Overview of Cisco Crosswork Data Gateway
When Cisco Crosswork Data Gateway and Cisco Crosswork Platform (also referred to as Cisco Crosswork in this guide) are deployed together, Cisco Crosswork acts as the controller application for the Cisco Crosswork Data Gateway instance. You can use the Cisco Crosswork UI to manage Cisco Crosswork Data Gateway no matter if they are forwarding data to Cisco Crosswork or other compatible data destination (external gRPC or Kafka servers). The number of Cisco Crosswork Data Gateways you need depends on the number of devices being supported, the amount of data being processed and your network architecture.
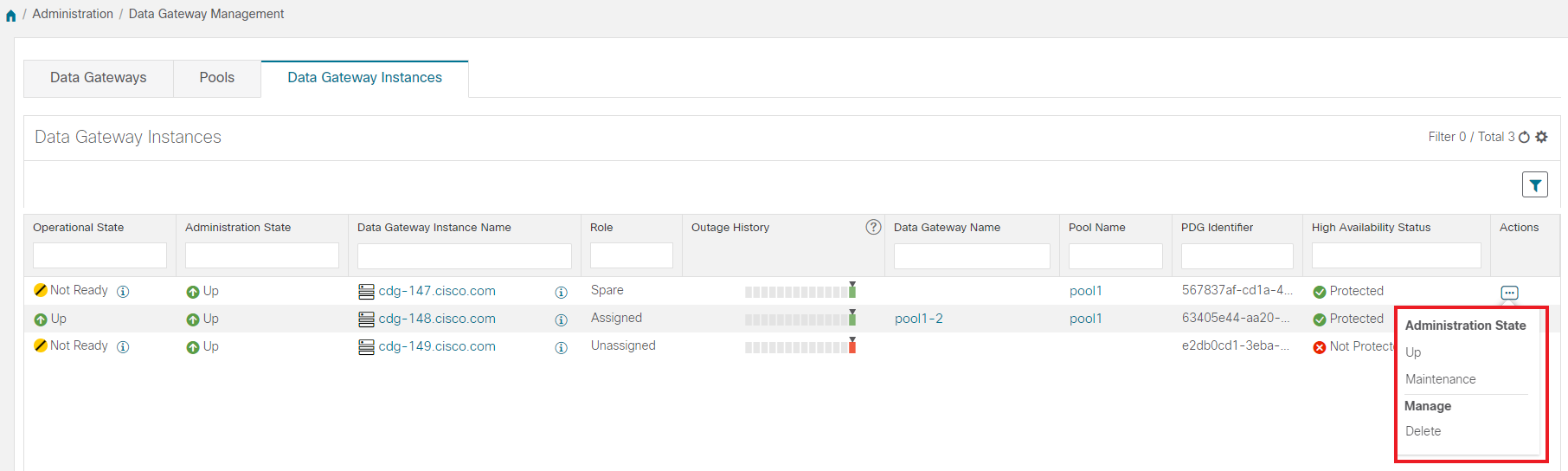
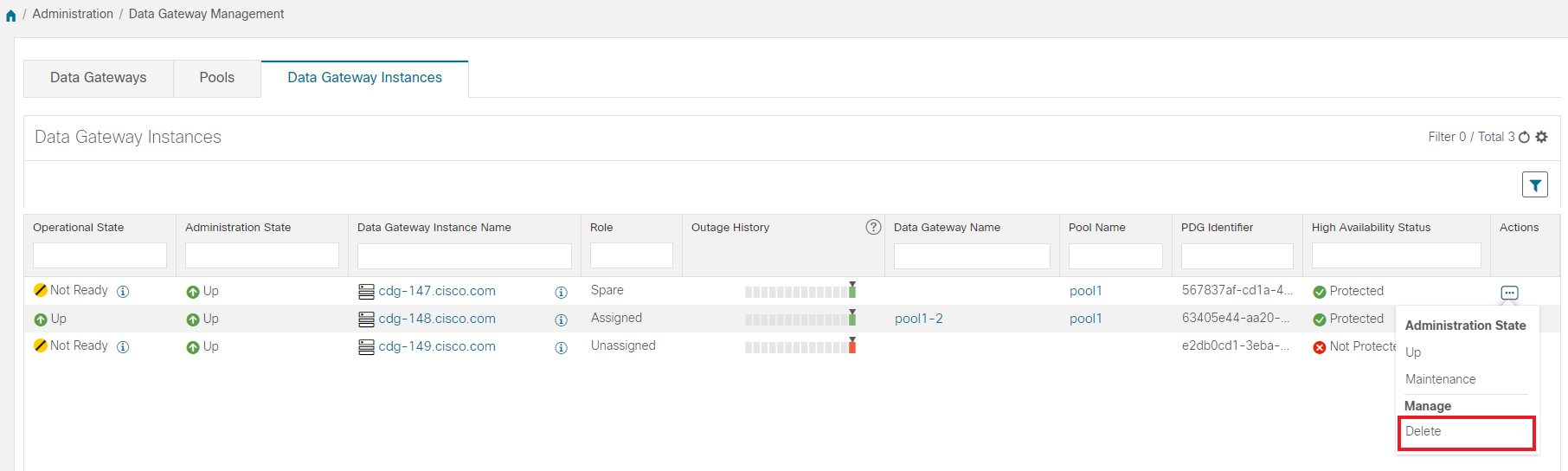
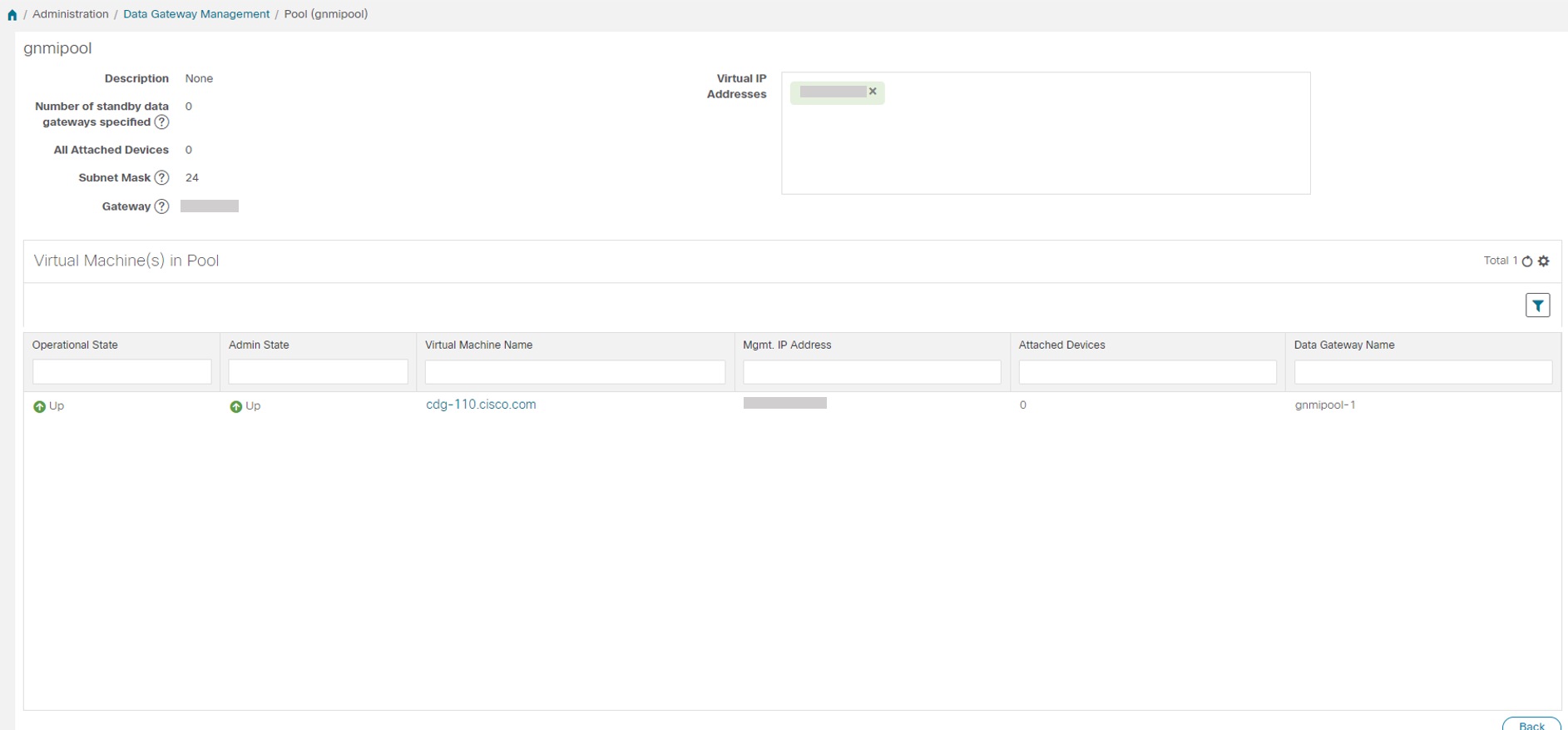
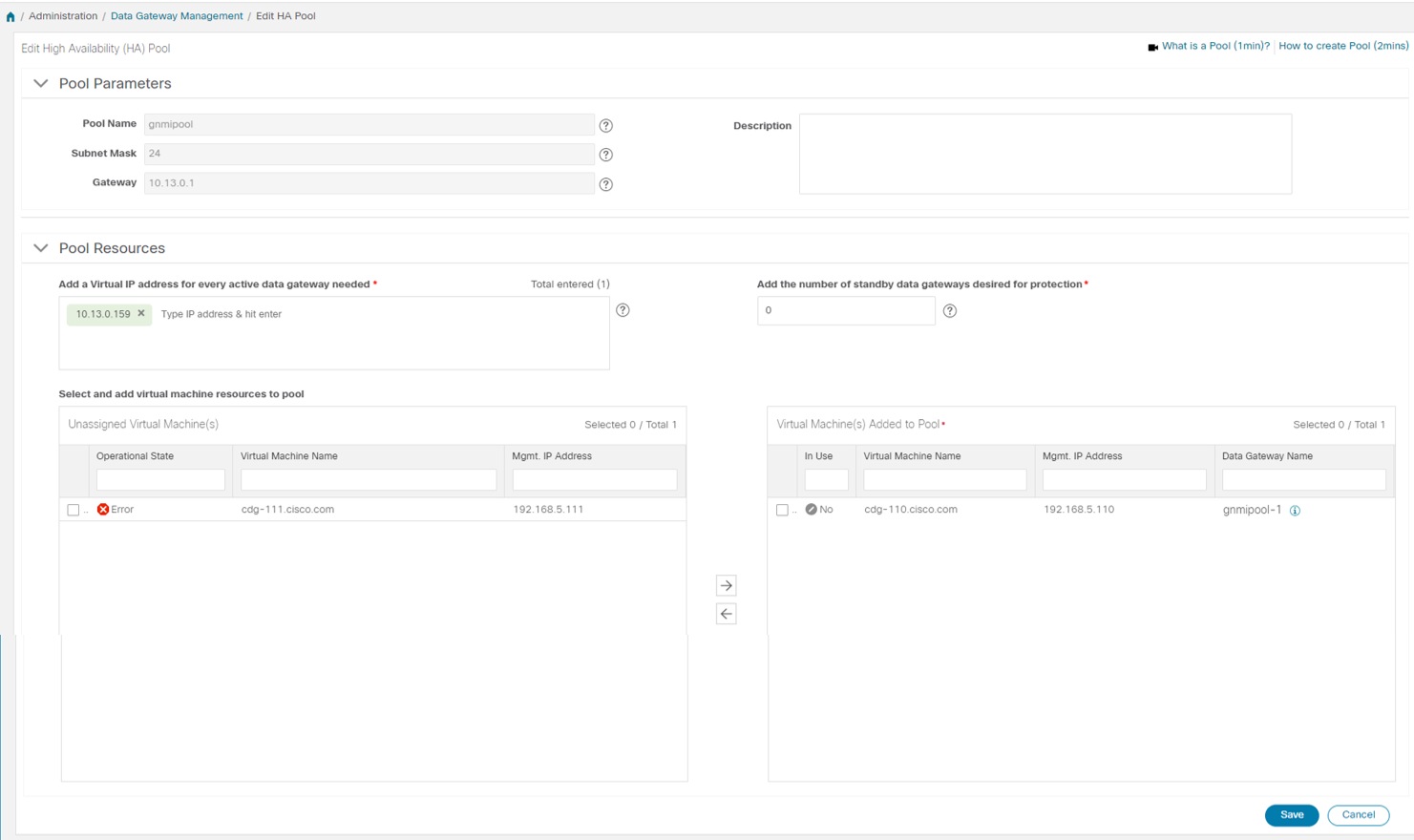
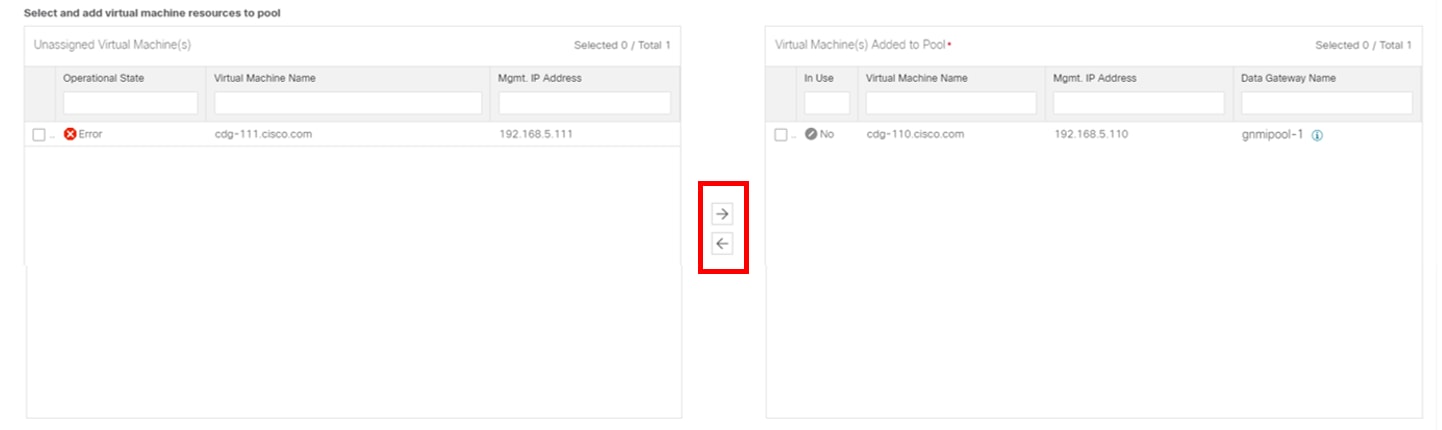
Once you install a Cisco Crosswork Data Gateway VM, it identifies itself to Cisco Crosswork and enrolls itself automatically. Newly enrolled Cisco Crosswork Data Gateway VMs will have the Operational Status as "Degraded" until enrollment is completed. Cisco Crosswork Data Gateway VMs that have the Role as "Unassigned" need to be assigned to a Crosswork Data Gateway pool before they can used. A pool can consist of one or more Cisco Crosswork Data Gateway VMs with an option to enable HA configuration.
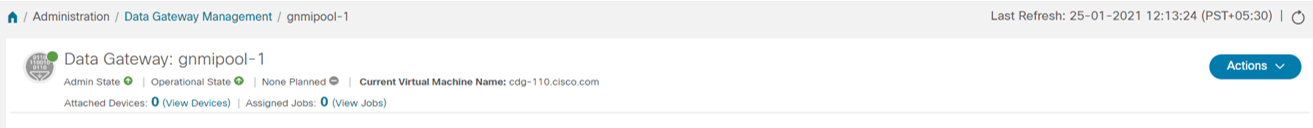
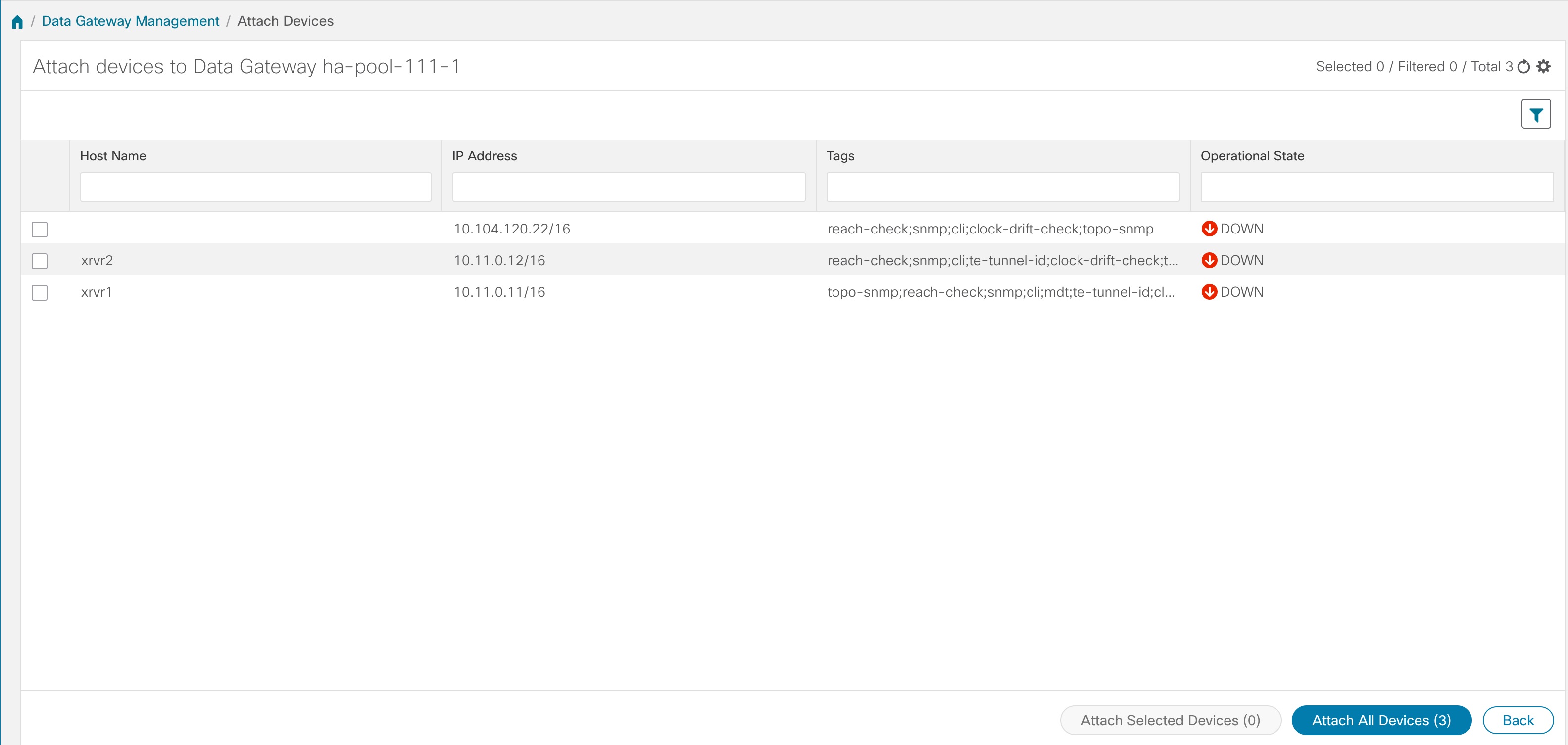
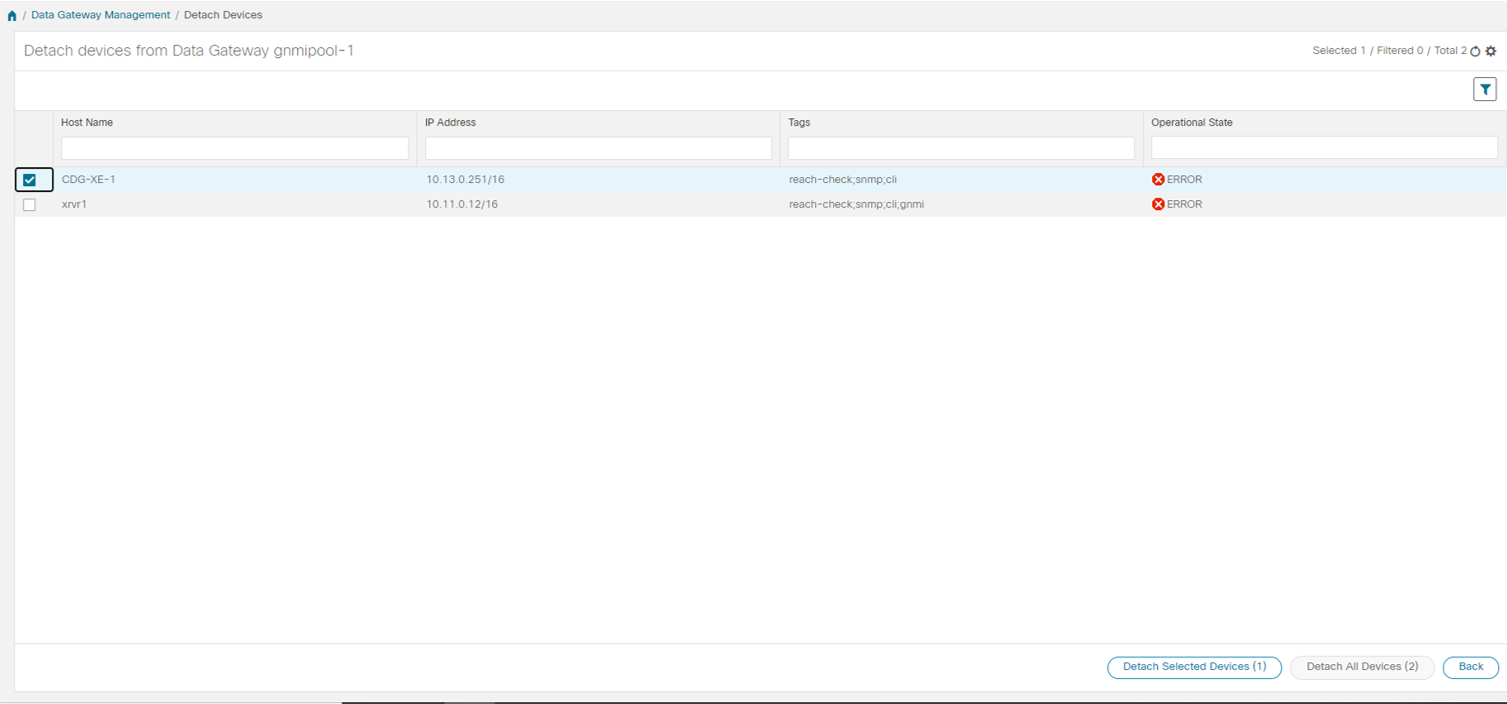
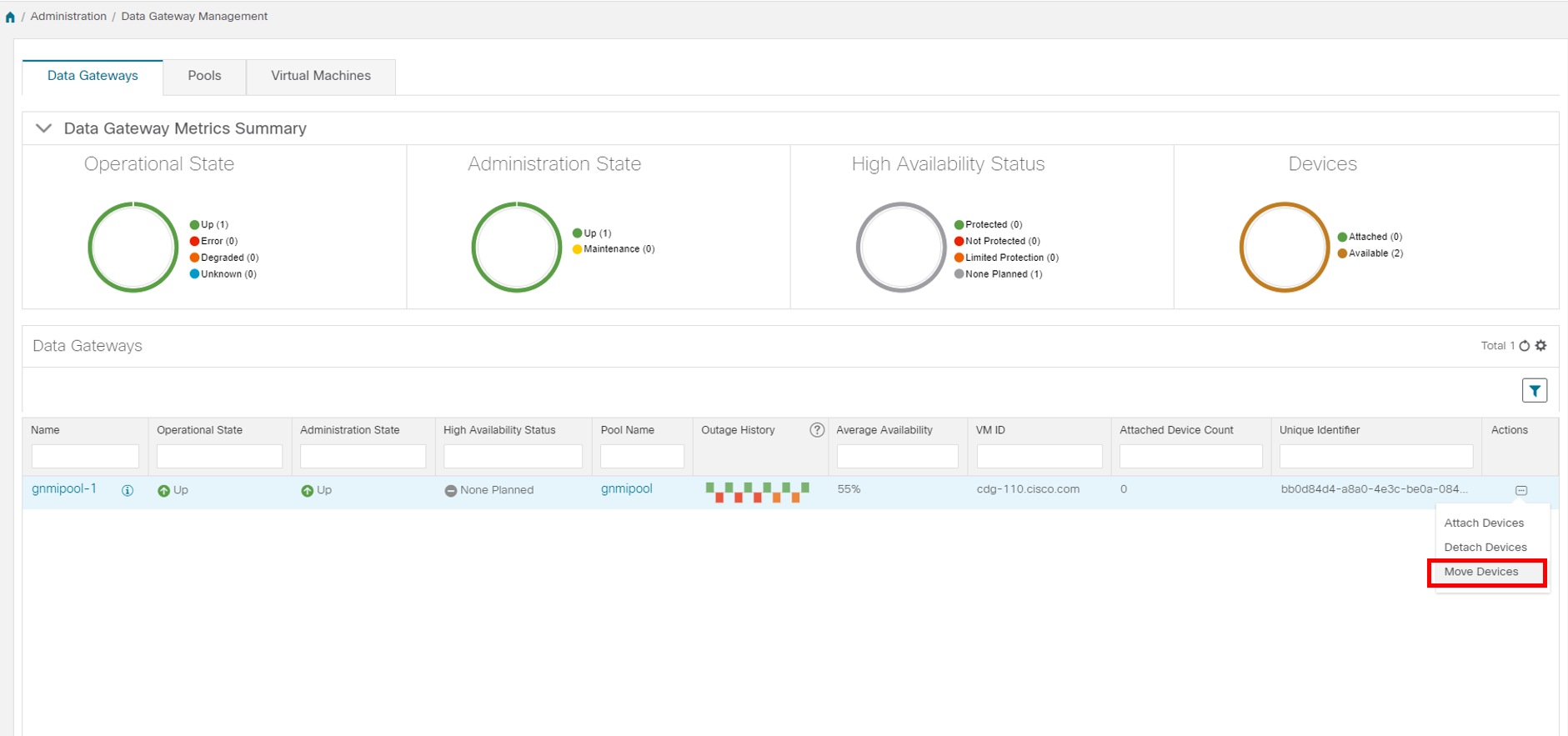
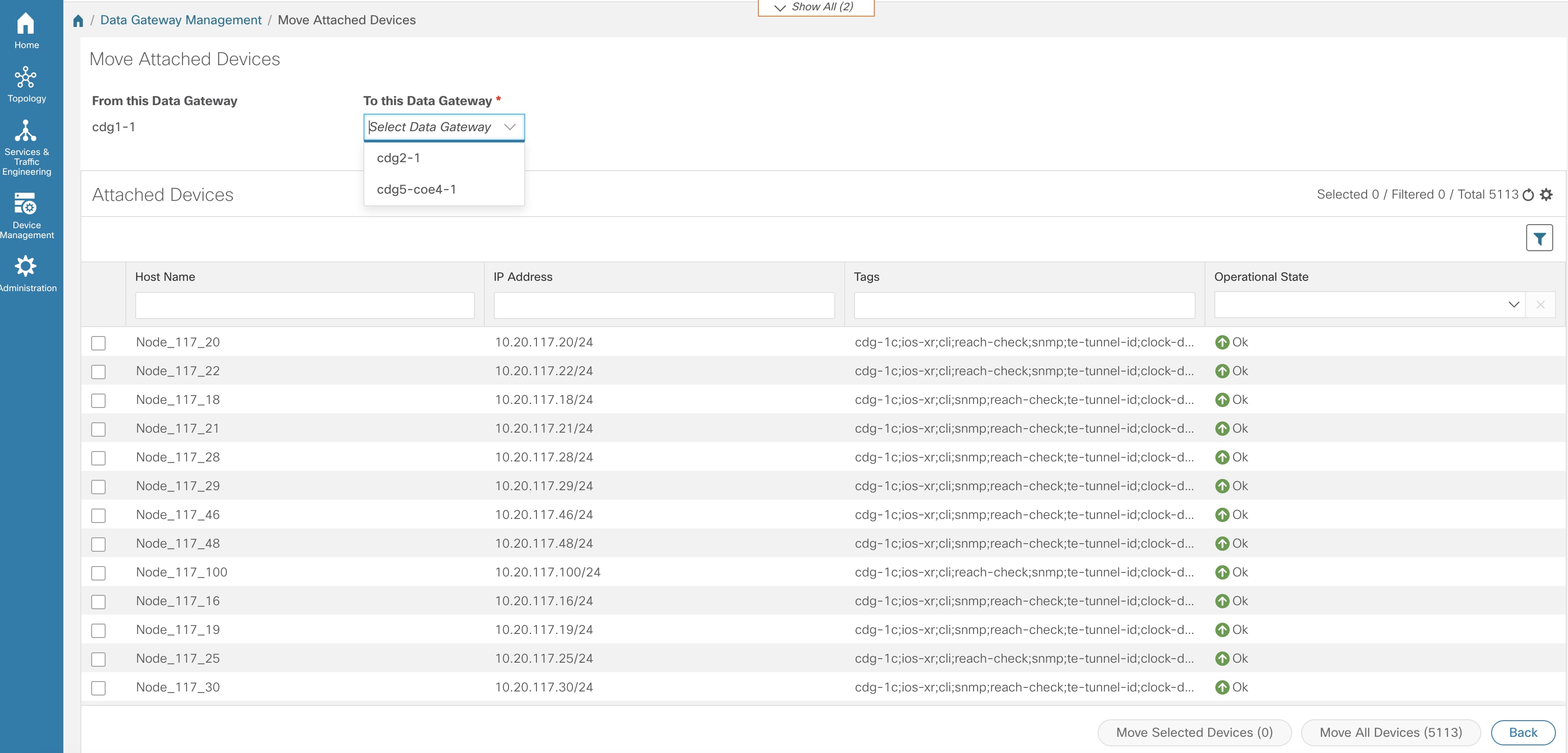
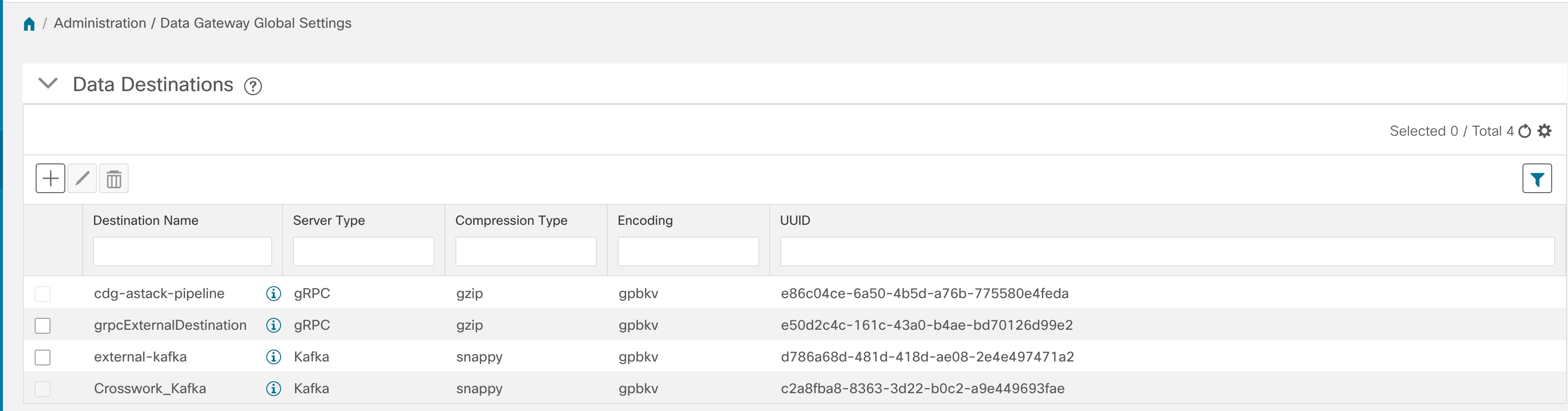
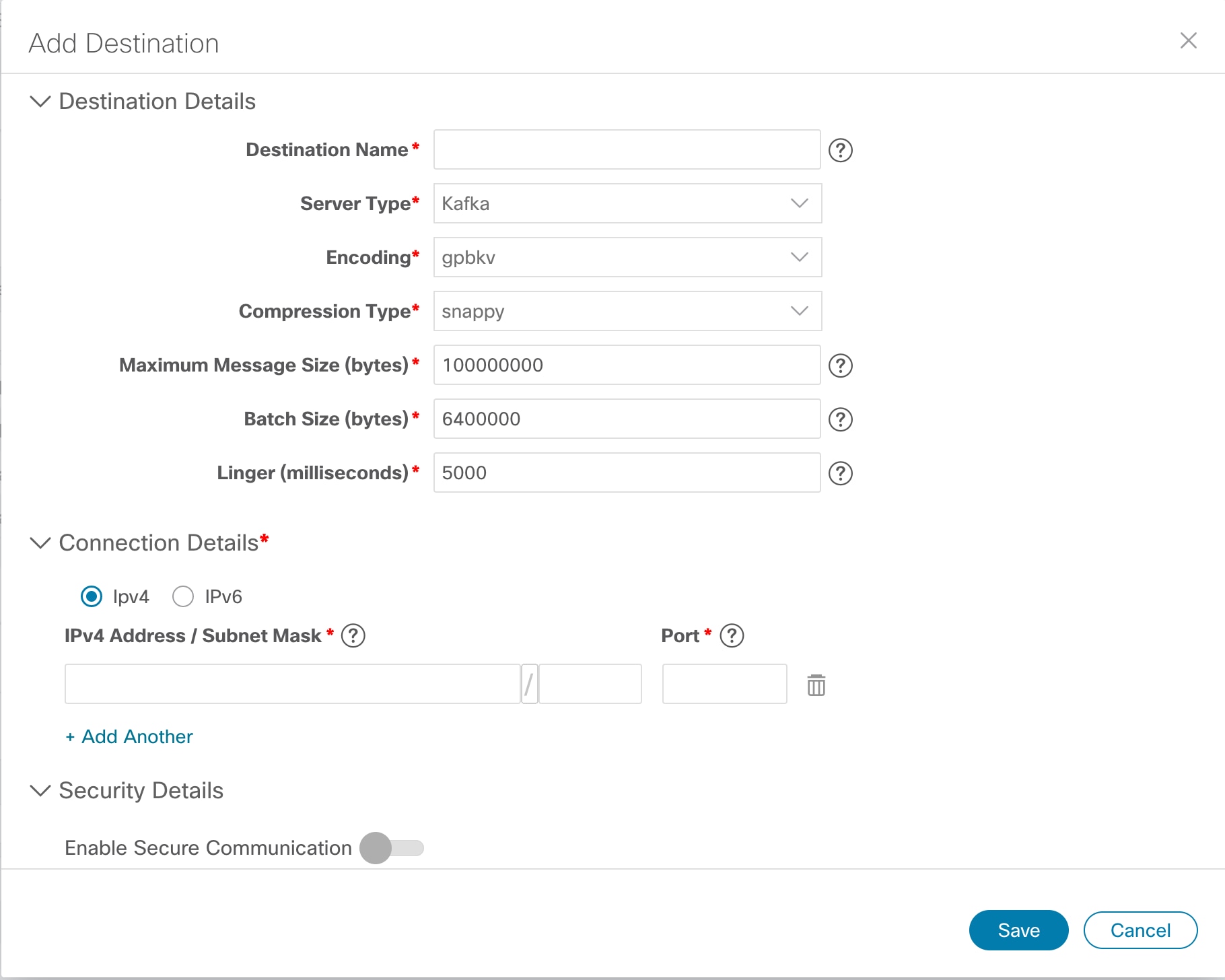
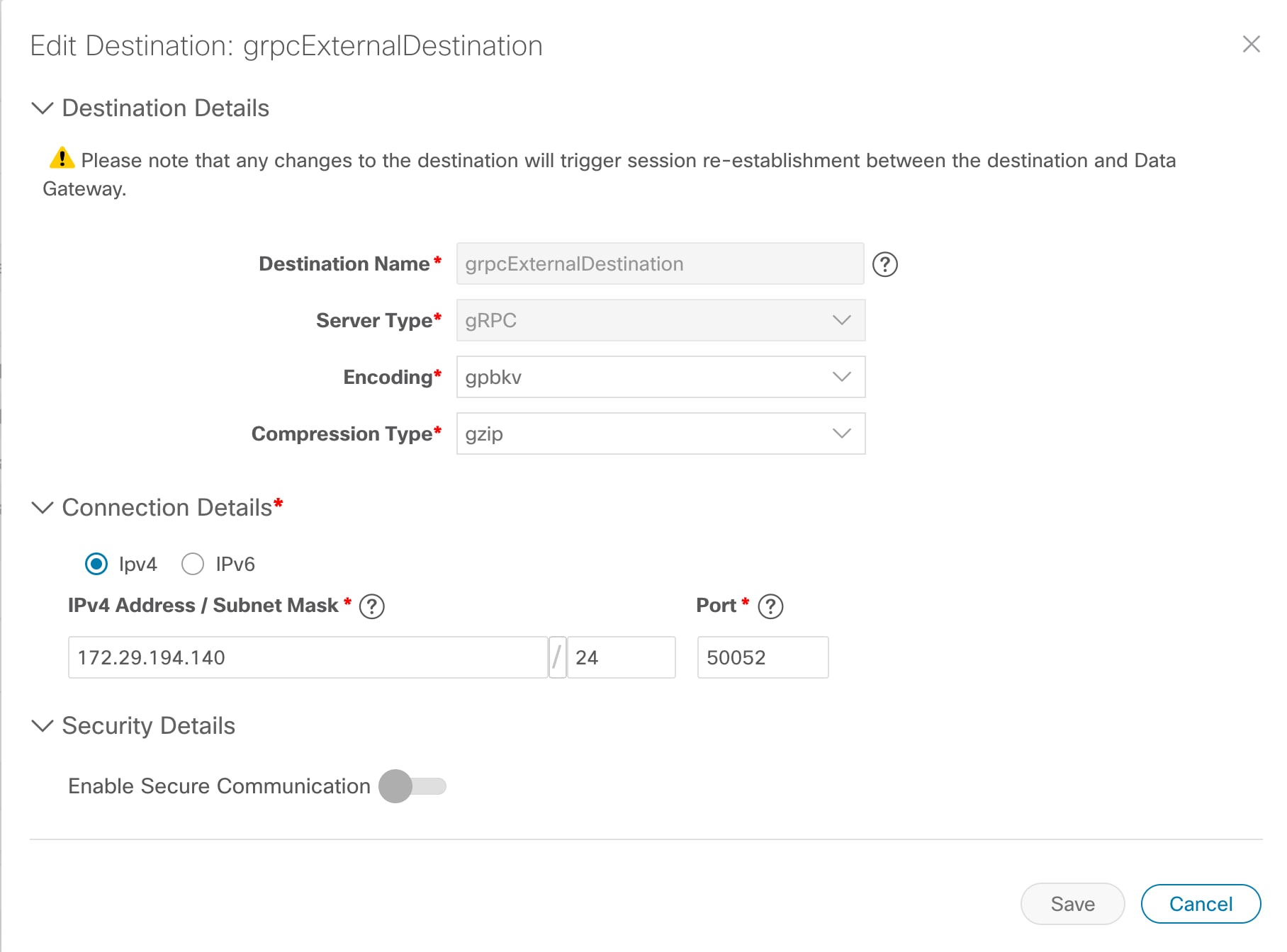
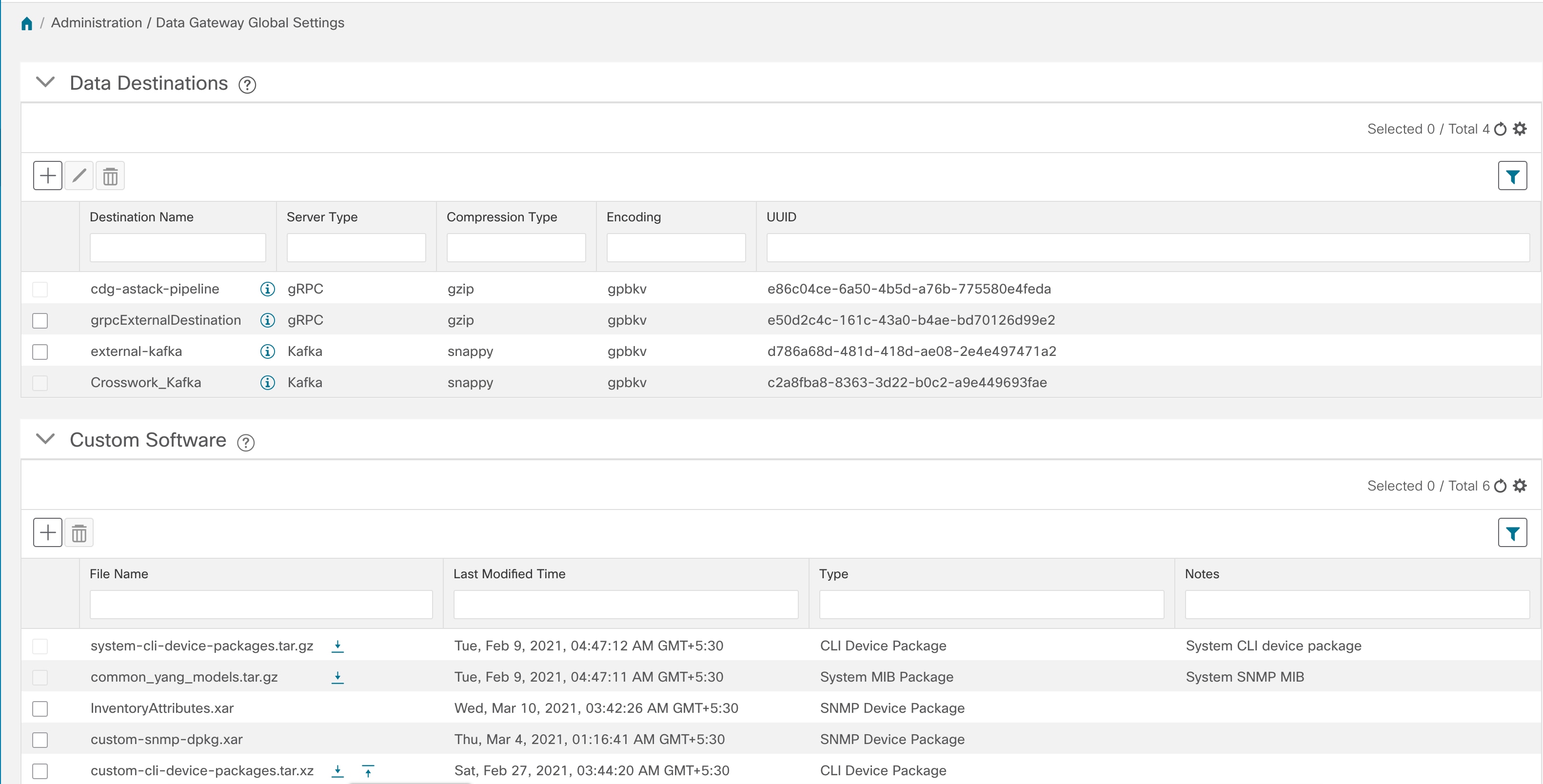
Once you assign a Cisco Crosswork Data Gateway VM to a pool, a virtual Cisco Crosswork Data Gateway gets created automatically and is visible under Data Gateways tab. You can then attach or detach devices to the pool, create external data destinations and run collection jobs to forward data to the preferred data destination.
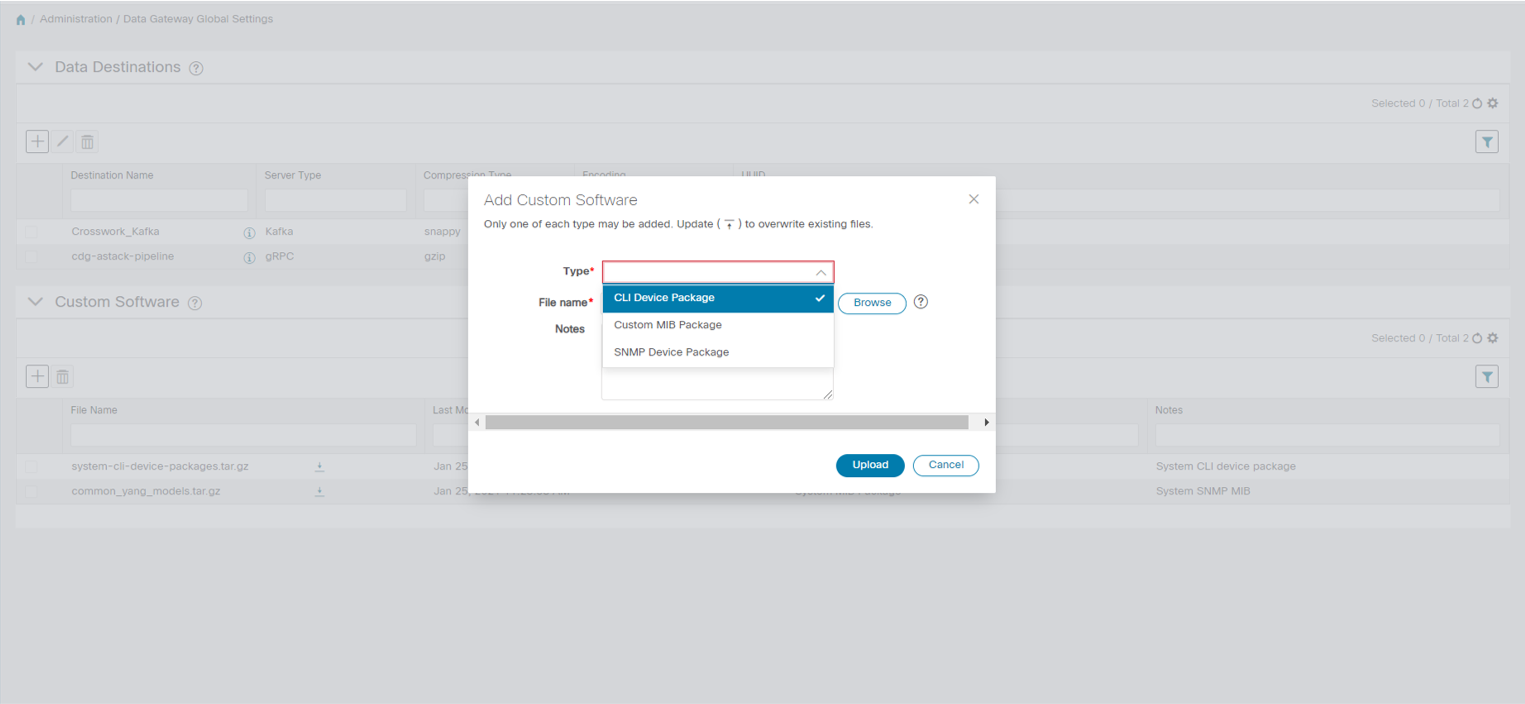
Cisco Crosswork includes MIB files and device model definitions for many Cisco products and provides the ability to load custom software packages in order to add data collection capability for currently unsupported devices.
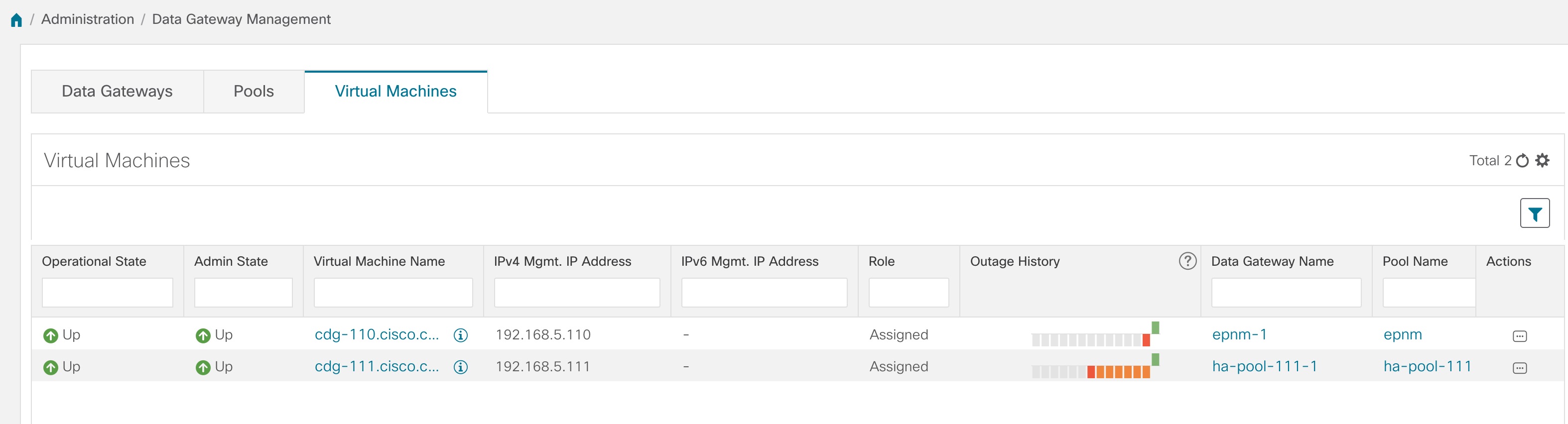
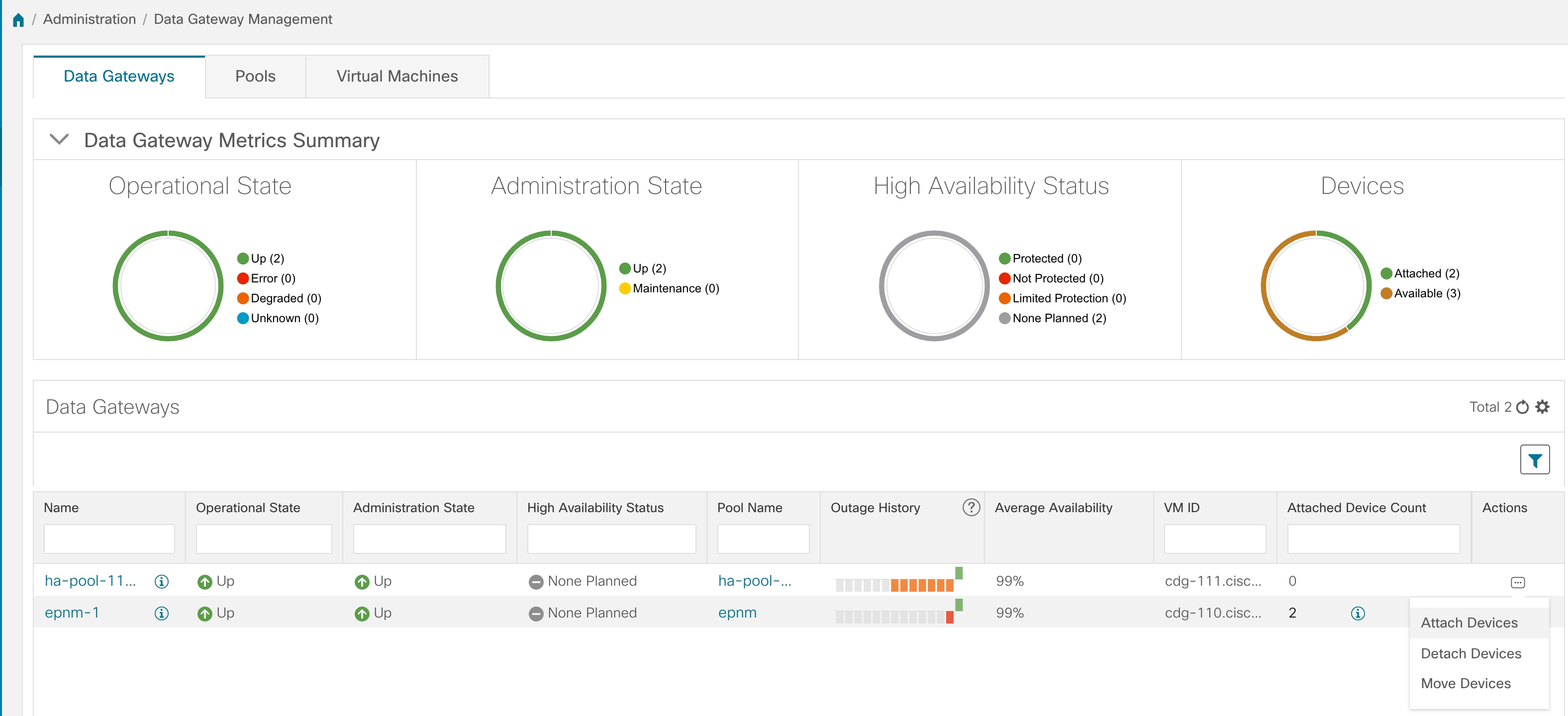
Cisco Crosswork Data Gateway features can be accessed the Cisco Crosswork main menu. To open Cisco Crosswork Data Gateway management view, choose Administration > Data Gateway Management from the left navigation bar.
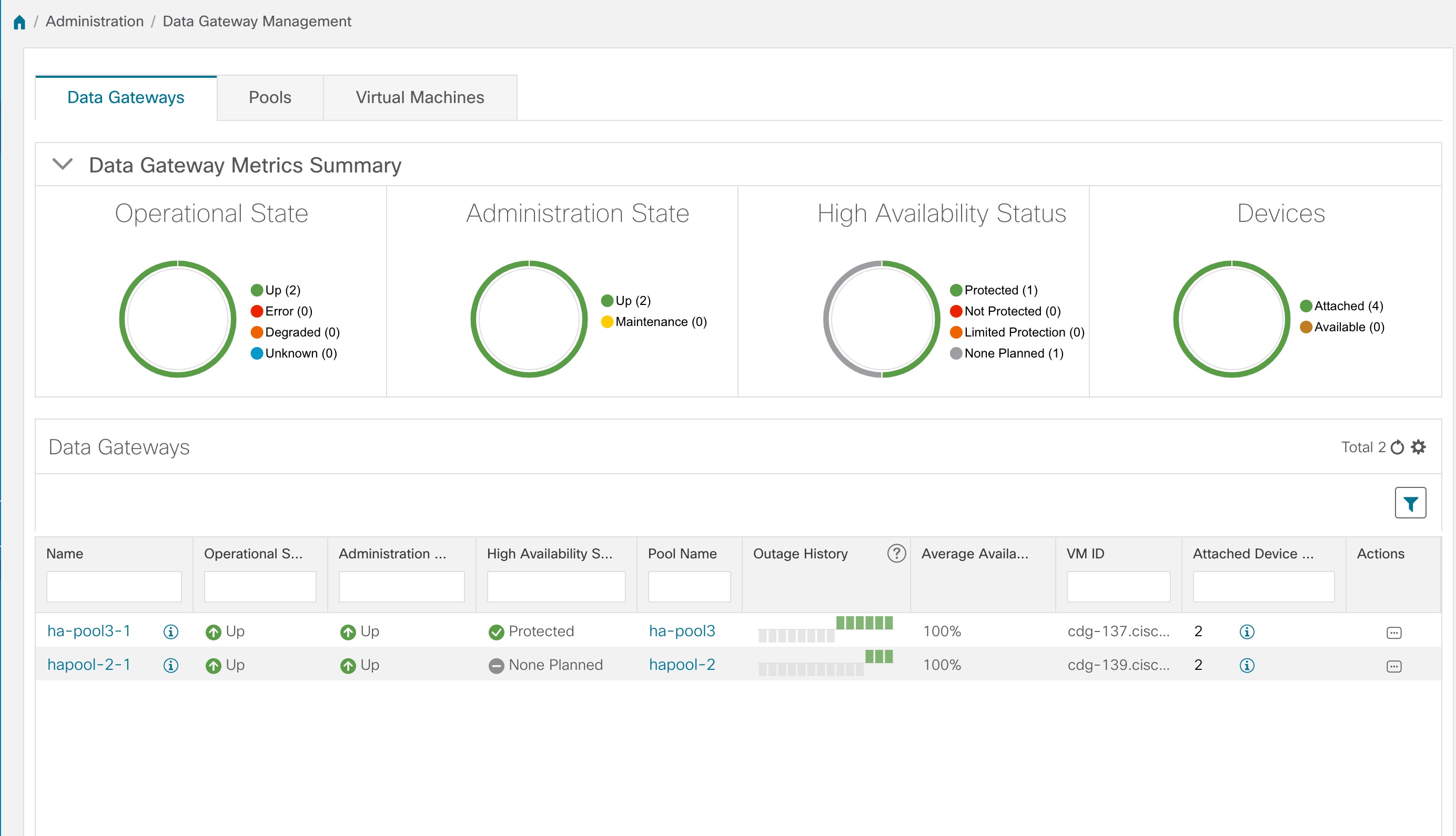
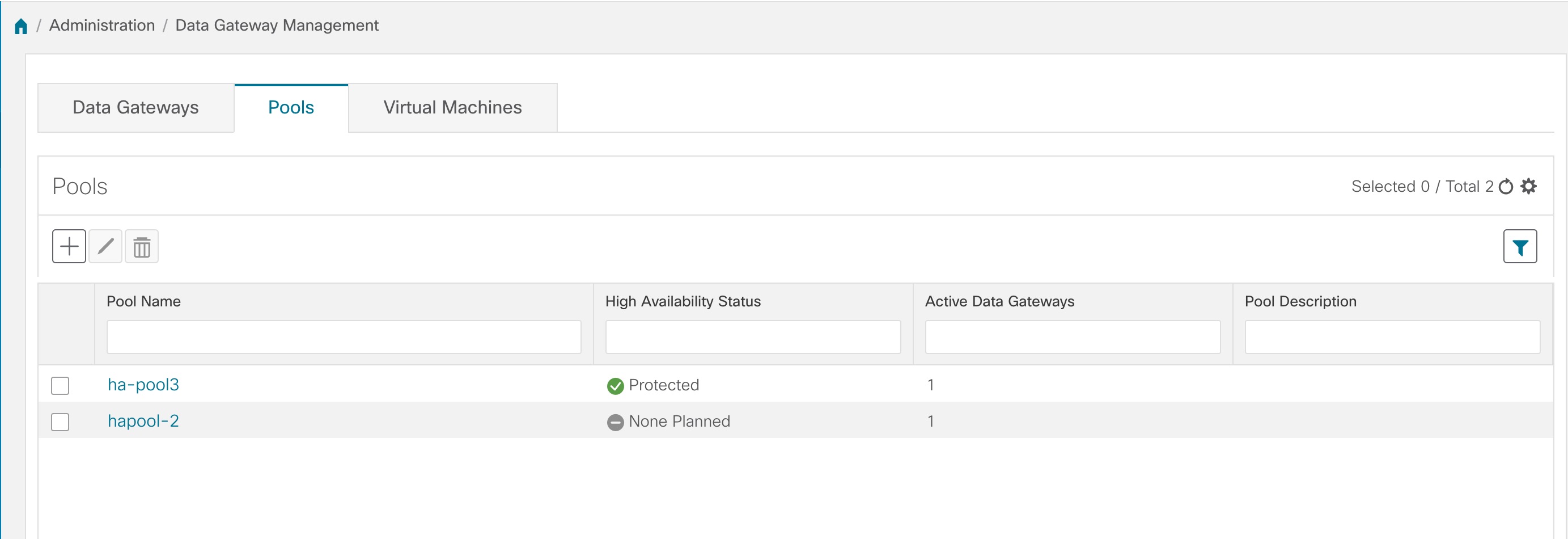
Data Gateway Management page has three tabs:
-
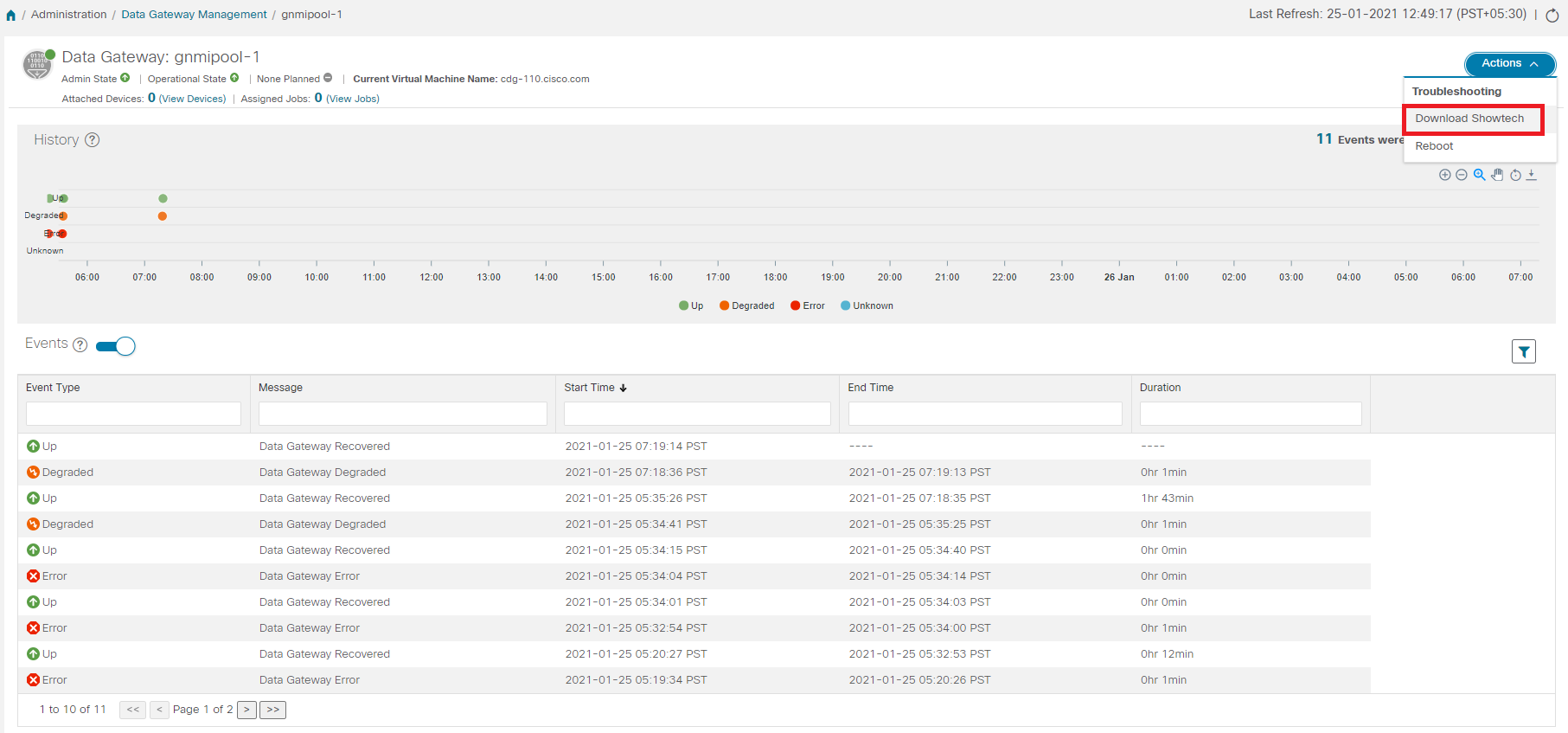
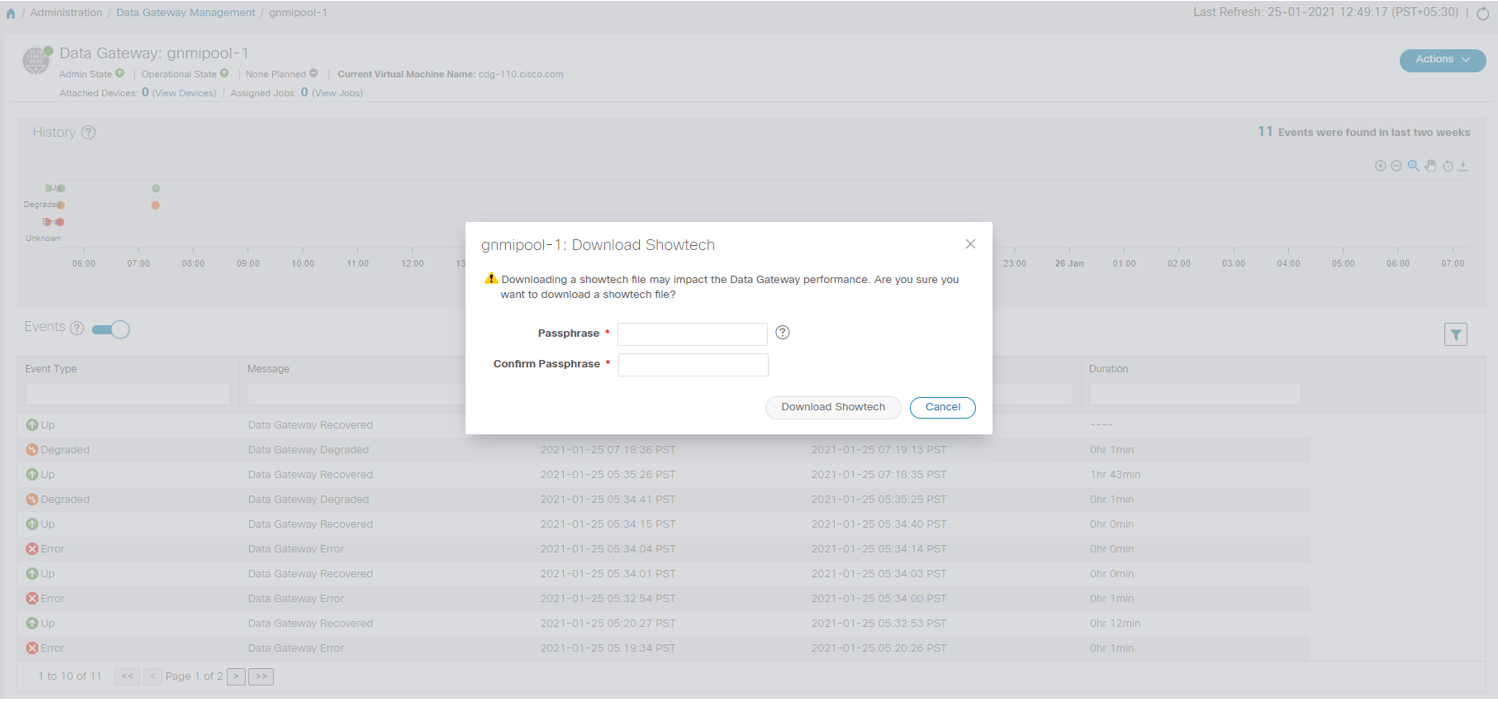
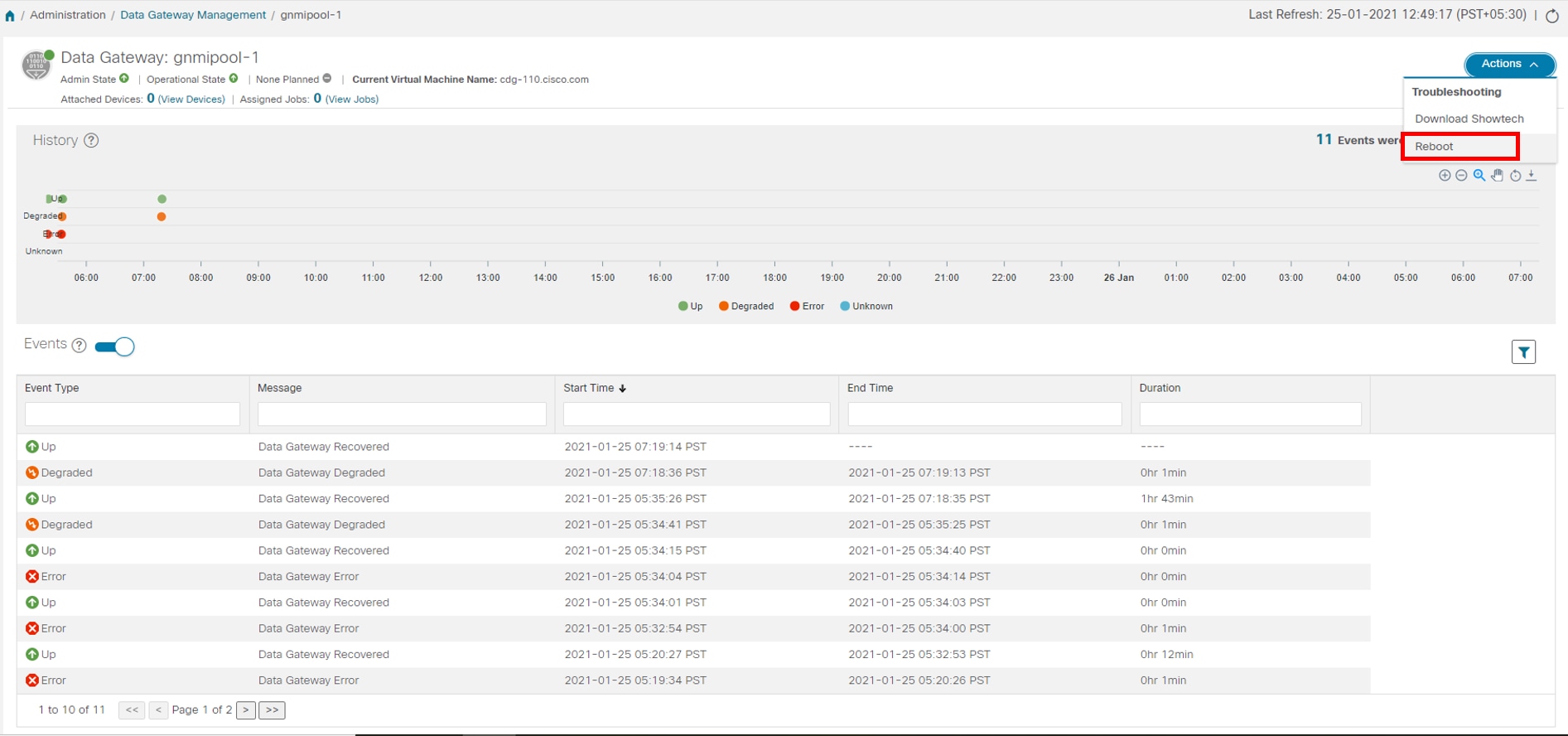
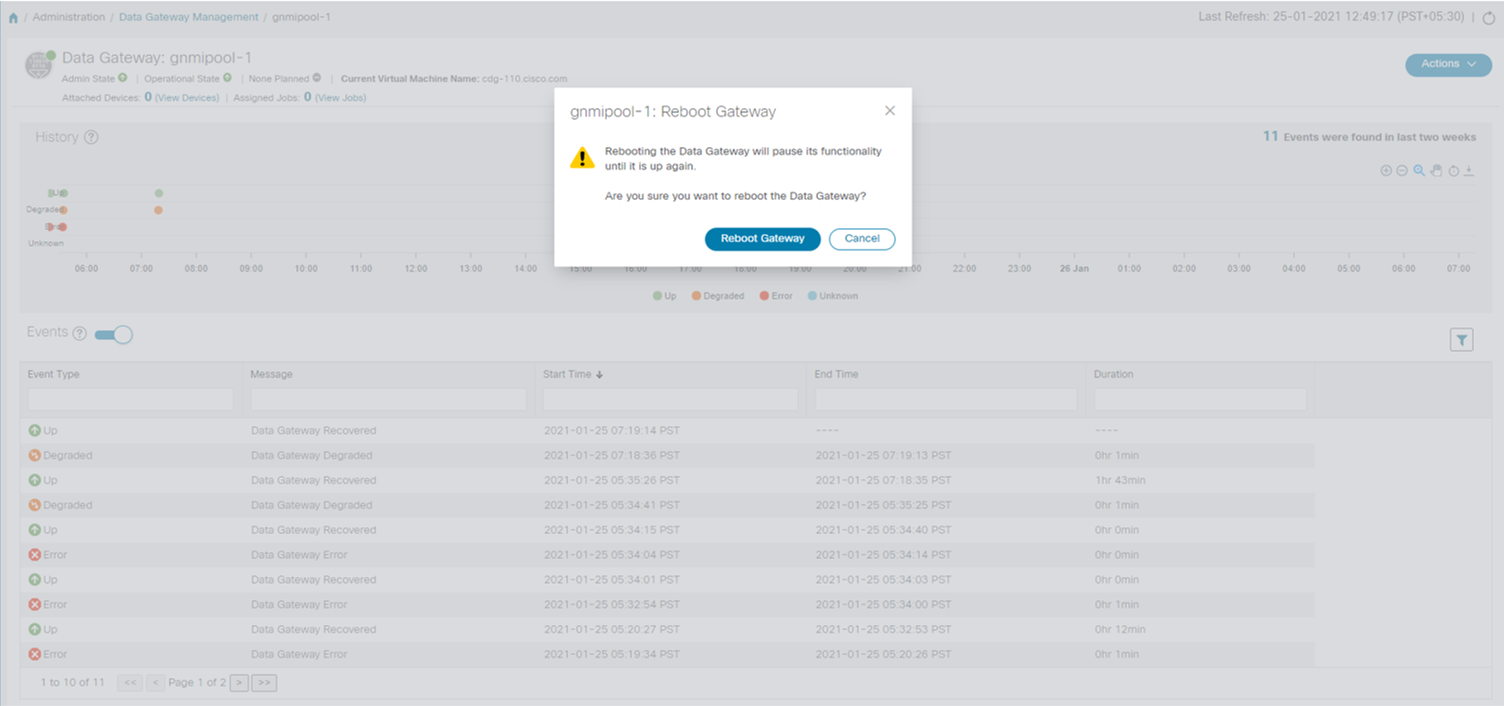
Data Gateways: Displays details of the virtual Cisco Crosswork Data Gateway instances.
-
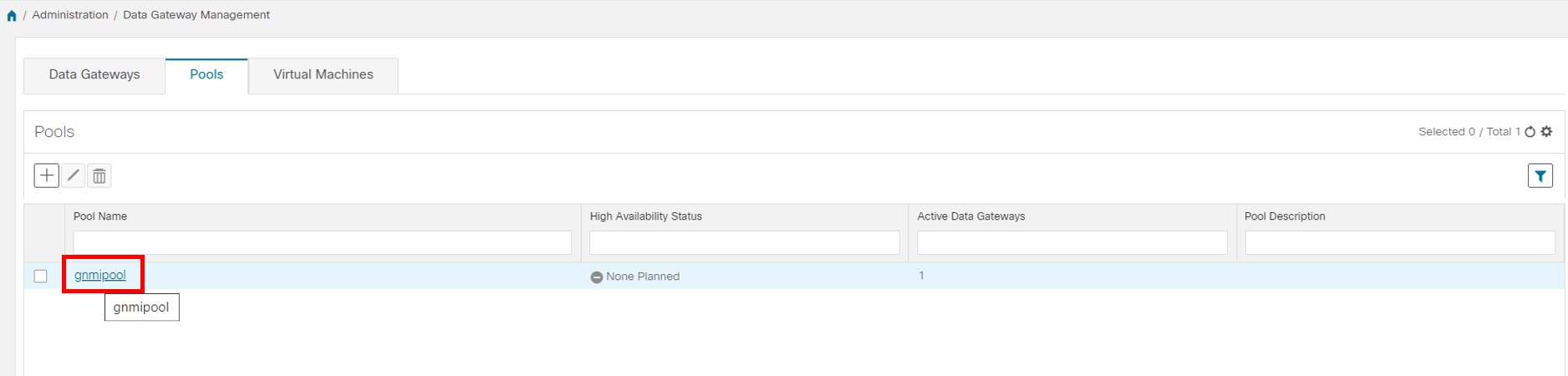
Pools: Manage Cisco Crosswork Data Gateway pools.
-
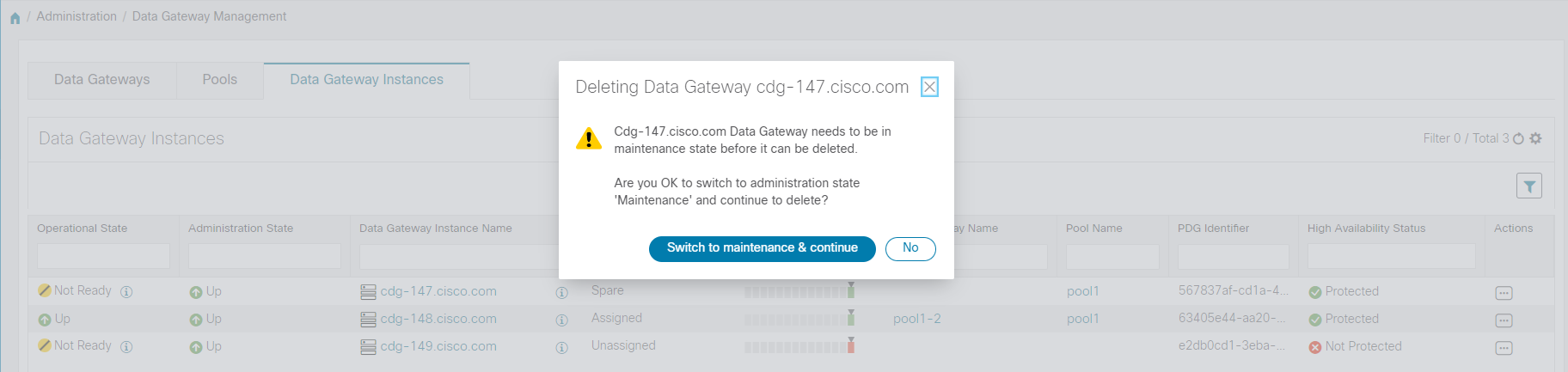
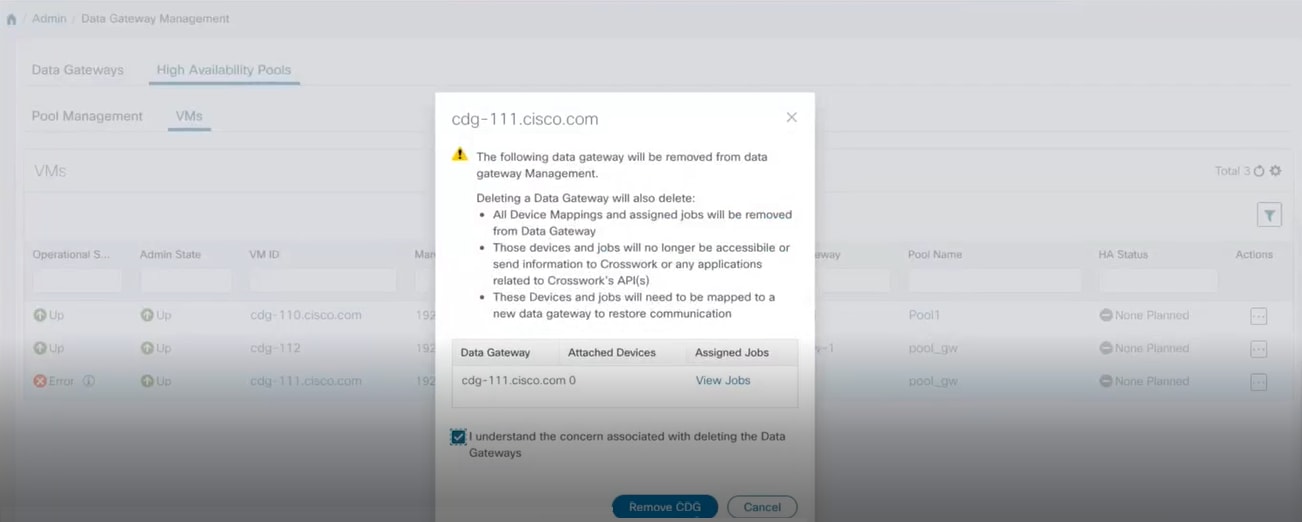
Virtual Machines: Manage physical Cisco Crosswork Data Gateway VMs.


 button next to its name in the File Name column.
button next to its name in the File Name column.
 Feedback
Feedback