Cisco Prime Collaboration Assurance Guide - Advanced, 11.x
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- January 16, 2017
Chapter: Manage Users
- Cisco Prime Collaboration Assurance-Advanced User Roles
- Single Sign-On for Cisco Prime Collaboration
- Default User Accounts
- User Roles and Tasks
- Add, Edit, and Delete a User
- Modify User Roles
- Configure an LDAP Server
- LDAP Configuration Parameters
- Reset Cisco Prime Collaboration Assurance Passwords
- Change Passwords
- Unlock Cisco Prime Collaboration Assurance Account
Manage Users
Cisco Prime Collaboration supports built-in static roles with predefined access control that enables you to perform different tasks.
In Cisco Prime Collaboration, you can create users and assign roles to the users. In Cisco Prime CollaborationAssurance-Standard, a user is assigned the Super Administrator role. Cisco Prime Collaboration Assurance- Advanced supports several user roles.
Cisco Prime Collaboration Assurance enables Role-based Access Control (RBAC) through these built-in static roles. Hence the tasks a user can perform, or the device or device groups a user can view or manage is controlled by the role allocated by the Super Administrator.
You can enforce further access control of selected devices or device groups, and tasks related to those by associating the devices or device groups to specific customers (if you have deployed Cisco Prime Collaboration in MSP mode) or domains (if you have deployed Cisco Prime Collaboration in Enterprise mode). Typically, a user with Operator role, is granted access to certain customers or domains only.
- Cisco Prime Collaboration Assurance-Advanced User Roles
- Single Sign-On for Cisco Prime Collaboration
- Default User Accounts
- User Roles and Tasks
- Add, Edit, and Delete a User
- Modify User Roles
- Configure an LDAP Server
- LDAP Configuration Parameters
- Reset Cisco Prime Collaboration Assurance Passwords
- Change Passwords
- Unlock Cisco Prime Collaboration Assurance Account
Cisco Prime Collaboration Assurance-Advanced User Roles
User roles are used to define the authorizations of tasks that users can access.
You can be assigned one of the following roles:
-
For Cisco Prime Collaboration Release 11.5 and later
Report Viewer—Can view and export the reports only. The homepage of Report Viewer is CDR & CMR Reports. The global user interface components like Search, Device Status Summary, Alarms, and Get Advanced are not available for the Report Viewer user role. You can view all the reports except the following:
-
Helpdesk—Views and accesses network status information only and cannot perform any action on a device or schedule a job that reaches the network.
-
Operator—Performs all Helpdesk tasks and tasks related to the network data collection. Cannot perform any Inventory Management operations such as adding, discovering, or importing devices. Also, an operator cannot configure thresholds for Alarms and Events.
-
Network administrator—Performs all Operator tasks and tasks that result in a network configuration change like credential management, threshold settings, and so on.
-
System administrator—Performs the Assurance user interface-related administration tasks such as backup and restore, maintaining log files, configuring users, and so on.
-
Super administrator—Can perform tasks that both system administrator and network administrator can perform.
Helpdesk is a preselected role that is assigned to every user in Cisco Prime Collaboration.
For Cisco Prime Collaboration Release 11.5 and later
Report Viewer is a preselected role that is assigned to every user in Cisco Prime Collaboration.
The roles selected for a user, determines the access to data of other users. For example, a user with the Super Admin role can view all other users, however a user with the Network Administrator role cannot view the users with higher roles such as Super Administrator, or System Administrator, but can look at other user's data whose role is of Operator or Helpdesk.
If you have deployed Cisco Prime Collaboration in MSP Mode, you can look at customers belonging to another user of the same role, only if you are associated with the customer(s).
If you have deployed Cisco Prime Collaboration in ENT Mode, you can look at domains belonging to another user of the same role, only if you are associated with the domain(s).
Note: The User Management submenu is not available to the following roles:
For Cisco Prime Collaboration Release 11.5 and later
For Cisco Prime Collaboration Release 11.6 and later
The default user role selection is removed from Cisco Prime Collaboration.
Note: If Report Viewer user role is selected, the system does not allow the user to choose any other roles and vice versa.
Single Sign-On for Cisco Prime Collaboration
Cisco Prime Collaboration provides users with admin privileges to enable Single Sign-On (SSO) in Cisco Prime Collaboration Assurance using Security Assertion Markup Language (SAML).
Cisco Prime Collaboration does not support multiserver SAN certificates and end user SAML SSO.
Ensure that the following prerequisites are met before you enable SSO:
- At least one LDAP Administrative user exists in the system—by manually creating an LDAP administrative user in Cisco Prime Collaboration Assurance.
- An Identity Provider (IdP)
server that enables you to use SSO to access many other applications from a
single hosted application and a Service Provider. The Service Provider is a
website that hosts the applications.
Following are the supported third-party IdP servers: For the steps to setup an IdP server, see the SAML SSO Deployment Guide for Cisco Unified Communication Applications, Release 10.0(1).
- Download the Identity Provider metadata file from the IdP server and save it in your local system.
To enable Single Sign-On:
Troubleshooting and Logs for SSO
- When you are logged out of the Cisco Prime Collaboration server while enabling SSO, it is recommended that you close the browser and re-launch the Cisco Prime Collaboration application. Because, though your conference expires in Cisco Prime Collaboration server, the IdP server conference might still be active.
- While enabling SSO, ensure that the hostname for Cisco Prime Collaboration is set and is part of DNS.
- Use the recovery URL- https://<PCserver IP address or host name that is part of DNS>/ssosp/local/login.
- Disable Single Sign-On from CMD Utility.
| Operations can be .. | Values can be .. | ||
| 1-To get the Single Sign-On status | Not applicable | ||
| 2-To get the recovery URL status | Not applicable | ||
| 3-To set the Single Sign-On status | False
|
||
| 4-To set the recovery URL status | True or False |
cpcmconfigsso.sh 3 false
 Note | By default, the recovery URL is enabled. If you want to disable it for security reasons, set it as False. |
Default User Accounts
Cisco Prime Collaboration is preconfigured with a default web client administrator user called globaladmin; globaladmin is a superuser who can access Cisco Prime Collaboration Assurance user interfaces.
Specify a password for globaladmin when you configure your virtual appliance. You need to use these credentials when you launch the Cisco Prime Collaboration web client for the first time.
Cisco Prime Collaboration Assurance server supports the CLI user: admin.
You cannot create CLI users using the web client user interface. CLI users are created during OVA configuration. By default, the username is admin; the password is specified during OVA configuration and is used to log into the CLI to check the application status and perform backup and restore.
 Caution | We recommend that you note down the root password, as if it is forgotten/lost you will have to open a TAC support case to reset the root password. |
 Note |
|
If you are logging in for the first time to the Cisco Prime Collaboration Assurance web client, log in as globaladmin.
 Caution | You must not create a user with the name: globaladmin, pmadmin and admin. |
Choose . Click the Download Log button. Download the tar file and untar it. Check the /opt/emms/emsam/log/importedprovisioninguser.log file, to find the users who were not imported into Cisco Prime Collaboration Assurance database due to several reasons such as duplicate user names (user names already used in Cisco Prime Collaboration Assurance), user names with no passwords and so on.
The Cisco Prime Collaboration Assurance applications do not share inventory database. You must manage the devices separately to perform the Assurance tasks. See Manage Device Credentials to perform device management tasks using the Cisco Prime Collaboration Assurance application.
User Roles and Tasks
The User Roles and Tasks wiki page lists the Cisco Prime Collaboration Assurance user roles and tasks they are mapped to.
 Note | Super administrator has access to all of the user interface menus and can perform all the tasks. Hence, the super administrator is not listed . |
Add, Edit, and Delete a User
You can add a user and assign predefined static roles. The user has access to the Cisco Prime Collaboration web client only and cannot log in to the Cisco Prime Collaboration Assurance server through the CLI.
| Step 1 | Choose . | ||
| Step 2 | In the User Management page, click Add. | ||
| Step 3 | In the
Add
User page, enter the required user details.
Note that because the LDAP server performs authentication, it should have the same user ID as Cisco Prime Collaboration. For more information, see Configure an LDAP Server. If you select the LDAP User option, the Password and Confirm Password fields are not displayed. | ||
| Step 4 | If you have deployed the
Managed Service Provider (MSP) version of Cisco Prime Collaboration, select a
customer from the
Customer drop-down list. If you have deployed
the Enterprise version of Cisco Prime Collaboration, you can select a domain
from the
Assosiate to Domain drop-down list, however it is
not mandatory.
| ||
| Step 5 | Select the appropriate Cisco Prime Collaboration Assurance roles. | ||
| Step 6 | Click
Save.
To edit user details, select a user at and make the necessary changes. For Cisco Prime Collaboration Release 11.6 and later To exclude Report Viewer user role from the assigned roles, you have to manually deselect the Report Viewer option and click Save. As part of your regular system administration tasks, you sometimes must delete users from the Cisco Prime Collaboration database. However, you cannot delete the Cisco Prime Collaboration web client default administrator globaladmin. To delete a user, select the user from and click Delete. Any jobs that are scheduled in the deleted user name continue to run until canceled. |
Modify User Roles
When the contact information, role, or account status of a user changes, the administrator must edit the corresponding details in the system.
To edit user details, select a user at and make the necessary changes.
For Cisco Prime Collaboration Release 11.6 and later
To exclude Report Viewer user role from the assigned roles, you have to manually deselect the Report Viewer option and click Save.
As part of your regular system administration tasks, you sometimes must delete users from the Cisco Prime Collaboration database. However, you cannot delete the Cisco Prime Collaboration web client default administrator- globaladmin.
To delete a user, select the user from and click Delete. Any jobs that are scheduled in the deleted user name continue to run until they are cancelled.
Configure an LDAP Server
You can configure Cisco Prime Collaboration to connect to a Lightweight Directory Access Protocol (LDAP) server, to access user information stored in the LDAP server.
You must create an LDAP user from the User Management page to enable the user to log in using LDAP credentials. To add a user, see Add a User and to edit or delete a user, see Modify User Roles.
Cisco Prime Collaboration supports one primary LDAP server and one backup LDAP server.
 Note | If you have deployed Cisco Prime Collaboration in MSP mode, the LDAP server configured must be a provider LDAP. This provider LDAP server has all the resellers, customers, and admin users. You can configure only one LDAP server. Multiple LDAP server configuration is not supported. |
| Step 1 | Choose . | ||
| Step 2 | In the LDAP Settings page,
enter values for all the fields. See
Table
LDAP Server Configuration
for
the field descriptions.
| ||
| Step 3 | Click Test Connection to check the connectivity to the LDAP server. | ||
| Step 4 | Upon successful connection,
click
Apply Settings
and restart Cisco Prime Collaboration Assurance server to log
in using LDAP.
To restart Cisco Prime Collaboration Assurance Server, log in as admin user and execute the following commands: application stop cpcm application start cpcm The application stop cpcm command takes 10 minutes to complete execution and application start cpcm takes 10 to 15 minutes to complete execution. |
LDAP Configuration Parameters
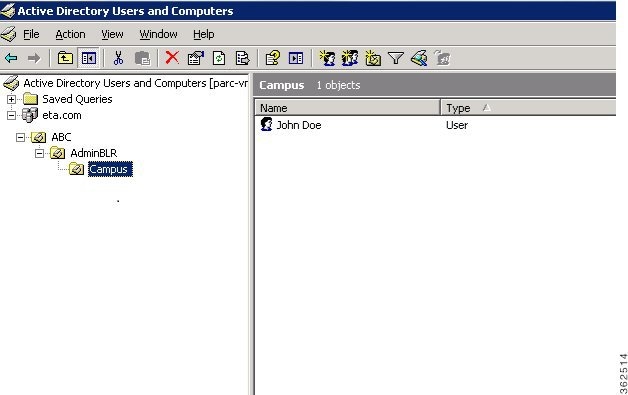
For example, Consider Microsoft Active Directory.
|
Enter the Port number on which the LDAP requests for the server is received. Optionally enter the Backup LDAP server Port number.
|
|||
|
Admin Distinguished Name is the distinguished name to use. |
|||
|
Enter the password for the LDAP server authentication and reconfirm the password.
|
|||
|
Enter the user search base. LDAP server searches for users under this base.
|
 Note | For a list of LDAP servers supported by Cisco Prime Collaboration 11.6, see Supported Devices for Prime Collaboration Assurance. |
Reset Cisco Prime Collaboration Assurance Passwords
As a super administrator, system administrator or network operator, you can reset the password for other Cisco Prime Collaboration users.
Prerequisite - Root access feature is mandatory to perform this task, hence you should raise a TAC case to obtain root access.
You can reset the Cisco Prime Collaboration Assurance web client globaladmin password using the following procedure.
To reset the Cisco Prime Collaboration Assurance globaladmin password:
| Step 1 | Log in as a root user. |
| Step 2 | Execute the following:
#cd /opt/emms/emsam/bin/
# ./resetGlobalAdminPassword.sh
|
| Step 3 | Enter a new password for the globaladmin when prompted, and also confirm the new password, when prompted. A message notifies that the globaladmin passwords has been successfully reset. |
Change Passwords
To change your own password, go to , click Reset Password, and make the necessary changes.
Unlock Cisco Prime Collaboration Assurance Account
For Cisco Prime Collaboration Release 11.5 and later
The permissible login attempts to access the Cisco Prime Collaboration Assurance user interface is 10. If you make 10 failed attempts to log in to Cisco Prime Collaboration Assurance user interface, your account gets disabled.
A globaladmin user with administrator privileges can unlock the account.
To unlock the account:
 Feedback
Feedback