Introduction to Rules
Rules in various policies exert granular control over network traffic. The system evaluates traffic against rules in the order that you specify, using a first-match algorithm.
Although these rules may include other configurations that are not consistent across policies, they share many basic characteristics and configuration mechanics, including:
-
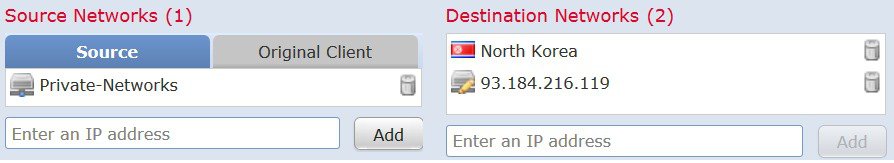
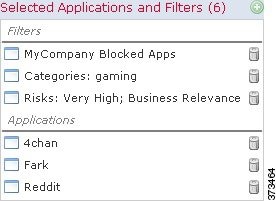
Conditions—Rule conditions specify the traffic that each rule handles. You can configure each rule with multiple conditions. Traffic must match all conditions to match the rule.
-
Action—A rule's action determines how the system handles matching traffic. Note that even if a rule does not have an Action list you can choose from, the rule still has an associated action. For example, a custom network analysis rule uses a network analysis policy as its "action." As another example, QoS rules do not have an explicit action because all QoS rules do the same thing: rate limit traffic.
-
Position—A rule's position dermines its evaluation order. When using a policy to evaluate traffic, the system matches traffic to rules in the order you specify. Usually, the system handles traffic according to the first rule where all the rule’s conditions match the traffic. (Monitor rules, which track and log but do not affect traffic flow, are an exception.) Proper rule order reduces the resources required to process network traffic, and prevents rule preemption.
-
Category—To organize some rule types, you can create custom rule categories in each parent policy.
-
Logging—For many rules, logging settings govern whether and how the system logs connections handled by the rule. Some rules (such as identity and network analysis rules) do not include logging settings because the rules neither determine the final disposition of connections, nor are they specifically designed to log connections. As another example, QoS rules do not include logging settings; you cannot log a connection simply because it was rate limited.
-
Comments—For some rule types, each time you save changes, you can add comments. For example, you might summarize the overall configuration for the benefit of other users, or note when you change a rule and the reason for the change.
 Tip |
A right-click menu in many policy editors provides shortcuts to many rule management options, including editing, deleting, moving, enabling, and disabling. |
Rules with Shared Characteristics
This chapter documents many common aspects of the following rules and configurations. For information on non-shared configurations, see:
-
Access control rules—Access Control Rules
-
Tunnel and prefilter rules—Tunnel and Prefilter Rule Components
-
SSL rules—Creating and Modifying TLS/SSL Rules
-
DNS rules—Creating and Editing DNS Rules
-
Identity rules—Create an Identity Rule
-
Network analysis rules—Configuring Network Analysis Rules
-
QoS rules—Configuring QoS Rules
-
Intelligent Application Bypass (IAB)—Intelligent Application Bypass
-
Application filters—Application Filters
Rules without Shared Characteristics
Rules whose configurations are not documented in this chapter include:
-
Intrusion rules—Tuning Intrusion Policies Using Rules
-
File rules—File Rules
-
Correlation rules—Configuring Correlation Rules
-
NAT rules (Classic)—NAT for 7000 and 8000 Series Devices
-
NAT rules (Firepower Threat Defense)—Network Address Translation (NAT) for Firepower Threat Defense
-
8000 Series fastpath rules—Configuring Fastpath Rules (8000 Series)





 Feedback
Feedback