IPv6 ACLs Overview
You can filter IP Version 6 (IPv6) traffic by creating IPv6 access control lists (ACLs) and applying them to interfaces similar to how you create and apply IP Version 4 (IPv4) named ACLs. You can also create and apply input router ACLs to filter Layer 3 management traffic when the switch is running IP base and LAN base feature sets.
A switch supports three types of IPv6 ACLs:
-
IPv6 router ACLs are supported on outbound or inbound traffic on Layer 3 interfaces, which can be routed ports, switch virtual interfaces (SVIs), or Layer 3 EtherChannels. IPv6 router ACLs apply only to IPv6 packets that are routed.
-
IPv6 port ACLs are supported on outbound and inbound Layer 2 interfaces. IPv6 port ACLs are applied to all IPv6 packets entering the interface.
-
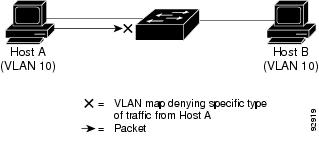
VLAN ACLs or VLAN maps access-control all packets in a VLAN. You can use VLAN maps to filter traffic between devices in the same VLAN. ACL VLAN maps are applied on L2 VLANs. VLAN maps are configured to provide access control based on Layer 3 addresses for IPv6. Unsupported protocols are access-controlled through MAC addresses using Ethernet ACEs. After a VLAN map is applied to a VLAN, all packets entering the VLAN are checked against the VLAN map.
The switch supports VLAN ACLs (VLAN maps) for IPv6 traffic.
You can apply both IPv4 and IPv6 ACLs to an interface. As with IPv4 ACLs, IPv6 port ACLs take precedence over router ACLs.
Switch Stacks and IPv6 ACLs
The active switch supports IPv6 ACLs in hardware and distributes the IPv6 ACLs to the stack members.
If a standby switch takes over as the active switch, it distributes the ACL configuration to all stack members. The member switches sync up the configuration distributed by the new active switch and flush out entries that are not required.
When an ACL is modified, attached to, or detached from an interface, the active switch distributes the change to all stack members.
ACL Precedence
When VLAN maps, Port ACLs, and router ACLs are configured on the same switch, the filtering precedence, from greatest to least for ingress traffic is port ACL, VLAN map, and then router ACL. For egress traffic, the filtering precedence is router ACL, VLAN map, and then port ACL.
The following examples describe simple use cases:
-
When both an input port ACL and a VLAN map are applied, incoming packets received on ports with a port ACL applied are filtered by the port ACL. Other packets are filtered by the VLAN map
-
When an input router ACL and input port ACL exist in a switch virtual interface (SVI), incoming packets received on ports to which a port ACL is applied are filtered by the port ACL. Incoming routed IP packets received on other ports are filtered by the router ACL. Other packets are not filtered.
-
When an output router ACL and input port ACL exist in an SVI, incoming packets received on the ports to which a port ACL is applied are filtered by the port ACL. Outgoing routed IP packets are filtered by the router ACL. Other packets are not filtered.
-
When a VLAN map, input router ACL, and input port ACL exist in an SVI, incoming packets received on the ports to which a port ACL is applied are only filtered by the port ACL. Incoming routed IP packets received on other ports are filtered by both the VLAN map and the router ACL. Other packets are filtered only by the VLAN map.
-
When a VLAN map, output router ACL, and input port ACL exist in an SVI, incoming packets received on the ports to which a port ACL is applied are only filtered by the port ACL. Outgoing routed IP packets are filtered by both the VLAN map and the router ACL. Other packets are filtered only by the VLAN map.
VLAN Maps
VLAN ACLs or VLAN maps are used to control network traffic within a VLAN. You can apply VLAN maps to all packets that are bridged within a VLAN in the switch or switch stack. VACLs are strictly for security packet filtering and for redirecting traffic to specific physical interfaces. VACLs are not defined by direction (ingress or egress).
All non-IP protocols are access-controlled through MAC addresses and Ethertype using MAC VLAN maps. (IP traffic is not access controlled by MAC VLAN maps.) You can enforce VLAN maps only on packets going through the switch; you cannot enforce VLAN maps on traffic between hosts on a hub or on another switch connected to this switch.
With VLAN maps, forwarding of packets is permitted or denied, based on the action specified in the map.
Hitless TCAM Update
The Hitless TCAM update for IPv4 and IPv6 provides the capability to apply existing features to the incoming traffic while updating new features in the TCAM. Any change in IPv4 and IPv6 ACL on a given interface would trigger a reprogramming of TCAM.
Starting with Cisco IOS XE Fuji 16.8.1a, Hitless TCAM update is enabled.
This feature is always enabled. You cannot disable this feature.
-
If there are value compare unit (VCU) registers in use from ACEs with layer 4 operators, there could be a few packet drops during the change.
-
If there are not enough VCU bits remaining to add a second set of access control entries and if there is not enough space in TCAM to expand these entries, the old ACL change method will apply; which will drop all packets, delete the old ACL, add the new ACL entries into TCAM, and then remove the entry that is causing the packets to drop.
-
If there is not enough space in TCAM to add the modified entries, the old ACL change method will automatically be applied. 
Note
-
To perform Hitless ACL update for an IPv4 ACL which has X number of ACEs, TCAM should have a free space for accommodating X+1 entries.
-
To perform Hitless ACL update for an IPv6 ACL which has X number of ACEs, TCAM should have a free space for accommodating 2X+2 entries.
-
Interactions with Other Features and Switches
-
If an IPv6 router ACL is configured to deny a packet, the packet is not routed. A copy of the packet is sent to the Internet Control Message Protocol (ICMP) queue to generate an ICMP unreachable message for the frame.
-
If a bridged frame is to be dropped due to a port ACL, the frame is not bridged.
-
You can create both IPv4 and IPv6 ACLs on a switch or switch stack, and you can apply both IPv4 and IPv6 ACLs to the same interface. Each ACL must have a unique name; an error message appears if you try to use a name that is already configured.
You use different commands to create IPv4 and IPv6 ACLs and to attach IPv4 or IPv6 ACLs to the same Layer 2 or Layer 3 interface. If you use the wrong command to attach an ACL (for example, an IPv4 command to attach an IPv6 ACL), you receive an error message.
-
You cannot use MAC ACLs to filter IPv6 frames. MAC ACLs can only filter non-IP frames.
-
If the hardware memory is full, packets are dropped on the interface and an unload error message is logged.
 Feedback
Feedback