Release Notes for the Catalyst 4500E Series Switch, Cisco IOS XE 3.6.xE
Available Languages
Table of Contents
Release Notes for the Catalyst 4500E Series Switch, Cisco IOS XE Release 3.6.xE
Supported Hardware on the Catalyst 4500E Series Switch
Supported E Series Hardware on Cisco IOS XE Release 3.6.0E
Features Not Supported on the Cisco Catalyst 4500E Series Switch
New Software Features in Release IOS XE 3.6.10E
New Software Features in Release IOS XE 3.6.8E
New Software Features in Release IOS XE 3.6.7E
New Software Features in Release IOS XE 3.6.6E
New Software Features in Release IOS XE 3.6.5aE
New Software Features in Release IOS XE 3.6.5E
New Software Features in Release IOS XE 3.6.4E
New Software Features in Release IOS XE 3.6.3E
New Hardware Features in Release IOS XE 3.6.2E
New Software Features in Release IOS XE 3.6.2E
New Software Features in Release IOS XE 3.6.1E
New Hardware Features in Release IOS XE 3.6.0E
New Software Features in Release IOS XE 3.6.0E
New and Modified IOS Software Features Supported in Cisco IOS XE 3.5.0E
Cisco IOS XE to Cisco IOS Version Number Mapping
Manual Field Programmable Gate Array Upgrades
Upgrading ROMMON Image for Supervisor Engine 8-E
Identifying an +E Chassis and ROMMON
Resolved Caveats for Cisco IOS XE Release 3.6.10E
Resolved Caveats for Cisco IOS XE Release 3.6.9E
Resolved Caveats for Cisco IOS XE Release 3.6.8E
Resolved Caveats for Cisco IOS XE Release 3.6.7E
Resolved Caveats for Cisco IOS XE Release 3.6.6E
Resolved Caveats for Cisco IOS XE Release 3.6.5Ea
Resolved Caveats for Cisco IOS XE Release 3.6.5E
Resolved Caveats for Cisco IOS XE Release 3.6.4E
Resolved Caveats for Cisco IOS XE Release 3.6.3E
Resolved Caveats for Cisco IOS XE Release 3.6.2E
Resolved Caveats for Cisco IOS XE Release 3.6.1E
Resolved Caveats for Cisco IOS XE Release 3.6.0E
Release Notes for the Catalyst 4500E Series Switch, Cisco IOS XE Release 3.6.xE
Current release
IOS XE 3.6.10E—May 31, 2019
Prior releases
IOS XE 3.6.9E—September 12, 2018, IOS XE 3.6.8E—January 31, 2018, IOS XE 3.6.7E—July 10, 2017, IOS XE 3.6.6E—December 23, 2016, IOS XE 3.6.5aE, IOS XE 3.6.5E, IOS XE 3.6.4E, IOS XE 3.6.3E, IOS XE 3.6.2E, IOS XE 3.6.1E, IOS XE 3.6.0E
This release note describes the features, modifications, and caveats for the Cisco IOS XE 3.6.xE software on the Catalyst 4500E series switch with Supervisor Engine 7-E, 7L-E, and 8-E.

Note![]() For the Supervisor Engine 8-E to support IOS XE 3.6.0E, the ROMMON version must be upgraded to 15.1(1r)SG4. (Refer to Upgrading the System Software).
For the Supervisor Engine 8-E to support IOS XE 3.6.0E, the ROMMON version must be upgraded to 15.1(1r)SG4. (Refer to Upgrading the System Software).
Cisco IOS XE 3.6.0E is a feature rich new software feature release for IOS and IOS-XE based Catalyst Access Switching products (Cat4500E/X, 3850/3650, 3K-X, Cat2K and 2K/3K Compact switches) which brings new innovations for Converged Access in wired and wireless topologies, IT Simplicity, Application Experience, and Mobility. This release will provide long-lived extended maintenance with planned rebuilds. It will also have all the Govt. certifications for IOS-XE and currently shipping IOS platforms.
Cisco IOS XE 3.6.0E provides VSS support on Supervisor Engine 8-E with complete feature parity with Supervisor Engine 7-E.
Support for Cisco IOS XE Release 3.6.0E follows the standard Cisco Systems® support policy, available at
http://www.cisco.com/en/US/products/products_end-of-life_policy.html
For more information on the Catalyst 4500E series switches, visit the following URL:
http://www.cisco.com//en/US/products/hw/switches/ps4324/index.html

Note![]() Although this release note and those for the Catalyst 4900M, Catalyst 4948E, Catalyst 4948E-F Series Switches, Catalyst 4500 Series Switches, and the Catalyst 4500-X Series Switches differ, each leverages the same Software Configuration Guide, Command Reference Guide, and System Message Guide.
Although this release note and those for the Catalyst 4900M, Catalyst 4948E, Catalyst 4948E-F Series Switches, Catalyst 4500 Series Switches, and the Catalyst 4500-X Series Switches differ, each leverages the same Software Configuration Guide, Command Reference Guide, and System Message Guide.
Cisco IOS Software Packaging
The Enterprise Services image supports all Cisco Catalyst 4500E Series software features based on Cisco IOS Software, including enhanced routing.
The IP Base image supports Open Shortest Path First (OSPF) for Routed Access, Enhanced Interior Gateway Routing Protocol (EIGRP) "limited" Stub Routing, Nonstop Forwarding/Stateful Switchover (NSF/SSO), and RIPv1/v2. The IP Base image does not support enhanced routing features such as BGP, Intermediate System-to-Intermediate System (IS-IS), Full OSPF, Full Enhanced Interior Gateway Routing Protocol (EIGRP) & Virtual Routing Forwarding (VRF-lite).
The LAN Base image complements the existing IP Base and Enterprise Services images. It is focused on customer access and Layer 2 requirements and therefore many of the IP Base features are not required. The IP upgrade image is available if at a later date you require some of those features
Starting with Cisco IOS Release XE 3.5.0E, OSPF Routed Access in IP Base support rose to 1000 routes.
Cisco XE Release Strategy
Customers with Catalyst 4500 Series Switches who need the latest hardware and software features should migrate to Cisco IOS Release XE 3.6.0E.
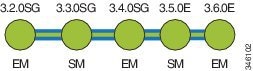
IOS XE 3.2.xSG is an active maintenance train that supports Sup7E only. IOS XE 3.4.xSG is a maintenance train supporting Sup7E and Sup7L-E. IOS XE 3.6.xSG is a maintenance train supporting Sup7E, Sup7L-E and Sup8-E. IOS XE 3.6.xE, 3.4.xSG, and 3.2.xSG are extended maintenance (EM) releases. IOS XE 3.5.xE and 3.3.0SG are standard releases (SM).
Figure 1 displays the release strategy.
Figure 1 Software Release Strategy for the Catalyst 4500E Series Switch
Support
Support for Cisco IOS Software Release XE 3.6.0E follows the standard Cisco Systems® support policy, available at
http://www.cisco.com/en/US/products/products_end-of-life_policy.html
System Requirements
This section describes the system requirements:
- Supported Hardware on the Catalyst 4500E Series Switch
- Supported E Series Hardware on Cisco IOS XE Release 3.6.0E
- Feature Support by Image Type
- MIB Support
- Features Not Supported on the Cisco Catalyst 4500E Series Switch
- Orderable Product Numbers
Supported Hardware on the Catalyst 4500E Series Switch
Table 1 lists the hardware supported on the Catalyst 4500E Series Switch.
Catalyst 4500E-series switch Supervisor Engine 7-E Note This engine is supported on E-series, R-E, and R+E chassis. |
|
Catalyst 4500E-series switch Supervisor Engine 7L-E Note This engine is supported on E-series, R-E, and R+E chassis. |
|
18-port 1000BASE-X (GBIC) Gigabit Ethernet server switching module |
|
12-port 1000BASE-T Gigabit Ethernet and 2-GBIC ports switching module |
|
24-port 10/100/1000BASE-T Gigabit Ethernet RJ-45 switching module |
|
48-port 1000BASE-LX (small form-factor pluggable) Gigabit Ethernet fiber optic interface switching module |
|
6-port Alternately-Wired 10/100/1000BASE-T Catalyst 4500 series Power over Ethernet (PoE) 802.3af or 1000BASE-X SFP |
|
24-port 10/100/1000BASE-T RJ-45 Catalyst 4500 series PoE 802.3af |
|
48-port 10/100/1000BASE-T RJ-45 Catalyst 4500 series PoE 802.3af |
|
12-port 1000BASE-X (small form factor pluggable) module with jumbo frame support |
|
Non-blocking 24-port 1000BASEX (small form factor pluggable) module |
|
80 ports with Gigabit compact SFP (4:1 oversubscribed); 40 modules of Gigabit SFP line card (1000BaseX), providing 24 gigabits per-slot capacity (SFP optional) (2:1 oversubscribed) |
|
48 port 10/100/1000BT with 2 to 1 oversubscription and jumbo frame support |
|
48 port 10/100/1000 Mb with 2 to 1 oversubscription PoE 802.3af providing up to 20 Watts power/port |
|
48 port 10/100/1000 Mb with 2 to 1 oversubscription PoE 802.3at providing up to 30 Watts power/port |
|
48-port 10/100/1000 line card nonblocking PoE 802.3at providing up to 30 Watts power/port |
|
48-port 10/100/1000 line card nonblocking PoE 802.3at and 60 watt UPoE PoE linecard with Ethernet Energy Efficient feature. |
|
48-port 10/100/1000 nonblocking line card with the Ethernet Energy Efficient feature |
|
48-port 1000Base-X SFP (small form factor pluggable) line card |
|
24-port 1000Base-X SFP (small form factor pluggable) line card |
|
12-port 1000Base-X SFP (small form factor pluggable) line card |
|
24-port 100BASE-FX Fast Ethernet MT-RJ multimode fiber switching module |
|
48-port 100BASE-FX Fast Ethernet MT-RJ multimode fiber switching module |
|
48-port 100BASE-LX10 Fast Ethernet MT-RJ single-mode fiber switching module |
|
24-port 10/100BASE-TX RJ-45 Cisco Catalyst 4500 series PoE 802.3af |
|
32-port 10/100 Fast Ethernet RJ-45, plus 2-port 1000BASE-X (GBIC) Gigabit Ethernet switching module |
|
48-port 10/100BASE-T RJ-45 Cisco Catalyst 4500 series PoE 802.3af |
|
48-port 10/100 Fast Ethernet RJ-21 Cisco Catalyst 4500 series PoE 802.3af telco |
|
32-port 10/100 Fast Ethernet RJ-45 modular uplink switching module |
|
1000BASE-SX small form-factor pluggable module with DOM support |
|
1000BASE-LX/LH small form-factor pluggable module with DOM support |
|
1000BASE-ZX small form-factor pluggable module with DOM support |
|
TwinGig Converter Module; converts a 10 Gigabit Ethernet X2 interface into two Gigabit Ethernet Small Form-Factor Pluggable (SFP) ports. |
|
CWDM small form-factor pluggable module (See Table 2 for a list of supported wavelengths.) |
|
Dense Wavelength-Division Multiplexing (DWDM) Small Form Factor Pluggable (SFP) module |
|
10GBASE-LR X2 transceiver module for SMF, 1310-nm wavelength, SC duplex connector |
|
10GBASE-ER X2 transceiver module for SMF, 1550-nm wavelength, SC duplex connector |
|
10GBASE-CX4 X2 transceiver module for CX4 cable, copper, Infiniband 4X connector |
|
10GBASE-LX4 X2 transceiver module for MMF, 1310-nm wavelength, SC duplex connector |
|
10GBASE-LRM X2 transceiver module for MMF, 1310-nm wavelength, SC duplex connector |
|
10GBASE-SR X2 transceiver module for MMF, 850-nm wavelength, SC duplex connector |
|
10GBASE-T X2 transceiver module, up to 100m wavelength on CAT6A or CAT7 copper cables |
|
10GBASE-ZR X2 transceiver module for SMF, 1550 nm wavelength up to 80 km. DOM is not supported. |
|
10GBASE-ZR X2 transceiver module for SMF, 32 nontunable ITU 100-GHz wavelengths up to 80 km are supported. DOM is supported. Dual SC/PC connectors are supported. |
|
Hot-swappable input/output (I/O) converter module that fits into a 10-Gigabit Ethernet X2 slot on a switch or line card module. Hosts one 10-Gigabit Ethernet SFP+ transceiver module. |
|
10GBASE Dense Wavelength-Division Multiplexing (DWDM) SFP+ Module |
|
10GBASE Dense Wavelength-Division Multiplexing (DWDM) SFP+ Module |
|
CWDM gigabit interface converter (See Table 2 for a list of supported wavelengths.) |
|
Dense Wavelength-Division Multiplexing ITU 100-Ghz grid 15xx.yy nm GBIC. |
|
Catalyst 4500 series switch 1000 Watt AC power supply for chassis 4503, 4506, and 4507R (data only) |
|
Catalyst 4500 series switch 1400 Watt DC triple input power supply (data-only) |
|
Catalyst 4500 series switch 1400 Watt DC power supply with integrated PEM |
|
Catalyst 4500 series switch 1400 Watt AC power supply (data-only) |
|
Catalyst 4500 series switch 1300 Watt AC power supply with integrated voice for chassis 4503, 4506, and 4507R |
|
Catalyst 4500 series switch 2800 Watt AC power supply with integrated voice (data and PoE) for chassis 4503, 4506, and 4507R |
|
Catalyst 4500 series switch 4200 Watt AC dual input power supply with integrated voice (data and PoE) |
|
Catalyst 4500 series switch auxiliary power shelf (25-slot), including one PWR-4502 |
|
Catalyst 4500 series switch auxiliary power shelf redundant power supply |
|
Table 2 briefly describes the supported CWDM wavelengths in the Catalyst 4500E Series Switch.
Table 3 briefly describes the supported DWDM wavelengths in the Catalyst 4500E Series Switch.
For details on transceiver module compatibility information, please refer to the URL:
http://www.cisco.com/en/US/products/hw/modules/ps5455/products_device_support_tables_list.html
Supported E Series Hardware on Cisco IOS XE Release 3.6.0E
A brief list of primary E-Series hardware supported by Cisco IOS XE Release 3.6.0E is shown in Table 4 .
Feature Support by Image Type
Table 5 is a detailed list of features supported on Catalyst 4500E Supervisor Engine 7-E, Supervisor Engine 7L-E, and Supervisor Engine 8-E running Cisco IOS XE Software Release 3.6.0E categorized by image type. Please visit Feature Navigator for package details:
http://tools.cisco.com/ITDIT/CFN/
BGP Increased Support of Numbered as-path Access Lists to 500 |
|||
CFM/IEEE 802.1ag - D8.1 standard Compliant CFM, Y.1731 multicast LBM / AIS / RDI / LCK, IP SLA for Ethernet |
|||
Class Based Ethernet CoS Matching & Marking (802.1p & ISL CoS) |
|||
Easy VSS1 |
|||
IEEE 802.1s Multiple Spanning Tree (MST) Standard Compliance |
|||
IEEE 802.1t2 |
|||
IEEE 802.3ad Link Aggregation (LACP) Port-Channel Standalone Disable |
|||
IGMP Version 3 - Explicit Tracking of Hosts, Groups, and Channels |
|||
IP Multicast Load Splitting - Equal Cost Multipath (ECMP) using S, G and Next-hop |
|||
IPv6 First Hop Security (FHS): IPv6 Snooping (Data Gleaning, per-limit Address Limit) |
|||
IPv6 First Hop Security (FHS) Phase 2: Lightweight DHCPv6 Relay Agent (LDRA) Neighbor Discovery (ND) Multicast Suppress Source and Prefix Guard3 |
|||
IPv6 Multicast: Multicast Listener Discovery (MLD) Protocol, Versions 1 and 2 |
|||
IPv6 Multicast: RPF Flooding of Bootstrap Router (BSR) Packets |
|||
Yes 5 |
|||
Yes 5 |
|||
IPv6 Policy-Based Routing4 |
|||
Yes5 |
|||
IPv6 Services: Cisco Discovery Protocol (CDP) - IPv6 Address Family Support for Neighbor Information |
|||
IPv6 Switching: CEFv6 Switched Automatic IPv4-compatible Tunnels (in software) |
|||
IPv6 Tunneling: Automatic IPv4-compatible Tunnels (in software) |
|||
IPv6 Tunneling: Manually Configured IPv6 over IPv4 Tunnels (in software) |
|||
Medianet: Integrated Video Traffic Simulator (hardware-assisted IP SLA); IPSLA generator and responder |
|||
Medianet: Media Monitoring (Performance Monitoring and Mediatrace) |
|||
NEAT Enhancement: Re-Enabling BPDU Guard Based on User Configuration |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
OSPF for Routed Access6 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
Yes 5 |
|||
RADIUS Attribute 44 (Accounting Session ID) in Access Requests |
|||
Smart Install Director—Configuration-only Deployment and Smooth Upgrade |
|||
Source Specific Multicast (SSM) - IGMPv3,IGMP v3lite, and URD |
|||
Time Domain Reflectometry (TDR)7 |
|||
TrustSec: IEEE 802.1ae MACSec encryption on user facing ports |
|||
TrustSec: IEEE 802.1ae MACSec encryption on user facing ports SSO |
|||
TrustSec: IEEE 802.1ae MACSec encryption between switch-to-switch links using Cisco SAP (Security Association Protocol) |
|||
MIB Support
For information on MIB support, please refer to this URL:
ftp://ftp.cisco.com/pub/mibs/supportlists/cat4000/cat4000-supportlist.html
Features Not Supported on the Cisco Catalyst 4500E Series Switch
The following features are not supported on a Catalyst 4500E Series Switch with Supervisor Engine 7-E and Supervisor Engine 7L-E:
New and Changed Information
These sections describe the new and changed information for the Catalyst 4500 series switch running Cisco IOS XE software:
- New Software Features in Release IOS XE 3.6.10E
- New Software Features in Release IOS XE 3.6.8E
- New Software Features in Release IOS XE 3.6.7E
- New Software Features in Release IOS XE 3.6.6E
- New Hardware Features in Release IOS XE 3.6.2E
- New Software Features in Release IOS XE 3.6.2E
- New Software Features in Release IOS XE 3.6.1E
- New Hardware Features in Release IOS XE 3.6.0E
- New Software Features in Release IOS XE 3.6.0E
New Software Features in Release IOS XE 3.6.3E
New Hardware Features in Release IOS XE 3.6.2E
Support for USB ports on Supervisor Engine 8-E, with hardware revision 1.1 or higher.
New Software Features in Release IOS XE 3.6.2E
USB Support on Supervisor Engine8-E - Software support for USB ports on Supervisor Engine 8-E.
New Software Features in Release IOS XE 3.6.1E
The following table list the new features for Release IOS XE 3.6.1E.
New Hardware Features in Release IOS XE 3.6.0E
New Software Features in Release IOS XE 3.6.0E
The following table list the new features for Release IOS XE 3.6.0E.
Use this URL for the Cisco IOS Release 15E Documentation Roadmap |
Provides quick and easy access to all relevant documentation for specific platforms. Look for Quick Links to Platform Documentation on the respective platform documentation pages. |
Determines the level of network access provided to an endpoint based on the type of the endpoint device. This feature also permits hardbinding between the end device and the interface. Autoconfig falls under the umbrella of Smart Operations solution. |
|
Provides a single line CLI, to enable base line security features (Port Security, DHCP snooping, DAI). |
|
Banner Page and Inactivity timeout for HTTP/S connections—Allows you to create a banner page and set an inactivity timeout for HTTP or HTTP Secure (HTTPS) connections. The banner page allows you to logon to the server when the session is invalid or expired. |
|
Enhances the functionality of Cisco TrustSec with SXP version 4 by adding support for Security Group Tag (SGT) Exchange Protocol (SXP) bindings that can be propagated in both directions between a speaker and a listener over a single connection. |
|
This is a read--only DHCP functionality that allows components to register and glean DHCP packets. |
|
Enables you to configure VSS with a single command on the active switch and no action on the VSS standby switch. With IOS XE 3.6.0E, Easy VSS is supported only on IP Base (Sup7E and Sup8E) and Enterprise Services (Sup7LEand Sup8E). |
|
Involves the definition of a Layer 2 bridging architecture that supports Ethernet services. The switch supports a lite version of the EVC feature on Supervisor Engine 7L-E. |
|
The NMSP Strong Cipher enhancement enables strong ciphers for new NMSP connections. The existing NMSP connections will use the default cipher |
|
Helps to resolve the destination domain name to an IP address, which is provided to the client as a part of the domain name system (DNS) response. |
|
Protects data traffic from a failed router or circuit while allowing packet load sharing between a group of redundant routers. |
|
Allows users to configure multiple non-link local addresses as virtual addresses. The Hot Standby Router Protocol (HSRP) ensures host-to-router resilience and failover, in case the path between a host and the first-hop router fails, or the first-hop router itself fails. |
|
Allows the device-sensor to extract the HTTP packet Type-Length-Value (TLV) to derive useful information about the end device type. |
|
Provides a mechanism to configure multiple commands at the same time and associate it with a target such as an interface. An interface template is a container of configurations or policies that can be applied to specific ports |
|
Allows you to manually configure how the received packets should be routed. PBR allows you to identify packets by using several attributes and to specify the next hop or the output interface to which the packet should be sent. Note With IOS XE Release 3.6.0E and IOS 15.2(2)E, IPv6 PBR is not supported on Supervisor Engine 8-E. |
|
Allows an IPv6 Static Route to be associated with a tracked-object. |
|
Introduces dynamic learning of IP-SGT mappings for IPv6 addresses. |
|
In-Service Software Upgrade8 |
Allows Cisco software to be upgraded or downgraded, at a router level. |
Provides the capability to diagnose Media Stream on top of various instrumentations in Cisco routers/switches and endpoints. Also addresses the MediaNet Video monitoring requirement to discover the signaling path and provides end-to-end diagnostics along the media stream routes. |
|
Expands the Enhanced Object Tracking (EOT) functionality to allow the tracking of IP version 6 (IPv6) routes. |
|
Switch based agent support for zero touch automated device installation solution called NG-PNP. |
|
Provides a mechanism to authenticate Open Shortest Path First version 3 (OSPFv3) protocol packets as an alternative to existing OSPFv3 IPsec authentication. |
|
Enhances route maps to enable configuration of a recursive next-hop IP address that is used by policy-based routing (PBR). |
|
Allows users to select the type, length, value (TLV) fields that are sent on a particular interface to filter information sent through Cisco Discovery Protocol packets. |
|
Controls and manages the Cisco TrustSec access control on a network device based on an attribute-based access control list. When a security group access control list (SGACL) is enabled globally, the SGACL is enabled on all interfaces in the network by default; use Security Group ACL at Interface Level feature to disable the SGACL on a Layer 3 interface. |
|
Enables a Catalyst 4k standalone switch acting as Smart Install Client. |
|
Ensures that the Network Device Admission Control (NDAC)-authenticated 802.1X links between Cisco TrustSec devices are in open state even when the Authentication, Authorization, and Accounting (AAA) server is not reachable. |
|
Allows you to track the behavior of an object and receive notifications of changes. This feature explains how object tracking, in particular the tracking of IPv6 objects, is integrated into VRRP version 3 (VRRPv3) and describes how to track an IPv6 object using a VRRPv3 group. |
|
Enables a group of routers to form a single virtual router to provide redundancy. This feature also provides the capability to support IPv4 and IPv6 addresses. |
|
IOS XE 3.6.0E and Enterprise Services enables VSS support on Supervisor Engine 8-E with complete feature parity with Supervisor Engine 7-E. |
|
Enables networks to redirect guest users to the URL they had originally requested. This feature is enabled by default and requires no configuration. |
New and Modified IOS Software Features Supported in Cisco IOS XE 3.5.0E
The following new and modified software features function as a unified agent and adds functionality to enhance the current solutions.
IPv6 Static Routing: Support for Tracking Objects—Allows an IPv6 Static Route to be associated with a tracked-object.
Object Tracking: IPv6 Route Tracking—Expands the Enhanced Object Tracking (EOT) functionality to allow the tracking of IP version 6 (IPv6) routes.
http://www.cisco.com/en/US/docs/ios-xml/ios/san/configuration/15-e/san-macsec.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dhcp/configuration/15-e/dhcp-gleaning.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dhcp/configuration/xe-3e/dhcp-xe-3e-book.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dns/configuration/15-e/dns-15-e-book.html
802.1X support for trunk ports
http://www.cisco.com/en/US/docs/ios-xml/ios/sec_usr_8021x/configuration/15-e/config-ieee-802x-pba.html
http://www.cisco.com/en/US/docs/ios-xml/ios/sec_usr_8021x/configuration/xe-3e/sec-usr-8021x-xe-3e-book.html
Commented IP Access List Entries
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-acl-comm-ipacl.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/xe-3e/sec-acl-comm-ipacl.html
IPv6 ACL Extensions for Hop by Hop Filtering
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/ip6-acl-ext-hbh.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-acl-seq-num.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/xe-3e/sec-acl-seq-num.html
ACL Support for Filtering IP Options
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-acl-support-filter-ip-option.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/xe-3e/sec-acl-support-filter-ip-option.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-create-filter-tcp.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/xe-3e/sec-create-filter-tcp.html
ACL - Named ACL Support for Noncontiguous Ports on an Access Control Entry
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-named-acl-support-for-noncontiguous-ports.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/xe-3e/sec-named-acl-support-for-noncontiguous-ports.html
IP Access List Entry Sequence Numbering
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-acl-seq-num.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/xe-3e/sec-acl-seq-num.html
IOS ACL Support for filtering IP Options
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-acl-support-filter-ip-option.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-acl-syslog.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/sec-acl-named.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/xe-3e/sec-acl-named.html
http://cisco.com/en/US/docs/ios-xml/ios/sec_data_acl/configuration/15-e/ip6-pacl-supp.html
http://www.cisco.com/en/US/docs/ios-xml/ios/bsdcm/configuration/15-e/bsdcm-15-e-book.html
http://www.cisco.com/en/US/docs/ios-xml/ios/snmp/configuration/15-e/snmp-15-e-book.html
http://www.cisco.com/en/US/docs/ios-xml/ios/snmp/configuration/xe-3e/snmp-xe-3e-book.html
http://www.cisco.com/en/US/docs/ios-xml/ios/cns/configuration/15-e/cns-15-e-book.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipmulti_pim/configuration/15-e/ip6-mcast-pim-pass.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipmulti_pim/configuration/15-e/imc_hsrp_aware.html
OSPFv3 ABR Type 3 LSA Filtering
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-abr-type-3.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-ospfv3-dc-ignore.html
Graceful Shutdown Support for OSPFv3
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-ospfv3-gshutdown.html
OSPF Support for BFD over IPv4
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_bfd/configuration/15-e/irbfd-bfd-ospf-ipv4-supp.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_bfd/configuration/15-e/irbfd-vrf-supp.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_bfd/configuration/15-e/irbfd-bfd-static-route-supp.html
Static Route Support for BFD over IPv6
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_bfd/configuration/15-e/ip6-bfd-static.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_bfd/configuration/15-e/irbfd-bfd-eigrp-supp.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_bfd/configuration/15-e/ip6-route-bfd-ospfv3.html
http://www.cisco.com/en/US/docs/ios-xml/ios/sec_usr_tacacs/configuration/15-e/sec-usr-tacacs-15-e-book.html
http://www.cisco.com/en/US/docs/ios-xml/ios/sec_usr_ssh/configuration/15-e/sec-secure-shell-v2.html
Client Information Signalling Protocol (CISP)
http://www.cisco.com/en/US/docs/ios-xml/ios/sec_usr_8021x/configuration/15-e/sec-ieee-neat.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-ospfv3-mib.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-nsr-ospf.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/ip6-route-ospfv3-max-lsa.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-vrf-lite-pe-ce.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipapp_fhrp/configuration/15-e/fhp-15-e-book_chapter_0100.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipv6_fhsec/configuration/15-e/ip6f-15-e-book_chapter_0110.html
IPv6 Router Advertisement Throttler
http://www.cisco.com/en/US/docs/ios-xml/ios/ipv6_fhsec/configuration/15-e/ip6f-15-e-book_chapter_0111.html
IPv6 Neighbor Discovery Multicast Suppress
http://www.cisco.com/en/US/docs/ios-xml/ios/ipv6_fhsec/configuration/15-e/ip6-nd-mcast-supp.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipv6_fhsec/configuration/15-e/ipv6-dest-guard.html
DHCPv6 Relay - Lightweight DHCPv6 Relay Agent
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dhcp/configuration/15-e/dhcp-ldra.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dns/configuration/15-e/dns-15-e-book_chapter_01.html
DHCPv6 - Relay chaining for Prefix Delegation
http://www.cisco.com/en/US/docs/ios-xml/ios/ipaddr_dhcp/configuration/15-e/dhcp-15e-book_chapter_010.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/command/ospf-i1.html
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-ospfv3-nssa-cfg.html
OSPF support for NSSA RFC 3101
http://www.cisco.com/en/US/docs/ios-xml/ios/iproute_ospf/configuration/15-e/iro-ospfv2-nssa-cfg.html
http://www.cisco.com/en/US/docs/ios-xml/ios/ipv6_nman/configuration/15-e/ip6-tftp-supp.html
http://www.cisco.com/en/US/docs/ios-xml/ios/saf/configuration/15-e/saf-capman.html
Extensible Messaging Client Protocol (XMCP) 2.0
http://www.cisco.com/en/US/docs/ios-xml/ios/saf/configuration/15-e/saf-xmcp.html
Cisco IOS XE to Cisco IOS Version Number Mapping
As Table 7 shows, each version of Cisco IOS XE has an associated Cisco IOS version:
Upgrading the System Software
- Before upgrading to Cisco IOS XE Release 3.6.6E, you need to upgrade the Prime Infrastructure software to Release 3.1.4 with Device Pack(DP) 6.
For details on how to upgrade ROMMON, refer to: http://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst4500/release/note/OL_30306-01.html
- If you are upgrading to Cisco IOS XE 3.6.0E and using Supervisor Engine 7-E or 7L-E, you must use ROMMON version 15.0(1r)SG10 or a higher version (if available).

Note![]() If dual supervisor engines are present, first upgrade your software to Cisco IOS XE 3.2.0SG or higher, then upgrade your ROMMON to IOS Version 15.0(1r)SG7 to avoid an uplinks issue (CSCtj54375).
If dual supervisor engines are present, first upgrade your software to Cisco IOS XE 3.2.0SG or higher, then upgrade your ROMMON to IOS Version 15.0(1r)SG7 to avoid an uplinks issue (CSCtj54375).

Note![]() When you upgrade to Cisco IOS XE Release 3.6.5E, SSH access is lost, because it cannot use the CISCO_IDEVID_SUDI_LEGACY RSA server key. Before upgrade, generate the server key using the crypto key generate rsa command in global configuration mode. To verify whether the RSA server key is available on your device, run the show crypto key command.
When you upgrade to Cisco IOS XE Release 3.6.5E, SSH access is lost, because it cannot use the CISCO_IDEVID_SUDI_LEGACY RSA server key. Before upgrade, generate the server key using the crypto key generate rsa command in global configuration mode. To verify whether the RSA server key is available on your device, run the show crypto key command.
- If you are upgrading to Cisco IOS XE Version 3.5.0E and plan to use VSS, you must upgrade your ROMMON to version 15.0(1r)SG10. Otherwise, you must upgrade your ROMMON to at least IOS Version 15.0(1r)SG2.
Manual Field Programmable Gate Array Upgrades
If you have installed WS-X4748-UPOE in the chassis, note the following:
With Cisco IOS XE Release 3.6.xE, after an ISSU upgrade, you may have to manually upgrade the Field Programmable Gate Array (FPGA) for WS-X4748-UPOE+E line cards that have version ID (VID) 03 or later versions. (To check the VID, enter the show inventory command in privileged EXEC mode).
The required FPGA upgrades are not triggered automatically after an ISSU upgrade. This may result in an unexpected FPGA upgrade of all applicable linecards if a linecard is inserted online (OIR), after ISSU upgrade. The solution to this problem is to manually perform an FPGA upgrade during a maintenance window.
Follow these steps for all WS-X4748-UPOE+E linecards in the chassis:
Upgrading ROMMON Image for Supervisor Engine 8-E
For IOS XE Release 3.6.0E, the ROMMON image must be upgraded to use the 3.6.0XE image (15.1(1r)SG4). The IOS XE Bundle format for Supervisor Engine 8-E has changed, necessitating a new ROMMON image.
The following [error] messages might be observed if IOS XE 3.6.0XE images are booted with older ROMMON images:
Identifying an +E Chassis and ROMMON
When supervisor engine 1 (sup1) is in ROMMON and supervisor engine 2 (sup2) is in IOS, only sup2 can read the idprom contents of chassis’ idprom. Chassis type is displayed as “+E” in the output of the show version command. Conversely, sup1 can only display the chassis type as “E.”
When both sup1 and sup2 are in ROMMON, both engines can read the chassis’ idprom. Chassis type is displayed correctly as “+E” in the output of the show version command.
When both sup1 and sup2 are in IOS, both engines can read the chassis’ idprom. Chassis type is displayed correctly as “+E” in the output of the show version command.
Limitations and Restrictions
- If WLAN applied client policy is invalid, the client is excluded with the exclusion reason being 'Client QoS Policy failure'.
- The show exception files all command lists only crashinfo files from the active supervisor engine. You must issue the dir slavecrashinfo: and dir slvecrashinfo-dc: commands to obtain lists of crashinfo files from the standby supervisor engine.
- Performing an ISSU from a prior release to IOS XE 3.6.0E is unsupported.
- We recommend that you configure the access-session interface-template sticky timer timer-value command at the global or interface configuration mode, and not within the template.
- The WS-X4712-SFP+E module is not supported in the WS-C4507R-E or WS-C4510R-E chassis and does not boot. This module is supported in the WS-C4503-E, WS-C4506-E, WS-C4507R+E, and WS-C4510R+E chassis.
- More than 16K QoS policies can be configured in software. Only the first 16K are installed in hardware.
- Adjacency learning (through ARP response frames) is restricted to roughly 1000 new adjacencies per second, depending on CPU utilization. This should only impact large networks on the first bootup. After adjacencies are learned they are installed in hardware.
- Multicast fastdrop entries are not created when RPF failure occurs with IPv6 multicast traffic. In a topology where reverse path check failure occurs with IPv6 multicast, this may cause high CPU utilization on the switch.
- The SNMP ceImageFeature object returns a similar feature list for all the three license levels (LAN Base, IP Base, and EntServices). Although the activated feature set for a universal image varies based on the installed feature license, the value displayed by this object is fixed and is not based on the feature license level.
- Standard TFTP implementation limits the maximum size of a file that can be transferred to 32 MB. If ROMMON is used to boot an IOS image that is larger than 32 MB, the TFTP transfer fails at the 65,xxx datagram.
TFTP numbers its datagrams with a 16 bit field, resulting in a maximum of 65,536 datagrams. Because each TFTP datagram is 512 bytes long, the maximum transferable file is 65536 x 512 = 32 MB. If both the TFTP client (ROMMON) and the TFTP server support block number wraparound, no size limitation exists.
Cisco has modified the TFTP client to support block number wraparound. So, if you encounter a transfer failure, use a TFTP server that supports TFTP block number wraparound. Because most implementations of TFTP support block number wraparound, updating the TFTP daemon should fix the issue.
The outputs of certain commands, such as show ip route and show access-lists, contain non-deterministic text. While the output is easily understood, the output text does not contain strings that are consistently output. A general purpose specification file entry is unable to parse all possible output.
While a general purpose specification file entry may not be possible, a specification file entry might be created that returns the desired text by searching for text that is guaranteed to be in the output. If a string is guaranteed to be in the output, it can be used for parsing.
For example, the output of the show ip access-lists SecWiz_Gi3_17_out_ip command is this:
The first line is easily parsed because access list is guaranteed to be in the output:
The remaining lines all contain the term host. As a result, the specification file may report the desired values by specifying that string. For example, this line
will produce the following for the first and second rules
and the following for the third statement
Request the output of the show running-config command using NETCONF and parse that output for the desired strings. This is useful when the desired lines contain nothing in common. For example, the rules in this access list do not contain a common string and the order (three permits, then a deny, then another permit), prevent the spec file entry from using permit as a search string, as in the following example:
The XML output of show running-config command includes the following, which can then be parsed programmatically, as desired:
- When attaching a existing policy-map (that is already applied to a control-port) to another front-panel port, the following message displays:
Workaround: Define a policy-map with a different name and then reattach. CSCti26172
- If the number of unique FNF monitors attached to target exceeds 2048 (one per target), a switch responds slowly:
–![]() Decrease the number of monitors.
Decrease the number of monitors.
–![]() Attach the same monitor to multiple targets. CSCti43798
Attach the same monitor to multiple targets. CSCti43798
- ciscoFlashPartitionFileCount object returns an incorrect file count for bootflash:, usb0:, slot0:, slaveslot0:, slavebootflash:, and slaveusb0:.
Workaround: Use the dir device command (for example, dir bootflash:) to obtain the correct file count. CSCti74130
- If multicast is configured and you make changes to the configuration, Traceback and CPUHOG messages are displayed if the following conditions exist:
–![]() At least 10K groups and roughly 20K mroutes exist.
At least 10K groups and roughly 20K mroutes exist.
–![]() IGMP joins with source traffic transit to all the multicast groups.
IGMP joins with source traffic transit to all the multicast groups.
This is caused by the large number of updates generating SPI messages that must be processed by the CPU to ensure that the platform is updated with the changes in all the entries.
- With traffic running, entering clear ip mroute * with larger number of mroutes and over 6 OIFs will cause Malloc Fail messages to display.
You cannot clear a large number of mroutes at one time when traffic is still running.
Workaround: Do not clear all mroutes at once.
- Although you can configure subsecond PIM query intervals on Catalyst 4500 platforms, such an action represents a compromise between convergence (reaction time) and a number of other factors (number of mroutes, base line of CPU utilization, CPU speed, processing overhead per 1 m-route, etc.). You must account for those factors when configuring subsecond PIM timers. We recommend that you set the PIM query interval to a minimum of 2 seconds. By adjusting the available parameters, you can achieve flawless operation; that is, a top number of multicast routes per given convergence time on a specific setup.
- Energywise WOL is not “waking up” a PC in hibernate or standby mode.
Workaround: Use the show version command. CSCtr30294
Workaround: Select an alternate destination or source port. CSCty05405
–![]() 10/100/1000BaseT Premium POE E Series WS-X4648-RJ45V+E (JAE1348OY52)
10/100/1000BaseT Premium POE E Series WS-X4648-RJ45V+E (JAE1348OY52)
–![]() 4 Sup 7-E 10GE (SFP+), 1000BaseX (SFP) WS-X45-SUP7-E (CAT1434L0G4)
4 Sup 7-E 10GE (SFP+), 1000BaseX (SFP) WS-X45-SUP7-E (CAT1434L0G4)
the following restrictions apply:
–![]() Sub-interfaces are not supported on 1 Gigabit and Ten-Gigabit interfaces.
Sub-interfaces are not supported on 1 Gigabit and Ten-Gigabit interfaces.
–![]() Port-channel members do not support multiple classification criteria for a QoS policy.
Port-channel members do not support multiple classification criteria for a QoS policy.
–![]() CEF is disabled automatically when uRFP is enabled and TCAM is fully utilized.
CEF is disabled automatically when uRFP is enabled and TCAM is fully utilized.
- When either the RADIUS-server test feature is enabled or RADIUS-server dead-criteria is configured, and either RADIUS-server deadtime is set to 0 or not configured, the RADIUS-server status is not properly relayed to AAA.
Workaround: Configure both dead-criteria and deadtime.
–![]() Links flap for various Layer 3 protocols.
Links flap for various Layer 3 protocols.
–![]() A traffic loss of several seconds is observed during the upgrade process.
A traffic loss of several seconds is observed during the upgrade process.
Workaround: Do not use the quick option with the issu changeversion command. CSCto51562
- While configuring an IPv6 access-list, if you specify hardware statistics as the first statement in v6 access-list mode (i.e. before issuing any other v6 ACE statement), it will not take effect. Similarly, your hardware statistics configuration will be missing from the output of the show running command.
You will not experience this behavior with IPv4 access lists.
Workaround: During IPv6 access-list configuration, configure at least one IPv6 ACE before the "hardware statistics" statement. CSCuc53234
- Routed packets that are fragmented are not policed if the egress interface is on the VSS Standby switch. However, if the egress interface is on the VSS Active switch, these packets are policed.
This applies to QoS policing only. QoS marking, shaping and sharing behave as expected.
- When an IPv6 FHS policy is applied on a VLAN and an EtherChannel port is part of that VLAN, packets received by EtherChannel (from neighbors) are not bridged across the local switch.
Workaround: Apply FHS policies on a non EtherChannel port rather than a VLAN. CSCua53148
- During VSS conversion, the switch intended as the Standby device may require up to 9 minutes to reach an SSO state. The boot up time depends on the configuration and on the number of line cards in the system.
- Dual connectors (like, an SFP+ transceiver inserted into a CVR-X2-SFP10G module) on the WS-X4606-X2-E line card are not supported as a VSL.
Workaround: Use any X2-pluggable module on its own in the WS-X4606-X2-E line card. CSCuc70321
Workaround: Observe the show module command output. CSCua79513
- Beginning with IOS Release XE 3.5.0E, error messages that occur when a QoS policy is applied will no longer appear directly on the console when no logging console is configured. They will appear only when a logging method is active (e.g., logging buffered, logging console, …).
Workaround: None. QoS groups are not supported in VSS. CSCuc84739
- Auto negotiation cannot be disabled on the Fa1 port. It must be set to auto/auto, or fixed speed with duplex auto.
- The following messages are seen during boot up after POST check.
These messages are cosmetic only, and no ssh services are available unless configured within IOS.
- When a logging discriminator is configured and applied to a device, memory leak is seen under heavy syslog or debug output. The rate of the leak is dependent on the quantity of logs produced. In extreme cases, the device may crash. As a workaround, disable the logging discriminator on the device (CSCur45606, CSCur28336).
Caveats
Caveats describe unexpected behavior in Cisco IOS releases. Caveats listed as open in a prior release are carried forward to the next release as either open or resolved.

Note![]() For the latest information on PSIRTS, refer to the Security Advisories on CCO at the following URL:
For the latest information on PSIRTS, refer to the Security Advisories on CCO at the following URL:
http://www.cisco.com/en/US/products/products_security_advisories_listing.html
Cisco Bug Search Tool
The Bug Search Tool (BST), which is the online successor to Bug Toolkit, is designed to improve the effectiveness in network risk management and device troubleshooting. The BST allows partners and customers to search for software bugs based on product, release, and keyword, and aggregates key data such as bug details, product, and version. The tool has a provision to filter bugs based on credentials to provide external and internal bug views for the search input.
To view the details of a caveat listed in this document:
1.![]() Access the BST (use your Cisco user ID and password) at https://tools.cisco.com/bugsearch/.
Access the BST (use your Cisco user ID and password) at https://tools.cisco.com/bugsearch/.
2.![]() Enter the bug ID in the Search For: field.
Enter the bug ID in the Search For: field.
- Open Caveats
- Resolved Caveats for Cisco IOS XE Release 3.6.10E
- Resolved Caveats for Cisco IOS XE Release 3.6.9E
- Resolved Caveats for Cisco IOS XE Release 3.6.8E
- Resolved Caveats for Cisco IOS XE Release 3.6.7E
- Resolved Caveats for Cisco IOS XE Release 3.6.6E
- Resolved Caveats for Cisco IOS XE Release 3.6.5E
- Resolved Caveats for Cisco IOS XE Release 3.6.4E
- Resolved Caveats for Cisco IOS XE Release 3.6.3E
- Resolved Caveats for Cisco IOS XE Release 3.6.2E
- Resolved Caveats for Cisco IOS XE Release 3.6.1E
- Resolved Caveats for Cisco IOS XE Release 3.6.0E
Open Caveats
Resolved Caveats for Cisco IOS XE Release 3.6.10E
Resolved Caveats for Cisco IOS XE Release 3.6.9E
Resolved Caveats for Cisco IOS XE Release 3.6.8E
Resolved Caveats for Cisco IOS XE Release 3.6.7E
Resolved Caveats for Cisco IOS XE Release 3.6.6E
Resolved Caveats for Cisco IOS XE Release 3.6.5Ea
Resolved Caveats for Cisco IOS XE Release 3.6.5E
Resolved Caveats for Cisco IOS XE Release 3.6.4E
Resolved Caveats for Cisco IOS XE Release 3.6.3E
Resolved Caveats for Cisco IOS XE Release 3.6.2E
Resolved Caveats for Cisco IOS XE Release 3.6.1E
Related Documentation
Refer to the following documents for additional Catalyst 4500 series information:
http://www.cisco.com//en/US/products/hw/switches/ps4324/index.html
Hardware Documents
Installation guides and notes including specifications and relevant safety information are available at the following URLs:
http://www.cisco.com/en/US/docs/switches/lan/catalyst4500/hardware/catalyst4500e/installation/guide/Eseries.html
- For information about individual switching modules and supervisors, refer to the Catalyst 4500 Series Module Installation Guide at:
http://www.cisco.com/en/US/docs/switches/lan/catalyst4500/hardware/configuration/notes/OL_25315.html
http://www.cisco.com/en/US/docs/switches/lan/catalyst4500/hardware/regulatory/compliance/78_13233.html
http://www.cisco.com/en/US/products/hw/switches/ps4324/prod_installation_guides_list.html
Software Documentation
Software release notes, configuration guides, command references, and system message guides are available at the following URLs:
http://www.cisco.com/en/US/products/hw/switches/ps4324/prod_release_notes_list.html
Software documents for the Catalyst 4500 Classic, Catalyst 4500 E-Series, Catalyst 4900 Series, and Catalyst 4500-X Series switches are available at the following URLs:
http://www.cisco.com/en/US/products/hw/switches/ps4324/products_installation_and_configuration_guides_list.html
http://www.cisco.com/en/US/products/hw/switches/ps4324/prod_command_reference_list.html
http://www.cisco.com/en/US/products/hw/switches/ps4324/products_system_message_guides_list.html
Cisco IOS Documentation
Platform- independent Cisco IOS documentation may also apply to the Catalyst 4500 and 4900 switches. These documents are available at the following URLs:
http://www.cisco.com/en/US/products/ps6350/products_installation_and_configuration_guides_list.html
http://www.cisco.com/en/US/products/ps6350/prod_command_reference_list.html
You can also use the Command Lookup Tool at:
http://tools.cisco.com/Support/CLILookup/cltSearchAction.do
http://www.cisco.com/en/US/products/ps6350/products_system_message_guides_list.html
You can also use the Error Message Decoder tool at:
http://www.cisco.com/pcgi-bin/Support/Errordecoder/index.cgi
Notices
The following notices pertain to this software license.
OpenSSL/Open SSL Project
This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/).
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com).
This product includes software written by Tim Hudson (tjh@cryptsoft.com).
License Issues
The OpenSSL toolkit stays under a dual license, i.e. both the conditions of the OpenSSL License and the original SSLeay license apply to the toolkit. See below for the actual license texts. Actually both licenses are BSD-style Open Source licenses. In case of any license issues related to OpenSSL please contact openssl-core@openssl.org.
Copyright © 1998-2007 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1.![]() Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
2.![]() Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materials provided with the distribution.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materials provided with the distribution.
3.![]() All advertising materials mentioning features or use of this software must display the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/)”.
All advertising materials mentioning features or use of this software must display the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/)”.
4.![]() The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact openssl-core@openssl.org.
The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact openssl-core@openssl.org.
5.![]() Products derived from this software may not be called “OpenSSL” nor may “OpenSSL” appear in their names without prior written permission of the OpenSSL Project.
Products derived from this software may not be called “OpenSSL” nor may “OpenSSL” appear in their names without prior written permission of the OpenSSL Project.
6.![]() Redistributions of any form whatsoever must retain the following acknowledgment:
Redistributions of any form whatsoever must retain the following acknowledgment:
“This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit ( http://www.openssl.org/)”.
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS”' AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com). This product includes software written by Tim Hudson (tjh@cryptsoft.com).
Copyright © 1995-1998 Eric Young (eay@cryptsoft.com). All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are adhered to. The following conditions apply to all code found in this distribution, be it the RC4, RSA, lhash, DES, etc., code; not just the SSL code. The SSL documentation included with this distribution is covered by the same copyright terms except that the holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young’s, and as such any Copyright notices in the code are not to be removed. If this package is used in a product, Eric Young should be given attribution as the author of the parts of the library used. This can be in the form of a textual message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1.![]() Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
2.![]() Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
3.![]() All advertising materials mentioning features or use of this software must display the following acknowledgement:
All advertising materials mentioning features or use of this software must display the following acknowledgement:
“This product includes cryptographic software written by Eric Young (eay@cryptsoft.com)”.
The word ‘cryptographic’ can be left out if the routines from the library being used are not cryptography-related.
4.![]() If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: “This product includes software written by Tim Hudson (tjh@cryptsoft.com)”.
If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: “This product includes software written by Tim Hudson (tjh@cryptsoft.com)”.
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The license and distribution terms for any publicly available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and put under another distribution license [including the GNU Public License].
“Notices” section.
CCVP, the Cisco logo, and Welcome to the Human Network are trademarks of Cisco Systems, Inc.; Changing the Way We Work, Live, Play, and Learn is a service mark of Cisco Systems, Inc.; and Access Registrar, Aironet, Catalyst, CCDA, CCDP, CCIE, CCIP, CCNA, CCNP, CCSP, Cisco, the Cisco Certified Internetwork Expert logo, Cisco IOS, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Cisco Unity, Enterprise/Solver, EtherChannel, EtherFast, EtherSwitch, Fast Step, Follow Me Browsing, FormShare, GigaDrive, HomeLink, Internet Quotient, IOS, iPhone, IP/TV, iQ Expertise, the iQ logo, iQ Net Readiness Scorecard, iQuick Study, LightStream, Linksys, MeetingPlace, MGX, Networkers, Networking Academy, Network Registrar, PIX, ProConnect, ScriptShare, SMARTnet, StackWise, The Fastest Way to Increase Your Internet Quotient, and TransPath are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries.
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback