The table below lists the TrustSec features to be eventually implemented
on TrustSec-enabled Cisco switches. Successive general availability releases of
TrustSec will expand the number of switches supported and the number of
TrustSec features supported per switch.
| Cisco TrustSec Feature
|
Description
|
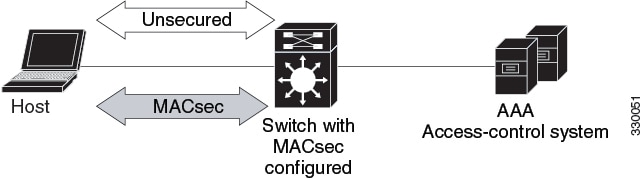
| 802.1AE Tagging (MACsec)
|
Protocol for IEEE 802.1AE-based wire-rate hop-to-hop Layer 2
encryption.
Between MACsec-capable devices, packets are encrypted on
egress from the transmitting device, decrypted on ingress to the receiving
device, and in the clear within the devices.
This feature is only available between TrustSec
hardware-capable devices.
|
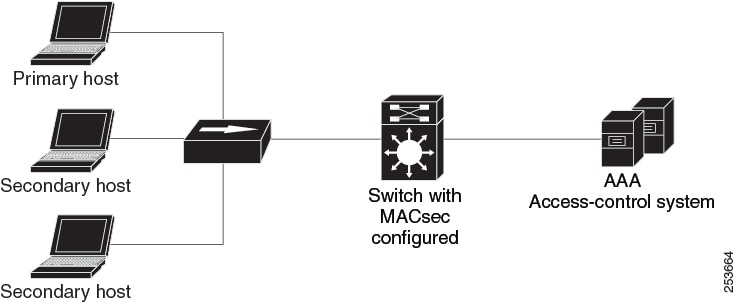
| Endpoint Admission Control (EAC)
|
EAC is an authentication process for an endpoint user or a
device connecting to the TrustSec domain. Usually EAC takes place at the access
level switch. Successful authentication and authorization in the EAC process
results in Security Group Tag assignment for the user or device. Currently EAC
can be 802.1X, MAC Authentication Bypass (MAB), and Web Authentication Proxy
(WebAuth).
|
| Network Device Admission Control (NDAC)
|
NDAC is an authentication process where each network device
in the TrustSec domain can verify the credentials and trustworthiness of its
peer device. NDAC utilizes an authentication framework based on IEEE 802.1X
port-based authentication and uses EAP-FAST as its EAP method. Successful
authentication and authorization in NDAC process results in Security
Association Protocol negotiation for IEEE 802.1AE encryption.
|
| Security Association Protocol (SAP)
|
After NDAC authentication, the Security Association Protocol
(SAP) automatically negotiates keys and the cipher suite for subsequent MACSec
link encryption between TrustSec peers. SAP is defined in IEEE 802.11i.
|
| Security Group Tag (SGT)
|
An SGT is a 16-bit single label indicating the security
classification of a source in the TrustSec domain. It is appended to an
Ethernet frame or an IP packet.
|
|
SGT Exchange Protocol (SXP)
|
Security Group Tag Exchange Protocol (SXP). With SXP, devices
that are not TrustSec-hardware-capable can receive SGT attributes for
authenticated users and devices from the Cisco Identity Services Engine (ISE)
or the Cisco Secure Access Control System (ACS). The devices can then forward a
sourceIP-to-SGT binding to a TrustSec-hardware-capable device will tag the
source traffic for SGACL enforcement.
|
When both ends of a link support 802.1AE MACsec, SAP negotiation occurs.
An EAPOL-key exchange occurs between the supplicant and the authenticator to
negotiate a cipher suite, exchange security parameters, and manage keys.
Successful completion of these tasks results in the establishment of a security
association (SA).
Depending on your software version and licensing and link hardware support, SAP negotiation can use one of these modes of
operation:
-
Galois Counter Mode (GCM)—authentication and encryption
-
GCM authentication (GMAC)— GCM authentication, no encryption
-
No Encapsulation—no encapsulation (clear text)
-
Null—encapsulation, no authentication or encryption

 Feedback
Feedback