Network Requirements
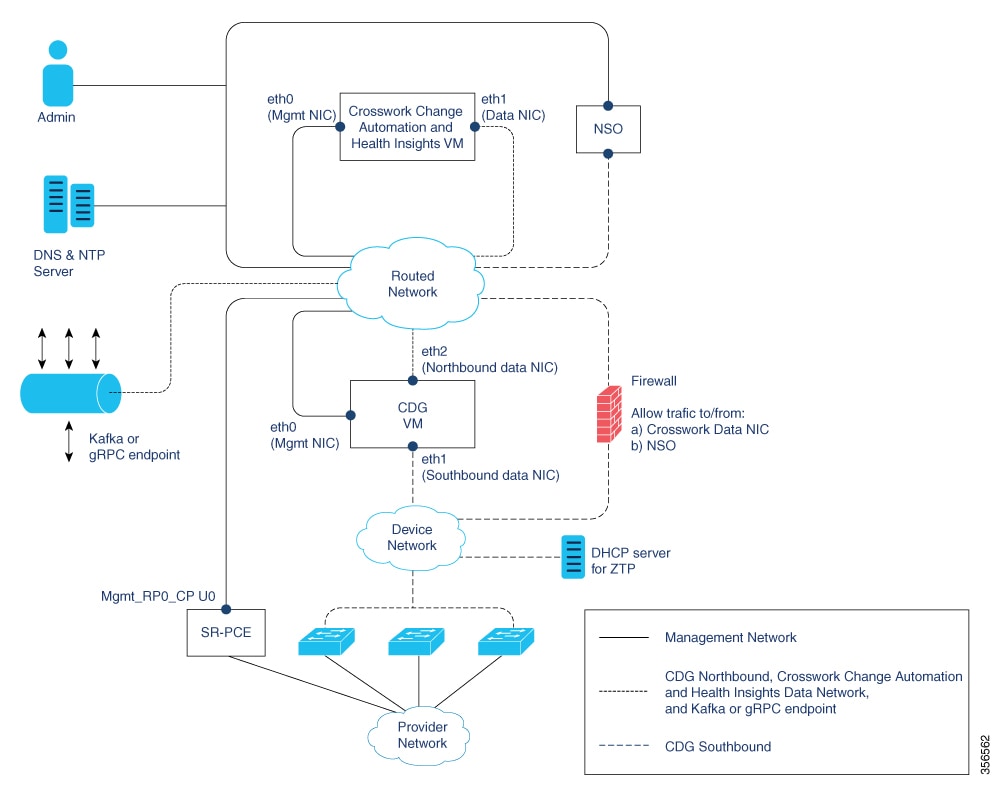
This figure shows the network components and connections needed to install and use Cisco Crosswork Change Automation and Health Insights.
Cisco Crosswork Change Automation and Health Insights Virtual Machine (VM)
The Cisco Crosswork Change Automation and Health Insights VM has the following vNICs:
-
Management NIC (eth0)—Used for traffic management to all Crosswork applications via the API or UI.
-
Data NIC (eth1)—Used for Crosswork applications to reach devices and Cisco Crosswork Data Gateway (northbound).
Cisco Crosswork Data Gateway VM
The Cisco Crosswork Data Gateway VM has the following vNICs:
-
Management NIC (eth0)—Provides control plane communication between Cisco Crosswork Data Gateway and Crosswork VM.
-
Southbound Data NIC (eth1)—Used for Cisco Crosswork Data Gateway collectors to reach devices.
-
Northbound Data NIC (eth2)—Sends data collected from devices to Crosswork applications or external data sinks (Kafka or gRPC receiver).
Cisco Network Services Orchestrator (NSO) VM
The NSO VM has the following vNICs:
-
Management NIC (eth0): Used for Crosswork applications to reach NSO.
-
Southbound data NIC (eth1): Used for NSO to reach devices (southbound) or RFS NSO.
 Note |
Multiple NICs are not required for any of the VMs. However, it is recommended to have separate vNICs so that security policies can be applied (virtually or physically on the switch) if needed. |
Routed and Device Networks
Connectivity between the various components should be accomplished via an external routing entity (shown as 'Routed Network' in the figure). The figure shows various line styles suggesting possible routing domains within the Routed Network.
-
Solid—Management routing domain.
-
Dotted—Cisco Crosswork Data Gateway northbound data routing domain (towards Crosswork/External data sink).
-
Dashes—Device access routing domain (from Cisco Crosswork Data Gateway and NSO).
The IP/subnet addressing scheme on each of these domains depend on the type of deployment.
Routing between domains is needed for Crosswork and NSO to reach the devices. However, proper firewall rules need to be in place to allow only select sources (for example, Crosswork and NSO) to reach the devices.
If you plan to access devices via host name, be sure that host names are registered with your deployment’s DNS server.
On the Device network, devices may be reached in-band or via out-of-band management interfaces depending on the local security policies of each deployment.
An SR-PCE is both a device and an SDN controller. Some deployments may want to treat an SR-PCE as a device, in which case they would need access via the device network. Some deployments may want to treat an SR-PCE as an SDN controller and access it on the Management routing domain. Both of these models are supported.
To enable Crosswork access to an SR-PCE as an SDN controller on the management domain (shown in the figure), just add an SR-PCE as a provider.
To enable Crosswork access to an SR-PCE as a device on the device network (not shown
in figure), add an SR-PCE as a provider with an additional property:
outgoing-interface:eth1.
If you plan to use Zero Touch Provisioning, the device network needs to be equipped with a DHCP server.
 Feedback
Feedback