Prerequisites for 802.1x Port-Based Authentication
The following tasks must be completed before implementing the IEEE 802.1X Port-Based Authentication feature:
-
IEEE 802.1X must be enabled on the device port.
-
The device must have a RADIUS configuration and be connected to the Cisco secure access control server (ACS). You should understand the concepts of the RADIUS protocol and have an understanding of how to create and apply access control lists (ACLs).
-
EAP support must be enabled on the RADIUS server.
-
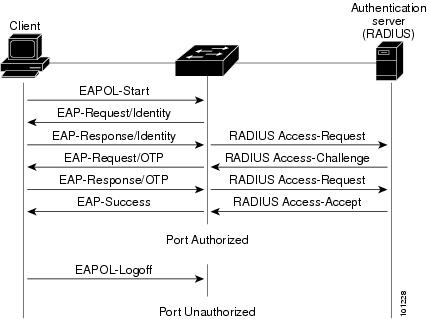
You must configure the IEEE 802.1X supplicant to send an EAP-logoff (Stop) message to the device when the user logs off. If you do not configure the IEEE 802.1X supplicant, an EAP-logoff message is not sent to the device and the accompanying accounting Stop message is not sent to the authentication server.
-
Authentication, authorization, and accounting (AAA) must be configured on the port for all network-related service requests. The authentication method list must be enabled and specified. A method list describes the sequence and authentication method to be queried to authenticate a user.
-
The port must be successfully authenticated.

 Feedback
Feedback