About Logical Devices
A logical device lets you run one application instance (either ASA or Firepower Threat Defense) and also one optional decorator application (Radware DefensePro) to form a service chain .
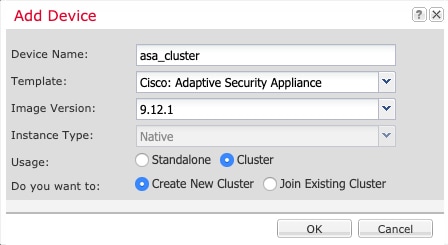
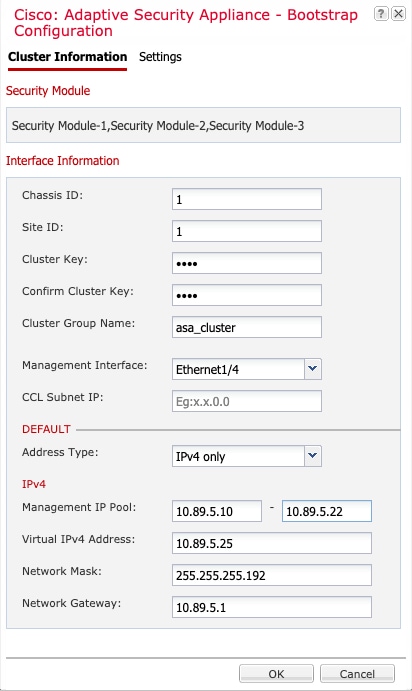
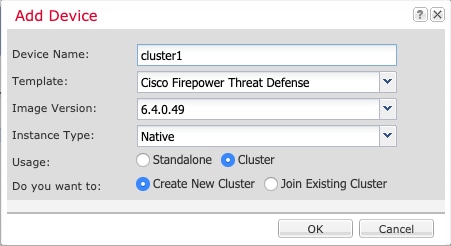
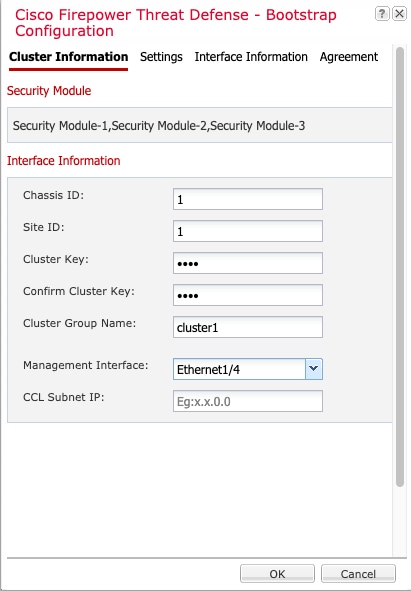
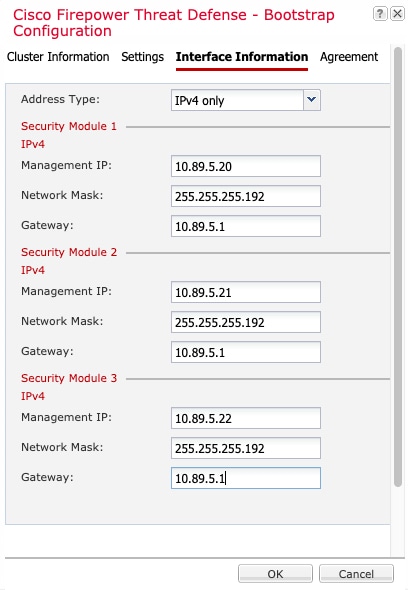
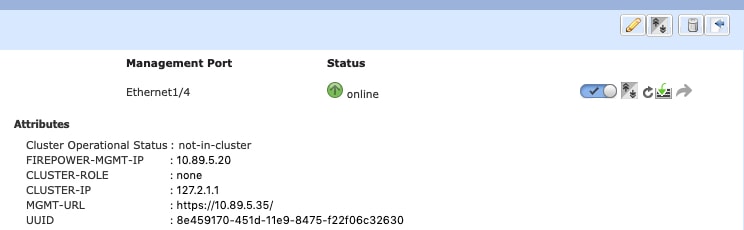
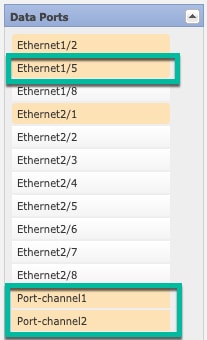
When you add a logical device, you also define the application instance type and version, assign interfaces, and configure bootstrap settings that are pushed to the application configuration.
 Note |
For the Firepower 9300, you must install the same application instance type (ASA or FTD) on all modules in the chassis; different types are not supported at this time. Note that modules can run different versions of an application instance type. |
Standalone and Clustered Logical Devices
You can add the following logical device types:
-
Standalone—A standalone logical device operates as a standalone unit or as a unit in a High Availability pair.
-
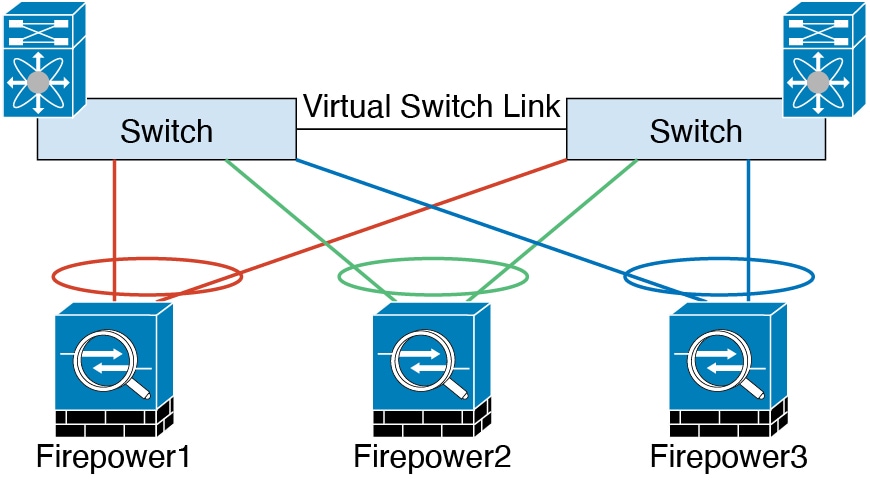
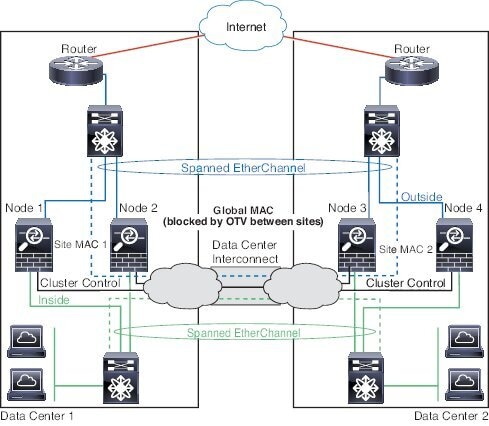
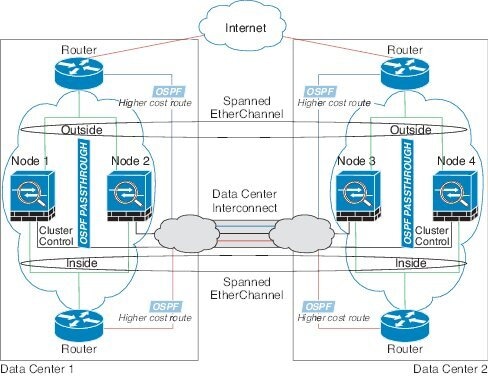
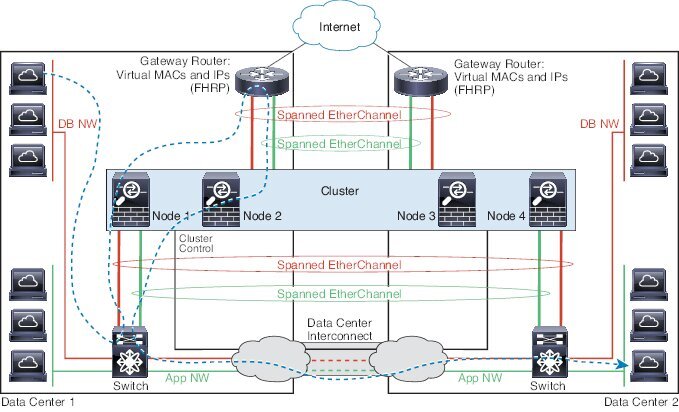
Cluster—A clustered logical device lets you group multiple units together, providing all the convenience of a single device (management, integration into a network) while achieving the increased throughput and redundancy of multiple devices. Multiple module devices, like the Firepower 9300, support intra-chassis clustering. For the Firepower 9300, all three modules must participate in the cluster.
 )
)
 )
) )
) )
)
 )
)
 Feedback
Feedback