-
Cisco MDS 9020 Fabric Switch Configuration Guide and Command Reference, Release 2.x
-
Index
-
Preface
-
Product Overview
-
Before You Begin
-
Initial Configuration
-
Software Images
-
Managing System Hardware
-
Configuring Interfaces
-
Configuring and Managing Zones
-
Managing FLOGI and FDMI
-
Configuring Switch Security
-
Configuring SNMP
-
Configuring Fibre Channel Routing Services and Protocols
-
Configuring IP Services
-
Configuring Domain Parameters
-
Configuring System Message Logging
-
Advanced Features and Concepts
-
Monitoring System Processes and Logs
-
Cisco SAN-OS Features Supported in CiscoFabricWare
-
Command Reference
-
Table Of Contents
Configuring and Managing Zones
Active and Full Zone Set Considerations
Recovering from Link Isolation
Clearing the Zone Server Database
Renaming Zone Sets, Zones and, fcaliases
Configuring and Managing Zones
Zoning enables you to set up access control between storage devices or user groups. If you have administrator privileges in your fabric, you can create zones to increase network security and to prevent data loss or corruption. Zoning is enforced by examining the source-destination ID field.
This chapter includes the following sections:
•
Recovering from Link Isolation
•
Renaming Zone Sets, Zones and, fcaliases
Zoning Features
Zoning has the following features:
•
A zone consists of multiple zone members.
–
Members in a zone can access each other; members in different zones cannot access each other.
–
If zoning is not activated, all devices are members of the default zone.
–
If zoning is activated, any device that is not in an active zone (a zone that is part of an active zone set) is a member of the default zone.
–
Zones can vary in size.
–
Devices can belong to more than one zone.
•
A zone set consists of one or more zones.
–
A zone set can be activated or deactivated as a single entity across all switches in the fabric.
–
Only one zone set can be activated at any time.
–
A zone can be a member of more than one zone set.
•
Zoning can be administered from any switch in the fabric.
–
When you activate a zone set (from any switch), all switches in the fabric receive the active zone set. Additionally, full zone sets are distributed to all switches in the fabric if this feature is enabled in the source switch.
–
If a new switch is added to an existing fabric, zone sets are acquired by the new switch.
•
Zone changes can be configured nondisruptively. New zones and zone sets can be activated without interrupting traffic on unaffected ports or devices.
•
Zone membership criteria is based on Port world wide name (pWWN). The pWWN of an N port is attached to the switch as a member of the zone.
•
Default zone membership includes all ports or WWNs that do not have a specific membership association. Access between default zone members is controlled by the default zone policy.
Zoning Example
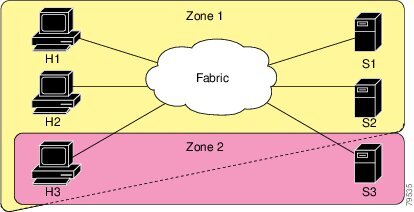
Figure 7-1 illustrates a zone set with two zones, zone 1 and zone 2, in a fabric. Zone 1 provides access from all three hosts (H1, H2, H3) to the data residing on storage systems S1 and S2. Zone 2 restricts the data on S3 to access only by H3. Note that H3 resides in both zones.
Figure 7-1 Fabric with Two Zones
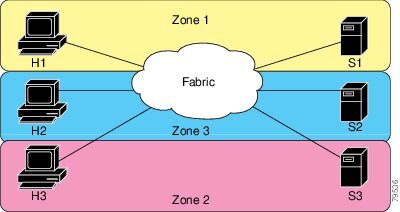
Of course, there are other ways to partition this fabric into zones. Figure 7-2 illustrates another possibility. Assume that there is a need to isolate storage system S2 for the purpose of testing new software. To achieve this, zone 3 is configured, which contains only host H2 and storage S2. You can restrict access to just H2 and S2 in zone 3, and to H1 and S1 in zone 1.
Figure 7-2 Fabric with Three Zones
Zone Implementation
The Cisco MDS 9020 Fabric Switch automatically supports the following basic zone features (no additional configuration is required):
•
Name server queries are soft-zoned.
•
Only active zone sets are distributed.
•
Unzoned devices cannot access each other.
•
Active zone sets cannot be changed without activating a full zone database.
•
Active zone sets are preserved across switch reboots.
•
Changes to the full database must be explicitly saved.
•
Zone reactivation (a zone set is active and you activate another zone set) does not disrupt existing traffic.
If required, you can additionally configure the following zone features:
•
Propagate full zone sets to all switches.
•
Change the default policy for unzoned members.
•
Bring E ports out of isolation.
Zone Configuration
A zone can be configured using one of the following types to assign members:
•
pWWN—The WWN of the N or NL port in hex format (for example, 10:00:00:23:45:67:89:ab).
•
FC alias—The alias name is in alphabetic characters (for example, Payroll) and denotes a WWN. The alias can also include multiple WWN members.
CautionYou must only configure pWWN-type zoning on an MDS switch running Cisco SAN-OS if there is a Cisco MDS 9020 switch running FabricWare in the same fabric to avoid Inter-Switch Link (ISL) isolation. It is important to remove all non-pWWN-type zone entries prior to merging fabrics.
Configuring a Zone
To configure a zone and assign a zone name, perform this task:
Alias Configuration
You can assign an alias name and configure an alias member using pWWN values.
Tip
The Cisco MDS 9020 Fabric Switch supports a maximum of 2500 aliases.
To create an alias using the fcalias command, perform this task:
Zone Set Creation
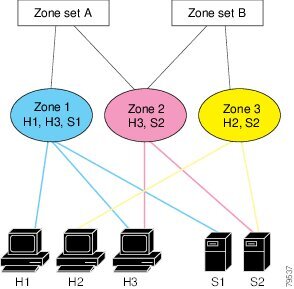
In Figure 7-3, two separate sets are created, each with its own membership hierarchy and zone members.
Figure 7-3 Hierarchy of Zone Sets, Zones, and Zone Members
Zones provide a mechanism for specifying access control, while zone sets are a grouping of zones to enforce access control in the fabric. Either zone set A or zone set B can be activated (but not together).
To create a zone set to include several zones, perform this task:
Active and Full Zone Set Considerations
Before configuring a zone set, consider the following guidelines:
•
When you create a zone set, that zone set becomes a part of the full zone set.
•
When you activate a zone set, a copy of the zone set from the full zone set is used to enforce zoning and is called the active zone set. An active zone set cannot be modified. A zone that is part of an active zone set is called an active zone.
•
The administrator can modify the full zone set even if a zone set with the same name is active. However, the modification will be enforced only upon reactivation.
•
When the activation is done, the active zone set is automatically stored in persistent configuration. This enables the switch to preserve the active zone set information across switch resets.
•
All other switches in the fabric receive the active zone set so they can enforce zoning in their respective switches.
•
Soft zoning is implemented using the active zone set. Modifications take effect during zone set activation.
Note
You must explicitly deactivate the currently active zone set before activating a new zone set.
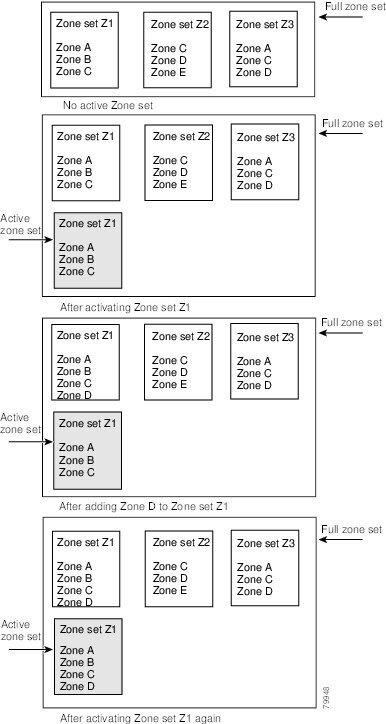
Figure 7-4 shows a zone being added to an activated zone set.
Figure 7-4 Active and Full Zone Sets
Activating a Zone Set
You can activate a zone set using the zoneset activate name command. The changes to a full zone set do not take effect until the zone set is activated with the zoneset activate name command.
Tip
You do not have to enter the copy running-config startup-config command to store the active zone set. However, you need to enter the copy running-config startup-config command to explicitly store full zone sets. It is not available across switch resets.
To activate a zone set, perform this task:
Zone Enforcement
Zoning is enforced in the form of soft zones. Each end device (N port or NL port) discovers other devices in the fabric by querying the name server. When a device logs in to the name server, the name server returns the list of other devices that can be accessed by the querying device. If an Nx port does not know about the FC IDs of other devices outside of its zone, it cannot access those devices. Zoning restrictions are applied only during interaction between the name server and the end device. If an end device somehow knows the FC ID of a device outside its zone, it can access that device.
The Default Zone
Each member of a fabric (in effect a device attached to an Nx port) can belong to any zone. If a member is not part of any active zone, it is considered to be part of the default zone. Therefore, if no zone set is active in the fabric, all devices are considered to be in the default zone. Even though a member can belong to multiple zones, a member that is part of the default zone cannot be part of any other zone. The switch determines whether or not a port is a member of the default zone when the attached port comes up.
Note
Unlike configured zones, default zone information is not distributed to the other switches in the fabric.
Traffic can either be permitted or denied among members of the default zone. This information is not distributed to all switches; it must be configured in each switch.
Note
When the switch is initialized for the first time, no zones are configured and all members are considered to be part of the default zone. Members are not permitted to talk to each other.
Configure the default zone policy on each switch in the fabric. If you change the default zone policy on one switch in a fabric, be sure to change it on all the other switches in the fabric.
Note
The default settings for default zone configurations can be changed.
To permit or deny traffic in the default zone, perform this task:
Full Zone Set Propagation
The Cisco MDS 9020 Fabric Switch distributes active zone sets when new E port links come up or when a new zone set is activated. The zone set distribution takes effect while sending merge requests to the adjacent switch or while activating a zone set.
The zoneset distribute full command in configuration mode distributes the full zone set along with the active zone set.
To propagate full zone sets to all switches, perform this task:
Step 1
switch# config t
Enters configuration mode.
Step 2
switch(config)# zoneset distribute full
Enables sending a full zone set along with an active zone set.
Recovering from Link Isolation
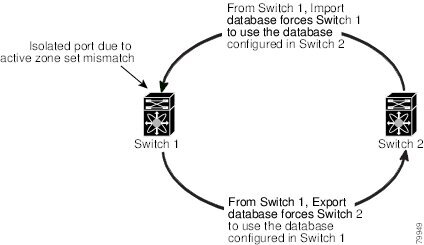
When two switches in a fabric are merged using an E port, the E ports may become isolated when the active zone sets are different between the two switches or fabrics. When an E port becomes isolated, you can recover that port from its isolated state using one of three options:
•
Import the neighboring switch's active zone set database, and replace the current active zone set. (See Figure 7-5.)
•
Export the current database to the neighboring switch. (See Figure 7-5.)
•
Manually resolve the conflict by editing the full zone set, activating the corrected zone set, and then bringing up the link.
Figure 7-5 Importing and Exporting the Database
Zone Database Information
If required, you can clear configured information stored in the zone server database.
Note
Clearing a zone set only erases the full zone database, not the active zone database.
Clearing the Zone Server Database
To clear the zone server database, use the clear zone database command:
switch# clear zone databaseThis command clears all configured information in the zone server.
Note
After entering a clear zone database command, you need to explicitly enter the copy running-config startup-config to ensure that the running configuration is used when you next start the switch.
Renaming Zone Sets, Zones and, fcaliases
To rename a zone set, zone, or fcalias, perform this task:
Displaying Zone Information
You can view any zone information by using the show command. If you request information for a specific object (for example, a specific zone, zone set, fcalias, or even a keyword like brief or active), only information for the specified object is displayed. If you do not request specific information, all available information is displayed. (See Examples 7-1 to 7-8.)
Example 7-1 Displays Zone Information
switch# show zonezone name Z1pwwn 10:00:00:c0:dd:07:00:f8fcalias name A1pwwn 10:00:00:c0:dd:07:00:f9Use the show zoneset command to view the configured zone sets.
Example 7-2 Displays Configured Zone Set Information
switch# show zonesetzoneset name ZS1zone name Z1pwwn 10:00:00:c0:dd:07:00:f8fcalias name A1pwwn 10:00:00:c0:dd:07:00:f9Use the show zone name command to display members of a specific zone.
Example 7-3 Displays Members of a Zone
switch# show zone name Zone1zone name Z1pwwn 10:00:00:c0:dd:07:00:f8fcalias name A1pwwn 10:00:00:c0:dd:07:00:f9Use the show fcalias command to display fcalias configuration.
Example 7-4 Displays fcalias Configuration
switch# show fcaliasfcalias name Alias2fcalias name Alias1pwwn 21:00:00:20:37:6f:db:ddpwwn 21:00:00:20:37:9c:48:e5Use the show zone member command to display all zones to which a member belongs using the pWWN.
Example 7-5 Displays Membership Status
switch# show zone member pwwn 10:00:00:c0:dd:07:00:f9fcalias name A1pwwn 10:00:00:c0:dd:07:00:f9Example 7-6 Displays Active Zones
switch# show zone activezone name zone1pwwn 10:11:22:33:44:55:66:77pwwn 10:11:22:33:44:55:66:88pwwn 10:11:22:33:44:55:66:99zone name zone2pwwn 20:11:22:33:44:55:66:00pwwn 20:11:22:33:44:55:66:01pwwn 20:11:22:33:44:55:66:02pwwn 20:11:22:33:44:55:66:03Example 7-7 Displays Active Zone Sets
switch# show zoneset activezoneset name circuszone name bozopwwn 10:11:22:33:44:55:66:77pwwn 10:11:22:33:44:55:66:88pwwn 10:11:22:33:44:55:66:99zone name clownpwwn 20:11:22:33:44:55:66:00pwwn 20:11:22:33:44:55:66:01pwwn 20:11:22:33:44:55:66:02pwwn 20:11:22:33:44:55:66:03Example 7-8 Displays Zone Status
switch# show zone statusFull Zoning Database :Zonesets: 1 Zones: 1 Aliases: 1Active Zoning Database:Name: ZS1 Zonesets: 1 Zones: 1Status:Merging the Database
The merge behavior is governed by the merge rules specified in Table 7-1.
CautionRemove all non-pWWN-type zone entries on all MDS switches running Cisco SAN-OS prior to merging fabrics if there is a Cisco MDS 9020 switch running FabricWare in the adjacent fabric to avoid Inter-Switch Link (ISL) isolation.
Default Zone Policies
To permit or deny traffic in the default zone, perform this task:
Default Settings
Table 7-2 lists the default settings for basic zone parameters.
Table 7-2 Default Basic Zone Parameters
Default zone policy
Denied to all members.
Full zone set distribute
The full zone set(s) is not distributed.

 Feedback
Feedback