Information About Control Plane Policing
Control Plane Policing Overview
To protect the control plane on a router from DoS attacks and to provide fine-control over the traffic to the control plane, the Control Plane Policing feature treats the control plane as a separate entity with its own interface for ingress (input) and egress (output) traffic. This interface is called the punt or inject interface, and it is similar to a physical interface on the router. Along this interface, packets are punted from the forwarding plane to the RP (in the input direction) and injected from the RP to the forwarding plane (in the output direction). A set of quality of service (QoS) rules can be applied on this interface (in the input direction) in order to achieve CoPP.
These QoS rules are applied only after the packet has been determined to have the control plane as its destination. You can configure a service policy (QoS policy map) to prevent unwanted packets from progressing after a specified rate limit has been reached; for example, a system administrator can limit all TCP/TELNET packets that are destined for the control plane.
You can use the platform qos-feature copp-mpls enable command to enable the Control Plane Policing feature on the device for MPLS explicit null scenario, control packets destined to the device is punted to proper control CPU Q. If CoPP-MPLS remains disabled, then self destined control packets like BGP, LDP, telnet and so on, that are MPLS explicit null tagged are not classified by CoPP and is punted to HOST_Q instead of CFM_Q/CONTROL_Q.
 Note |
The command platform qos-feature copp-mpls enable is supported only on Cisco NCS 4200 platform. |
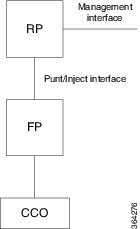
The figure provides an abstract illustration of the router with a single RP and forwarding plane. Packets that are destined to the control plane come in through the carrier card and then go through the forwarding plane before being punted to the RP. When an input QoS policy map is configured on the control plane, the forwarding plane performs the QoS action (for example, a transmit or drop action) before punting packets to the RP in order to achieve the best protection of the control plane in the RP.
 Note |
The figure is not applicable to the RSP3 module. |
 Note |
As mentioned in this section, the control plane interface is directly connected to the RP, so all traffic through the control plane interface to or from the control-plane is not subject to the CoPP function performed by the forwarding plane. |
Benefits of Control Plane Policing
Configuring the Control Plane Policing feature on your Cisco router or switch provides the following benefits:
-
Protection against DoS attacks at infrastructure routers and switches
-
QoS control for packets that are destined to the control plane of Cisco routers or switches
-
Ease of configuration for control plane policies
-
Better platform reliability and availability
Control Plane Terms to Understand
On the router, the following terms are used for the Control Plane Policing feature:
-
Control plane—A collection of processes that run at the process level on the Route Processor (RP). These processes collectively provide high-level control for most Cisco IOS XE functions. The traffic sent to or sent by the control plane is called control traffic.
-
Forwarding plane—A device that is responsible for high-speed forwarding of IP packets. Its logic is kept simple so that it can be implemented by hardware to do fast packet-forwarding. It punts packets that require complex processing (for example, packets with IP options) to the RP for the control plane to process them.
Supported Protocols
The following table lists the protocols supported on Control Plane Policing feature. It is mandatory that the IP address should match the source or destination IP address.
|
Supported Protocols |
Criteria |
Match |
Queue# |
||
|---|---|---|---|---|---|
|
TFTP - Trivial FTP |
Port Match |
IP access list ext copp-system-acl-tftp permit udp any any eq 69 |
NQ_CPU_HOST_Q |
||
|
TELNET |
Port Match |
IP access list ext copp-system-acl-telnet permit tcp any any eq telnet |
NQ_CPU_CONTROL_Q |
||
|
NTP - Network Time Protocol |
Port Match |
IP access list ext copp-system-acl-ntp permit udp any any eq ntp |
NQ_CPU_HOST_Q |
||
|
FTP - File Transfer Protocol |
Port Match |
IP access list ext copp-system-acl-ftp permit tcp host any any eq ftp |
NQ_CPU_HOST_Q |
||
|
SNMP - Simple Network Management Protocol |
Port Match |
IP access list ext copp-system-acl-snmp permit udp any any eq snmp |
NQ_CPU_HOST_Q |
||
|
TACACS - Terminal Access Controller Access-Control System |
Port Match |
IP access list ext copp-system-acl-tacacs permit tcp any any tacacs |
NQ_CPU_HOST_Q |
||
|
FTP-DATA |
Port Match |
IP access list ext copp-system-acl-ftpdata permit tcp any any eq 20 |
NQ_CPU_HOST_Q |
||
|
HTTP - Hypertext Transfer Protocol |
Port Match |
IP access list ext copp-system-acl-http permit tcp any any eq www |
NQ_CPU_HOST_Q |
||
|
WCCP - Web Cache Communication Protocol |
Port Match |
IP access list ext copp-system-acl-wccp permit udp any eq 2048 any eq 2048 |
NQ_CPU_HOST_Q |
||
|
SSH - Secure Shell |
Port Match |
IP access list ext copp-system-acl-ssh permit tcp any any eq 22 |
NQ_CPU_HOST_Q |
||
|
ICMP - Internet Control Message Protocol |
Protocol Match |
IP access list copp-system-acl-icmp permit icmp any any |
NQ_CPU_HOST_Q |
||
|
DHCP - Dynamic Host Configuration Protocol |
Port Match |
IP access list copp-system-acl-dhcp permit udp any any eq bootps |
NQ_CPU_HOST_Q |
||
|
MPLS- OAM |
Port Match |
IP access list copp-system-acl-mplsoam permit udp any eq 3503 any |
NQ_CPU_HOST_Q |
||
|
LDP - Label Distribution Protocol |
Port Match |
IP access list copp-system-acl-ldp permit udp any eq 646 any eq 646 permit tcp any any eq 646 |
NQ_CPU_CFM_Q |
||
|
RADIUS - Remote Authentication Dial In User Service |
Port Match |
IP access list copp-system-radius permit udp any any eq 1812 permit udp any any eq 1813 permit udp any any eq 1645 permit udp any any eq 1646 permit udp any eq 1812 any permit udp any eq 1813 any permit udp any eq 1645 any |
NQ_CPU_HOST_Q |
||
|
Network Configuration Protocol (NETCONF) |
IP/Port Match |
IP access list ext copp-system-acl-telnet permit tcp any any eq 830 - NETCONF |
NQ_CPU_HOST_Q |
||
|
PostgreSQL Support |
IP/Port Match |
IP access list ext copp-system-acl-telnet PostgreSQL IP/Port Match permit tcp 169.223.252.0.0 0.0.3.255 host 169.223.253.1 eq 5432 |
NQ_CPU_HOST_Q |
||
|
Source IP or Destination IP |
IP/Port Match |
Permit IP host 10.1.1.1 or 10.1.1.2
|
NQ_CPU_HOST_Q |
Input Rate-Limiting and Silent Mode Operation
A router is automatically enabled to silently discard packets when you configure input policing on control plane traffic using the service-policy input policy-map-name command.
Rate-limiting (policing) of input traffic from the control plane is performed in silent mode. In silent mode, a router that is running Cisco IOS XE software operates without receiving any system messages. If a packet that is entering the control plane is discarded for input policing, you do not receive an error message.
 Feedback
Feedback