- Preface
- Chapter 1: CPwE IDMZ Overview
- Chapter 2: System Design Considerations
- Chapter 3: Configuring the Infrastructure
- Chapter 4: CPwE IDMZ Troubleshooting
- Appendix A: References
- Appendix B: Test Hardware and Software
- Appendix C: Acronyms and Initialisms
- Appendix D: About the Cisco Validated Design (CVD) Program
CPwE IDMZ Overview
CPwE IDMZ Introduction
The prevailing trend in Industrial Automation and Control System (IACS) networking is the convergence of technology, specifically IACS operational technology (OT) with information technology (IT). Converged Plantwide Ethernet (CPwE) helps to enable IACS network and security technology convergence, including OT-IT persona convergence, by using standard Ethernet, Internet Protocol (IP), network services, security services, and EtherNet/IP. A reliable and secure converged plant-wide or site-wide IACS architecture helps to enable the Industrial Internet of Things (IIoT).
IIoT helps offer the promise of business benefits by using innovative technology such as mobility, collaboration, analytics and cloud-based services. The challenge for industrial operations is to develop a balanced security stance to take advantage of IIoT innovation while maintaining the integrity of industrial security best practices. Business practices, corporate standards, security policies and procedures, application requirements, industry security standards, regulatory compliance, risk management policies, and overall tolerance to risk are all key factors in determining the appropriate security stance.
Many organizations and standards bodies recommend segmenting business system networks from plant-wide and site-wide networks by using an Industrial Demilitarized Zone (IDMZ). The IDMZ exists as a separate network in a level between the Industrial and Enterprise Zones, commonly referred to as Level 3.5. An IDMZ environment consists of numerous infrastructure devices, including firewalls, virtual private network (VPN) servers, IACS application mirrors, remote gateway services and reverse proxy servers, in addition to network infrastructure devices such as routers, switches and virtualized services. CPwE IDMZ details considerations to help with the successful design and implementation of an IDMZ to securely share IACS data between the business systems within the Enterprise Zone and industrial operations within the Industrial Zone.
CPwE Overview
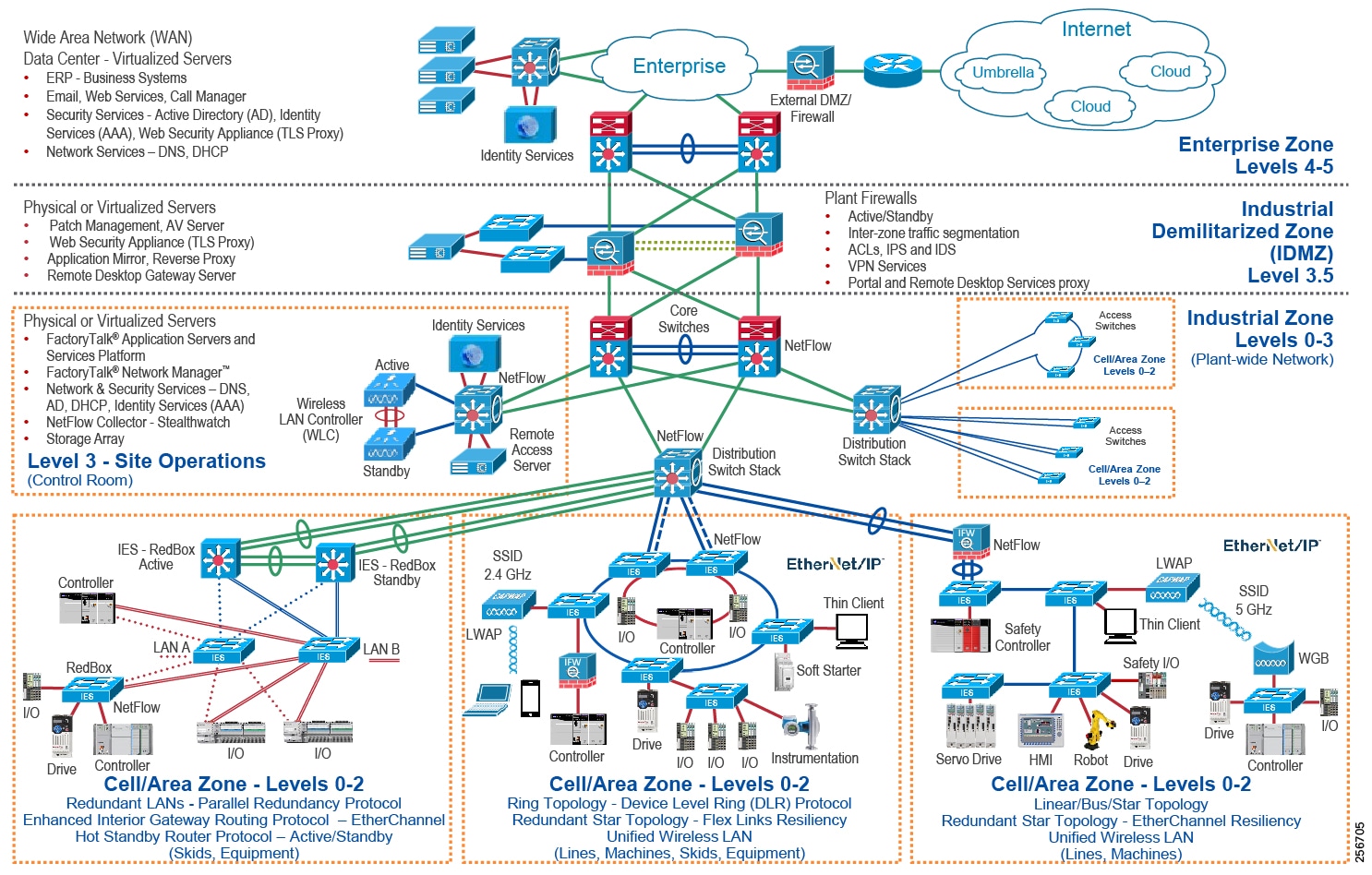
CPwE is the underlying architecture that provides standard network and security services for control and information disciplines, devices, and equipment found in modern IACS applications. The CPwE architectures (Figure 1-1) were architected, tested, and validated to provide design and implementation guidance, test results, and documented configuration settings. This can help to achieve the real-time communication, reliability, scalability, security, and resiliency requirements of modern IACS applications. The content and key tenets of CPwE are relevant to both OT and IT disciplines.
- Smart IIoT devices-Controllers, I/O, drives, instrumentation, actuators, analytics, and a single IIoT network technology (EtherNet/IP), facilitating both technology coexistence and IACS device interoperability, which helps to enable the choice of best-in-class IACS devices
- Zoning (segmentation)-Smaller connected LANs, functional areas, and security groups
- Managed infrastructure-Managed Allen-Bradley® Stratix® industrial Ethernet switches (IES), Cisco Catalyst® distribution/core switches, FactoryTalk® Network Manager™ software, and Stratix® industrial firewalls
- Resiliency-Robust physical layer and resilient or redundant topologies with resiliency protocols
- Time-critical data-Data prioritization and time synchronization via CIP Sync® and IEEE-1588 Precision Time Protocol (PTP)
- Wireless-Unified wireless LAN (WLAN) to enable mobility for personnel and equipment
- Holistic defense-in-depth security-Multiple layers of diverse technologies for threat detection and prevention, implemented by different persona (for example, OT and IT) and applied at different levels of the plant-wide or site-wide IACS architecture
- Convergence-ready-Seamless plant-wide or site-wide integration by trusted partner application
CPwE Industrial Security Framework Overview
No single product, technology, methodology or strategy can fully secure plant-wide or site-wide architectures. Protecting IACS assets requires a holistic defense-in-depth security approach that addresses internal and external security threats. This approach uses multiple layers of defense (administrative, technical, and physical) using diverse technologies for threat detection and prevention, implemented by different personas, and applied at separate levels of the IACS architecture (Figure 1-2).
- Control System Engineers (highlighted in tan) - IACS asset hardening (for example, physical and electronic), IACS application hardening (for example, CIP SecurityTM with FactoryTalk® Policy Manager), infrastructure device hardening (for example, port security), network monitoring and change management (for example, FactoryTalk Network Manager), cybersecurity visibility and threat detection (for example, Cyber Vision), network segmentation (trust zoning), industrial firewalls (with deep packet inspection) at the IACS application edge, and IACS policy-based application authentication, authorization, and accounting (AAA).
- Control System Engineers in collaboration with IT Network Engineers (highlighted in blue) - Computer hardening (OS patching), network device hardening (for example, access control, and resiliency), network monitoring and inspection, and wired and wireless LAN access policies.
- IT Security Architects in collaboration with Control Systems Engineers (highlighted in purple) - Identity and Mobility Services (wired and wireless), network monitoring with anomaly detection, Active Directory (AD), Remote Access Servers, plant/site firewalls, Industrial Demilitarized Zone (IDMZ) design best practices, data brokers (for example, Web Security Appliance), and OpenDNS (for example, Umbrella).
Figure 1-2 CPwE Industrial Cybersecurity Framework
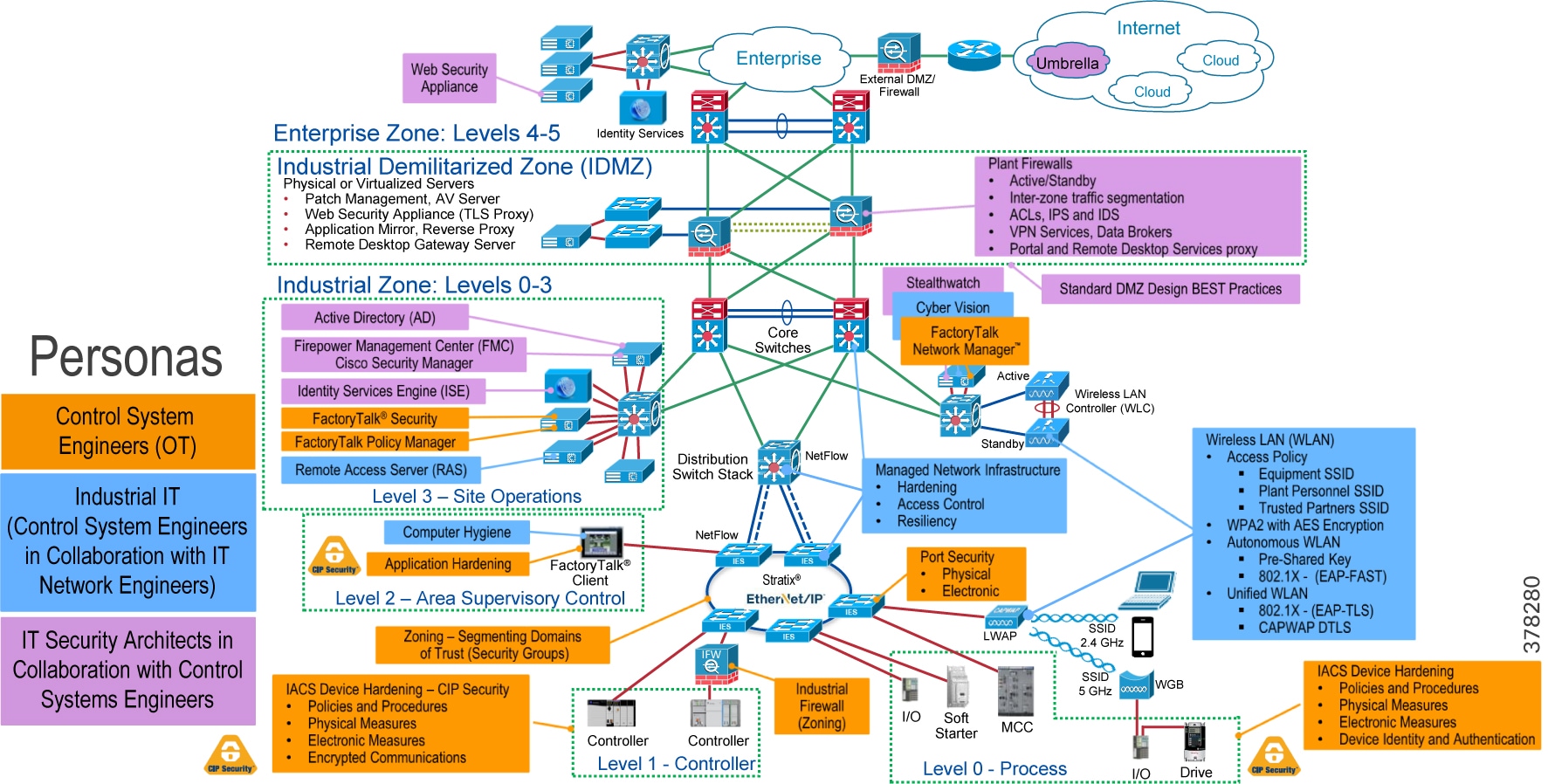
The CPwE Industrial Security Framework (Figure 1-2), using a defense-in-depth approach (Figure 1-3), is aligned to industrial security standards such as ISA/IEC-62443 Industrial Automation and Control Systems (IACS) Security and NIST 800-82 Industrial Control System (ICS) Security.
Defense-in-depth applies policies and procedures that address many different types of threats.
To achieve a defense-in-depth approach, an operational process is required to establish and maintain the security capability. A security-operational process includes the following actions:
1.![]() Identify IACS asset device types and locations within the plant-wide or site-wide network infrastructure.
Identify IACS asset device types and locations within the plant-wide or site-wide network infrastructure.
2.![]() Identify potential internal and external vulnerabilities and threats to those IACS assets and assess the associated risks.
Identify potential internal and external vulnerabilities and threats to those IACS assets and assess the associated risks.
3.![]() Understand the application and functional requirements of the IACS assets including 24x7 operations, communication patterns, topology, required resiliency, and traffic types.
Understand the application and functional requirements of the IACS assets including 24x7 operations, communication patterns, topology, required resiliency, and traffic types.
4.![]() Understand the associated risks of balancing the application and functional requirements of IACS assets with the need to help protect the availability, integrity, and confidentiality of IACS asset data.
Understand the associated risks of balancing the application and functional requirements of IACS assets with the need to help protect the availability, integrity, and confidentiality of IACS asset data.
Figure 1-3 Defense-in-Depth Security
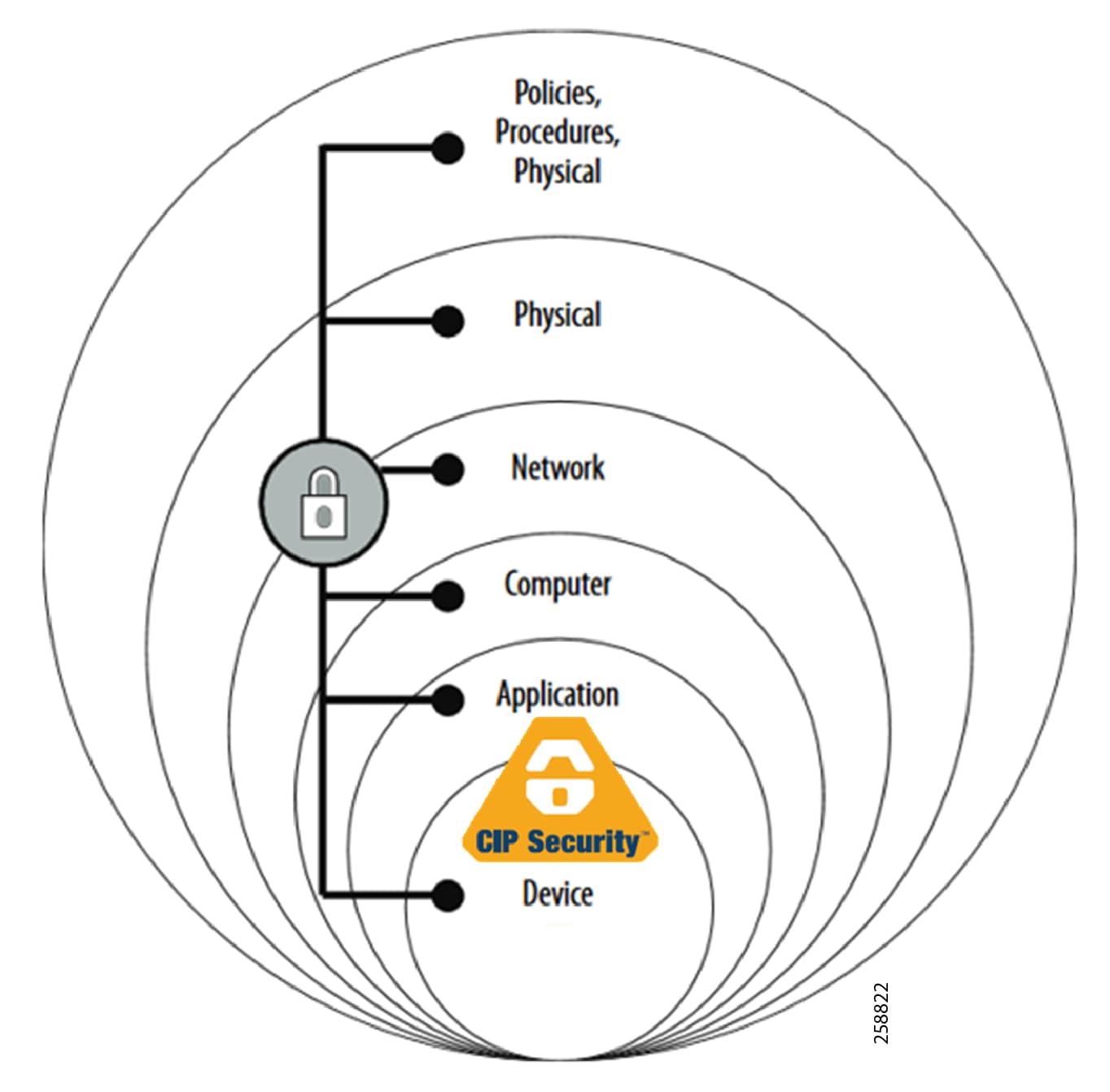
In a defense-in-depth security approach (Figure 1-3), different solutions are needed to address various network and security requirements for a plant-wide or site-wide architecture. This section summarizes the existing Cisco, Panduit, and Rockwell Automation CPwE security CVDs and CRDs that address different aspects of the CPwE Industrial Security Framework (Figure 1-2).
- Deploying Network Security within a Converged Plantwide Ethernet Architecture Design and Implementation Guide outlines several industrial security architecture use cases, with Cisco ISE, for designing with visibility, segmentation, and anomaly detection throughout a plant-wide IACS network infrastructure.
–![]() Rockwell Automation site:
Rockwell Automation site:
https://literature.rockwellautomation.com/idc/groups/literature/documents/td/enet-td019_-en-p.pdf
–![]() Cisco site:
Cisco site:
https://www.cisco.com/c/en/us/td/docs/solutions/Verticals/CPwE/5-1/Network_Security/DIG/CPw E-5-1-NetworkSecurity-DIG.html
- Deploying Identity and Mobility Services within a Converged Plantwide Ethernet Architecture Design and Implementation Guide outlines several industrial security and mobility architecture use cases, with Cisco ISE, for designing and deploying mobile devices, with FactoryTalk® applications, throughout a plant-wide or site-wide IACS network infrastructure.
–![]() Rockwell Automation site:
Rockwell Automation site:
http://literature.rockwellautomation.com/idc/groups/literature/documents/td/enet-td008_-en-p.pdf
–![]() Cisco site:
Cisco site:
http://www.cisco.com/c/en/us/td/docs/solutions/Verticals/CPwE/3-5-1/ISE/DIG/CPwE_ISE_CVD. html
- Cloud Connectivity to a Converged Plantwide Ethernet Architecture Design Guide outlines several industrial security architecture use cases for designing and deploying restricted end-to-end outbound connectivity from FactoryTalk applications to the Rockwell Automation cloud within a CPwE architecture.
–![]() Rockwell Automation site:
Rockwell Automation site:
https://literature.rockwellautomation.com/idc/groups/literature/documents/td/enet-td017_-en-p.pd f
–![]() Cisco site:
Cisco site:
https://www.cisco.com/c/en/us/td/docs/solutions/Verticals/CPwE/5-1/Cloud/DIG/CPwE_Cloud_C onnect_CVD.html
- Deploying Industrial Firewalls within a Converged Plantwide Ethernet Architecture Design and Implementation Guide outlines several use cases for designing, deploying, and managing industrial firewalls throughout a plant-wide IACS network. The Industrial Firewall is ideal for IACS applications that need trusted zone segmentation.
–![]() Rockwell Automation site:
Rockwell Automation site:
http://literature.rockwellautomation.com/idc/groups/literature/documents/td/enet-td002_-en-p.pdf
–![]() Cisco site:
Cisco site:
https://www.cisco.com/c/en/us/td/docs/solutions/Verticals/CPwE/5-0/Firewalls/DIG/CPwE-5-IFS-%20DIG.html
- Deploying CIP Security within a Converged Plantwide Ethernet Architecture Design Guide outlines a comprehensive explanation of the CIP Security application design. It includes information about key requirements, possible deployment models, potential challenges, technology considerations, and guidelines for implementation and configuration of these specific use security cases within the CPwE framework.
–![]() Rockwell Automation site:
Rockwell Automation site:
https://literature.rockwellautomation.com/idc/groups/literature/documents/td/enet-td022_-en-p.pdf
–![]() Cisco site:
Cisco site:
https://www.cisco.com/c/en/us/td/docs/solutions/Verticals/CPwE/5-0/Firewalls/DIG/CPwE-5-IFS-%20DIG.html
Industrial Demilitarized Zone
Sometimes referred to as a perimeter network, the IDMZ (see Figure 1-4) is a buffer that enforces data security policies between a trusted network (Industrial Zone) and an untrusted network (Enterprise Zone). The IDMZ is an additional layer of defense-in-depth to securely share IACS data and network services between the Industrial and Enterprise Zones. The demilitarized zone concept is commonplace to traditional IT networks and adoption for IACS applications.
For secure IACS data sharing, the IDMZ contains assets that act as brokers between the zones. Multiple methods to broker IACS data across the IDMZ exist:
–![]() PI-to-PI interface for FactoryTalk Historian
PI-to-PI interface for FactoryTalk Historian
–![]() Secure File Transfer Gateway
Secure File Transfer Gateway
–![]() Windows Server Update Services (WSUS)
Windows Server Update Services (WSUS)
- Use Microsoft® Remote Desktop (RD) Gateway services for secure remote access via Remote Desktop Connection client and ThinManager.
These broker methods, which help to hide and protect the existence and characteristics of the Industrial Zone servers from clients and servers in the Enterprise Zone, are highlighted in Figure 1-4 and are covered in CPwE IDMZ.
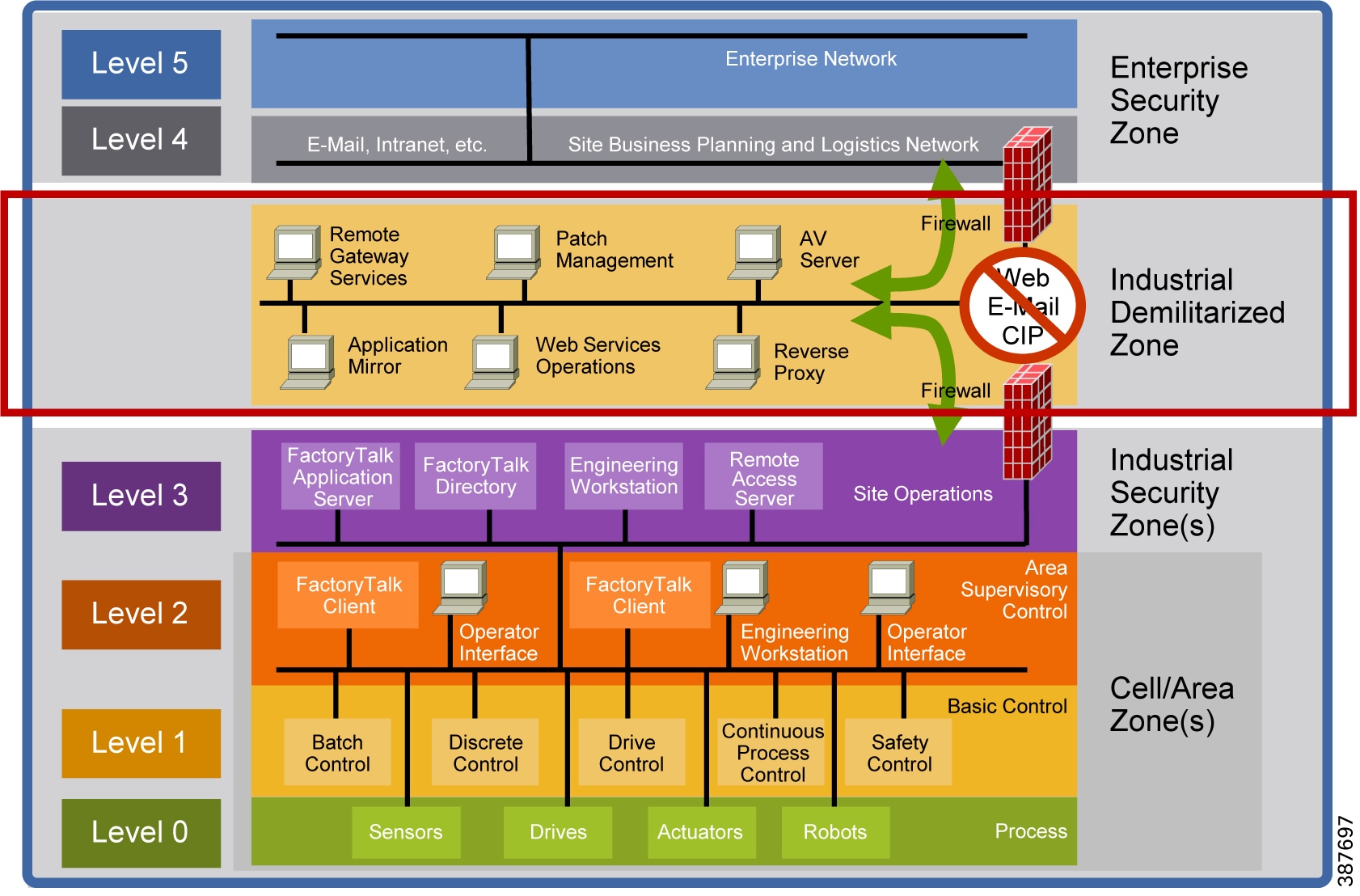
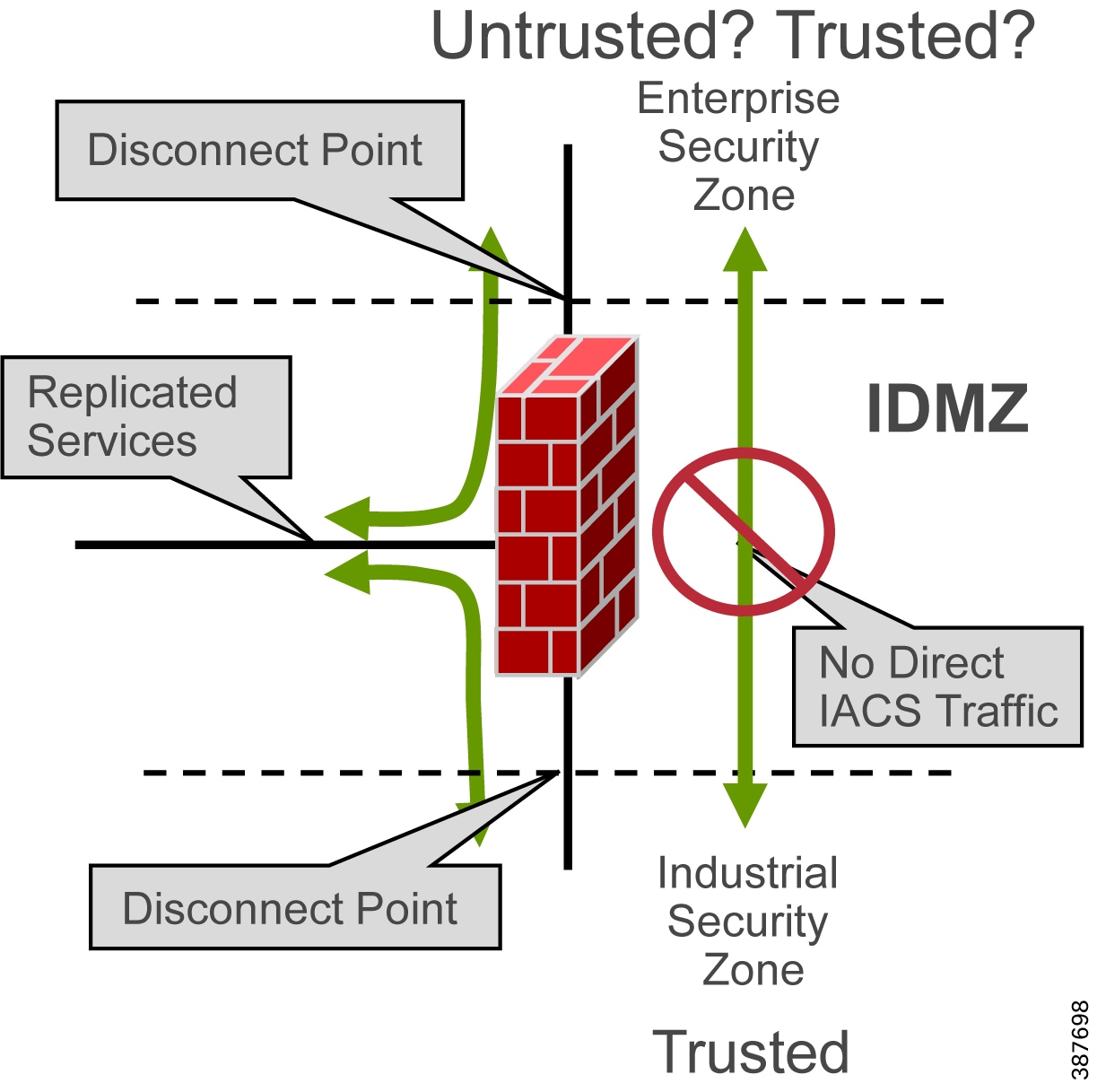
High-level IDMZ design principles (see Figure 1-5) include:
- All IACS network traffic from either side of the IDMZ terminates in the IDMZ; no IACS traffic directly traverses the IDMZ
- EtherNet/IP IACS traffic does not enter the IDMZ; it remains within the Industrial Zone
- Primary services are not permanently stored in the IDMZ
- All data is transient; the IDMZ does not permanently store data
- Functional sub-zones within the IDMZ are configured to segment access to IACS data and network services (for example, IT, Operations and Trusted Partner zones)
- A properly designed IDMZ will support the capability of being unplugged if compromised, while still allowing the Industrial Zone to operate without disruption
Figure 1-5 IDMZ High Level Concepts
CPwE IDMZ Solution Use Cases
CPwE IDMZ outlines key requirements and design considerations to help with successfully designing and deploying an IDMZ and implementing IACS data and network services between the Industrial and Enterprise Zones:
–![]() Redundant distribution/aggregation Ethernet switches
Redundant distribution/aggregation Ethernet switches
–![]() PI-to-PI interface for FactoryTalk Historian
PI-to-PI interface for FactoryTalk Historian
–![]() Secure File Transfer Gateway
Secure File Transfer Gateway
–![]() Use Microsoft Remote Desktop (RD) Gateway services for secure remote access via Remote Desktop Connection client and ThinManager
Use Microsoft Remote Desktop (RD) Gateway services for secure remote access via Remote Desktop Connection client and ThinManager
–![]() IACS applications-for example, Secure File Transfer, FactoryTalk applications (FactoryTalk Historian, FactoryTalk® VantagePoint®, FactoryTalk View Site Edition, FactoryTalk ViewPoint, FactoryTalk AssetCentre, Studio 5000 Logix Designer®)
IACS applications-for example, Secure File Transfer, FactoryTalk applications (FactoryTalk Historian, FactoryTalk® VantagePoint®, FactoryTalk View Site Edition, FactoryTalk ViewPoint, FactoryTalk AssetCentre, Studio 5000 Logix Designer®)
–![]() Network services-for example, AD, Cisco Identity Services Engine (ISE), Network Time Protocol (NTP), licensing management via Cisco Smart Software Manager On-Prem, and Windows Updates
Network services-for example, AD, Cisco Identity Services Engine (ISE), Network Time Protocol (NTP), licensing management via Cisco Smart Software Manager On-Prem, and Windows Updates
–![]() ThinManager access via Remote Desktop Gateway to IACS assets
ThinManager access via Remote Desktop Gateway to IACS assets
 Feedback
Feedback