Cisco VSG for Microsoft Hyper-V, Release 5.2(1)VSG1(4.1) and Cisco VNMC, Release 2.1 Installation Guide
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- June 3, 2013
Chapter: Installing the Cisco VNMC and Cisco VSG - Quick Start
Installing the Cisco VNMC and Cisco VSG - Quick Start
This chapter contains the following sections:
- Information About Installing the Cisco VNMC and the Cisco VSG
- Task 1: Installing the Cisco VNMC from an ISO Image
- Task 2: On the VSM, Configuring the Cisco VNMC Policy Agent
- Task 3: On the VSM, Preparing Cisco VSG Port Profiles
- Task 4: Installing the Cisco VSG from an ISO Image
- Task 5: On the VSG, Configuring the Cisco VNMC Policy Agent
- Task 6: On the Cisco VSG and Cisco VNMC, Verifying the VNM Policy-Agent Status
- Task 7: On the Cisco VNMC, Configuring a Tenant, Security Profile, and Compute Firewall
- Task 8: On the Cisco VNMC, Assigning the Cisco VSG to the Compute Firewall
- Task 9: On the Cisco VNMC, Configuring a Permit-All Rule
- Task 10: On the Cisco VSG, Verifying the Permit-All Rule
- Task 11: Enabling Logging
- Task 12: Enabling the Traffic VM Port-Profile for Firewall Protection and Verifying the Communication Between the VSM, VEM, and VSG
- Task 13: Sending Traffic Flow and on the Cisco VSG Verifying Statistics and Logs
Information About Installing the Cisco VNMC and the Cisco VSG
This chapter describes how to install and set up a basic working configuration of the Cisco VNMC and Cisco VSG. The example in this chapter uses the ISO files of the software for installation. The steps assume that the Cisco Nexus 1000V Series switch is operational, and endpoint VMs are already installed.
Cisco VSG and Cisco VNMC Installation Planning Checklists
Planning the arrangement and architecture of your network and equipment is essential for a successful operation of the Cisco VNMC and Cisco VSG.
- Basic Hardware and Software Requirements
- VLAN Configuration Requirements
- Required Cisco VNMC and Cisco VSG Information
- Tasks and Prerequisites Checklist
- Host Requirements
- Obtaining the Cisco VNMC and the Cisco VSG Software
Basic Hardware and Software Requirements
Cisco VSG is supported as VSB on Nexus Cloud Services platform only.
- Microsoft SCVMM SP1
- 6 GB (2 GB for VSG and 4 GB for VNMC) of memory
- 27 GB (2 GB for VSG and 25 GB for VNMC) of disk space
- Three Network Interfaces (NICs) for VSG
- Cisco VSG software available for download at http://www.cisco.com/en/US/products/ps11208/index.html
- Cisco VNMC software available for download at http://www.cisco.com/en/US/products/ps11213/index.html
VLAN Configuration Requirements
Follow these VLAN requirements top prepare the Cisco Nexus 1000V Series switch for further installation processes:
- You must have a HA VLAN configured on the Cisco Nexus 1000V Series switch uplink ports (the VLAN does not need to be the system VLAN).
- You must have two port profiles that are configured on the Cisco Nexus 1000V Series switch: one port profile for the service VLAN and one port profile for the HA VLAN (you will be configuring the Cisco VSG IP address on the Cisco VSG so that the Cisco Nexus 1000V Series switch can communicate with it)
Required Cisco VNMC and Cisco VSG Information
The following information can be used later during the Cisco VNMC and Cisco VSG installation.
| Type | Your Information | ||
|---|---|---|---|
Cisco VSG name—Unique within the inventory folder and up to 80 characters |
|||
Hostname—Where the Cisco VSG will be installed in the inventory folder |
|||
ISOs—Managed within SCVMM library, if stored at C:\ProgramData\Virtual Machine Manager Library Files\ISO to manage. Refresh the SCVMM library after saving the ISO file to the specified location. |
|||
Cisco VSG management IP address |
|||
VSM management IP address |
|||
Cisco VNMC instance IP address |
|||
Mode for installing the Cisco VSG |
|||
Cisco VSG VLAN number |
|||
Cisco VSG port profile name
|
|||
HA pair ID (HA domain ID) |
|||
Cisco VSG admin password |
|||
Cisco VNMC admin password |
|||
Cisco VSM admin password |
|||
Shared secret password (Cisco VNMC, Cisco VSG policy agent, Cisco VSM policy agent) |
Tasks and Prerequisites Checklist
Tasks |
Prerequisites | ||||
|---|---|---|---|---|---|
| Task 1: Installing the Cisco VNMC from an ISO image. |
|
||||
| Task 2: On the VSM, Configuring the Cisco VNMC Policy Agent |
|
||||
| Task 3: On the VSM, Preparing Cisco VSG Port Profiles |
|
||||
| Task 4: Installing the Cisco VSG from an ISO Image |
|
||||
| Task 5: On the VSG, Configuring the Cisco VNMC Policy Agent |
|
||||
| Task 6: On the Cisco VSG and Cisco VNMC, Verifying the VNM Policy-Agent Status | — | ||||
| Task 7: On the Cisco VNMC, Configuring a Tenant, Security Profile, and Compute Firewall |
|
||||
| Task 8: On the Cisco VNMC, Assigning the Cisco VSG to the Compute Firewall | — | ||||
| Task 9: On the Cisco VNMC, Configuring a Permit-All Rule | — | ||||
| Task 10: On the Cisco VSG, Verifying the Permit-All Rule | — | ||||
| Task 11: Enabling Logging | — | ||||
| Task 12: Enabling the Traffic VM Port-Profile for Firewall Protection and Verifying the Communication Between the VSM, VEM, and VSG |
|
||||
| Task 13: Sending Traffic Flow and on the Cisco VSG Verifying Statistics and Logs | — |
Host Requirements
Obtaining the Cisco VNMC and the Cisco VSG Software
The Cisco VSG software is available for download at the following URL:
http://www.cisco.com/en/US/products/ps11208/index.htmlThe Cisco VNMC software is available for download at the following URL:
http://www.cisco.com/en/US/products/ps11213/index.htmlTask 1: Installing the Cisco VNMC from an ISO Image
Know the following:
Task 2: On the VSM, Configuring the Cisco VNMC Policy Agent
Once the Cisco VNMC is installed, you must register the VSM with the Cisco VNMC policy.
Make sure that you know the following:
-
The Cisco VNMC policy-agent image is available on the VSM (for example, vsmhv-pa.2.1.1a.bin)

Note
The string vsmhv-pa must appear in the image name as highlighted.
- The IP address of the Cisco VNMC
- The shared secret password you defined during the Cisco VNMC installation
-
That IP connectivity between the VSM and the Cisco VNMC is working

Note
If you upgrade your VSM, you must also copy the latest Cisco VSM policy agent image. This image is available in the Cisco VNMC image bundle to boot from a flash drive and to complete registration with the Cisco VNMC.
 Note |
VSM clock should be synchronized with the VNMC clock. |
1. On the VSM, enter the following commands:
2. Check the status of the VNM policy agent configuration to verify that you have installed the Cisco VNMC correctly and it is reachable by entering the show vnm-pa status command. This example shows that the Cisco VNMC is reachable and the installation is correct:
DETAILED STEPS
| Step 1 |
On the VSM, enter the following commands: vsm# configure terminal vsm(config)# vnm-policy-agent vsm(config-vnm-policy-agent)# registration-ip 10.193.75.95 vsm(config-vnm-policy-agent)# shared-secret Example_Secret123 vsm(config-vnm-policy-agent)# policy-agent-image vsmhv-pa.2.1.1a.bin vsm(config-vnm-policy-agent)# exit vsm(config)# copy running-config startup-config vsm(config)# exit |
| Step 2 |
Check the status of the VNM policy agent configuration to verify that you have installed the Cisco VNMC correctly and it is reachable by entering the show vnm-pa status command. This example shows that the Cisco VNMC is reachable and the installation is correct: vsm# show vnm-pa status VNM Policy-Agent status is - Installed Successfully. Version 2.1(1a)-vsm vsm The VSM is now registered with the Cisco VNMC. |
This example shows that the Cisco VNMC is unreachable or an incorrect IP is configured:
vsm# show vnm-pa status VNM Policy-Agent status is - Installation Failure VNMC not reachable. vsm#
This example shows that the VNM policy-agent is not configured or installed:
vsm# show vnm-pa status VNM Policy-Agent status is - Not Installed
Task 3: On the VSM, Preparing Cisco VSG Port Profiles
To prepare Cisco VSG port profiles, you must create the VLANs and use the VLANs in the Cisco VSG data port profile and the Cisco VSG-ha port profile.
Make sure that you know the following:
1. Create a Cisco VSG data port profile and a Cisco VSG-ha port profile by first enabling the Cisco VSG data port-profile configuration mode. Use the configure command to enter global configuration mode.
2. Enter the configuration commands to set up an uplink port-profile.
3. Create the network segment and port-profile for the Data VLAN.
4. Create the network segment and port-profile for the HA VLAN.
DETAILED STEPS
| Step 1 |
Create a Cisco VSG data port profile and a Cisco VSG-ha port profile by first enabling the Cisco VSG data port-profile configuration mode. Use the configure command to enter global configuration mode. vsm# configure |
| Step 2 |
Enter the configuration commands to set up an uplink port-profile. vsm(config)# nsm network logical vsm_LogicalNet vsm(config-logical-net)# exit vsm(config)# nsm network segment pool vsm_NetworkSite vsm(config-net-seg-pool)# member-of network logical vsm_LogicalNet vsm(config-net-seg-pool)# exit vsm(config)# nsm ip pool template VM_IP_Pool vsm(config-ip-pool-template)# ip-address 10.0.0.2 10.0.0.255 vsm(config-ip-pool-template)# netmask 255.255.255.0 vsm(config-ip-pool-template)# gateway 10.0.0.1 vsm(config-ip-pool-template)# exit vsm(config)# nsm network uplink vsm_Uplink vsm(config-uplink-net)# allow network segment pool vsm_NetworkSite vsm(config-uplink-net)# publish uplink-network vsm(config-uplink-net)# exit |
| Step 3 |
Create the network segment and port-profile for the Data VLAN. vsm(config)# nsm network segment VMAccess_502 vsm(config-net-seg)# member-of network segment pool vsm_NetworkSite vsm(config-net-seg)# switchport access vlan 502 vsm(config-net-seg)# import ip-pool-template VM_IP_Pool vsm(config-net-seg)# publish network-segment vsm(config-net-seg)# exit vsm(config)# port-profile type vethernet VSG_Data vsm(config-port-prof)# no shutdown vsm(config-port-prof)# state enabled vsm(config-port-prof)# publish port-profile vsm(config-port-prof)# exit |
| Step 4 |
Create the network segment and port-profile for the HA VLAN. vsm(config)# nsm network segment VMAccess_503 vsm(config-net-seg)# member-of network segment pool vsm_NetworkSite vsm(config-net-seg)# switchport access vlan 503 vsm(config-net-seg)# import ip-pool-template VM_IP_Pool vsm(config-net-seg)# publish network-segment vsm(config-net-seg)# exit vsm(config)# port-profile type vethernet VSG_HA vsm(config-port-prof)# no shutdown vsm(config-port-prof)# state enabled vsm(config-port-prof)# publish port-profile vsm(config-port-prof)# exit |
Task 4: Installing the Cisco VSG from an ISO Image
 Note |
Cisco VSG is supported as VSB on Nexus Cloud Services platform only. |
Make sure that you know the following:
- Microsoft SCVMM SP1 is installed.
- Download the Cisco VSG ISO image and upload it to the server (C:\ProgramData\Virtual Machine Manager Library Files\ISO). Refresh the library server under the Library tab.
- The Cisco VSG-Data port profile: VSG-Data
- The Cisco VSG-ha port profile: VSG-ha
- The HA ID
- The IP/subnet mask/gateway information for the Cisco VSG
- The admin password
- 2 GB RAM and 4 GB hard disk space are available
- The Cisco VNMC IP address
- The shared secret password
- The IP connectivity between Cisco VSG and Cisco VNMC is okay.
- The Cisco VSG VNM-PA image name (vsghv-pa.2.1.1a.bin) is available.
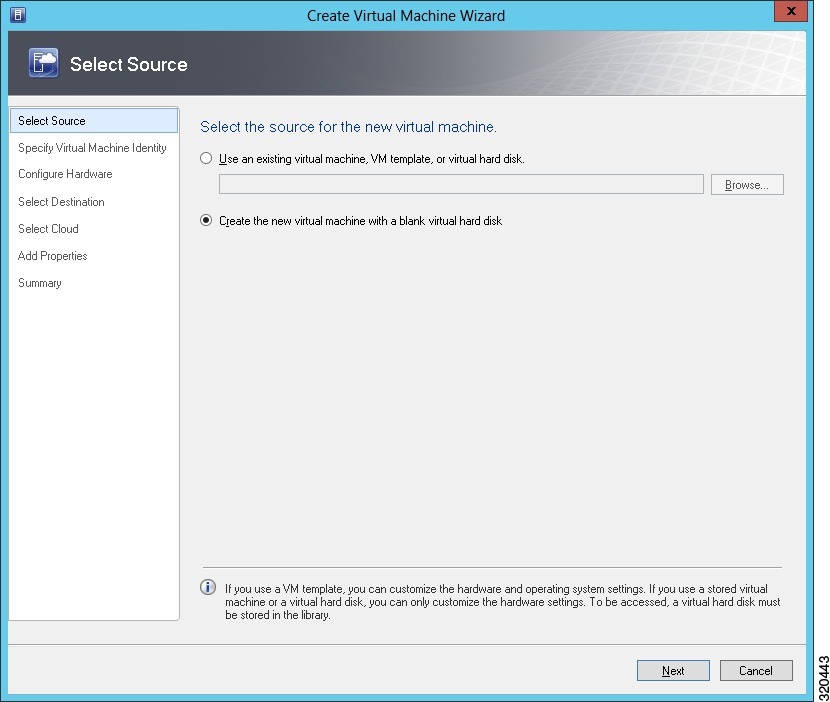
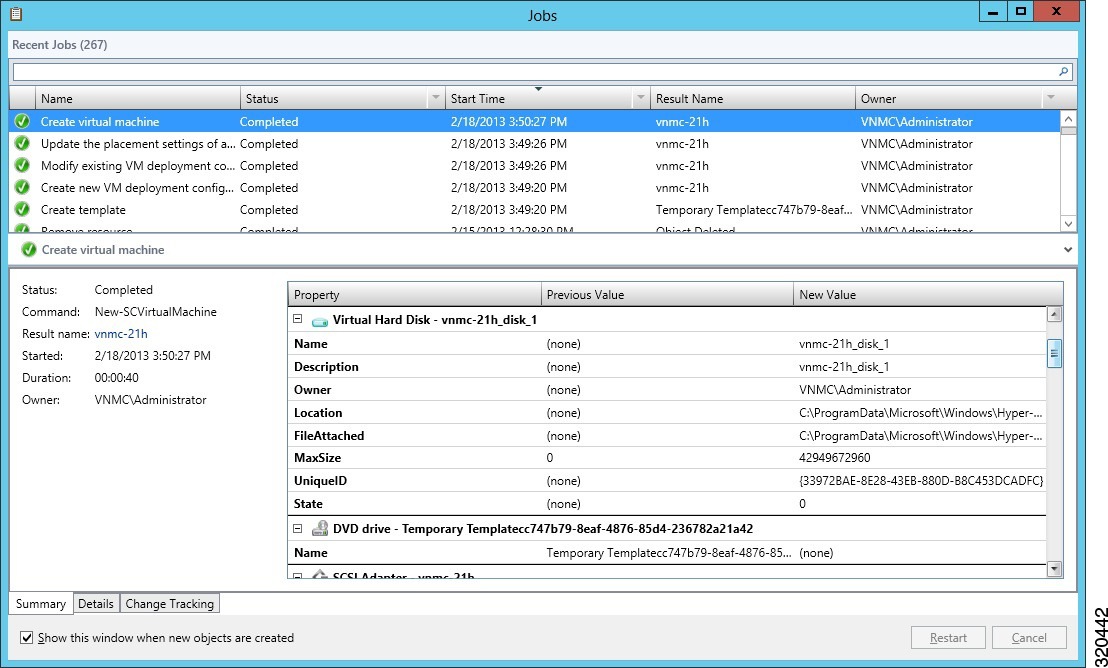
| Step 1 | Launch SCVMM. |
| Step 2 | In the VMs and Services tab, click Create Virtual Machine. |
| Step 3 | In the Create Virtual Machine Wizard, in theSelect Source screen, check Create the new virtual machine with a blank virtual hard disk radio button and click Next. |
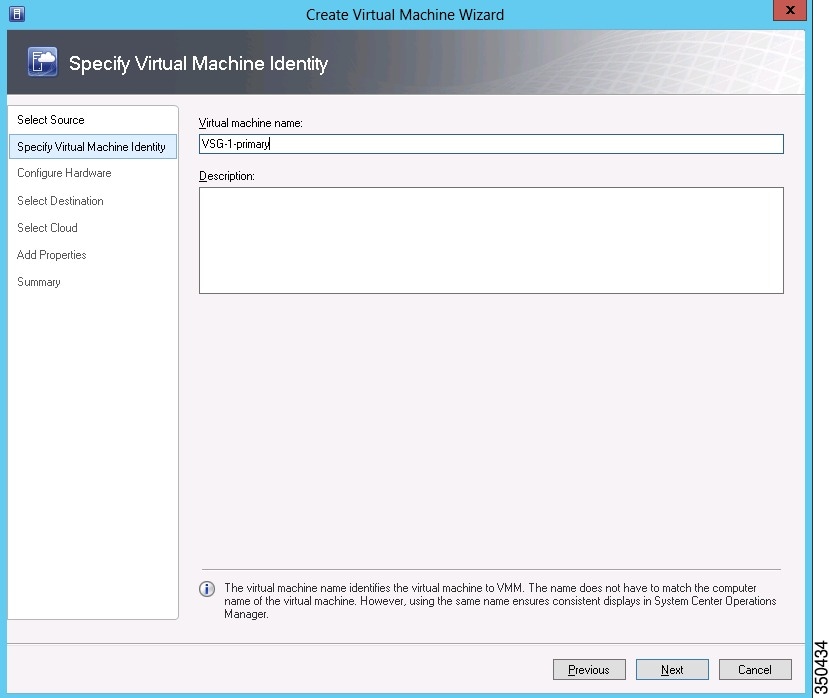
| Step 4 |
In the Specify Virtual Machine Identity screen, enter the name for the Cisco VSG in the Virtual machine name field and click Next.
|
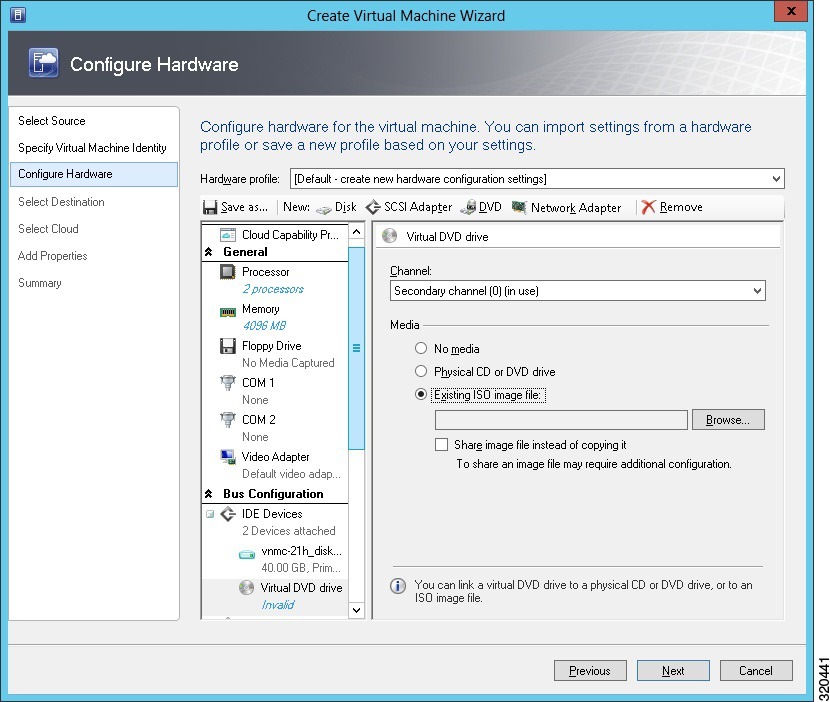
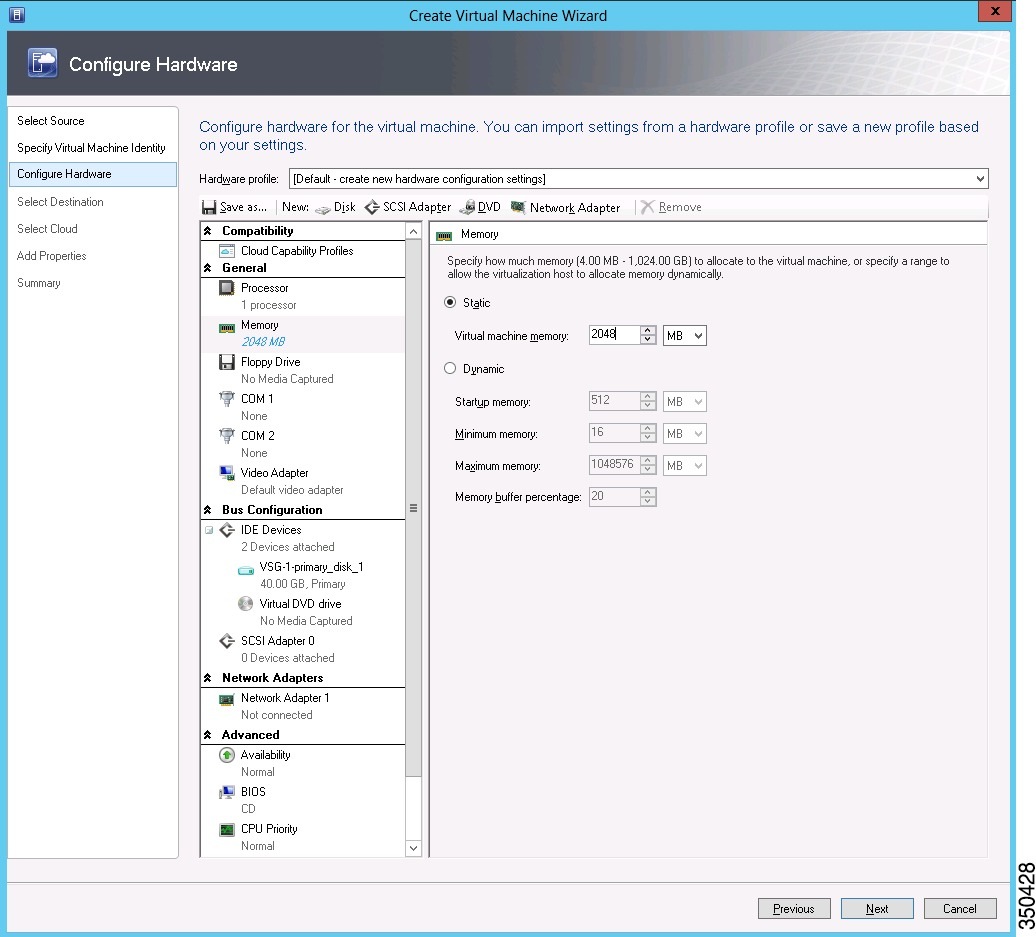
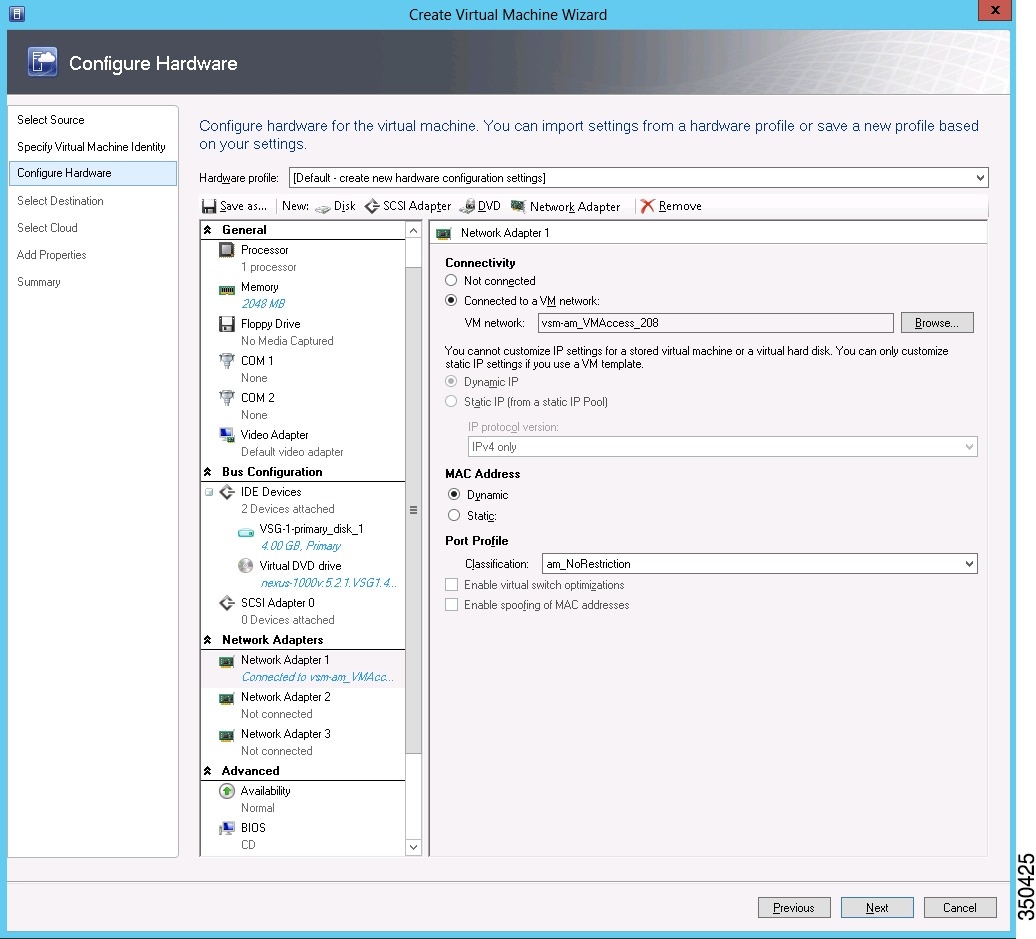
| Step 5 |
In the Configure Hardware section, do the following:
|
| Step 6 | In the Select Destination section, choose Place the virtual machine in a host and select the host group on which you want to store the VSG from the drop-down and click Next. |
| Step 7 |
In the Select Host section, select the host you wish to place the VSG on and click Next.
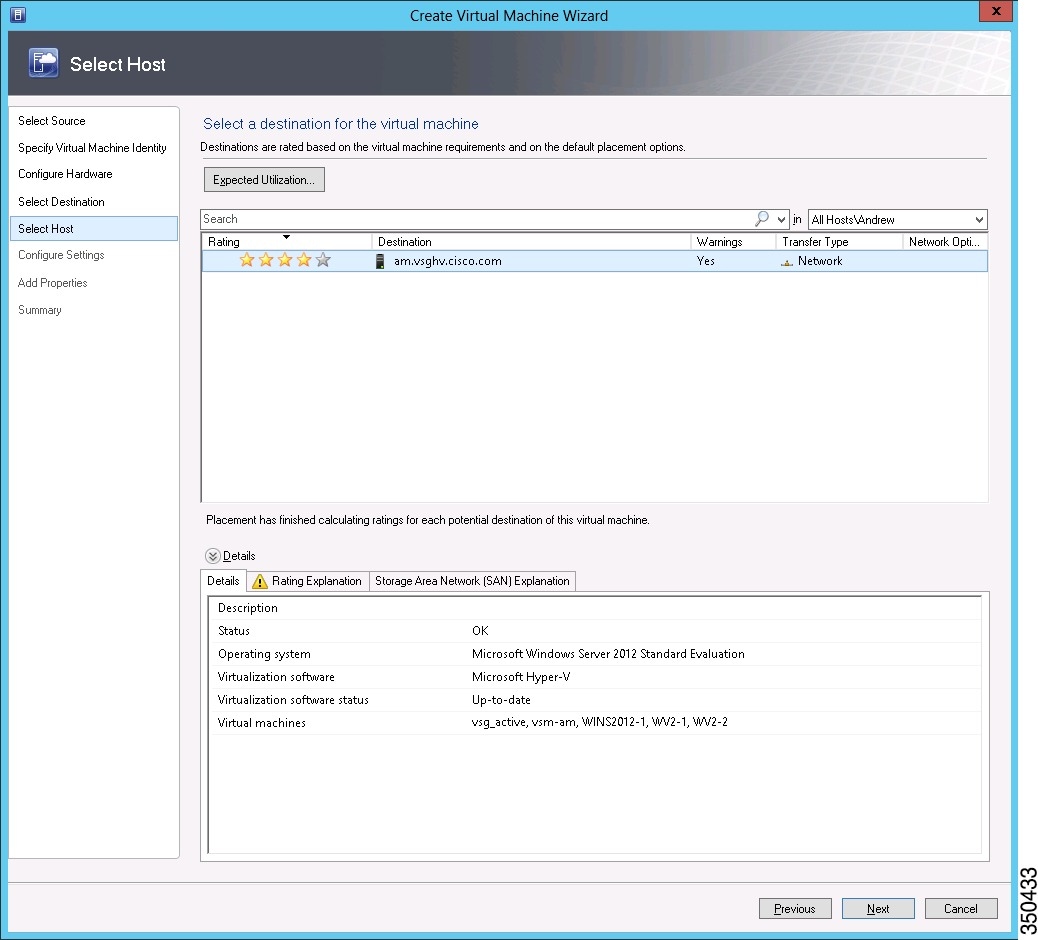
|
| Step 8 | In the Configure Settings section, review the virtual machine settings to ensure they are correct and click Next. |
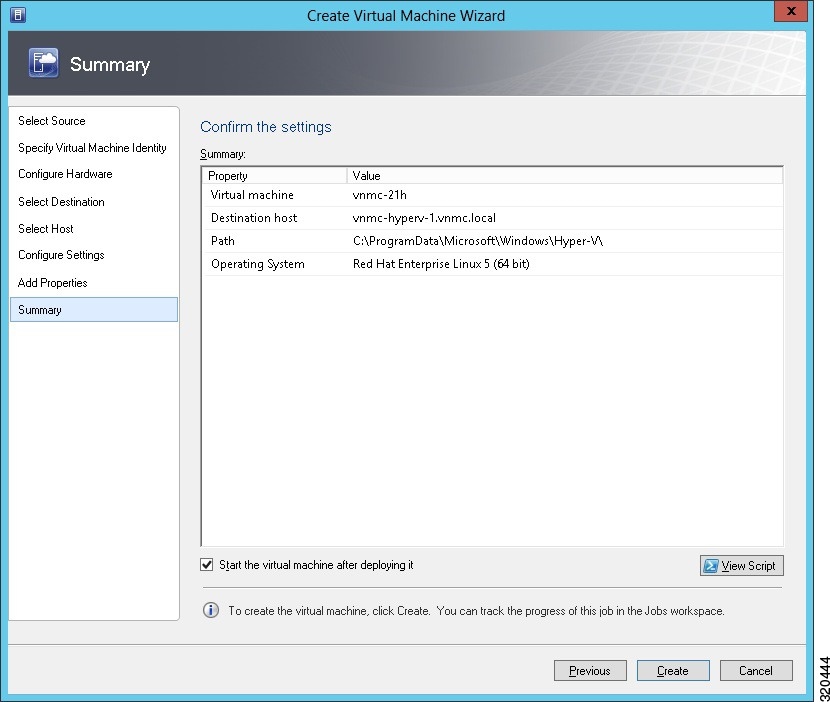
| Step 9 | (Optional) In the Add Properties section, select Other Linux (64-bit) from the Operating System drop-down, then click Next. |
| Step 10 | In the Summary section, click Create. |
| Step 11 | Launch the Microsoft Hyper-V Manager on the server hosting the VSG. |
| Step 12 | In the left pane, select the server that hosts the VSG instance you created. |
| Step 13 | Under Virtual Machines, select the VSG you created. |
| Step 14 | Under Actions, click Settings to open the Settings dialog-box. |
| Step 15 | Select the first interface for the VSG instance and select Advanced Features. |
| Step 16 | Under MAC address, select Enable MAC address spoofing. |
| Step 17 | Click OK. |
| Step 18 | Close the Microsoft Hyper-V Manager to return to the SCVMM interface. |
| Step 19 | After MAC spoofing is configured and the VSG is successfully installed, select the VSG in the VMs and Services tab and click Power On. |
| Step 20 | Connect to the VSG using Connect or View -> Connect via Console. |
Task 5: On the VSG, Configuring the Cisco VNMC Policy Agent
Once the Cisco VNMC is installed, you must register the VSG with the Cisco VNMC.
Make sure that you know the following:
-
The Cisco VNMC policy-agent image is available on the VSG (for example, vsghv-pa.2.1.1a.bin)

Note
The string vsghv-pa must appear in the image name as highlighted.
- The IP address of the Cisco VNMC
- The shared secret password you defined during the Cisco VNMC installation
-
That IP connectivity between the VSG and the Cisco VNMC is working

Note
If you upgrade your VSG, you must also copy the latest Cisco VSG policy agent image. This image is available in the Cisco VNMC image bundle to boot from a flash drive and to complete registration with the Cisco VNMC.
 Note |
VSG clock should be synchronized with the VNMC clock. |
1. On the VSG, enter the following commands:
2. Check the status of the VNM policy agent configuration to verify that you have installed the Cisco VNMC correctly and it is reachable by entering the show vnm-pa status command. This example shows that the Cisco VNMC is reachable and the installation is correct:
DETAILED STEPS
| Step 1 |
On the VSG, enter the following commands: vsg# configure terminal vsg(config)# vnm-policy-agent vsg(config-vnm-policy-agent)# registration-ip 10.193.75.95 vsg(config-vnm-policy-agent)# shared-secret Example_Secret123 vsg(config-vnm-policy-agent)# policy-agent-image vsghv-pa.2.1.1a.bin vsg(config-vnm-policy-agent)# exit vsg(config)# copy running-config startup-config vsg(config)# exit |
| Step 2 |
Check the status of the VNM policy agent configuration to verify that you have installed the Cisco VNMC correctly and it is reachable by entering the show vnm-pa status command. This example shows that the Cisco VNMC is reachable and the installation is correct: vsg# show vnm-pa status VNM Policy-Agent status is - Installed Successfully. Version 2.1(1a)-vsg vsg# The VSG is now registered with the Cisco VNMC. |
This example shows that the Cisco VNMC is unreachable or an incorrect IP is configured:
vsg# show vnm-pa status VNM Policy-Agent status is - Installation Failure VNMC not reachable. vsg#
This example shows that the VNM policy-agent is not configured or installed:
vsg# show vnm-pa status VNM Policy-Agent status is - Not Installed
Task 6: On the Cisco VSG and Cisco VNMC, Verifying the VNM Policy-Agent Status
You can use the show vnm-pa status command to verify the VNM policy-agent status (which can indicate that you have installed the policy-agent successfully).
1. Log in to the Cisco VSG.
2. Check the status of VNM-PA configuration by entering the following command:
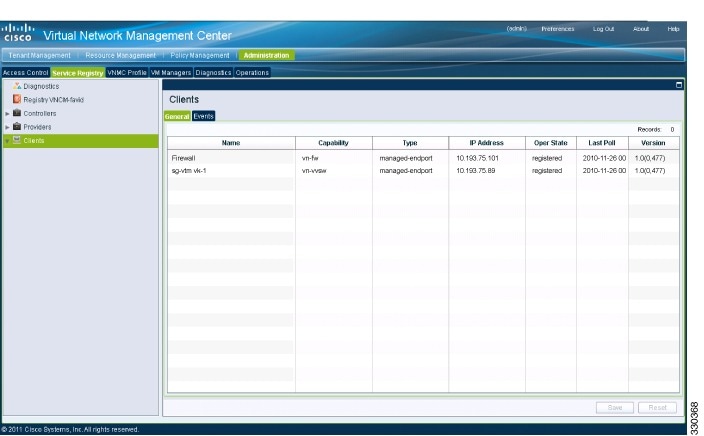
3. Log in to the Cisco VNMC. The VNMC Administration on Service Registry window opens.
4. Choose .
5. In the Client pane of the VNMC Administration Service Registry window, verify that the Cisco VSG and VSM information is listed.
DETAILED STEPS
| Step 1 | Log in to the Cisco VSG. |
| Step 2 |
Check the status of VNM-PA configuration by entering the following command: vsg# show vnm-pa status VNM Policy-Agent status is - Installed Successfully. Version 2.0(1a)-vsg vsg# |
| Step 3 |
Log in to the Cisco VNMC. The VNMC Administration on Service Registry window opens.
|
| Step 4 | Choose . |
| Step 5 | In the Client pane of the VNMC Administration Service Registry window, verify that the Cisco VSG and VSM information is listed. |
Task 7: On the Cisco VNMC, Configuring a Tenant, Security Profile, and Compute Firewall
Now that you have the Cisco VNMC and the Cisco VSG successfully installed with the basic configurations, you should configure some of the basic security profiles and policies.
This task includes the following subtasks:
Configuring a Tenant on the Cisco VNMC
Tenants are entities (businesses, agencies, institutions, and so on) whose data and processes are hosted on VMs on the virtual data center. To provide firewall security for each tenant, the tenant must first be configured in the Cisco VNMC.
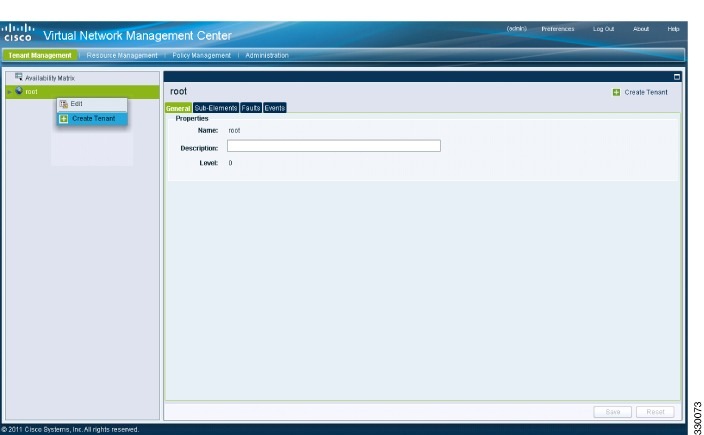
1. From the Cisco VNMC toolbar, click the Tenant Management tab.
2. In the Navigation pane directory tree, right-click on root, and from the drop-down list, choose Create Tenant.
3. In the root pane, click the General tab and do the following:
4. Click OK.
DETAILED STEPS
| Step 1 |
From the Cisco VNMC toolbar, click the Tenant Management tab.
|
| Step 2 | In the Navigation pane directory tree, right-click on root, and from the drop-down list, choose Create Tenant. |
| Step 3 | In the root pane, click the General tab and do the following: |
| Step 4 |
Click OK. Notice that the tenant you just created is listed in the left-side pane under root. |
What to Do Next
Configuring a Security Profile on the Cisco VNMC
You can configure a security profile on the Cisco VNMC.
| Step 1 |
Click the Policy Management tab in the Cisco VNMC toolbar. The Policy Management window opens.
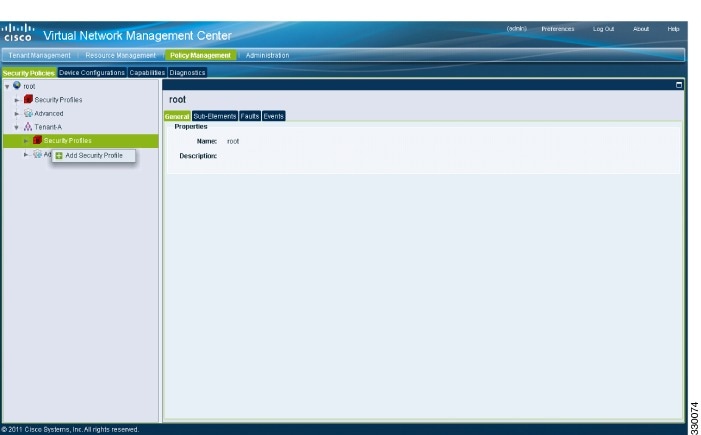
|
| Step 2 | In the Policy Management Security Policies window, from the directory path, choose . |
| Step 3 |
Right click in an empty space and choose Add Security Profile from the drop-down list. The Add Security Profile dialog box opens. 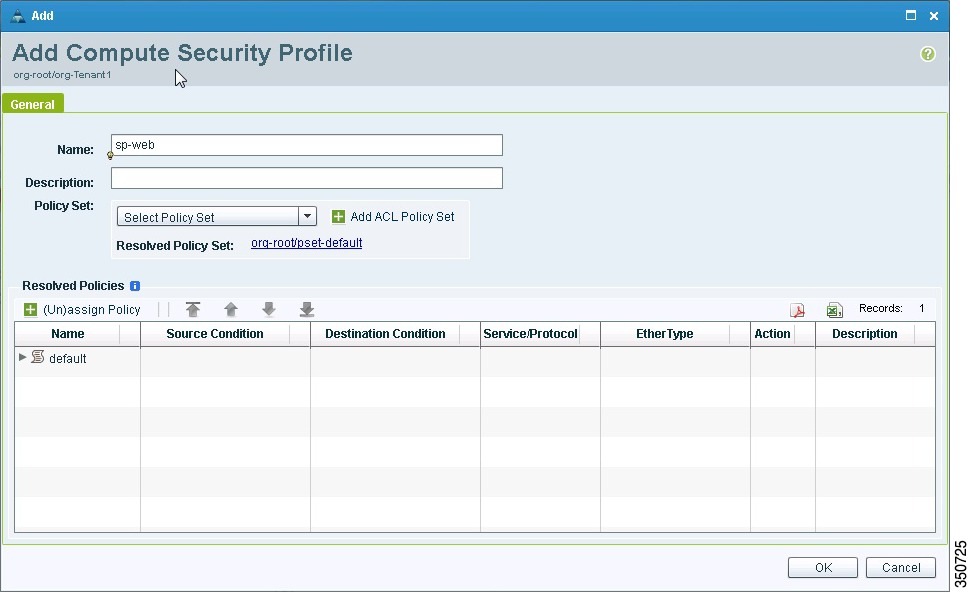
|
| Step 4 | In the Add Compute Security Profile dialog box, do the following: |
| Step 5 | Click OK |
What to Do Next
Configuring a Compute Firewall on the Cisco VNMC
The compute firewall is a logical virtual entity that contains the device profile that you can bind (assign) to a Cisco VSG VM. The device policy in the device profile is then pushed from the Cisco VNMC to the Cisco VSG. Once this is complete, the compute firewall is in the applied configuration state on the Cisco VNMC.
1. From the Cisco VNMC, choose .
2. On the left-pane directory tree, choose .
3. From the drop-down list, choose Add Compute Firewall. The Add Compute Firewall dialog box opens.
4. In the Add Compute Firewall dialog box, do the following:
5. Click OK.
DETAILED STEPS
| Step 1 |
From the Cisco VNMC, choose . The Firewall Profiles window opens. 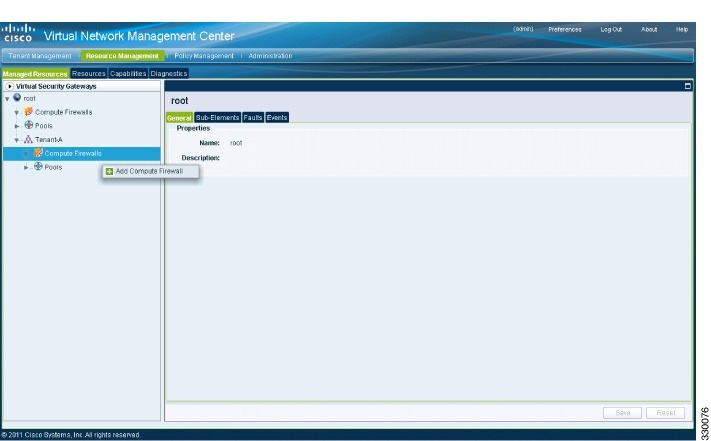
|
| Step 2 | On the left-pane directory tree, choose . |
| Step 3 |
From the drop-down list, choose Add Compute Firewall. The Add Compute Firewall dialog box opens.
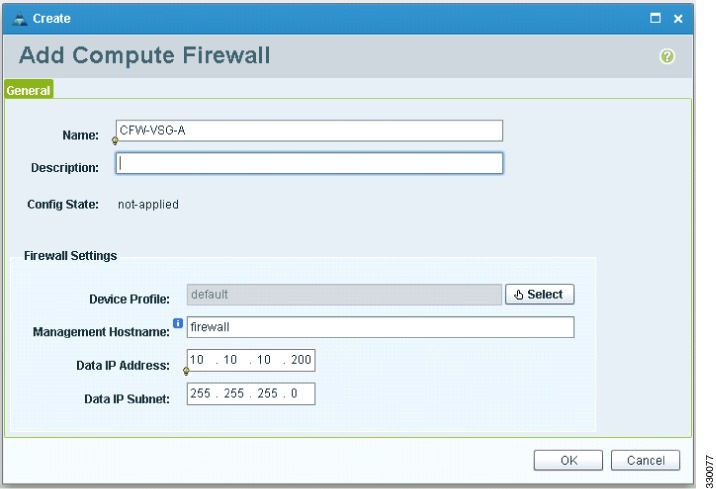
|
| Step 4 | In the Add Compute Firewall dialog box, do the following: |
| Step 5 |
Click OK. The new Compute Firewall pane displays with the information that you provided. |
Task 8: On the Cisco VNMC, Assigning the Cisco VSG to the Compute Firewall
The compute firewall is a logical virtual entity that contains the device profile that can be later bound to the device for communication with the Cisco VNMC and VSM.
| Step 1 |
Choose .
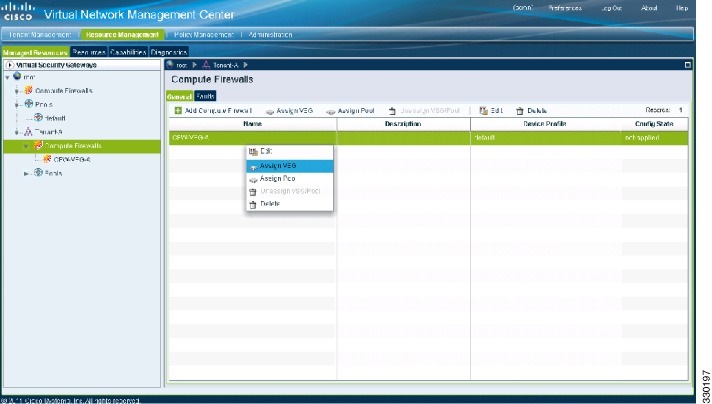
|
||
| Step 2 |
Right-click in the Compute Firewalls pane and choose Assign VSG from the drop-down list. The Assign VSG dialog box opens. 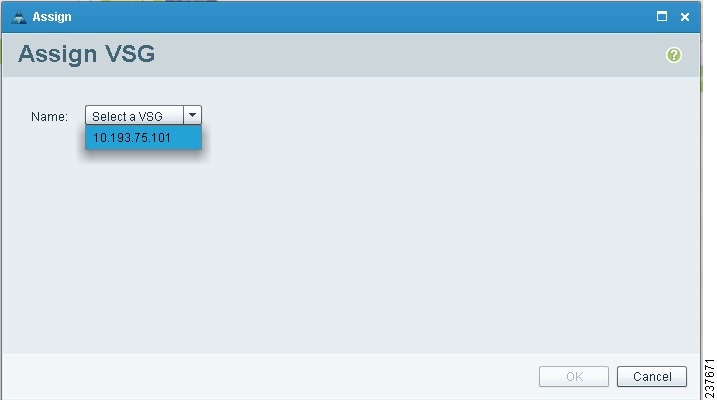
|
||
| Step 3 | From the Name drop-down list, choose the Cisco VSG IP address. | ||
| Step 4 |
Click OK.
|
Task 9: On the Cisco VNMC, Configuring a Permit-All Rule
You can configure a permit-all rule in the Cisco VNMC.
| Step 1 | Log in to the Cisco VNMC. |
| Step 2 |
Choose . The Cisco VNMC Policy Management Security Policies window opens.

|
| Step 3 | In the Cisco VNMC Policy Management Security Policies, window do the following: |
| Step 4 |
Click Add Policy. The Add Policy dialog box opens.
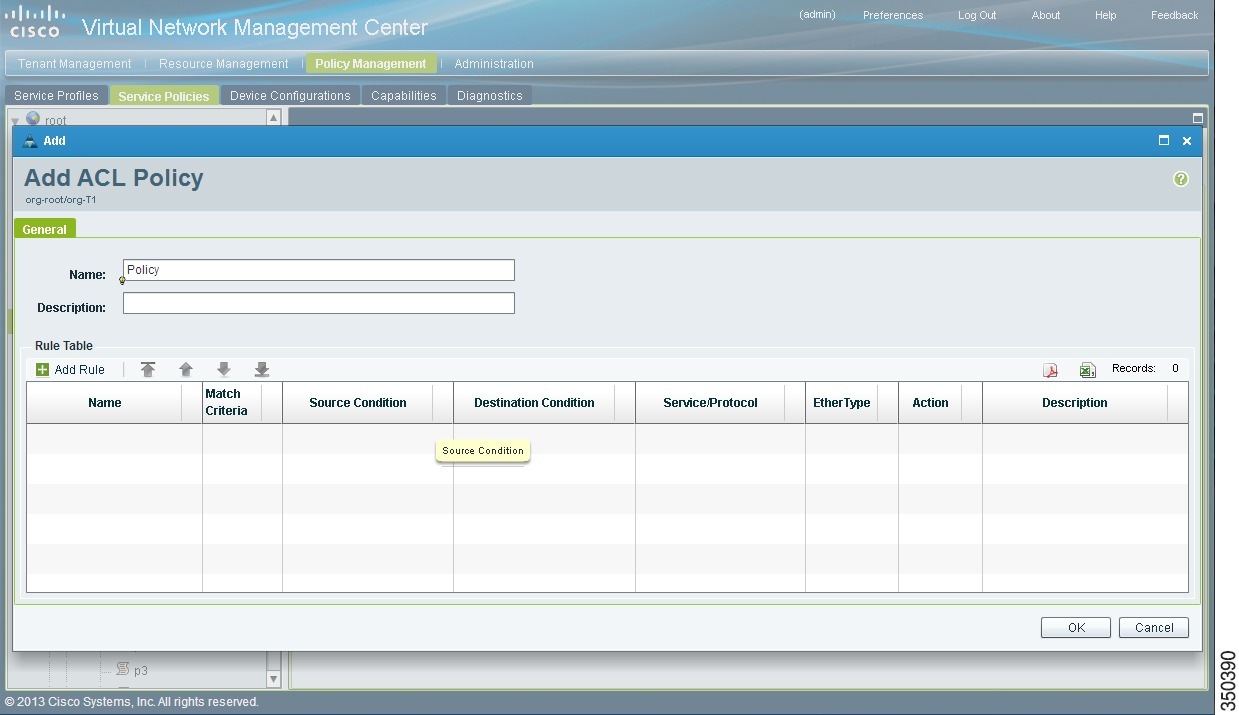
|
| Step 5 | In the Add Policy dialog box, do the following: |
| Step 6 |
In the Add Rule dialog box, do the following:
|
| Step 7 |
In the Add Policy dialog box, click OK. The newly created policy is displayed in the Assigned field. |
| Step 8 | In the Add Policy Set dialog box, click OK. |
| Step 9 | In the Service Profile window, click Save. |
Task 10: On the Cisco VSG, Verifying the Permit-All Rule
You can verify the rule presence in the Cisco VSG, by using the Cisco VSG CLI and the show commands.
vsg# show running-config | begin security security-profile SP_web@root/Tenant-A policy PS_web@root/Tenant-A custom-attribute vnsporg "root/tenant-a" security-profile default@root policy default@root custom-attribute vnsporg "root" rule Pol_web/permit-all@root/Tenant-A cond-match-criteria: match-all action permit action log rule default/default-rule@root cond-match-criteria: match-all action drop Policy PS_web@root/Tenant-A rule Pol_web/permit-all@root/Tenant-A order 101 Policy default@root rule default/default-rule@root order 2
Task 11: Enabling Logging
To enable logging follow these procedures:
Enabling Logging level 6 for Policy-Engine Logging
Logging enables you to see what traffic is going through your monitored virtual machine. This logging is helpful for verifying that you have a proper configuration and to help in troubleshooting. You can enable Logging Level 6 for policy-engine logging in a monitor session.
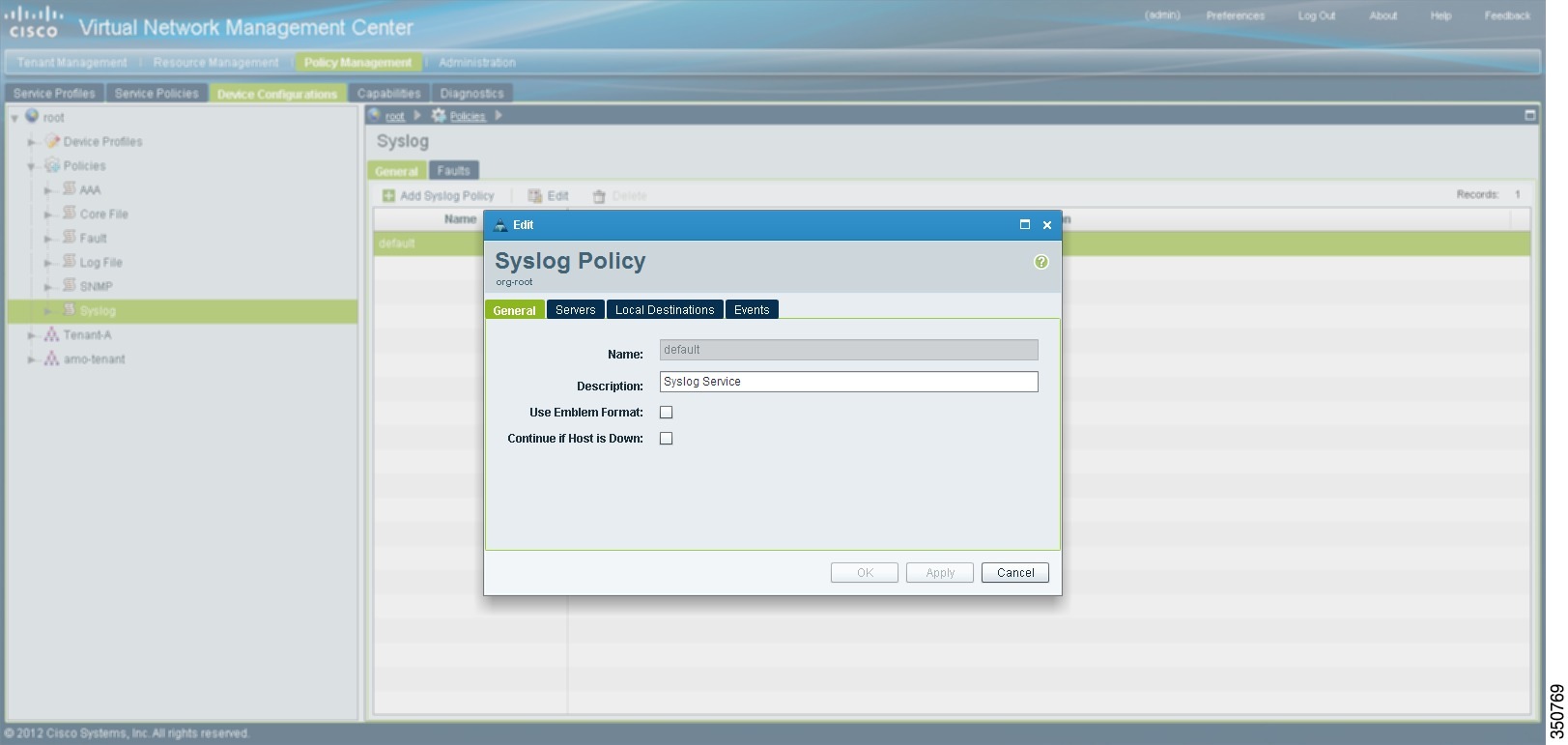
| Step 1 | Log in to the Cisco VNMC. |
| Step 2 | Choose . |
| Step 3 |
In the Device Configuration window, do the following:
|
| Step 4 |
In the Edit Syslog dialog box, do the following:
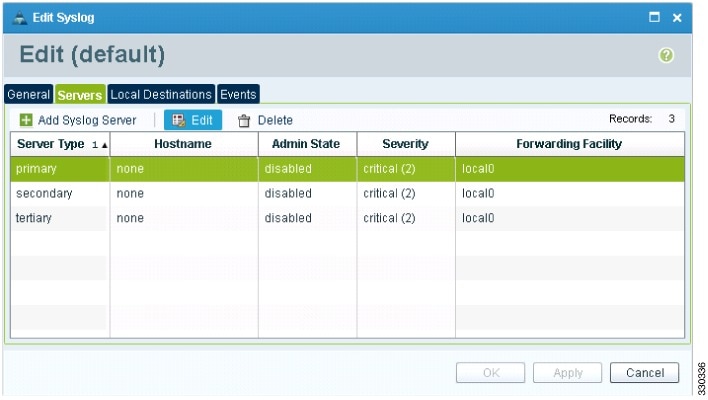
|
| Step 5 | In the Edit (Primary) Syslog Server dialog box, do the following: |
| Step 6 | Click OK. |
What to Do Next
Enabling Global Policy-Engine Logging
Logging enables you to see what traffic is going through your monitored VM. This logging is helpful for verifying that you have a proper configuration and to help in troubleshooting.
1. Log in to the Cisco VNMC.
2. In the Virtual Network Management Control window, choose . The default Device Profile window opens.
3. In the default window, do the following:
4. Click Save.
DETAILED STEPS
| Step 1 |
Log in to the Cisco VNMC.
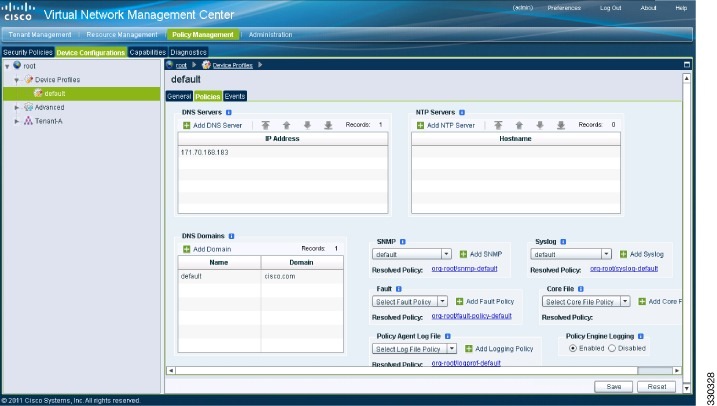
|
| Step 2 | In the Virtual Network Management Control window, choose . The default Device Profile window opens. |
| Step 3 | In the default window, do the following: |
| Step 4 | Click Save. |
Task 12: Enabling the Traffic VM Port-Profile for Firewall Protection and Verifying the Communication Between the VSM, VEM, and VSG
Make sure that you know the following:
- The server virtual machine that runs with an access port profile (for example, web server)
- The Cisco VSG data IP address (10.10.10.200) and VLAN ID (100)
- The security profile name (for example, sp-web)
- The organization (Org) name (for example, root/Tenant-A)
- The port profile that you would like to edit to enable firewall protection
- That one active port in the port-profile with vPath configuration has been set up
Enabling Traffic VM Port-Profile for Firewall Protection
You can enable a traffic VM port profile for traffic protection.
1. Enabling Traffic VM Port-Profile for Firewall Protection.
DETAILED STEPS
vsm(config)# nsm network segment VMAccess_400 vsm(config-net-seg)# member-of network segment pool vsm_NetworkSite vsm(config-net-seg)# switchport access vlan 400 vsm(config-net-seg)# import ip-pool-template VM_IP_Pool vsm(config-net-seg)# publish network-segment vsm(config-net-seg)# exit vsm(config)# port-profile type vethernet pp-webserver vsm(config-port-prof)# org root/Tenant-A vsm(config-port-prof)# vservice node VSG profile sp-web vsm(config-port-prof)# no shutdown vsm(config-port-prof)# state enabled vsm(config-port-prof)# publish port-profile vsm(config-port-prof)# exit vsm(config)# show port-profile pp-webserver |
Verifying the VSM or VEM for Cisco VSG Reachability
This example shows how to verify the communication between the VEM and the VSG:
vsm# show vservice brief
--------------------------------------------------------------------------------
License Information
--------------------------------------------------------------------------------
Type In-Use-Lic-Count UnLicensed-Mod
vsg 4
asa 0
--------------------------------------------------------------------------------
Node Information
--------------------------------------------------------------------------------
ID Name Type IP-Address Mode State Module
1 VSG_Root vsg 10.1.0.150 l3 Alive 4,5,
--------------------------------------------------------------------------------
Path Information
--------------------------------------------------------------------------------
--------------------------------------------------------------------------------
Port Information
--------------------------------------------------------------------------------
PortProfile:veth-10
Org:root/Tenant-1/VDC-1/App-1/Tier-1
Node:VSG-Root(10.1.0.150) Profile(Id):SP100(22)
Veth Mod VM-Name
6 5 vm-ub-20
7 4 vm-ub-10
A display showing the MAC-ADDR Listing and Up state verifies that the VEM can communicate with the Cisco VSG.
 Note |
In order to see the above status, one active port in the port profile with vPath configuration needs to be up. |
Checking the VM Virtual Ethernet Port for Firewall Protection
This example shows how to verify the VM Virtual Ethernet port for firewall protection:
VSM(config)# show vservice port brief vethernet 10
--------------------------------------------------------------------------------
Port Information
--------------------------------------------------------------------------------
PortProfile:veth-10
Org:root/Tenant-1/VDC-1/App-1/Tier-1
Node:VSG-Root(10.1.0.150) Profile(Id):SP100(22)
Veth Mod VM-Name
6 5 vm-ub-20
7 4 vm-ub-10
 Note |
Make sure that your VNSP ID value is greater than 1. |
Task 13: Sending Traffic Flow and on the Cisco VSG Verifying Statistics and Logs
This section includes the following topics:
Sending Traffic Flow
You can send traffic flow through the Cisco VSG to ensure that it is functioning properly.
| Step 1 |
Ensure that you have the VM (Server-VM) that is using the port profile (pp-webserver) configured for firewall protection.

|
| Step 2 |
In the Virtual Machine Properties window, do the following:
[root@]# wget http://172.31.2.92/ --2010-11-28 13:38:40-- http://172.31.2.92/ Connecting to 172.31.2.92:80... connected. HTTP request sent, awaiting response... 200 OK Length: 258 [text/html] Saving to: `index.html' 100%[=======================================================================>] 258 --.-K/s in 0s 2010-11-28 13:38:40 (16.4 MB/s) - `index.html' saved [258/258] [root]# |
| Step 3 | Check the policy-engine statistics and log on the Cisco VSG. |
What to Do Next
Go to Verifying Policy-Engine Statistics and Logs on the Cisco VSG.
Verifying Policy-Engine Statistics and Logs on the Cisco VSG
Log in to the Cisco VSG and check the policy-engine statistics and logs.
This example shows how to check the policy-engine statistics and logs:
vsg# show policy-engine stats Policy Match Stats: default@root : 0 default/default-rule@root : 0 (Drop) NOT_APPLICABLE : 0 (Drop) PS_web@root/Tenant-A : 1 pol_web/permit-all@root/Tenant-A : 1 (Log, Permit) NOT_APPLICABLE : 0 (Drop) vsg# terminal monitor vsg# 2010 Nov 28 05:41:27 firewall %POLICY_ENGINE-6-POLICY_LOOKUP_EVENT: policy=PS_web@root/Tenant-A rule=pol_web/permit-all@root/Tenant-A action=Permit direction=egress src.net.ip-address=172.31.2.91 src.net.port=48278 dst.net.ip-address=172.31.2.92 dst.net.port=80 net.protocol=6 net.ethertype=800
 Feedback
Feedback