Traffic Interception Methods
This section contains the following topics:
About Traffic Interception Methods
Prerequisities for configuring traffic interception for Cisco WAAS
-
Complete a basic initial installation and configuration of your Cisco WAAS network, as described in the Cisco Wide Area Application Services Quick Configuration Guide.
-
For detailed command syntax information for any of the Cisco WAAS CLI commands in this chapter, see Cisco Wide Area Application Services Command Reference.
-
For more information about WCCP see the Cisco IOS documentation.
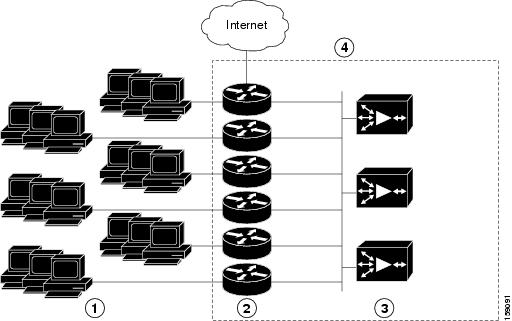
In a Cisco WAAS network, traffic between clients in the branch offices and the servers in the data center can be redirected to WAEs for optimization, redundancy elimination, and compression. Traffic is transparently intercepted and redirected to WAEs based on policies that have been configured on the routers or on an AppNav Controller (ANC). The network elements that transparently redirect requests to a local WAE can be a router using WCCP Version 2 or PBR to redirect traffic to the local WAE or a Layer 4 to Layer 7 switch, for example, the Catalyst 6500 series Content Switching Module (CSM) or Application Control Engine (ACE).
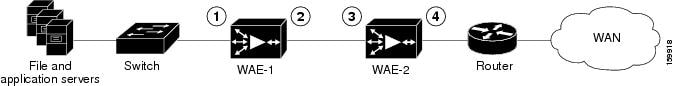
Alternately, you can intercept traffic directly by using the inline mode with a WAE that has a Cisco WAE Inline Network Adapter or Interface Module. When equipped with a Cisco AppNav Controller Interface Module, a WAVE appliance or cluster can intercept network traffic through WCCP or inline mode, and based on flow policies, distribute that traffic to one or more WAEs (WAAS nodes) for optimization.
The following table summarizes the transparent traffic interception methods that are supported in your Cisco WAAS network.
|
Method |
Description |
||
|---|---|---|---|
|
WCCP Version 2 |
Used for transparent interception of application traffic and Common Internet File System (SMB) traffic. Used in branch offices and data centers to transparently redirect traffic to the Cisco WAAS devices. The traffic is transparently intercepted and redirected to the local WAE or ANC by a WCCP-enabled router or a Layer 3 switch. You must configure WCCP on the router and WAE in the branch office and the router and WAE in the data center. For more information, see the following sections: |
||
|
PBR |
Used in branch offices used for wide area application optimization. The branch office router is configured to use PBR to transparently intercept and route both client and server traffic to the WAE that resides in the same branch office. In data centers, used for data center application optimization. The data center router or Layer 3 switch can be configured to use PBR to transparently intercept and route client and server traffic to WAEs within the data center. PBR, however, does not support load balancing across multiple WAEs, such as WCCP does. PBR does not support load balancing when you use a hardware load balancer, such as the Cisco CSM or Cisco ACE. See Using Policy-Based Routing Interception. |
||
|
Inline |
The WAE physically and transparently intercepts traffic between the clients and the router. To use this mode, you must use a Cisco WAAS device with the Cisco WAE Inline Network Adapter, Cisco Interface Module, or Cisco AppNav Controller Interface Module. See Using Inline Mode Interception. |
||
|
vPATH |
|
||
|
AppNav Controller |
For WAEs that are part of an AppNav deployment and are configured as WAAS nodes in an AppNav Cluster, you must configure them to use the appnav-controller interception method. This configuration allows WAEs to receive and optimize traffic that is intercepted and distributed by the AppNav Controllers. See Configuring AppNav Interception. |
||
|
ACE or CSM |
Cisco Application Control Engine (ACE) or Catalyst 6500 series Content Switching Module (CSM) installed in the data center for data center application optimization. The ACE or CSM allows for both traffic interception and load balancing across multiple WAEs within the data center. |
Guidelines for Configuring Traffic Interception
Note these guidelines when configuration traffic interception for your Cisco WAAS network:
-
ISR-WAAS devices support only the AppNav Controller interception method.
-
For Cisco vWAAS in Azure, the supported traffic interception method is PBR (Police-Based Routing); vWAAS in Azure does not support WCCP or AppNav interception methods.
-
Pass-through traffic does not benefit from optimization. For example, SSH port 22 has minimal traffic volume, so would not benefit by optimizing TCP flows.
-
If you use Microsoft System Center Configuration Manager with Preboot Execution Environment (SCCM/PXE), we recommend the following configurations for the ports that carry SCCM/PXE traffic: port 80, port 443, and port 445.
-
port 80: Communicates with the distribution point. Configure for pass-through traffic.
-
port 443: Communicates with the distribution point. Configure for pass-through traffic.
-
port 445: Used for software package distribution data transfer. Configure for traffic optimization.
Without these configurations you may see the error message PXE error code 80070056.
-
WCCP Interception
The Cisco WAAS software uses the WCCP standard, Version 2, for redirection. The main features of WCCP Version 2 include support for the following:
-
Up to 32 WAEs per WCCP service
-
Up to 32 routers per WCCP service
-
Authentication of protocol packets
-
Redirection of non-HTTP traffic
-
Packet return (including generic routing encapsulation [GRE], allowing a WAE to reject a redirected packet and to return it to the router to be forwarded)
-
Masking for improved load balancing
-
Multiple forwarding methods
-
Packet distribution method negotiation within a service group
-
Command and status interaction between the WAE and a service group
 Note |
WCCP works only with IPv4 networks. |
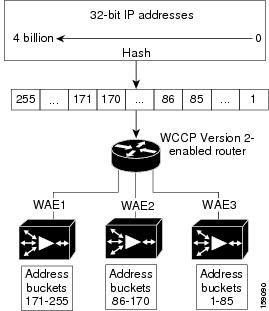
Cisco WAAS software supports the WCCP TCP promiscuous mode service (services 61 and 62 by default, though these service IDs are configurable). This WCCP service requires that WCCP Version 2 is running on the router and the WAE.
The TCP promiscuous mode service is a WCCP service that intercepts all TCP traffic and redirects it to the local WAE.
The Cisco WAAS software also supports service passwords, WAE failover, and interception ACLs.
Many Cisco routers and switches can be configured and enabled with WCCP Version 2 support for use with Cisco WAAS devices.
Many legacy Cisco routers, including the 2500, 2600, and 3600 routers, have far less processing power and memory than newer routing platforms, such as the Integrated Services Router (ISR) models 2800 and 3800. As such, the use of WCCPv2 or PBR may cause a high level of CPU utilization on the router and cause erratic behavior. WAAS can be configured to work with these routers, but not to the same levels of performance or scalability as can be found with newer routing platforms. The Cisco ISR is the routing platform of choice for the branch office.
If you are experiencing erratic behavior, such as the WAE being ejected from the service group, enable fair queuing, weighted fair queuing, or rate limiting on all physical interfaces on the router that connect to users, servers, WAEs, and the WAN. Fair queuing cannot be configured on subinterfaces, and should be configured on both ingress and egress physical interfaces. If another form of queuing is already configured on the LAN or WAN interfaces other than fair queuing, and provides similar fairness, it should be sufficient.
Additionally, limit the amount of bandwidth that can be received on the LAN-side interface of the router, to help the router keep its interface queues less congested and provide better performance and lower CPU utilization. Set the maximum interface bandwidth on the router to no more than 10 times the WAN bandwidth capacity. For instance, if the WAN link is a T1, the LAN interface and WAE LAN interface bandwidth should be throttled to 10 * T1 = 10 * 1.544 Mbps, or approximately 15 Mbps. See the Cisco IOS documentation for more information.
This section contains the following topics:
Configuring WCCP Version 2
This section contains the following topics:
Guidelines for Configuring WCCP Version 2
When you configure transparent redirection on a WAE using WCCP Version 2, follow these guidelines:
-
Creating WCCP Passwords
Use WCCP passwords to avoid denial-of-service attacks. For more information, see Setting a Service Group Password on a Router.
-
Configuring WCCP and Routers and WAEs
Configure the routers and WAEs to use WCCP Version 2 instead of WCCP Version 1 because WCCP Version 1 supports only web traffic (port 80).
To configure basic WCCP, enable the WCCP service on at least one router in your network and on the WAE or ANC that you want the traffic redirected to. It is not necessary to configure all the available WCCP features or services to get your WAE up and running. For an example of how to complete a basic WCCP configuration on routers and WAEs in a branch office and data center, see the Cisco Wide Area Application Services Quick Configuration Guide.
Cisco Express Forwarding (CEF) is required for WCCP and must be enabled on the router.
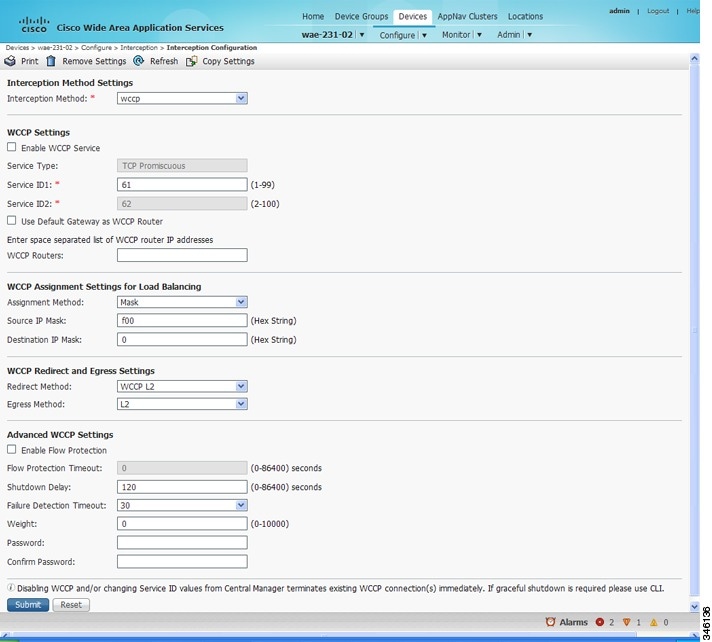
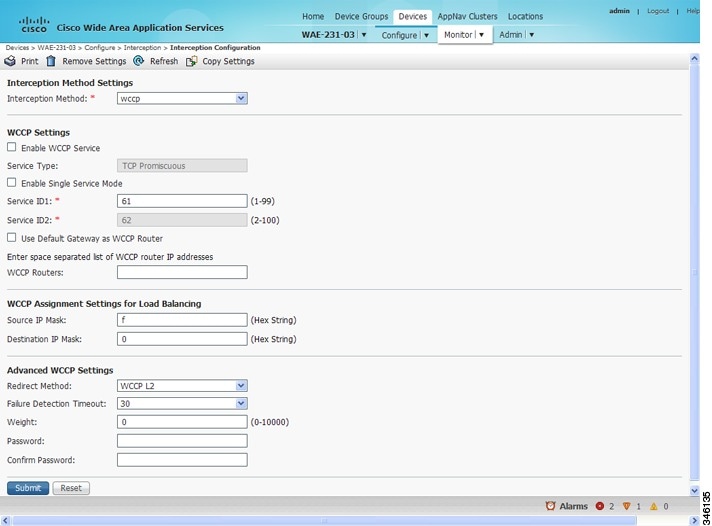
Use Cisco WAAS CLI commands to configure basic WCCP on both the routers and the WAEs or ANCs. Alternatively, you can use CLI commands to configure the router for WCCP and use the Cisco WAAS Central Manager to configure basic WCCP on the Cisco WAEs or Cisco ANCs. In the configuration example provided in the Cisco Wide Area Application Services Quick Configuration Guide, the wccp global configuration command is used to configure basic WCCP on the Cisco WAEs or ANCs.
We recommend that you use the Cisco WAAS CLI to complete the initial basic configuration of WCCP on your first branch WAE and data center WAE, as described in the Cisco Wide Area Application Services Quick Configuration Guide. After you have verified that WCCP transparent redirection is working properly, you can use the Cisco WAAS Central Manager to modify this basic WCCP configuration or configure additional WCCP settings, for example, load balancing, for a WAE. For more information, see Configuring WCCP on WAEs. After you have configured basic WCCP on the router, you can configure advanced WCCP features on the router, as described in Configuring Advanced WCCP Features on Routers.
-
Configuring WCCP and Branch WAEs
Branch WAEs must not have their packets encrypted or compressed and should be part of the inside Network Address Translation (NAT) firewall if one is present.
Place branch WAEs on the client side of the network to minimize client-side packets through the router.
-
Configuring WCCP Interception and Redirection
Intercept and redirect packets on the inbound interface whenever possible.
Use Layer 2 redirection as the packet forwarding method if you are using Catalyst 6500 series switches or Cisco 7600 Series Routers. Use Layer 3 GRE packet redirection if you are using any other Cisco router.
Use WCCP redirect lists for new implementations to limit client or server populations. For more information, see Configuring IP Access Lists on a Router.
Configure the WAE to accept redirected packets from one or more WCCP-enabled routers.
When you add a new router to an existing WCCP router farm or WCCP service group, the new router will reset existing connections. Until WCCP re-establishes path redirections and assignments, packets are sent directly to the client (as expected).
The router must support the redirect and return methods configured on the WAE. If the router does not support the configured methods, the WAE will not join the WCCP router farm. If you have a mix of routers in the farm, only those routers that support the configured methods will join the farm.
-
Configuring WCCP GRE and Generic GRE
Use WCCP GRE or generic GRE as the egress method to place WAEs on the same VLAN or subnet as clients and servers. This topology is not allowed when using the IP forwarding egress method.
-
Configuring WCCP Service Farms
To ensure consistency among WAEs, we recommend that you configure WCCP settings on one device and then use the Copy Settings taskbar icon from within the WCCP configuration window to copy the settings to other devices in your network. You should copy the settings only to the WAEs in the same WCCP service farm, AppNav Controller group (ANCG), or WAAS node group (WNG), because WCCP settings may have to be different in different farms or service groups.
The WAE joins the WCCP farm only if the assignment method configured on the WAE is supported by the router. (The strict assignment method is always enforced with Version 4.4.1 and later.)
A WAE joins a WCCP farm only if it is seen by all the configured routers in the farm. If there is a link failure in any one of the routers, the farm reconfigures, and the WAE is removed from the farm.
All the WAEs in a WCCP farm must use the same pair of WCCP service IDs (the default is 61 and 62), and these IDs must match all the routers that are supporting the farm. A WAE with different WCCP service IDs is not allowed to join the farm, and an alarm is raised. Likewise, all the WAEs in a farm must use the same value for failure detection timeout. A WAE raises an alarm if you configure it with a mismatching value.
-
Configuring WCCP and TCP Promiscuous Mode
After enabling WCCP on the router, configure the TCP promiscuous mode service on the router and the WAE, as described in the Cisco Wide Area Application Services Quick Configuration Guide. The service IDs are configurable on the WAE; you choose a pair of numbers that are different from the default of 61 and 62 to allow the router to support multiple WCCP farms because the WAEs in different farms can use different service IDs. The router configuration must use WCCP service IDs that match those configured on the WAEs in each farm it is supporting.
For the WAE to function in TCP promiscuous mode, the WAE uses WCCP Version 2 services 61 and 62 (the service IDs are configurable). These two WCCP services are represented by the canonical name tcp-promiscuous on the Cisco WAE.
-
Configuring WCCP, HSRP, and VRRP
When you configure WCCP for use with the Hot Standby Router Protocol (HSRP), you must configure the WAE with the HSRP or the Virtual Router Redundancy Protocol (VRRP) virtual router address as its default gateway, and the WAE WCCP router list with the primary address of the routers in the HSRP group.
-
WCCP Scalability
Virtual routing and forwarding-aware (VRF) WCCP scalability is as follows:
-
The maximum number of WAEs supported by a single VRF instance is 32.
-
The maximum number of VRF instances supported by the router is router dependent.
-
VRF-aware WCCP is supported only on specific releases of Cisco IOS software. Ensure that the router is running a release of Cisco IOS software that supports VRF-aware WCCP.
-
Each VRF instance has independent assignment, redirection, and return methods.
-
-
WCCP and Cisco WAAS Appnav Deployment
In a WAAS AppNav deployment, enable WCCP only on the ANC devices that are intercepting traffic and distributing it to the optimizing WAAS nodes (WNs). Configure WNs that are a part of the AppNav Cluster, with the appnav-controller interception method.
-
WCCP and MSS
To reduce the number of dropped packets in a network where WCCP L2 is deployed, we recommend that you configure the maximum segment size (MSS) to 1406 bytes on the WAAS nodes using the Cisco WAAS Central Manager. For more information on modifying MSS, see Modifying the Acceleration TCP Settings in the chapter "Configuring Application Acceleration."
Guidelines for File Server Access Methods
Some file servers have several network interfaces and can be reached through multiple IP addresses. For these server types, you must add all the available IP addresses to the branch WAE’s WCCP accept list. This situation prevents a client from bypassing the branch WAE by using an unregistered IP address.
Some file servers have several NetBIOS names and only one IP address. Cisco WAAS uses that name to perform NetBIOS negotiations between the data center WAE and the file server, and to create resources in the cache. If a file server uses multiple NetBIOS names to represent virtual servers (possibly with different configurations) and has one NetBIOS name that is identified as the primary server name, put that name in the server list before the other names.


 Feedback
Feedback