How does a ransomware attack work?
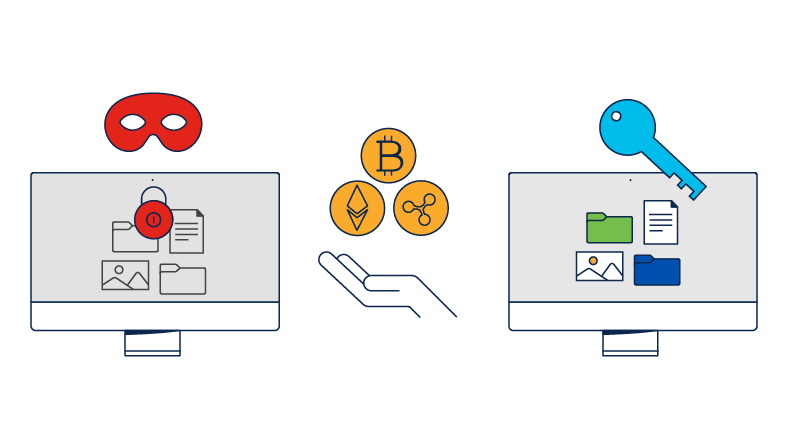
Ransomware is a cybercrime where a hacker encrypts a victim's data with malicious software with the intent that the attacker must be paid before the system will be unlocked. Once the ransom is paid, the attacker should send a decryption key to restore access to the victim's data, but often the system is unlocked and the stolen data is held for as second ransom. The ransom can range from a few hundred dollars to millions of dollars. Typically, payment is demanded in the form of a cryptocurrency, such as bitcoins.
Ransomware is typically distributed through a few main avenues. These include email phishing, malvertising (malicious malvertising), social engineering, and exploit kits. After ransomware is distributed, it encrypts selected files and notifies the victim of the required payment.
Ways to protect yourself from ransomware
Back up all your data
Make sure you have an enterprise data backup solution that can scale and won't experience bottlenecks when the time comes. In the event of an attack, you can power down the endpoint, reimage it, and reinstall your current backup. You will have all your data and prevent the ransomware from spreading to other systems.
Patch your systems
Make a habit of updating your software regularly. Patching commonly exploited third-party software will foil many attacks. If possible, turn on automatic patching.
Enable multi-factor authentication (MFA)
The weakest link in the security chain is usually human. Educate your users about whom and what to trust. Teach them to not fall for phishing or other schemes.
Protect your network
Take a layered approach, with security infused from the endpoint to email to the DNS layer. Use technologies such as a next-generation firewall (NGFW) or an intrusion prevention system (IPS).
Segment network access
Limit the resources that an attacker can access. By dynamically controlling access to resources based on sensitivity, like confidential or critical data, you help ensure that your entire network is not compromised in a single attack.
Keep a close eye on network activity
The ability to see everything happening across your network and data center can help you uncover attacks that bypass the perimeter. Deploy a demilitarized zone (DMZ) subnetwork or add a layer of security to your local area network (LAN). Leverage your security platform to effectively bring all the information together to triage, analyze, and respond quickly.
Prevent initial infiltration
Most ransomware infections occur through an email attachment or malicious download. Diligently block malicious websites, emails, and attachments through a layered security approach and a company-sanctioned file-sharing program.
Arm your endpoints
Antivirus solutions on your endpoints don't suffice anymore. Set up privileges so they perform tasks such as granting the appropriate network access or user permissions to endpoints. Two-factor authentications will also help.
Gain real-time threat intelligence
Know your enemy. Take advantage of threat intelligence from organizations such as Talos to understand the latest security information and become aware of emerging cybersecurity threats.
Engage with incident response specialists
Incident response teams provide a full suite of proactive and emergency services to help you prepare for, respond to, and recover from a breach.
The Future of Ransomware: Inside Cisco Talos Threat Hunters
Cisco Talos threat hunters identify new and evolving ransomware threats. See how their research and intelligence helps organizations build strong defenses.