Reduce complexity. Boost business.
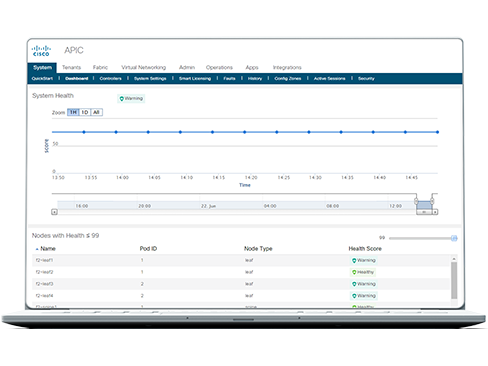
Optimize your network
Simplify and automate operations across multisite, multicloud data center networks.
Protect your business
Stay protected with zero-trust security and automated policy management for business continuity.
Streamline your path to hybrid cloud
Scale with seamless connectivity for any workload at any location.
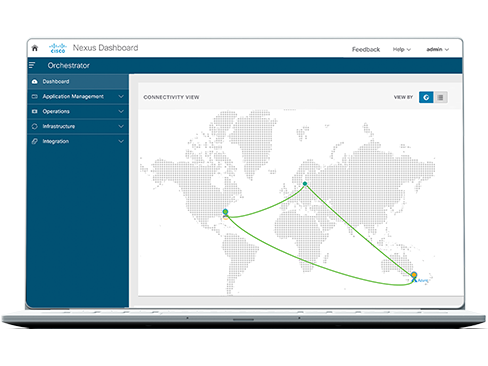
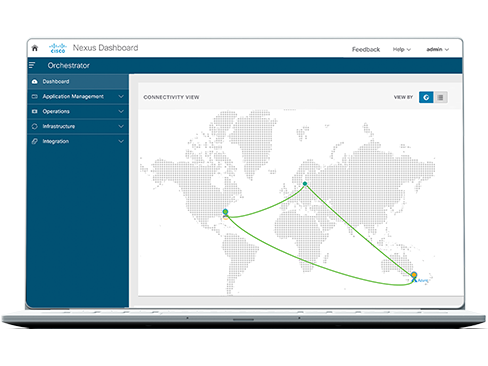
Connect to Cisco Nexus Dashboard
Configure, operate, and analyze everything connected to your data center and cloud networks, all from one place.
Get more for your network by optimizing with trusted integrations



Choose the right software subscription for you
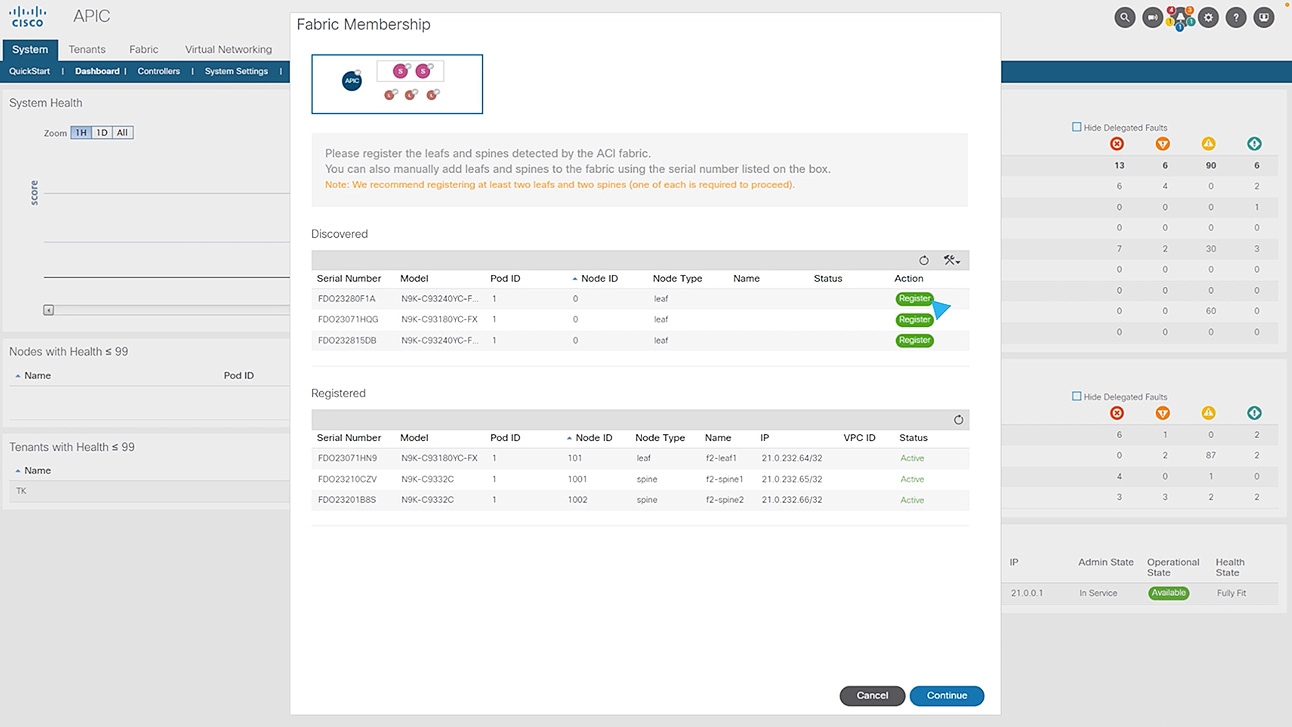
Cisco ACI
Networking Essentials
For single data center. Includes Cisco ACI management and operations capabilities.
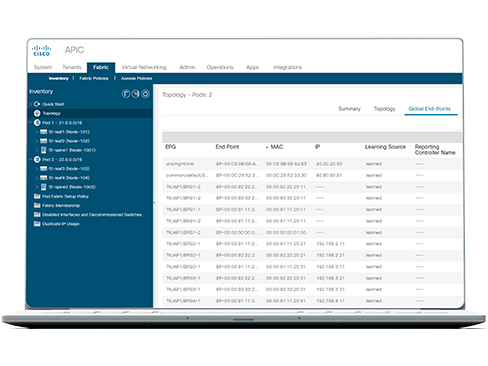
Cisco ACI
Networking Advantage
For multiple data centers and/or clouds. Includes advanced capabilities in addition to Networking Essentials.
Recommended
Cisco ACI
Networking Premier
For multiple data centers and/or clouds. Includes Essentials and Advantage as well as insights and orchestration capabilities.