Information About IGMP Snooping
Internet Group Management Protocol (IGMP) is a part of the IP and supports and manages IP multicast between a host and a multicast router. IP multicast allows the transfer of IP data to a host collection formed by a multicast group. The relationships of the multicast group members are dynamic. A host can dynamically add or exit this group to reduce network load to a minimum, and to improve effective data transmission in a network.
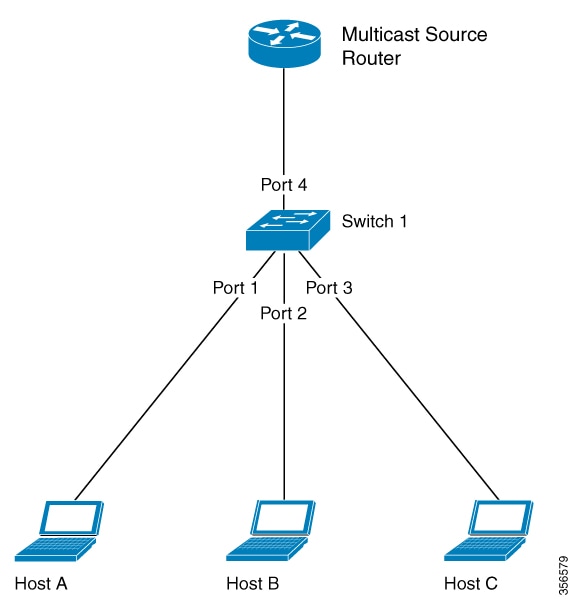
IGMP Snooping monitors IGMP packets between a host and routers. It can dynamically create, maintain, and delete a multicast address table. A multicast frame can transfer a packet according to its own multicast address table.

 Feedback
Feedback