Configure Machine and User Authentication with EAP-TTLS
Available Languages
Download Options
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Contents
Introduction
This document describes how to configure machine and user authentication with EAP-TTLS (EAP-MSCHAPv2) on Secure Client NAM and Cisco ISE.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics before proceeding with this deployment:
- Cisco Identity Services Engine (ISE)
- Secure Client Network Analysis Module (NAM)
- EAP Protocols
Components Used
The information in this document is based on these software and hardware versions:
- Identity Services Engine (ISE) version 3.4
- C9300 switch with Cisco IOS® XE Software, Version 16.12.01
- Windows 10 Pro Version 22H2 Built 19045.3930
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Network Topology
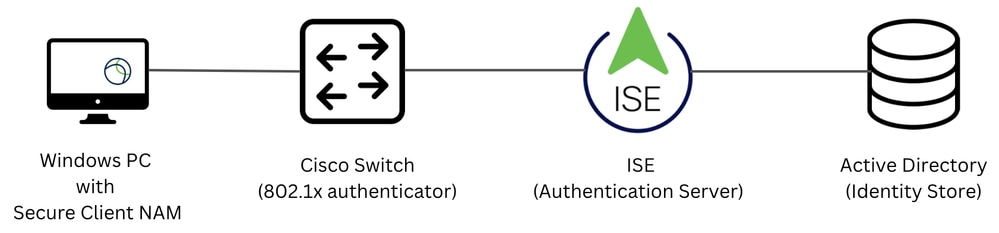 Network Topology
Network Topology
Configure
Configurations
Part 1: Download and Install Secure Client NAM (Network Access Manager)
Step 1. Go to Cisco Software Download. In the product search bar, enter Secure Client 5.
This configuration example uses version 5.1.11.388. The installation is performed using the pre-deploy method.
On the download page, locate and download Cisco Secure Client Pre-Deployment Package (Windows).
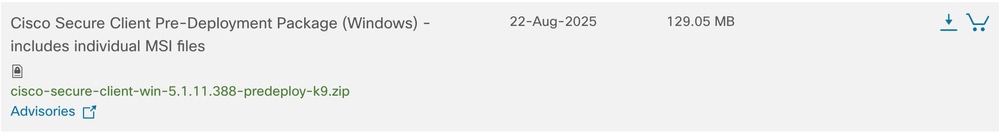 Predeployment zip file
Predeployment zip file

Note: Cisco AnyConnect has been deprecated and is no longer available on the Cisco Software Download site.
Step 2. Once downloaded and extracted, clickSetup.
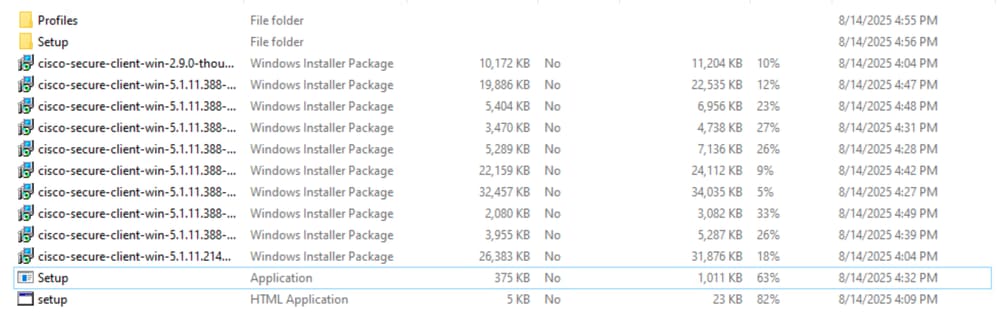 Predeployment Zip File
Predeployment Zip File
Step 3. Install theCore & AnyConnect VPN, Network Access Manager, and theDiagnostics and Reporting Toolmodules.
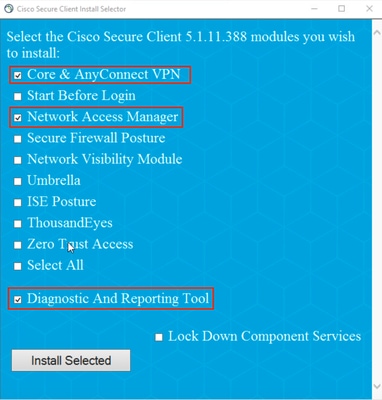 Secure Client Installer
Secure Client Installer
Click Install Selected.
Step 4. A reboot is required after installation. Click OK and restart your device.
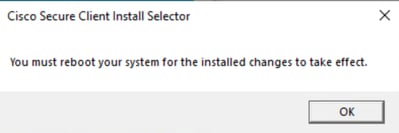 Reboot Required Pop-up
Reboot Required Pop-up
Part 2: Download and Install Secure Client NAM Profile Editor
Step 1. The Profile Editor can be found on the same downloads page as the Secure Client. This configuration example uses version 5.1.11.388.
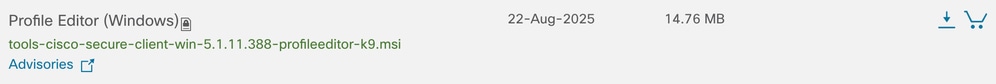 Profile Editor
Profile Editor
Download and install the Profile Editor.
Step 2. Run the MSI file.
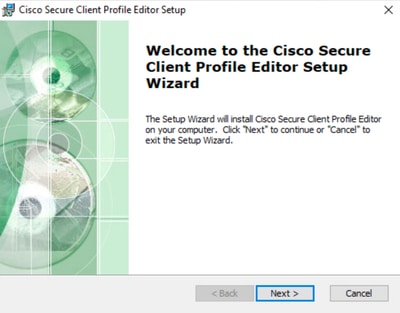 Profile Editor Setup Start
Profile Editor Setup Start
Step 3. Use the Typical setup option and install the NAM Profile Editor.
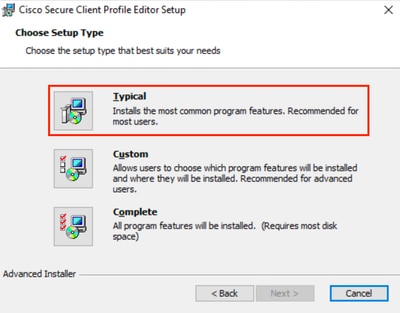 Profile Editor Setup
Profile Editor Setup
Part 3: Allow Windows Cache Credentials to be Accessed by NAM
By default, on Windows 10, Windows 11, and Windows Server 2012, the operating system prevents Network Access Manager (NAM) from retrieving the machine password required for machine authentication. As a result, machine authentication using the machine password does not work unless a registry fix is applied.
To enable NAM to access the machine credentials, apply the Microsoft KB 2743127 fix on the client desktop.

Caution: Editing the Windows registry incorrectly can cause serious problems. Make sure you back up the registry before making changes.
Step 1. In the Windows search bar, enter regedit, and then click Registry Editor.
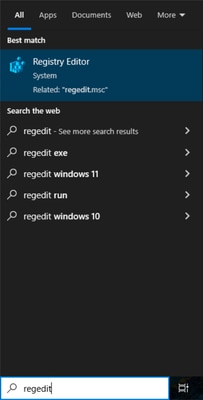 Registry Editor in Search Bar
Registry Editor in Search Bar
Step 2. In the Registry Editor, navigate to HKEY_LOCAL_MACHINE > System > CurrentControlSet > Control > Lsa.
Step 3. Right-click Lsa, choose New > DWORD (32-bit) Value, and name it LsaAllowReturningUnencryptedSecrets.
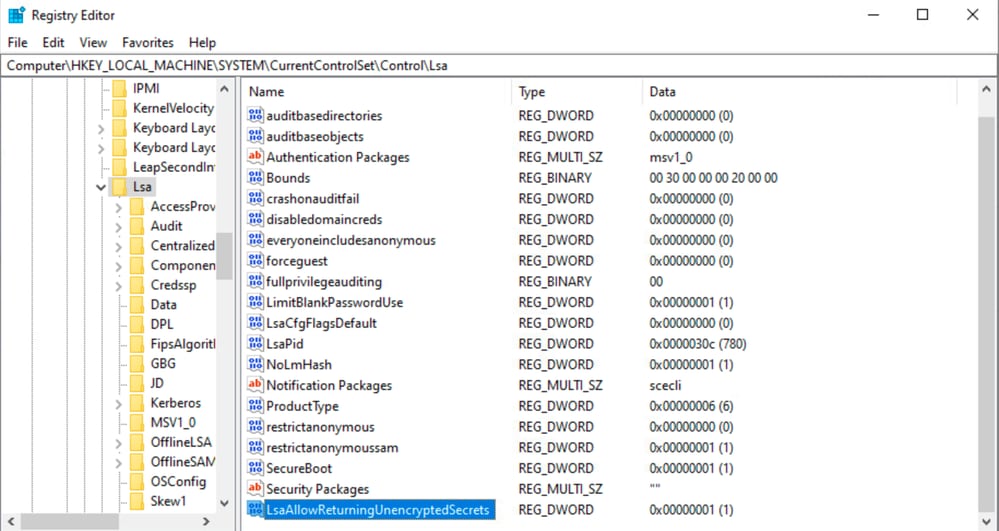 Lsa Registry DWORD
Lsa Registry DWORD
Step 4. Double-click LsaAllowReturningUnencryptedSecrets, set the value to 1, and then click OK.
 Edit DWORD Window
Edit DWORD Window
Part 4: Configure NAM Profile using NAM Profile Editor
Step 1. Open the NAM Profile Editor.
Step 2. In Client Policy:
- Ensure that Manage Wired (802.3) Media is enabled.
- If you are using WiFi, ensure that Manage Wi-Fi (wireless) Media is enabled with validation of WPA/WPA2/WPA3 handshake.
- Leave all other options at their default settings.
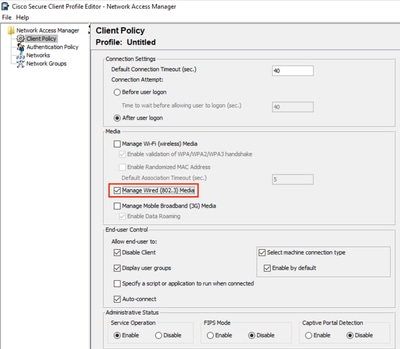 NAM Profile Editor Client Policy
NAM Profile Editor Client Policy
Step 3. In Authentication Policy:
-
Ensure that the required methods are selected.
-
In this example, use EAP-TTLS with EAP-MSCHAPv2. Hence, ensure that these methods are selected.
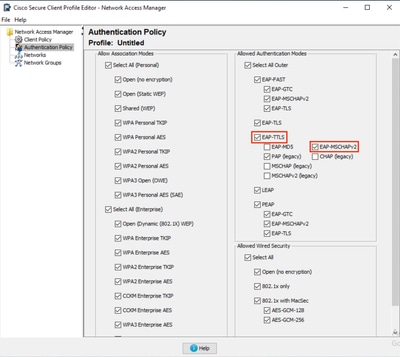 NAM Profile Editor Authentication Policy
NAM Profile Editor Authentication Policy
Part 5: Configure Wired Network for EAP-TTLS
Step 1. Under Networks, a default wired network is present. For this example, create a new network for EAP-TTLS.
Click Add to create a new network.
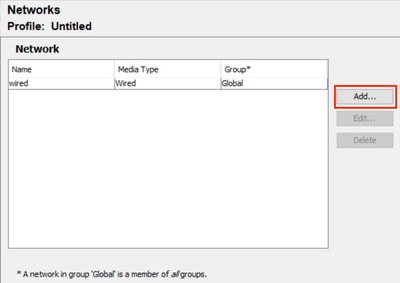 NAM Profile Editor Default Network
NAM Profile Editor Default Network
Name theNetworkprofile. In this example, the network is named EAP-TTLS.
SelectGlobalforGroup Membership. Select Wired (802.3)Network under Network Media and click Next.
 NAM Profile Editor New Network
NAM Profile Editor New Network
Step 2. In Security Level, choose Authenticating Network (for 802.1X authentication).
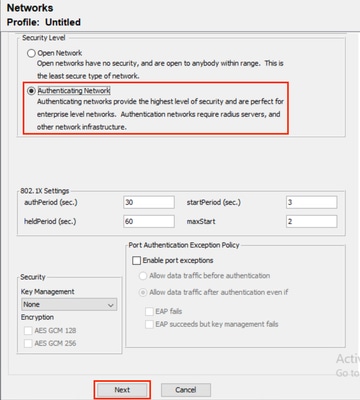 NAM Profile Editor Network Configuration
NAM Profile Editor Network Configuration
Step 3. For Connection Type, choose Machine and User Connection. Click Next.
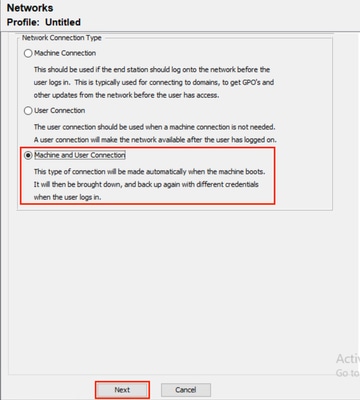 NAM Profile Editor User and Machine Authentication
NAM Profile Editor User and Machine Authentication
Step 4. Select EAP-TTLS as the general EAP Method.
From the multiple inner methods that exist for EAP-TTLS, selectUse EAP Methodsand selectEAP-MSCHAPv2.
Click Next to continue to the Certificate section.
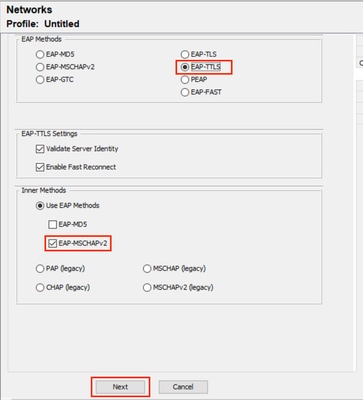 NAM Profile Editor Machine Authentication
NAM Profile Editor Machine Authentication
Step 5. Configure Certificate Validation Rules
-
Under Certificate Trusted Server Rules, configure a rule based on the server certificate common name.
You can also specify the common name of the Policy Service Node (PSN) EAP authentication certificate.
In this example, the PSN node certificate is issued by varshaah.varshaah.local. Hence, the rule Common Name ends with .local is used. This rule validates the certificate that the server presents during the EAP-TTLS flow. -
Under Certificate Trusted Authority, two options are available.
With this option, the Windows device trusts any EAP certificate that is signed by a certificate included in Certificates – Current User > Trusted Root Certification Authorities > Certificates (managed by the operating system).
In this scenario, the option Trust any Root Certificate Authority (CA) installed on the OS is used instead of adding a specific CA certificate. - Click Next to continue.
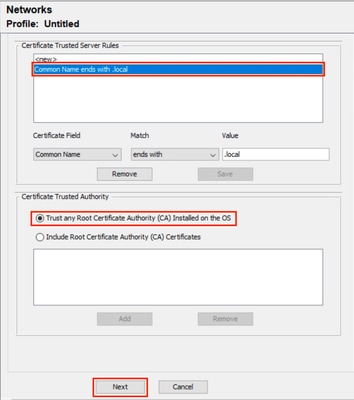 NAM Profile Editor Certificates
NAM Profile Editor Certificates
Step 6. In the Machine Credentials section, select Use Machine Credentials, and then click Next.
 NAM Profile Editor Credentials
NAM Profile Editor Credentials
Step 7. Configure User Auth section.
-
Select EAP-TTLS under EAP Methods.
-
Under Inner Methods, select Use EAP Methods and select EAP-MSCHAPv2.
-
Click Next.
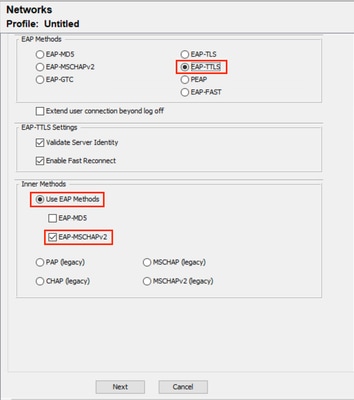 NAM Profile Editor User Authentication
NAM Profile Editor User Authentication
Step 8. In Certificates, configure the same certificate validation rules as described in Step 5.
Step 9. In User Credentials, select Use Single Sign-On Credentials, and then click Done.
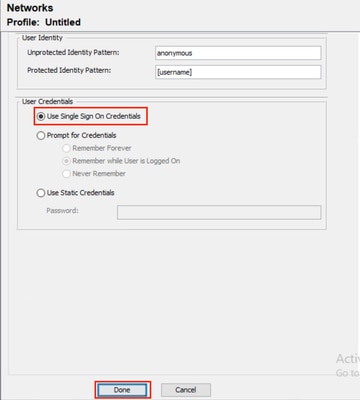 NAM Profile Editor User Credentials
NAM Profile Editor User Credentials
Part 6: Save the Network Configuration File
Step 1. Click File > Save.
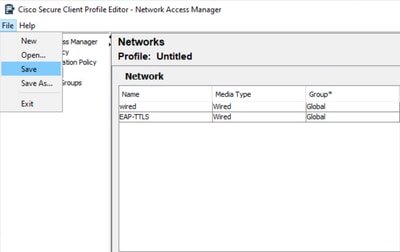 NAM Profile Editor Save Network Configuration
NAM Profile Editor Save Network Configuration
Step 2. Save the file as configuration.xml in the newConfigFiles folder.
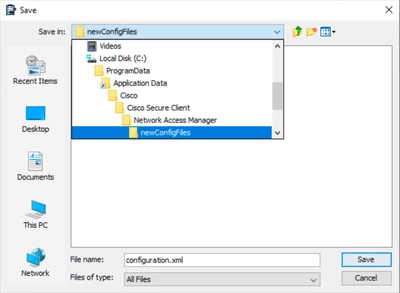 Save Network Configuration
Save Network Configuration
Part 7: Configure AAA on the Switch
C9300-1#sh run aaa
!
aaa authentication dot1x default group labgroup
aaa authorization network default group labgroup
aaa accounting dot1x default start-stop group labgroup
aaa accounting update newinfo periodic 2880
!
!
!
!
aaa server radius dynamic-author
client 10.76.112.135 server-key cisco
!
!
radius server labserver
address ipv4 10.76.112.135 auth-port 1812 acct-port 1813
key cisco
!
!
aaa group server radius labgroup
server name labserver
!
!
!
!
aaa new-model
aaa session-id common
!
!C9300-1(config)#dot1x system-auth-control
Note: The dot1x system-auth-control command does not appear in the show running-config output, but it is required to enable 802.1X globally.
Configure the Switch Interface for 802.1X:
C9300-1(config)#do sh run int gig1/0/44
Building configuration...
Current configuration : 242 bytes
!
interface GigabitEthernet1/0/44
switchport access vlan 96
switchport mode access
device-tracking
authentication order dot1x mab
authentication priority dot1x mab
authentication port-control auto
authentication host-mode multi-auth
authentication periodic
mab
dot1x pae authenticator
endPart 8: ISE Configurations
Step 1. Configure switch on ISE.
Navigate to Administration > Network Resources > Network Devices and click Add.
Enter the switch name and IP address here.
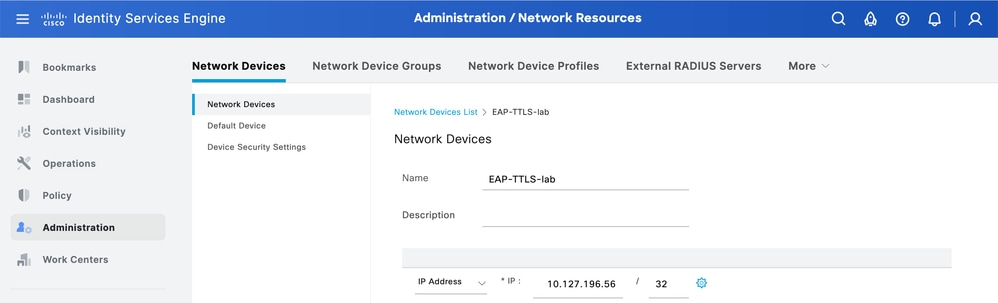 Adding Network Device ISE
Adding Network Device ISE
Enter the RADIUS shared secret, the same as the one configured earlier on the switch.
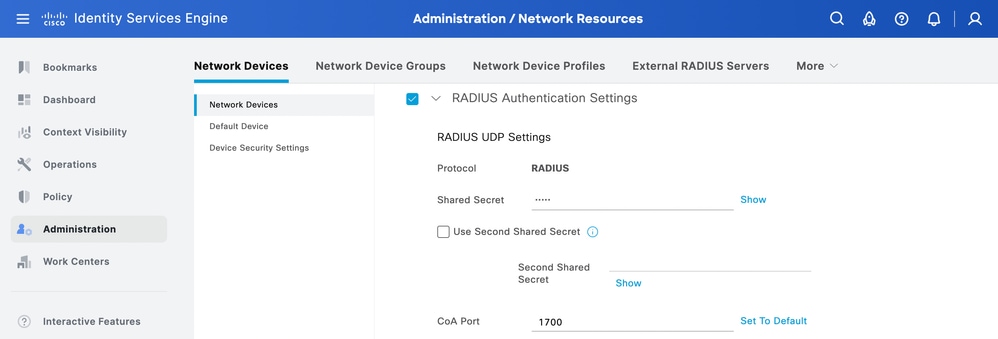 RADIUS Shared Secret ISE
RADIUS Shared Secret ISE
Step 2. Configure identity source sequence.
-
Navigate to Administration > Identity Management > Identity Source Sequences.
-
Click Add to create a new identity source sequence.
- Configure the identity sources under Authentication Search List.
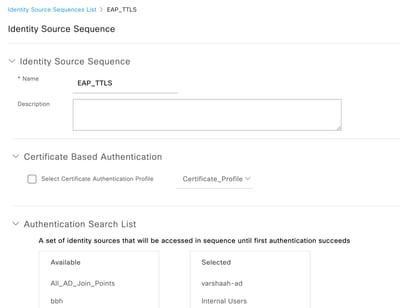 ISE Identity Source Sequence
ISE Identity Source Sequence
Step 3. Configure policy set.
Navigate to Policy > Policy Sets and create a new policy set. Configure the conditions as Wired_802.1x OR Wireless_802.1x. For Allowed Protocols, choose Default Network Access:
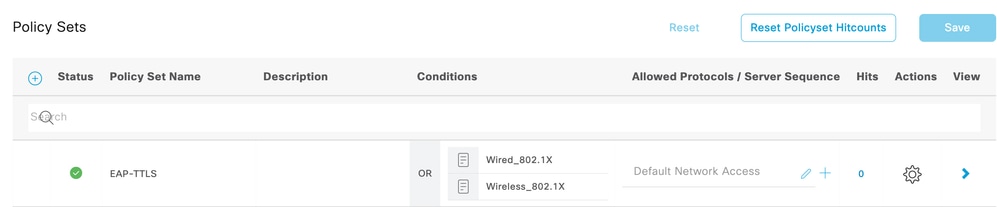 EAP-TTLS Policy Set
EAP-TTLS Policy Set
Create the authentication policy for dot1x and choose the identity source sequence created in Step 4.
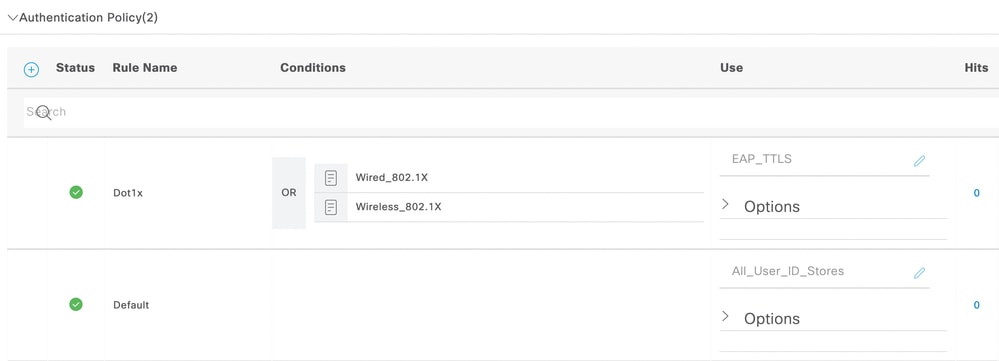 EAP-TTLS Authentication Policy
EAP-TTLS Authentication Policy
For authorization policy, create the rule with three conditions. The first condition checks for the condition that EAP-TTLS tunnel is used. The second condition checks that EAP-MSCHAPv2 is used as the inner EAP method. The third condition checks for the respective AD group.
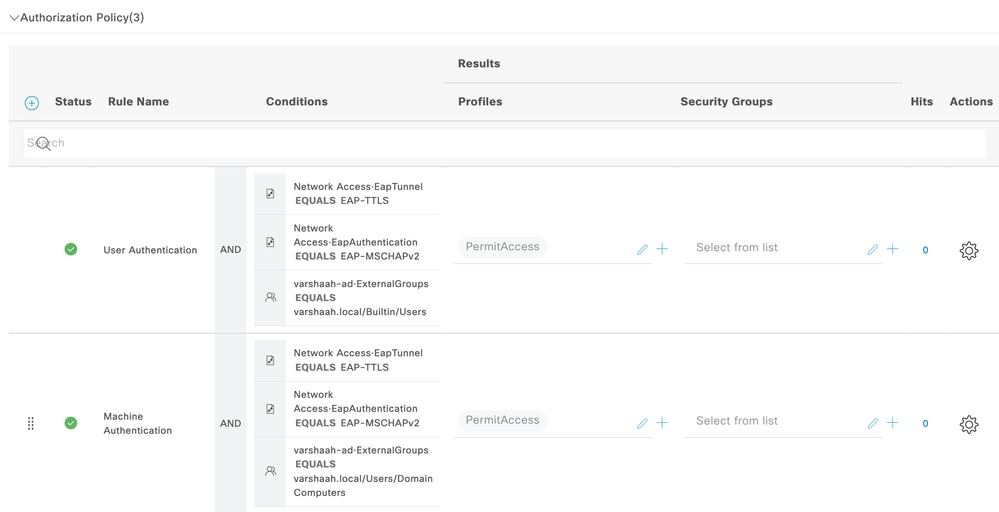 Dot1x Authorization Policy
Dot1x Authorization Policy
Verify
You can reboot the Windows 10 machine or you can sign out and then sign in. Whenever the windows log in screen is displayed, machine authentication is triggered.
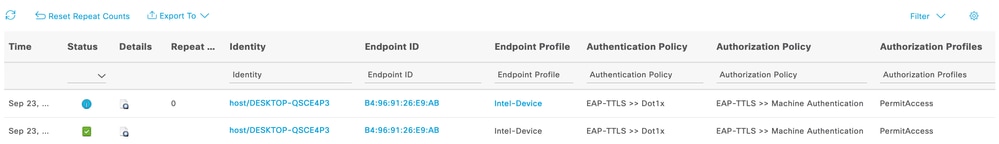 Live Log Machine Authentication
Live Log Machine Authentication
When you log in to the PC with credentials, user authentication is triggered.
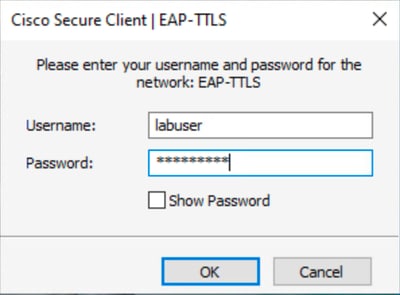 User Authentication Credentials
User Authentication Credentials

Note: This example uses Active Directory user credentials for authentication. Alternatively, you can create an internal user in Cisco ISE and use those credentials for log in.
After the credentials are entered and successfully verified, the endpoint is connected to the network with user authentication.
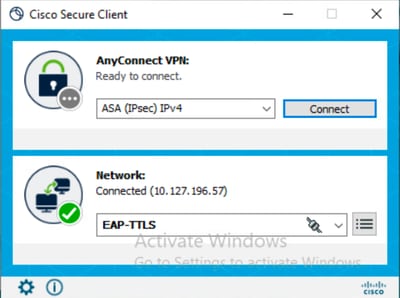 EAP-TTLS Connected
EAP-TTLS Connected
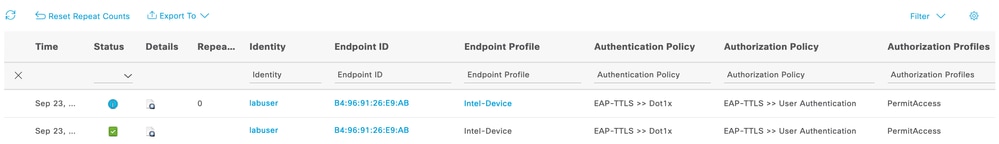 Live Log User Authentication
Live Log User Authentication
Analyze ISE RADIUS Live Logs
This section illustrates the RADIUS live log entries for successful machine and user authentication.
Machine Authentication
11001 Received RADIUS Access-Request
11017 RADIUS created a new session
...
...
11507 Extracted EAP-Response/Identity
12983 Prepared EAP-Request proposing EAP-TTLS with challenge
...
...
12978 Extracted EAP-Response containing EAP-TTLS challenge-response and accepting EAP-TTLS as negotiated
12800 Extracted first TLS record; TLS handshake started
12805 Extracted TLS ClientHello message
12806 Prepared TLS ServerHello message
12807 Prepared TLS Certificate message
12808 Prepared TLS ServerKeyExchange message
12810 Prepared TLS ServerDone message
...
...
12803 Extracted TLS ChangeCipherSpec message
12804 Extracted TLS Finished message
12801 Prepared TLS ChangeCipherSpec message
12802 Prepared TLS Finished message
12816 TLS handshake succeeded
...
...
11806 Prepared EAP-Request for inner method proposing EAP-MSCHAP with challenge
12985 Prepared EAP-Request with another EAP-TTLS challenge
11006 Returned RADIUS Access-Challenge
11001 Received RADIUS Access-Request
...
...
12971 Extracted EAP-Response containing EAP-TTLS challenge-response
11808 Extracted EAP-Response containing EAP-MSCHAP challenge-response for inner method and accepting EAP-MSCHAP as negotiated
...
...
24431 Authenticating machine against Active Directory - varshaah-ad
24325 Resolving identity - host/DESKTOP-QSCE4P3
...
...
24343 RPC Logon request succeeded - DESKTOP-QSCE4P3$@varshaah.local
24470 Machine authentication against Active Directory is successful - varshaah-ad
22037 Authentication Passed
...
...
12971 Extracted EAP-Response containing EAP-TTLS challenge-response
11810 Extracted EAP-Response for inner method containing MSCHAP challenge-response
11814 Inner EAP-MSCHAP authentication succeeded
11519 Prepared EAP-Success for inner EAP method
12975 EAP-TTLS authentication succeeded
...
...
15036 Evaluating Authorization Policy
24209 Looking up Endpoint in Internal Endpoints IDStore - host/DESKTOP-QSCE4P3
24211 Found Endpoint in Internal Endpoints IDStore
15048 Queried PIP - Network Access.Device IP Address
15048 Queried PIP - Network Access.EapTunnel
15016 Selected Authorization Profile - PermitAccess
...
...
11002 Returned RADIUS Access-Accept
User Authentication
11001 Received RADIUS Access-Request
11017 RADIUS created a new session
...
...
11507 Extracted EAP-Response/Identity
12983 Prepared EAP-Request proposing EAP-TTLS with challenge
...
...
12978 Extracted EAP-Response containing EAP-TTLS challenge-response and accepting EAP-TTLS as negotiated
12800 Extracted first TLS record; TLS handshake started
12805 Extracted TLS ClientHello message
12806 Prepared TLS ServerHello message
12807 Prepared TLS Certificate message
12808 Prepared TLS ServerKeyExchange message
12810 Prepared TLS ServerDone message
...
...
12812 Extracted TLS ClientKeyExchange message
12803 Extracted TLS ChangeCipherSpec message
12804 Extracted TLS Finished message
12801 Prepared TLS ChangeCipherSpec message
12802 Prepared TLS Finished message
12816 TLS handshake succeeded
...
...
11806 Prepared EAP-Request for inner method proposing EAP-MSCHAP with challenge
12985 Prepared EAP-Request with another EAP-TTLS challenge
11006 Returned RADIUS Access-Challenge
11001 Received RADIUS Access-Request
...
...
12971 Extracted EAP-Response containing EAP-TTLS challenge-response
11808 Extracted EAP-Response containing EAP-MSCHAP challenge-response for inner method and accepting EAP-MSCHAP as negotiated
...
...
24430 Authenticating user against Active Directory - varshaah-ad
24325 Resolving identity - labuser@varshaah.local
...
...
24343 RPC Logon request succeeded - labuser@varshaah.local
24402 User authentication against Active Directory succeeded - varshaah-ad
22037 Authentication Passed
...
...
12971 Extracted EAP-Response containing EAP-TTLS challenge-response
11810 Extracted EAP-Response for inner method containing MSCHAP challenge-response
11814 Inner EAP-MSCHAP authentication succeeded
11519 Prepared EAP-Success for inner EAP method
12975 EAP-TTLS authentication succeeded
...
...
15036 Evaluating Authorization Policy
24209 Looking up Endpoint in Internal Endpoints IDStore - labuser
24211 Found Endpoint in Internal Endpoints IDStore
15048 Queried PIP - Network Access.Device IP Address
15048 Queried PIP - Network Access.EapTunnel
15016 Selected Authorization Profile - PermitAccess
...
...
11002 Returned RADIUS Access-Accept
Analyze NAM Logs
NAM logs, especially after you enable Extended Logging, contains a large amount of data, most of which are irrelevant and can be ignored. This section lists out the debug lines to demonstrate each step NAM takes to establish a network connection. When you work through a log, these key phrases can be helpful to locate part of the log relevant to the issue.
Machine Authentication
2160: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.696 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11812][comp=SAE]: 8021X (3) recvd EAP TTLS frame (dot1x_util.c 303)The client receives an EAP-TTLS packet from the network switch, initiating the EAP-TTLS session. This is the starting point for the machine authentication tunnel.
2171: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.696 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11812][comp=SAE]: EAP (0) SSL STATE: SSLv3/TLS read server hello (eap_auth_tls_p.c 395)
2172: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.696 +0900: %csc_nam-6-INFO_MSG: %[tid=11812][comp=SAE]: CERT (0) looking up: "/CN=varshaah.varshaah.local" (lookup.c 97)
2173: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.696 +0900: %csc_nam-6-INFO_MSG: %[tid=11812][comp=SAE]: CERT (0) certificate with serial number 022d90152393a07cd58919379f added to list (lookup_win32.c 230)The client receives the Server Hello from ISE and begins validating the server certificate (CN=varshaah.varshaah.local). The certificate is found in the client's trust store and added for validation.
2222: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.696 +0900: %csc_nam-6-INFO_MSG: %[tid=11768]: Validating the server: varshaah.varshaah.local
2223: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.696 +0900: %csc_nam-6-INFO_MSG: %[tid=11768]: Server certificate validated: varshaah.varshaah.localThe server certificate is successfully validated, completing TLS tunnel establishment.
2563: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.789 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11768]: Network EAP-TTLS: NetworkStateMachine current state USER_T_NOT_DISCONNECTED, received auth request AUTHENTICATION_PASSED
2564: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.789 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11812][comp=SAE]: NET (0) SscfApiClass::EnablePortBlocking( {B4467C9A-0EBD-4181-B8CD-6D64F3831F30}, False ): Unblocking interface (cimdIo.cpp 291)
2565: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.789 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11768]: Network EAP-TTLS: NetworkStateMachine new state USER_T_NOT_DISCONNECTEDThe client signals that authentication has passed. The interface is unblocked, and the internal state machine transitions to USER_T_NOT_DISCONNECTED, indicating the machine can now pass traffic.
2609: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.821 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11768]: Network EAP-TTLS: AccessStateMachine current state = ACCESS_CONNECTING, received adapterState = authenticated
2610: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.821 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11824][comp=SAE]: NET (0) 0020 00 00 00 00 00 00 0A 7F C4 01 .......... (cimdIo.cpp 6080)
2611: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.821 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11768]: Network EAP-TTLS: Clearing the connection duration timer
2612: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.821 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11824][comp=SAE]: NET (0) CIMD Event: evtSeq#=0 msg=4 ifIndex=1 len=76 (cimdEvt.c 622)
2613: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.821 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11768]: Network EAP-TTLS: port authentication succeeded
2614: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.821 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11824][comp=SAE]: NET (2) cdiEvt:(3,1) dataLen=42 (cimdEvt.c 358)
2615: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.821 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11768]: Network EAP-TTLS: AccessStateMachine new state = ACCESS_AUTHENTICATEDThe adapter reports authenticated, and the NAM AccessStateMachine transitions to ACCESS_AUTHENTICATED. This confirms the machine has successfully completed authentication and has full network access.
User Authentication
100: DESKTOP-QSCE4P3: Sep 25 2025 14:01:26.669 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9664]: Network EAP-TTLS: AccessStateMachine new state = ACCESS_STARTED
The NAM client begins the EAP-TTLS connection process.
195: DESKTOP-QSCE4P3: Sep 25 2025 15:09:11.780 +0900: %csc_nam-7-DEBUG_MSG: %[tid=3252]: Binding adapter Intel(R) I350 Gigabit Network Connection and machine auth for network EAP-TTLS
198: DESKTOP-QSCE4P3: Sep 25 2025 15:09:11.780 +0900: %csc_nam-7-DEBUG_MSG: %[tid=3252]: Network EAP-TTLS: AccessStateMachine new state = ACCESS_ATTACHED
NAM binds the physical adapter to the EAP-TTLS network and moves into the ACCESS_ATTACHED state, confirming that the adapter is ready for authentication.
204: DESKTOP-QSCE4P3: Sep 25 2025 15:09:11.780 +0900: %csc_nam-7-DEBUG_MSG: %[tid=3252]: Network EAP-TTLS: AccessStateMachine current state = ACCESS_ATTACHED, received userEvent = CONNECT
247: DESKTOP-QSCE4P3: Sep 25 2025 15:09:11.780 +0900: %csc_nam-7-DEBUG_MSG: %[tid=3680][comp=SAE]: STATE (3) S_enterStateAux called with state = CONNECTING (dot1x_sm.c 142)
The client transitions from ATTACHED to CONNECTING, beginning the 802.1X exchange.
291: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.388 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6644][comp=SAE]: 8021X (4) Sent start frame (dot1x_sm.c 117)The client sends an EAPOL-Start to trigger the authentication process.
331: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.435 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6644][comp=SAE]: PORT (3) net: RECV (status: UP, AUTO) (portMsg.c 686)
332: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.435 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6644][comp=SAE]: 8021X (4) recvd EAP IDENTITY frame (dot1x_util.c 266)
340: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.435 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6644][comp=SAE]: EAP (0) EAP State: EAP_STATE_IDENTITY (eap_auth_client.c 940)
The switch requests an identity, and the client prepares to respond with an outer identity.
402: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.685 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9580]: EAP-CB: credential requested: sync=80, session-id=1, handle=04C96A74, type=AC_CRED_SESSION_START
422: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.685 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6088]: EAP: processing credential request: sync=80, session-id=1, eap-handle=04C96A74, eap-level=0, auth-level=0, protected=0, type=CRED_REQ_SESSION_START
460: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.685 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6088]: EAP: credential request completed, response sent: sync=80NAM sends the outer identity. By default, this is anonymous, indicating that the exchange is for user authentication (not machine).
488: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.497 +0900: %csc_nam-6-INFO_MSG: %[tid=6088]: EAP: EAP suggested by server: eapTtls
489: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.497 +0900: %csc_nam-6-INFO_MSG: %[tid=6088]: EAP: EAP requested by client: eapTtls
490: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.497 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6088]: EAP: EAP methods sent: sync=3
491: DESKTOP-QSCE4P3: Sep 25 2025 13:15:36.497 +0900: %csc_nam-7-DEBUG_MSG: %[tid=6088]: EAP: credential request 3: state transition: PENDING -> RESPONDED
Both client and server agree to use EAP-TTLS as the outer method.
660: DESKTOP-QSCE4P3: Sep 25 2025 14:01:27.185 +0900: %csc_nam-7-DEBUG_MSG: %[tid=8296][comp=SAE]: EAP (0) SSL STATE: SSLv3/TLS write client hello (eap_auth_tls_p.c 395)
661: DESKTOP-QSCE4P3: Sep 25 2025 14:01:27.185 +0900: %csc_nam-7-DEBUG_MSG: %[tid=8296][comp=SAE]: EAP (0) SSL STATE: SSLv3/TLS read server hello (eap_auth_tls_p.c 395)
The client sends Client Hello and receives the Server Hello, which includes the ISE certificate.
706: DESKTOP-QSCE4P3: Sep 25 2025 13:04:31.967 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: 8021X (4) recvd EAP TTLS frame (dot1x_util.c 303)
717: DESKTOP-QSCE4P3: Sep 25 2025 13:04:31.967 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: EAP (0) SSL STATE: SSLv3/TLS read server hello (eap_auth_tls_p.c 395)
718: DESKTOP-QSCE4P3: Sep 25 2025 13:04:31.967 +0900: %csc_nam-6-INFO_MSG: %[tid=11932][comp=SAE]: CERT (0) looking up: "/CN=varshaah.varshaah.local" (lookup.c 97)
719: DESKTOP-QSCE4P3: Sep 25 2025 13:04:31.983 +0900: %csc_nam-6-INFO_MSG: %[tid=11932][comp=SAE]: CERT (0) certificate with serial number 022d90152393a07cd58919379f added to list (lookup_win32.c 230)
726: DESKTOP-QSCE4P3: Sep 25 2025 13:04:31.983 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: EAP (0) SSL_ERROR_WANT_X509_LOOKUP (eap_auth_tls_p.c 194)
The server certificate is presented. The client looks up the CN varshaah.varshaah.local, finds a match, and validates the certificate. The handshake pauses while the X.509 certificate is checked.
729: DESKTOP-QSCE4P3: Sep 25 2025 13:04:31.983 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: EAP (2) EAP_EVENT_CRED_REQUEST queued (eapCredProcess.c 496)
730: DESKTOP-QSCE4P3: Sep 25 2025 13:04:31.983 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11916][comp=SAE]: EAP (2) EAP: CRED_REQUEST (eapMessage.c 355)
1110: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.044 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9644]: Auth[EAP-TTLS:user-auth]: Received username/password response
1111: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.044 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9644]: Auth[EAP-TTLS:user-auth]: ...resumedThe tunnel is established. NAM now requests and prepares the protected identity and credentials for inner authentication.
1527: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.169 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11916][comp=SAE]: EAP (0) SSL STATE: SSLv3/TLS write client key exchange (eap_auth_tls_p.c 395)
1528: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.169 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11916][comp=SAE]: EAP (0) SSL STATE: SSLv3/TLS write change cipher spec (eap_auth_tls_p.c 395)
1573: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.184 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: EAP (0) SSL STATE: SSL negotiation finished successfully (eap_auth_tls_p.c 395)
1574: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.184 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: EAP (0) EAP-TTLS: SSL handshake done (eap_auth_tls_p.c 426)
1575: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.184 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: EAP (0) EAP-TTLS: New session. (eap_auth_tls_p.c 434)The TLS handshake completes. A secure tunnel is now established for inner authentication.
1616: DESKTOP-QSCE4P3: Sep 25 2025 14:01:46.262 +0900: %csc_nam-6-INFO_MSG: %[tid=9664]: Protected identity/(Username) sent.
1620: DESKTOP-QSCE4P3: Sep 25 2025 14:01:46.262 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9664]: Auth[EAP-TTLS:user-auth]: Authentication state transition: AUTH_STATE_UNPROTECTED_IDENTITY_ACCEPTED -> AUTH_STATE_PROTECTED_IDENTITY_SENT
1689: DESKTOP-QSCE4P3: Sep 25 2025 14:01:46.277 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9664]: Auth[EAP-TTLS:user-auth]: Authentication state transition: AUTH_STATE_PROTECTED_IDENTITY_SENT -> AUTH_STATE_PROTECTED_IDENTITY_ACCEPTEDThe protected identity (username) is sent and accepted by ISE.
1708: DESKTOP-QSCE4P3: Sep 25 2025 14:01:46.277 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9456][comp=SAE]: EAP (1) deferred password request (eapRequest.c 148)
1738: DESKTOP-QSCE4P3: Sep 25 2025 13:01:44.758 +0900: %csc_nam-6-INFO_MSG: %[tid=11768]: Protected password sent.
1741: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.200 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9644]: Auth[EAP-TTLS:user-auth]: Authentication state transition: AUTH_STATE_PROTECTED_IDENTITY_ACCEPTED -> AUTH_STATE_CREDENTIAL_SENT
ISE requests the password. NAM sends the protected password inside the TLS tunnel.
1851: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.262 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9644]: Auth[EAP-TTLS:user-auth]: Authentication state transition: AUTH_STATE_CREDENTIAL_SENT -> AUTH_STATE_SUCCESS
1852: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.262 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: STATE (4) dot1x->eapSuccess is True (dot1x_sm.c 352)
1853: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.262 +0900: %csc_nam-7-DEBUG_MSG: %[tid=9644]: Auth[EAP-TTLS:user-auth]: Sending NOTIFICATION__SUCCESS to subscribers
1854: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.262 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: STATE (4) SUCCESS (dot1x_sm.c 358)
1855: DESKTOP-QSCE4P3: Sep 25 2025 13:04:42.262 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11932][comp=SAE]: STATE (4) S_enterStateAux called with state = AUTHENTICATED (dot1x_sm.c 142)ISE validates the password, sends EAP-Success, and NAM transitions to AUTHENTICATED. At this point, user authentication is complete and the client is allowed network access.
Troubleshoot
When troubleshooting Network Access Manager (NAM) issues with Cisco ISE and switch integration, logs must be collected from all three components: Secure Client (NAM), Cisco ISE, and the switch.
Secure Client (NAM) Logs
-
Enable NAM extended logging by following these steps.
-
Reproduce the issue. If the network profile does not apply, run Network Repair in Secure Client.
-
Collect the DART bundle using the Diagnostics and Reporting Tool (DART).
Cisco ISE Logs
Enable these debugs on ISE to capture authentication and directory interactions:
-
runtime-AAA
- nsf
- nsf-session
Switch Logs
Basic Debugs
request platform software trace rotate all
set platform software trace smd switch active R0 radius debug
set platform software trace smd switch active R0 aaa debug
set platform software trace smd switch active R0 dot1x-all debug
set platform software trace smd switch active R0 eap-all debug
debug radius all
Advanced Debugs (if Required)
set platform software trace smd switch active R0 epm-all debug
set platform software trace smd switch active R0 pre-all debug
Show Commands
show version
show debugging
show running-config aaa
show authentication session interface gix/x details
show dot1x interface gix/x
show aaa servers
show platform software trace message smd switch active R0
User Authentication Failure due to Invalid Credentials
When a user enters incorrect credentials, Secure Client displays a generic Password was incorrect for the network: EAP-TTLS message. The on-screen error does not specify whether the issue is due to an invalid username or password.
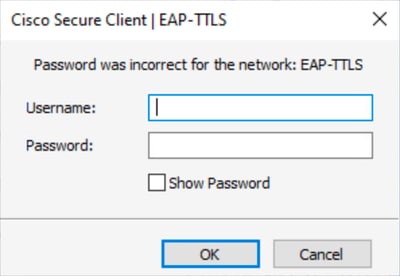 Incorrect Password Error
Incorrect Password Error
If authentication fails twice consecutively, Secure Client displays this message: An authentication error occurred for network 'EAP-TTLS'. Please try again. If the issue persists, contact your administrator.
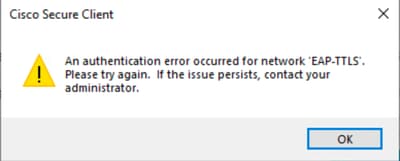 User Authentication Issue
User Authentication Issue
To identify the cause, review the NAM logs.
1. Incorrect password:
When a user enters an incorrect password, NAM logs show entries similar to this output:
3775: DESKTOP-QSCE4P3: Oct 02 2025 15:29:39.921 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11300][comp=SAE]: EAP (0) EAP-MSCHAP-V2: MSCHAP_FAILURE received (eap_auth_mschapv2_c.c 776) 3776: DESKTOP-QSCE4P3: Oct 02 2025 15:29:39.921 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11300][comp=SAE]: EAP (0) EAP-MSCHAP-V2: State: MSCHAP_STATE_R_RESULT (eap_auth_mschapv2_c.c 783) 3777: DESKTOP-QSCE4P3: Oct 02 2025 15:29:39.922 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11300][comp=SAE]: EAP (0) EAP-MSCHAP-V2: Error: MSCHAP_ERROR_AUTHENTICATION_FAILURE (eap_auth_mschapv2_c.c 616)
In Cisco ISE live logs, the corresponding event appears as:
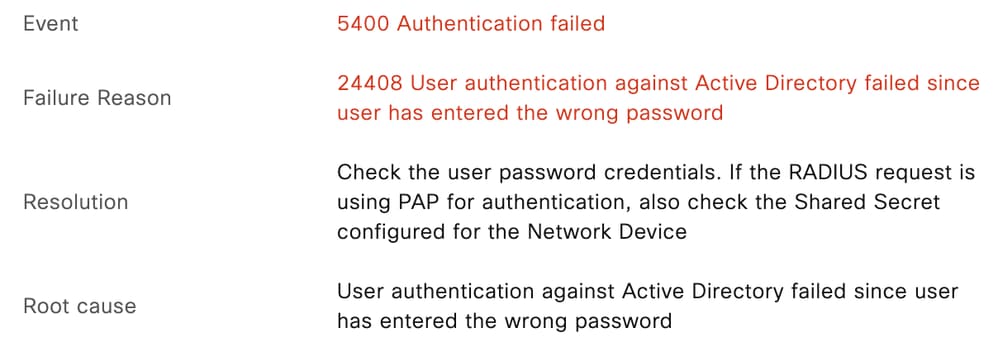 Incorrect Password
Incorrect Password
11001 Received RADIUS Access-Request
11017 RADIUS created a new session
...
...
11507 Extracted EAP-Response/Identity 10
12983 Prepared EAP-Request proposing EAP-TTLS with challenge
...
...
12978 Extracted EAP-Response containing EAP-TTLS challenge-response and accepting EAP-TTLS as negotiated
12800 Extracted first TLS record; TLS handshake started
...
...
12810 Prepared TLS ServerDone message
...
...
12812 Extracted TLS ClientKeyExchange message
12803 Extracted TLS ChangeCipherSpec message
...
...
12816 TLS handshake succeeded
...
...
11806 Prepared EAP-Request for inner method proposing EAP-MSCHAP with challenge 0
12985 Prepared EAP-Request with another EAP-TTLS challenge
11006 Returned RADIUS Access-Challenge 0
11001 Received RADIUS Access-Request
...
...
12971 Extracted EAP-Response containing EAP-TTLS challenge-response 0
11808 Extracted EAP-Response containing EAP-MSCHAP challenge-response for inner method and accepting EAP-MSCHAP as negotiated
...
...
15013 Selected Identity Source - varshaah-ad 0
24430 Authenticating user against Active Directory - varshaah-ad 0
24325 Resolving identity - labuser@varshaah.local 4
24313 Search for matching accounts at join point - varshaah.local 0
24319 Single matching account found in forest - varshaah.local 0
24323 Identity resolution detected single matching account 0
24344 RPC Logon request failed - STATUS_WRONG_PASSWORD, ERROR_INVALID_PASSWORD, labuser@varshaah.local 20
24408 User authentication against Active Directory failed since user has entered the wrong password - varshaah-ad 1
...
...
11823 EAP-MSCHAP authentication attempt failed
...
...
11815 Inner EAP-MSCHAP authentication failed 0
...
...
12976 EAP-TTLS authentication failed 0
...
...
11003 Returned RADIUS Access-Reject
2. Incorrect Username:
When a user enters an incorrect username, NAM logs show entries similar to this ouput:
3788: DESKTOP-QSCE4P3: Oct 02 2025 15:29:39.923 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11300][comp=SAE]: EAP (4) EAP status: AC_EAP_STATUS_ERR_CLIENT_IDENTITY_REJECTED (eapMessage.c 79) 3789: DESKTOP-QSCE4P3: Oct 02 2025 15:29:39.923 +0900: %csc_nam-7-DEBUG_MSG: %[tid=11300]: EAP-CB: EAP status notification: session-id=1, handle=051558CC, status=AC_EAP_STATUS_ERR_CLIENT_IDENTITY_REJECTED
In Cisco ISE live logs, the corresponding event appears as:
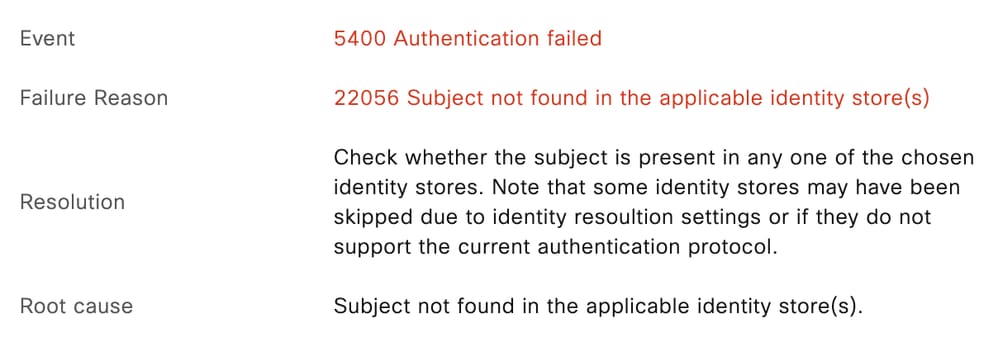 Incorrect Username
Incorrect Username
11001 Received RADIUS Access-Request
11017 RADIUS created a new session
...
...
11507 Extracted EAP-Response/Identity
12983 Prepared EAP-Request proposing EAP-TTLS with challenge
...
...
12978 Extracted EAP-Response containing EAP-TTLS challenge-response and accepting EAP-TTLS as negotiated
12800 Extracted first TLS record; TLS handshake started
...
...
12810 Prepared TLS ServerDone message
...
...
12812 Extracted TLS ClientKeyExchange message
12803 Extracted TLS ChangeCipherSpec message
...
...
12816 TLS handshake succeeded
...
...
11806 Prepared EAP-Request for inner method proposing EAP-MSCHAP with challenge
12985 Prepared EAP-Request with another EAP-TTLS challenge
11006 Returned RADIUS Access-Challenge
11001 Received RADIUS Access-Request
...
...
12971 Extracted EAP-Response containing EAP-TTLS challenge-response
11808 Extracted EAP-Response containing EAP-MSCHAP challenge-response for inner method and accepting EAP-MSCHAP as negotiated
...
...
15013 Selected Identity Source - All_AD_Join_Points
24430 Authenticating user against Active Directory - varshaah-ad
24325 Resolving identity - user@varshaah.local
24313 Search for matching accounts at join point - varshaah.local
...
...
24352 Identity resolution failed - ERROR_NO_SUCH_USER
24412 User not found in Active Directory - varshaah-ad
...
...
15013 Selected Identity Source - Internal Users
24210 Looking up User in Internal Users IDStore - user
24216 The user is not found in the internal users identity store
...
...
22056 Subject not found in the applicable identity store(s)
22058 The advanced option that is configured for an unknown user is used
22061 The 'Reject' advanced option is configured in case of a failed authentication request
11823 EAP-MSCHAP authentication attempt failed
...
...
11815 Inner EAP-MSCHAP authentication failed
...
...
12976 EAP-TTLS authentication failed 0
...
...
11504 Prepared EAP-Failure 1
11003 Returned RADIUS Access-Reject
Known Defects
| Bug ID | Description |
| Cisco bug ID 63395 | ISE 3.0 cannot locate REST ID store after services restart |
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
06-Oct-2025
|
Initial Release |
Contributed by Cisco Engineers
- Varshaah KarkalaTechnical Consulting Engineer
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback