- About Configuring TACACS+
- Information About TACACS+
- Prerequisites for TACACS+
- Guidelines and Limitations for TACACS+
- Configuring TACACS+
- TACACS+ Server Configuration Process
- Enabling TACACS+
- Configuring TACACS+ Server Hosts
- Configuring TACACS+ Global Preshared Keys
- Configuring TACACS+ Server Preshared Keys
- Configuring TACACS+ Server Groups
- Configuring the Global Source Interface for TACACS+ Server Groups
- Specifying a TACACS+ Server at Login
- Configuring AAA Authorization on TACACS+ Servers
- Configuring Command Authorization on TACACS+ Servers
- Testing Command Authorization on TACACS+ Servers
- Enabling and Disabling Command Authorization Verification
- Configuring Privilege Level Support for Authorization on TACACS+ Servers
- Permitting or Denying Commands for Users of Privilege Roles
- Configuring the Global TACACS+ Timeout Interval
- Configuring the Timeout Interval for a Server
- Configuring TCP Ports
- Configuring Periodic TACACS+ Server Monitoring
- Configuring the Dead-Time Interval
- Manually Monitoring TACACS+ Servers or Groups
- Disabling TACACS+
- TACACS+ Server Configuration Process
- Displaying TACACS+ Statistics
- Verifying the TACACS+ Configuration
- Configuration Examples for TACACS+
- Default Settings for TACACS+
Configuring TACACS+
This chapter contains the following sections:
About Configuring TACACS+
Information About TACACS+
The Terminal Access Controller Access Control System Plus (TACACS+) security protocol provides centralized validation of users attempting to gain access to a Cisco Nexus device. TACACS+ services are maintained in a database on a TACACS+ daemon typically running on a UNIX or Windows NT workstation. You must have access to and must configure a TACACS+ server before the configured TACACS+ features on your Cisco Nexus device are available.
TACACS+ provides for separate authentication, authorization, and accounting facilities. TACACS+ allows for a single access control server (the TACACS+ daemon) to provide each service (authentication, authorization, and accounting) independently. Each service is associated with its own database to take advantage of other services available on that server or on the network, depending on the capabilities of the daemon.
The TACACS+ client/server protocol uses TCP (TCP port 49) for transport requirements. The Cisco Nexus device provides centralized authentication using the TACACS+ protocol.
- TACACS+ Advantages
- User Login with TACACS+
- Default TACACS+ Server Encryption Type and Preshared Key
- Command Authorization Support for TACACS+ Servers
- TACACS+ Server Monitoring
TACACS+ Advantages
TACACS+ has the following advantages over RADIUS authentication:
- Provides independent AAA facilities. For example, the Cisco Nexus device can authorize access without authenticating.
- Uses the TCP transport protocol to send data between the AAA client and server, making reliable transfers with a connection-oriented protocol.
- Encrypts the entire protocol payload between the switch and the AAA server to ensure higher data confidentiality. The RADIUS protocol only encrypts passwords.
User Login with TACACS+
When a user attempts a Password Authentication Protocol (PAP) login to a Cisco Nexus device using TACACS+, the following actions occur:
-
When the Cisco Nexus device establishes a connection, it contacts the TACACS+ daemon to obtain the username and password.

Note
TACACS+ allows an arbitrary conversation between the daemon and the user until the daemon receives enough information to authenticate the user. This action is usually done by prompting for a username and password combination, but may include prompts for other items, such as the user’s mother’s maiden name.
-
The Cisco Nexus device receives one of the following responses from the TACACS+ daemon:
- ACCEPT—User authentication succeeds and service begins. If the Cisco Nexus device requires user authorization, authorization begins.
- REJECT—User authentication failed. The TACACS+ daemon either denies further access to the user or prompts the user to retry the login sequence.
- ERROR—An error occurred at some time during authentication dither at the daemon or in the network connection between the daemon and the Cisco Nexus device. If the Cisco Nexus deviceh receives an ERROR response, the switch tries to use an alternative method for authenticating the user.
- If TACACS+ authorization is required, the Cisco Nexus device again contacts the TACACS+ daemon and it returns an ACCEPT or REJECT authorization response. An ACCEPT response contains attributes that are used to direct the EXEC or NETWORK session for that user and determines the services that the user can access.
Services include the following:
Default TACACS+ Server Encryption Type and Preshared Key
You must configure the TACACS+ that is preshared key to authenticate the switch to the TACACS+ server. A preshared key is a secret text string shared between the Cisco Nexus device and the TACACS+ server host. The length of the key is restricted to 63 characters and can include any printable ASCII characters (white spaces are not allowed). You can configure a global preshared secret key for all TACACS+ server configurations on the Cisco Nexus deviceh to use.
You can override the global preshared key assignment by using the key option when configuring an individual TACACS+ server.
Command Authorization Support for TACACS+ Servers
By default, command authorization is done against a local database in the Cisco NX-OS software when an authenticated user enters a command at the command-line interface (CLI). You can also verify authorized commands for authenticated users using TACACS+.
TACACS+ Server Monitoring
An unresponsive TACACS+ server can delay the processing of AAA requests. A Cisco Nexus device can periodically monitor an TACACS+ server to check whether it is responding (or alive) to save time in processing AAA requests. The Cisco Nexus device marks unresponsive TACACS+ servers as dead and does not send AAA requests to any dead TACACS+ servers. The Cisco Nexus device periodically monitors dead TACACS+ servers and brings them to the alive state once they are responding. This process verifies that a TACACS+ server is in a working state before real AAA requests are sent to the server. Whenever an TACACS+ server changes to the dead or alive state, a Simple Network Management Protocol (SNMP) trap is generated and the Cisco Nexus device displays an error message that a failure is taking place before it can impact performance.
The following figure shows the different TACACS+ server states:
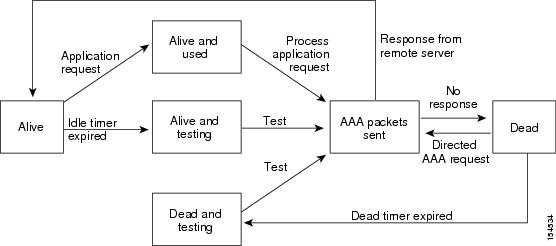
 Note |
The monitoring interval for alive servers and dead servers are different and can be configured by the user. The TACACS+ server monitoring is performed by sending a test authentication request to the TACACS+ server. |
Prerequisites for TACACS+
TACACS+ has the following prerequisites:
Guidelines and Limitations for TACACS+
TACACS+ has the following configuration guidelines and limitations:
Configuring TACACS+
TACACS+ Server Configuration Process
This section describes how to configure TACACS+ servers.
Enabling TACACS+
Although by default, the TACACS+ feature is disabled on the Cisco Nexus device. You can enable the TACACS+ feature to access the configuration and verification commands for authentication, perform this task:
Configuring TACACS+ Server Hosts
To access a remote TACACS+ server, you must configure the IPv4 address or the hostname for the TACACS+ server on the Cisco Nexus device. All TACACS+ server hosts are added to the default TACACS+ server group.You can configure up to 64 TACACS+ servers.
If a preshared key is not configured for a configured TACACS+ server, a warning message is issued if a global key is not configured. If a TACACS+ server key is not configured, the global key (if configured) is used for that server.
Before you configure TACACS+ server hosts, you should do the following:
You can delete a TACACS+ server host from a server group.
Configuring TACACS+ Global Preshared Keys
You can configure preshared keys at the global level for all servers used by the Cisco Nexus device. A preshared key is a shared secret text string between the Cisco Nexus device and the TACACS+ server hosts.
Before you configure preshared keys, you should do the following:
The following example shows how to configure global preshared keys:
switch# configure terminal switch(config)# tacacs-server key 0 QsEfThUkO switch(config)# exit switch# show tacacs-server switch# copy running-config startup-config
Configuring TACACS+ Server Preshared Keys
You can configure preshared keys for a TACACS+ server. A preshared key is a shared secret text string between the Cisco Nexus device and the TACACS+ server host.
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
||
| Step 2 | switch(config)# tacacs-server host {ipv4-address | host-name} key [0 | 7] key-value |
Specifies a preshared key for a specific TACACS+ server. You can specify a clear text ( 0 ) or encrypted ( 7 ) preshared key. The default format is clear text. The maximum length is 63 characters. This preshared key is used instead of the global preshared key. |
||
| Step 3 | switch(config)# exit |
Exits configuration mode. |
||
| Step 4 | switch# show tacacs-server |
(Optional) Displays the TACACS+ server configuration.
|
||
| Step 5 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
The following example shows how to configure the TACACS+ preshared keys:
switch# configure terminal switch(config)# tacacs-server host 10.10.1.1 key 0 PlIjUhYg switch(config)# exit switch# show tacacs-server switch# copy running-config startup-config
Configuring TACACS+ Server Groups
You can specify one or more remote AAA servers to authenticate users using server groups. All members of a group must belong to the TACACS+ protocol. The servers are tried in the same order in which you configure them.
You can configure these server groups at any time but they only take effect when you apply them to an AAA service.
You must use the feature tacacs+ command to enable TACACS+ before you configure TACACS+.
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
||
| Step 2 | switch(config)# aaa group server tacacs+ group-name |
Creates a TACACS+ server group and enters the TACACS+ server group configuration mode for that group. |
||
| Step 3 | switch(config)# tacacs-server host {ipv4-address | host-name} key [0 | 7] key-value |
Specifies a preshared key for a specific TACACS+ server. You can specify a clear text ( 0 ) or encrypted ( 7 ) preshared key. The default format is clear text. The maximum length is 63 characters. This preshared key is used instead of the global preshared key. |
||
| Step 4 | switch(config-tacacs+)# deadtime minutes |
(Optional) Configures the monitoring dead time. The default is 0 minutes. The range is from 0 through 1440.
|
||
| Step 5 | switch(config-tacacs+)# source-interface interface Example: switch(config-tacacs+)# source-interface mgmt 0 |
(Optional) Assigns a source interface for a specific TACACS+ server group. The supported interface types are management and VLAN.
|
||
| Step 6 | switch(config-tacacs+)# exit |
Exits configuration mode. |
||
| Step 7 | switch(config)# show tacacs-server groups |
(Optional) Displays the TACACS+ server group configuration. |
||
| Step 8 | switch(config)# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
The following example shows how to configure a TACACS+ server group:
switch# configure terminal
switch(config)# aaa group server tacacs+ TacServer
switch(config-tacacs+)# server 10.10.2.2
switch(config-tacacs+)# deadtime 30
switch(config-tacacs+)# exit
switch(config)# show tacacs-server groups
switch(config)# copy running-config startup-config
Configuring the Global Source Interface for TACACS+ Server Groups
You can configure a global source interface for TACACS+ server groups to use when accessing TACACS+ servers. You can also configure a different source interface for a specific TACACS+ server group.
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure terminal Example: switch# configure terminal switch(config) |
Enters global configuration mode. |
| Step 2 | ip tacacs source-interface interface Example: switch(config)# ip tacacs source-interface mgmt 0 |
Configures the global source interface for all TACACS+ server groups configured on the device. The source interface can be the management or the VLAN interface. |
| Step 3 | exit Example: switch(config)# exit switch# |
Exits configuration mode. |
| Step 4 | show tacacs-server Example: switch# show tacacs-server |
(Optional) Displays the TACACS+ server configuration information. |
| Step 5 | copy running-config startup config Example: switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Specifying a TACACS+ Server at Login
You can configure the switch to allow the user to specify which TACACS+ server to send the authenticate request by enabling the directed-request option. By default, a Cisco Nexus device forwards an authentication request based on the default AAA authentication method. If you enable this option, the user can log in as username@hostname, where hostname is the name of a configured RADIUS server.
 Note |
User specified logins are only supported for Telnet sessions. |
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
| Step 2 | switch(config)# tacacs-server directed-request |
Allows users to specify a TACACS+ server to send the authentication request when logging in. The default is disabled. |
| Step 3 | switch(config)# exit |
Exits configuration mode. |
| Step 4 | switch# show tacacs-server directed-request |
(Optional) Displays the TACACS+ directed request configuration. |
| Step 5 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Configuring AAA Authorization on TACACS+ Servers
You can configure the default AAA authorization method for TACACS+ servers.
Enable TACACS+.
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure terminal Example: switch# configure terminal switch(config)# |
Enters global configuration mode. |
| Step 2 | aaa authorization ssh-certificate default {group group-list [none] | local | none} Example: switch(config)# aaa authorization ssh-certificate default group TACACSServer1 TACACSServer2 |
Configures the default AAA authorization method for the TACACS+ servers. The ssh-certificate keyword configures TACACS+ or local authorization with certificate authentication. The default authorization is local authorization, which is the list of authorized commands for the user’s assigned role. The group-list argument consists of a space-delimited list of TACACS+ server group names. Servers belonging to this group are contacted for AAA authorization. The local method uses the local database for authorization, and the none method specifies that no AAA authorization be used. |
| Step 3 | exit Example: switch(config)# exit switch# |
Exits global configuration mode. |
| Step 4 | show aaa authorization [all] Example: switch# show aaa authorization |
(Optional) Displays the AAA authorization configuration. The all keyword displays the default values. |
| Step 5 | copy running-config startup-config Example: switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Configuring Command Authorization on TACACS+ Servers
You can configure authorization for commands on TACACS+ servers. Command authorization disables user role-based authorization control (RBAC), including the default roles.
 Note |
By default, context-sensitive help and command tab completion show only the commands that are supported for a user as defined by the assigned roles. When you enable command authorization, the Cisco NX-OS software displays all commands in the context sensitive help and in tab completion, regardless of the role assigned to the user. |
Enable TACACS+.
Configure TACACS host and server groups before configuring AAA command authorization.
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure terminal Example: switch# configure terminal switch(config)# |
Enters global configuration mode. |
| Step 2 | aaa authorization {commands | config-commands} default [group group-list [local] | local] Example: switch(config)# aaa authorization commands default group TacGroup |
Configures the default authorization method for commands for all roles. The commands keyword configures authorization sources for all EXEC commands, and the config-commands keyword configures authorization sources for all configuration commands. The default authorization for all commands is local authorization, which is the list of authorized commands for the user's assigned role. The group-list argument consists of a space-delimited list of TACACS+ server group names. Servers that belong to this group are contacted for command authorization. The local method uses the local role-based database for authorization. The local method is used only if all the configured server groups fail to respond and you have configured local as the fallback method. The default method is local. If you have not configured a fallback method after the TACACS+ server group method, authorization fails if all server groups fail to respond. |
| Step 3 | exit Example: switch(config)# exit switch# |
Exits global configuration mode. |
| Step 4 | show aaa authorization [all] Example: switch(config)# show aaa authorization |
(Optional) Displays the AAA authorization configuration. The all keyword displays the default values. |
| Step 5 | copy running-config startup-config Example: switch(config)# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Testing Command Authorization on TACACS+ Servers
You can test the command authorization for a user on the TACACS+ servers.
 Note |
You must send correct commands for authorization or the results might not be reliable. |
Enable TACACS+.
Ensure that you have configured command authorization for the TACACS+ servers.
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | test aaa authorization command-type {commands | config-commands} user username command command-string Example: switch# test aaa authorization command-type commands user TestUser command reload |
Tests a user's authorization for a command on the TACACS+ servers. The commands keyword specifies only EXEC commands and the config-commands keyword specifies only configuration commands.
|
Enabling and Disabling Command Authorization Verification
You can enable and disable command authorization verificaiton on the command-line interface (CLI) for the default user session or for another username.
 Note |
The commands do not execute when you enable authorization verification. |
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | terminal verify-only [username username] Example: switch# terminal verify-only |
Enables command authorization verification. After you enter this command, the Cisco NX-OS software indicates whether the commands you enter are authorized or not. |
| Step 2 | terminal no verify-only [username username] Example: switch# terminal no verify-only |
Disables command authorization verification. |
Configuring Privilege Level Support for Authorization on TACACS+ Servers
You can configure privilege level support for authorization on TACACS+ servers.
Unlike Cisco IOS devices, which use privilege levels to determine authorization, Cisco NX-OS devices use role-based access control (RBAC). To enable both types of devices to be administered by the same TACACS+ servers, you can map the privilege levels configured on TACACS+ servers to user roles configured on Cisco NX-OS devices.
When a user authenticates with a TACACS+ server, the privilege level is obtained and used to form a local user role name of the format “priv-n,” where n is the privilege level. The user assumes the permissions of this local role. Sixteen privilege levels, which map directly to corresponding user roles, are available. The following table shows the user role permissions that correspond to each privilege level.
| Privilege Level | User Role Permissions |
|---|---|
| 15 | network-admin permissions |
| 13 - 1 | |
| 0 | Permission to execute show commands and exec commands (such as ping, trace, and ssh). |
 Note |
When the feature privilege command is enabled, privilege roles inherit the permissions of lower level privilege roles. |
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: switch# configure terminal switch(config)# |
Enters global configuration mode. |
||
| Step 2 | [no] feature privilege Example: switch(config)# feature privilege |
Enables or disables the cumulative privilege of roles. Users can see the enable command only if this feature is enabled. The default is disabled. |
||
| Step 3 | [no] enable secret [0 | 5] password [priv-lvl priv-lvl | all] Example: switch(config)# enable secret 5 def456 priv-lvl 15 |
Enables or disables a secret password for a specific privilege level. Users are prompted to enter the correct password upon each privilege level escalation. The default is disabled. You can enter 0 to specify that the password is in clear text or 5 to specify that the password is in encrypted format. The password argument can be up to 64 alphanumeric characters. The priv-lvl argument is from 1 to 15.
|
||
| Step 4 | [no] username username priv-lvl n Example: switch(config)# username user2 priv-lvl 15 |
Enables or disables a user to use privilege levels for authorization. The default is disabled. The priv-lvl keyword specifies the privilege level to which the user is assigned. There is no default privilege level. Privilege levels 0 to 15 (priv-lvl 0 to priv-lvl 15) map to user roles priv-0 to priv-15. |
||
| Step 5 | show privilege Example: switch(config)# show privilege |
(Optional) Displays the username, current privilege level, and status of cumulative privilege support. |
||
| Step 6 | copy running-config startup-config Example: switch(config)# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
||
| Step 7 | exit Example: switch(config)# exit switch# |
Exits global configuration mode. |
||
| Step 8 | enable level Example: switch# enable 15 |
Enables a user to move to a higher privilege level. This command prompts for the secret password. The level argument specifies the privilege level to which the user is granted access. The only available level is 15. |
Permitting or Denying Commands for Users of Privilege Roles
As a network administrator, you can modify the privilege roles to permit users to execute specific commands or to prevent users from running those commands.
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: switch# configure terminal switch(config)# |
Enters global configuration mode. |
||
| Step 2 | [no] role name priv-n Example: switch(config)# role name priv-5 switch(config-role)# |
Enables or disables a privilege role and enters role configuration mode. The n argument specifies the privilege level and is a number between 0 and 13. |
||
| Step 3 | rule number {deny | permit} command command-string Example: switch(config-role)# rule 2 permit command pwd |
Configures a command rule for users of privilege roles. These rules permit or deny users to execute specific commands. You can configure up to 256 rules for each role. The rule number determines the order in which the rules are applied. Rules are applied in descending order. For example, if a role has three rules, rule 3 is applied before rule 2, which is applied before rule 1. The command-string argument can contain spaces.
|
||
| Step 4 | exit Example: switch(config-role)# exit switch(config)# |
Exits role configuration mode. |
||
| Step 5 | copy running-config startup-config Example: switch(config)# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Configuring the Global TACACS+ Timeout Interval
You can set a global timeout interval that the Cisco Nexus device waits for responses from all TACACS+ servers before declaring a timeout failure. The timeout interval determines how long the switch waits for responses from TACACS+ servers before declaring a timeout failure.
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
| Step 2 | switch(config)# tacacs-server timeout seconds |
Specifies the timeout interval for TACACS+ servers. The default timeout interval is 5 second and the range is from 1 to 60 seconds. |
| Step 3 | switch(config)# exit |
Exits configuration mode. |
| Step 4 | switch# show tacacs-server |
(Optional) Displays the TACACS+ server configuration. |
| Step 5 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Configuring the Timeout Interval for a Server
You can set a timeout interval that the Cisco Nexus device waits for responses from a TACACS+ server before declaring a timeout failure. The timeout interval determines how long the switch waits for responses from a TACACS+ server before declaring a timeout failure.
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
||
| Step 2 | switch(config)# switch(config)# tacacs-server host {ipv4-address | host-name} timeout seconds |
Specifies the timeout interval for a specific server. The default is the global value.
|
||
| Step 3 | switch(config)# exit |
Exits configuration mode. |
||
| Step 4 | switch# show tacacs-server |
(Optional) Displays the TACACS+ server configuration. |
||
| Step 5 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Configuring TCP Ports
You can configure another TCP port for the TACACS+ servers if there are conflicts with another application. By default, the Cisco Nexus device uses port 49 for all TACACS+ requests.
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
| Step 2 | switch(config)# tacacs-server host {ipv4-address | host-name} port tcp-port |
Specifies the UDP port to use for TACACS+ accounting messages.The default TCP port is 49. The range is from 1 to 65535. |
| Step 3 | switch(config)# exit |
Exits configuration mode. |
| Step 4 | switch# show tacacs-server |
(Optional) Displays the TACACS+ server configuration. |
| Step 5 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
The following example shows how to configure TCP ports:
switch# configure terminal switch(config)# tacacs-server host 10.10.1.1 port 2 switch(config)# exit switch# show tacacs-server switch# copy running-config startup-config
Configuring Periodic TACACS+ Server Monitoring
You can monitor the availability of TACACS+ servers. These parameters include the username and password to use for the server and an idle timer. The idle timer specifies the interval in which a TACACS+ server receives no requests before the Cisco Nexus device sends out a test packet.You can configure this option to test servers periodically, or you can run a one-time only test.
 Note |
To protect network security, we recommend that you use a username that is not the same as an existing username in the TACACS+ database. |
The test idle timer specifies the interval in which a TACACS+ server receives no requests before the Cisco Nexus device sends out a test packet.
 Note |
The default idle timer value is 0 minutes. When the idle time interval is 0 minutes, periodic TACACS+ server monitoring is not performed. |
To configure periodic TACACS+ server monitoring, perform this task:
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
||
| Step 2 | switch(config)# tacacs-server host {ipv4-address | host-name} test {idle-time minutes | password password [idle-time minutes] | username name [password password [idle-time minutes]]} |
Specifies parameters for server monitoring. The default username is test and the default password is test. The default value for the idle timer is 0 minutes and the valid range is from 0 to 1440 minutes.
|
||
| Step 3 | switch(config)# tacacs-server dead-time minutes |
Specifies the number minutes before the Cisco Nexus device checks a TACACS+ server that was previously unresponsive. The default value is 0 minutes and the valid range is 0 to 1440 minutes. |
||
| Step 4 | switch(config)# exit |
Exits configuration mode. |
||
| Step 5 | switch# show tacacs-server |
(Optional) Displays the TACACS+ server configuration. |
||
| Step 6 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
The following example shows how to configure periodic TACACS+ server monitoring:
switch# configure terminal switch(config)# tacacs-server host 10.10.1.1 test username user1 password Ur2Gd2BH idle-time 3 switch(config)# tacacs-server dead-time 5 switch(config)# exit switch# show tacacs-server switch# copy running-config startup-config
Configuring the Dead-Time Interval
You can configure the dead-time interval for all TACACS+ servers. The dead-time interval specifies the time that the Cisco Nexus device waits, after declaring a TACACS+ server is dead, before sending out a test packet to determine if the server is now alive.
 Note |
When the dead-time interval is 0 minutes, TACACS+ servers are not marked as dead even if they are not responding. You can configure the dead-time interval per group. |
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
| Step 2 | switch(config)# tacacs-server deadtime minutes |
Configures the global dead-time interval. The default value is 0 minutes. The range is from 1 to 1440 minutes. |
| Step 3 | switch(config)# exit |
Exits configuration mode. |
| Step 4 | switch# show tacacs-server |
(Optional) Displays the TACACS+ server configuration. |
| Step 5 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Manually Monitoring TACACS+ Servers or Groups
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# test aaa server tacacs+ {ipv4-address | host-name} [vrf vrf-name] username password |
Sends a test message to a TACACS+ server to confirm availability. |
| Step 2 | switch# test aaa group group-name username password |
Sends a test message to a TACACS+ server group to confirm availability. |
The following example shows how to manually issue a test message:
switch# test aaa server tacacs+ 10.10.1.1 user1 Ur2Gd2BH switch# test aaa group TacGroup user2 As3He3CI
Disabling TACACS+
You can disable TACACS+.
 Caution |
When you disable TACACS+, all related configurations are automatically discarded. |
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# configure terminal |
Enters configuration mode. |
| Step 2 | switch(config)# no feature tacacs+ |
Disables TACACS+. |
| Step 3 | switch(config)# exit |
Exits configuration mode. |
| Step 4 | switch# copy running-config startup-config |
(Optional) Copies the running configuration to the startup configuration. |
Displaying TACACS+ Statistics
To display the statistics, the switch maintains for TACACS+ activity, perform this task:
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# show tacacs-server statistics {hostname | ipv4-address} |
Displays the TACACS+ statistics. |
For detailed information about the fields in the output from this command, see the Command Reference for your Nexus switch.
Verifying the TACACS+ Configuration
To display TACACS+ configuration information, perform one of the following tasks:
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | switch# show tacacs+ {status | pending | pending-diff} |
Displays the TACACS+ Cisco Fabric Services distribution status and other details. |
| Step 2 | switch# show running-config tacacs [all] |
Displays the TACACS+ configuration in the running configuration. |
| Step 3 | switch# show startup-config tacacs |
Displays the TACACS+ configuration in the startup configuration. |
| Step 4 | switch# show tacacs-serve [host-name | ipv4-address] [directed-request | groups | sorted | statistics] |
Displays all configured TACACS+ server parameters. |
Configuration Examples for TACACS+
The following example shows how to configure TACACS+:
switch# configure terminal switch(config)# feature tacacs+ switch(config)# tacacs-server key 7 "ToIkLhPpG" switch(config)# tacacs-server host 10.10.2.2 key 7 "ShMoMhTl" switch(config)# aaa group server tacacs+ TacServer switch(config-tacacs+)# server 10.10.2.2 switch(config-tacacs+)# use-vrf management
The following example shows how to enable tacacs+ and how to configure the tacacs+ server preshared keys to specify remote AAA servers to authenticate server group TacServer1:
switch# config t switch(config)# feature tacacs+ switch(config)# tacacs-server key 7 "ikvhw10" switch(config)# tacacs-server host 1.1.1.1 switch(config)# tacacs-server host 1.1.1.2 switch(config)# aaa group server tacacs+ TacServer1 switch(config-tacacs+)# server 1.1.1.1 switch(config-tacacs+)# server 1.1.1.2
Default Settings for TACACS+
The following table lists the default settings for TACACS+ parameters.
| Parameters |
Default |
|---|---|
| TACACS+ |
Disabled |
| Dead-time interval |
0 minutes |
| Timeout interval |
5 seconds |
| Idle timer interval |
0 minutes |
| Periodic server monitoring username |
test |
| Periodic server monitoring password |
test |
 Feedback
Feedback