Integrate Microsoft Intune with Cisco ISE
Cisco ISE supports Microsoft Intune, an endpoint management solution, as an MDM integration. Communications between the two systems are governed by Microsoft's NAC integration designs as detailed in Network access control (NAC) integration with Intune.
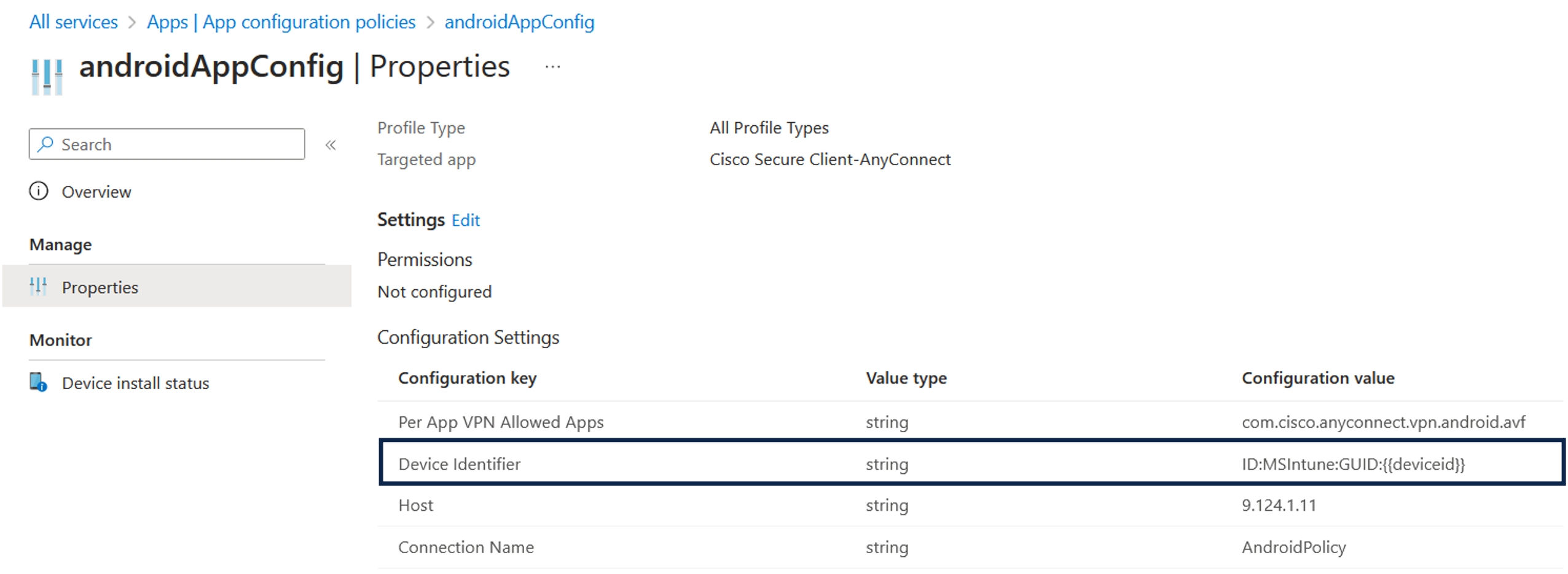
From 2024-03-24, Microsoft no longer supports the Intune NAC service API for MAC address and UDID-based queries. Only the Microsoft Compliance Retrieval API (NAC 2.0 API) is supported, allowing both GUID and MAC address-based queries, starting 2023-07-31.
After 2024-03-24, you must upgrade to one of these Cisco ISE releases to continue using your Microsoft Intune integrations:
-
Cisco ISE release 3.1 patch 8
-
Cisco ISE release 3.2 patch 4
The earlier patches of these releases cannot retrieve device registration and compliance information from connected Microsoft Intune servers from March 24, 2024.
With Microsoft's NAC 2.0 API, Cisco ISE can only retrieve these endpoint attribute information:
-
Compliance status
-
Managed by Intune
-
MAC address
-
Registered status

 Feedback
Feedback