Add a Managed Device to the Firepower Management Center
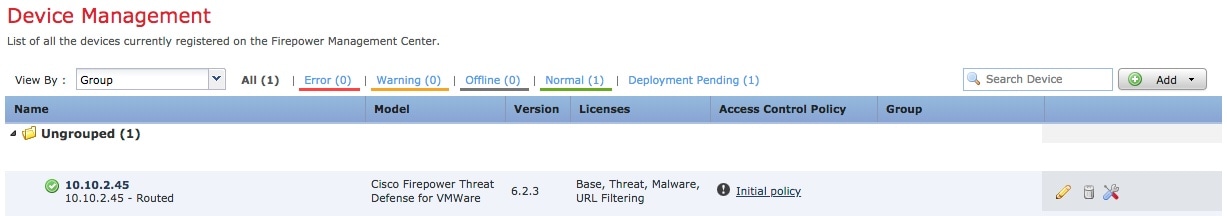
After you add a Firepower Threat Defense as a managed device, you configure it further using the Firepower Management Center.
Before you begin
You must complete all of the following tasks first:
Procedure
| Step 1 |
In the Firepower Management Center, click . |
| Step 2 |
Click .
|
| Step 3 |
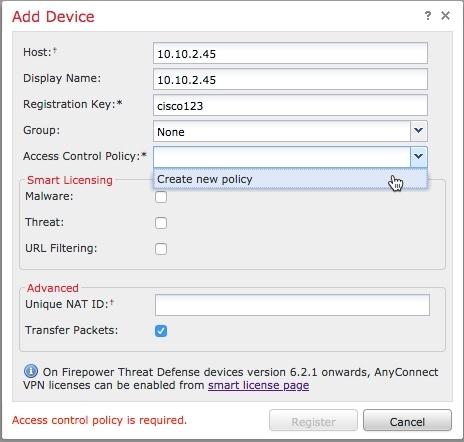
From the Access Control Policy list, click Create New Policy. |
| Step 4 |
In the New Policy dialog box, enter a name and, optionally, a description for the policy and click Block All Traffic as the following figure shows. (You'll change the default policy action later.) 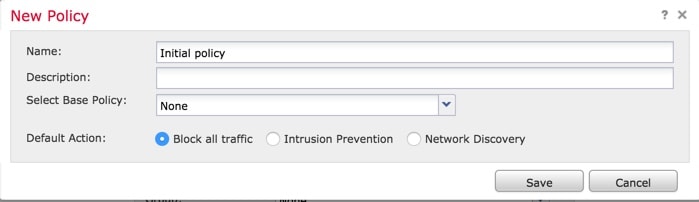 |
| Step 5 |
Click Save. |
| Step 6 |
In the Add Device dialog box, check all the boxes in the Smart Licensing section. |
| Step 7 |
Check Transfer Packets. |
| Step 8 |
Click Register and wait for device discovery and registration to complete.
|
 (edit) next to your managed device.
(edit) next to your managed device.
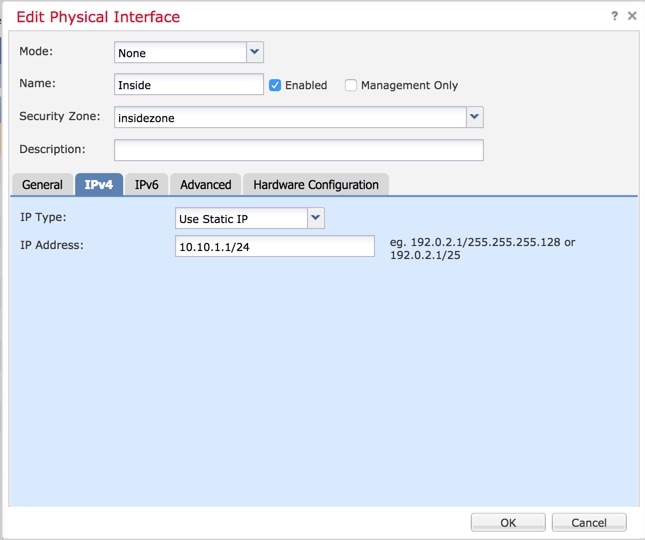
 (add) and
(add) and 

 Feedback
Feedback