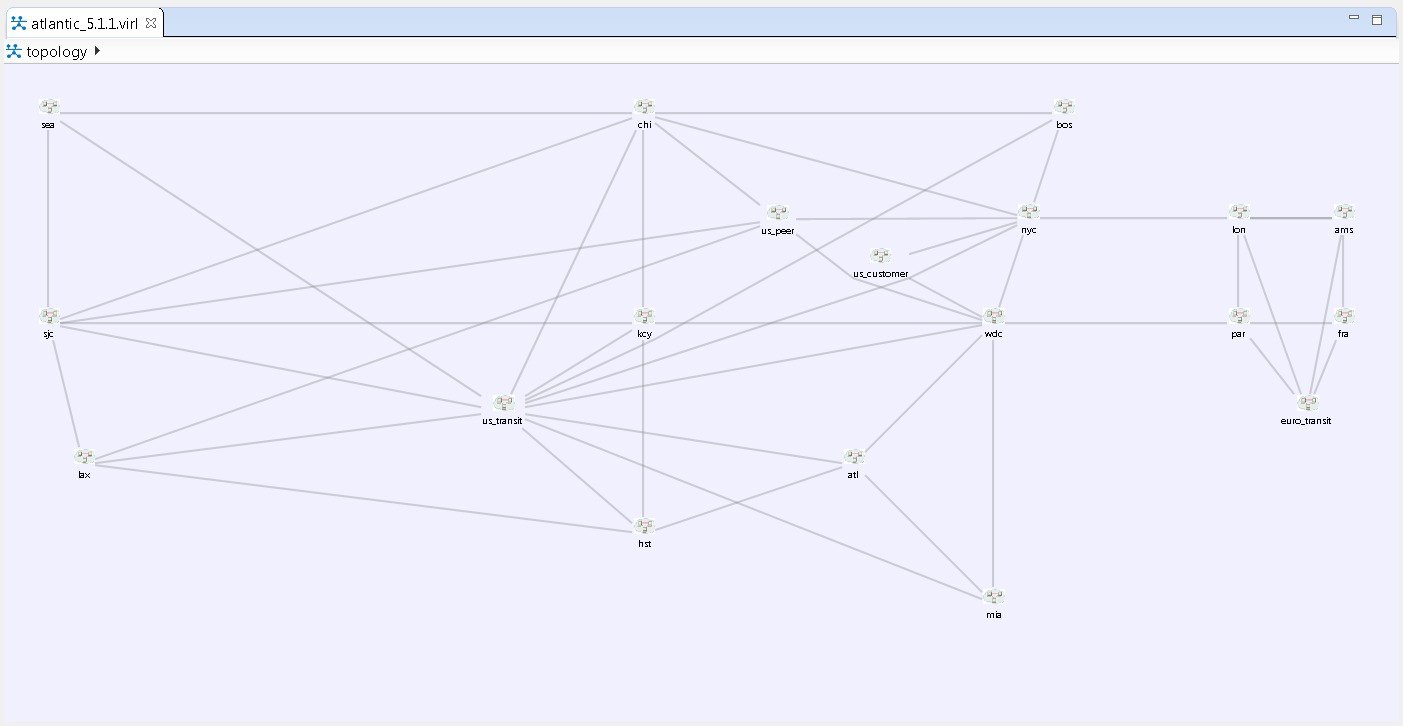
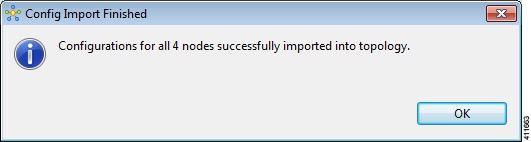
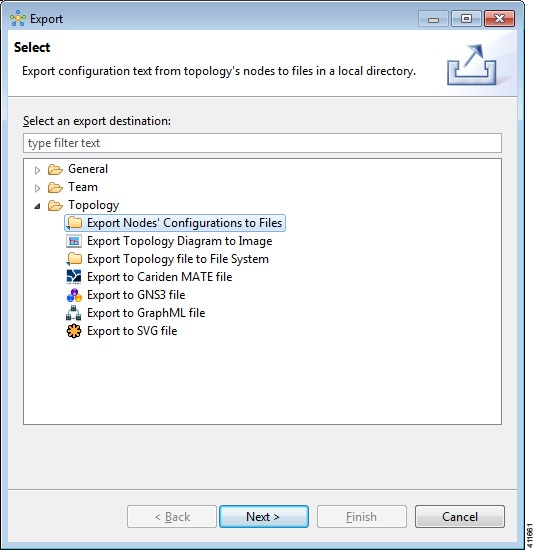
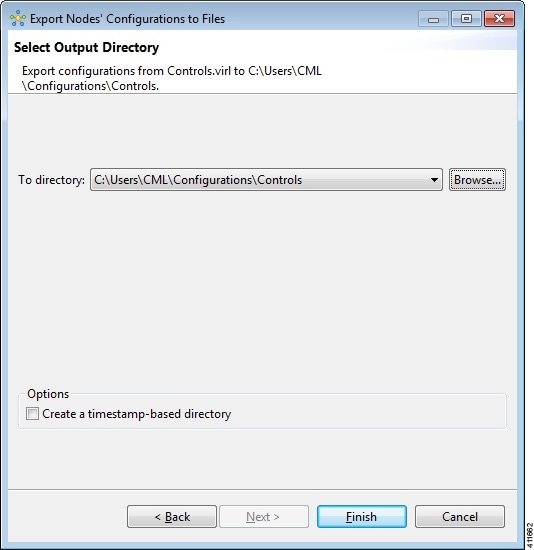
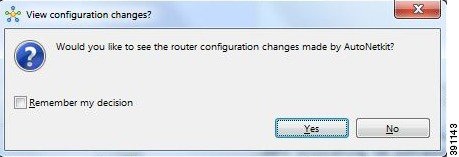
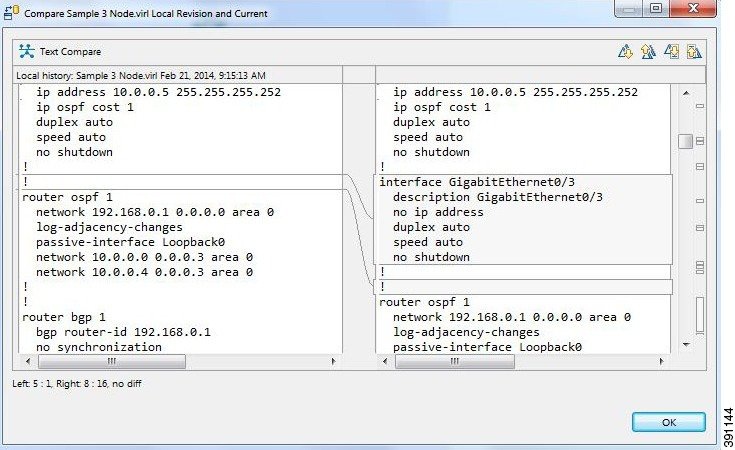
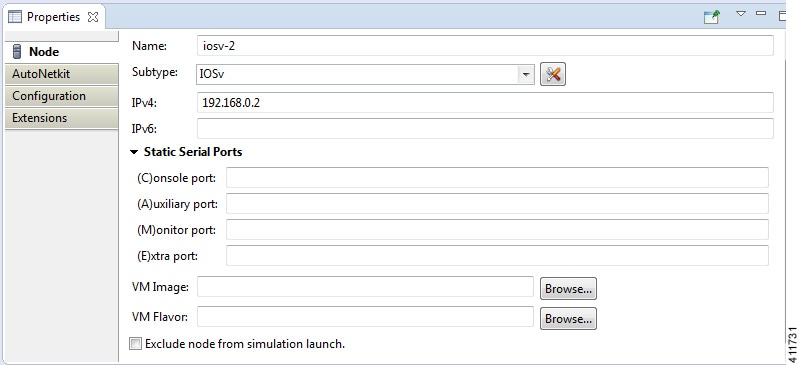
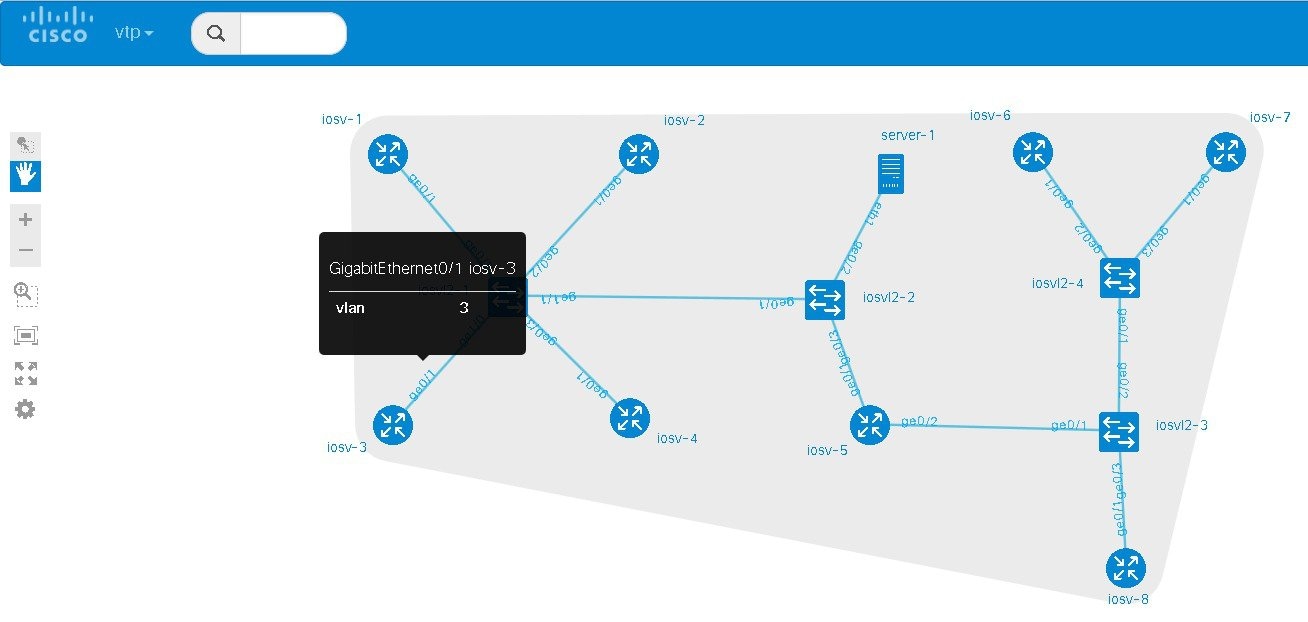
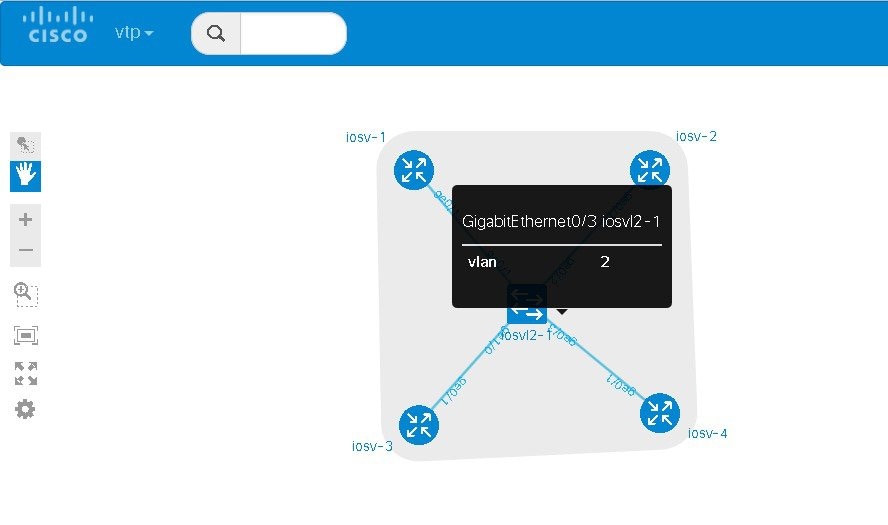
In the build phase, you build the configurations for each node. After selecting the options for the overall topology and each node, you create the configuration files. Alternatively, you can use AutoNetkit to create the configuration files.
You can modify and save configuration files for the topology and for each node in your topology.

 Feedback
Feedback