簡介
本檔案介紹如何在Firepower裝置上配置和驗證Firepower威脅防禦(FTD)高可用性(HA)(主用/備用故障轉移)。
必要條件
需求
本文件沒有特定需求。
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- 2個Cisco Firepower 9300
- 2個Cisco Firepower 4100(7.2.8)
- Firepower管理中心(FMC)(7.2.8)
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
附註:在搭載FTD的FPR9300裝置上,您只能設定機箱間HA。HA 組態中的兩個裝置必須符合本文件提及的條件。
工作 1: 確認條件
工作需求:
確認兩台FTD裝置均符合備註要求,且均可設定為HA裝置。
解決方案:
步驟 1. 連線至 FPR9300 管理 IP 並確認模組硬體。
確認 FPR9300-1 硬體。
KSEC-FPR9K-1-A# show server inventory
Server Equipped PID Equipped VID Equipped Serial (SN) Slot Status Ackd Memory (MB) Ackd Cores
------- ------------ ------------ -------------------- ---------------- ---------------- ----------
1/1 FPR9K-SM-36 V01 FLM19216KK6 Equipped 262144 36
1/2 FPR9K-SM-36 V01 FLM19206H71 Equipped 262144 36
1/3 FPR9K-SM-36 V01 FLM19206H7T Equipped 262144 36
KSEC-FPR9K-1-A#
確認 FPR9300-2 硬體。
KSEC-FPR9K-2-A# show server inventory
Server Equipped PID Equipped VID Equipped Serial (SN) Slot Status Ackd Memory (MB) Ackd Cores
------- ------------ ------------ -------------------- ---------------- ---------------- ----------
1/1 FPR9K-SM-36 V01 FLM19206H9T Equipped 262144 36
1/2 FPR9K-SM-36 V01 FLM19216KAX Equipped 262144 36
1/3 FPR9K-SM-36 V01 FLM19267A63 Equipped 262144 36
KSEC-FPR9K-2-A#
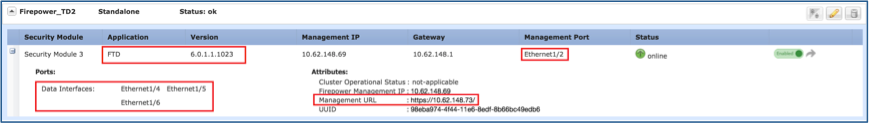
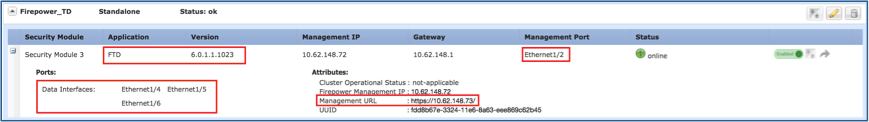
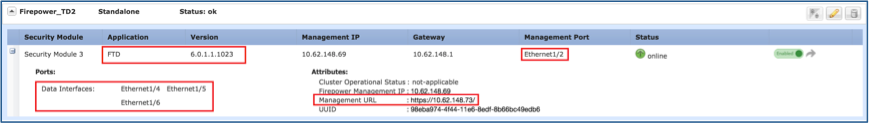
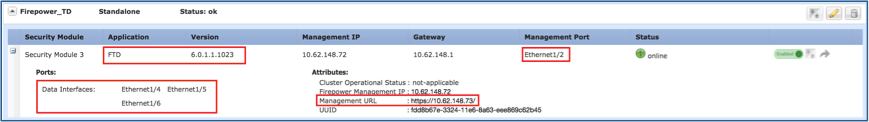
步驟 2. 登入 FPR9300-1 機箱管理員,然後導覽至邏輯裝置。
驗證介面的軟體版本、編號和型別。
任務2.配置FTD HA
工作需求:
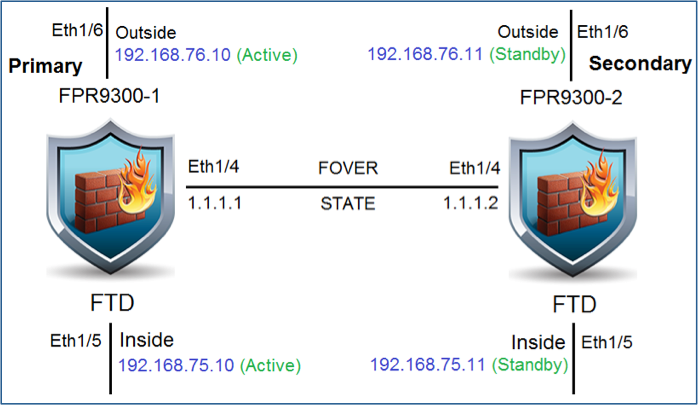
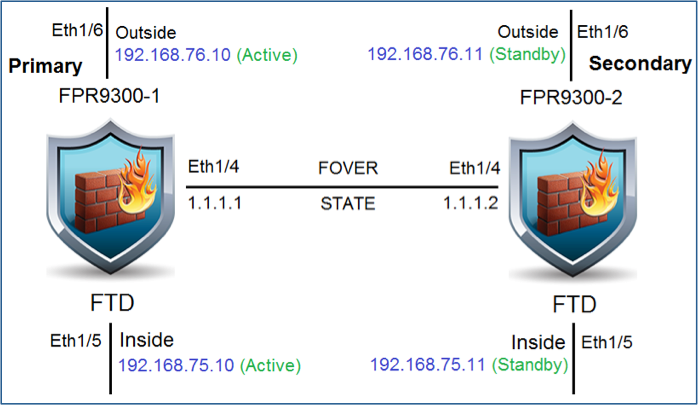
按照此圖表設定作用中/待命容錯移轉 (HA)。在這種情況下,使用41xx對。
解決方案
兩個 FTD 裝置已在 FMC 註冊,如圖所示。
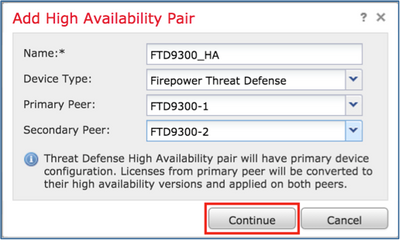
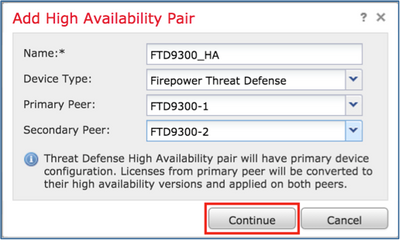
步驟1。若要設定FTD容錯移轉,請導覽至Devices > Device Management,然後選擇Add High Availability,如下圖所示。
步驟2.輸入Primary Peer和Secondary Peer,然後選擇Continue,如下圖所示。

警告:確保選擇正確的裝置作為主裝置。所選主裝置上的所有配置都將複製到所選輔助FTD裝置。通過複製,可以替換輔助裝置上的當前配置。
狀況
若要在 2 個 FTD 裝置之間建立 HA,必須符合下列條件:
- 型號相同
- 相同版本 — 這適用於FXOS和FTD — 主要(第一個數字)、次要(第二個數字)和維護(第三個數字)必須相等。
- 介面數目相同
- 介面類型相同
- 兩台裝置作為FMC中同一組/域的一部分。
- 具有相同的網路時間協定(NTP)配置。
- 完全部署在FMC上,無未提交的更改。
- 在相同的防火牆模式下: 路由或透明。

附註:在FTD裝置和FMC GUI上都必須檢查這一點,因為已發生FTD具有相同模式的情況,但FMC不會反映此情況。
- 任何介面均未配置DHCP/乙太網點對點協議(PPPoE)。
- 兩個機箱的主機名[完全限定域名(FQDN)]不同。若要檢查機箱主機名稱,請導覽至FTD CLI,然後執行以下命令:
firepower# show chassis-management-url
https://KSEC-FPR9K-1.cisco.com:443//
附註:在6.3後FTD中,使用命令show chassis detail。
Firepower-module1# show chassis detail
Chassis URL : https://FP4100-5:443//
Chassis IP : 10.62.148.187
Chassis IPv6 : ::
Chassis Serial Number : JAD19500BAB
Security Module : 1
如果兩個機箱的名稱相同,請使用下列命令變更其中一個機箱的名稱:
KSEC-FPR9K-1-A# scope system
KSEC-FPR9K-1-A /system # set name FPR9K-1new
Warning: System name modification changes FC zone name and redeploys them non-disruptively
KSEC-FPR9K-1-A /system* # commit-buffer
FPR9K-1-A /system # exit
FPR9K-1new-A#
變更機箱名稱後,請從 FMC 取消註冊 FTD,然後再重新註冊。接著,繼續建立 HA 配對。
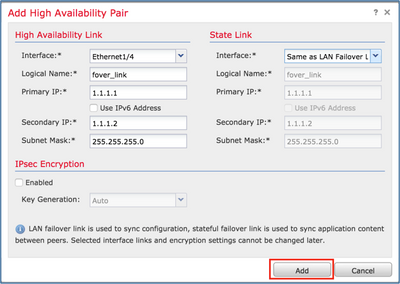
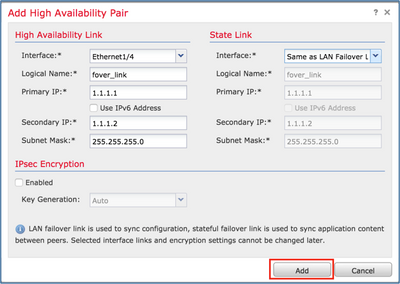
步驟 3. 設定 HA 和狀態連結設定。
依照您的情況,狀態連結的設定與高可用性相同。
選擇Add,並等待幾分鐘,以便部署HA配對,如下圖所示。

步驟 4. 設定資料介面(主要和待命 IP 位址)
在FMC GUI中選擇HA Edit,如下圖所示。
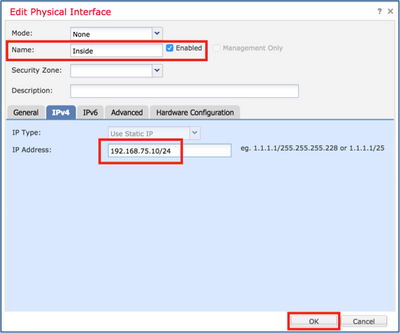
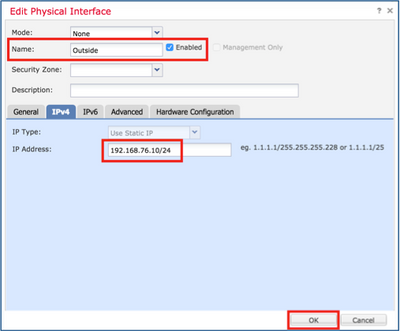
步驟5.配置介面設定:

如果是子介面,您需要首先啟用父介面:
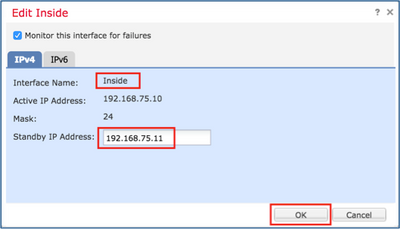
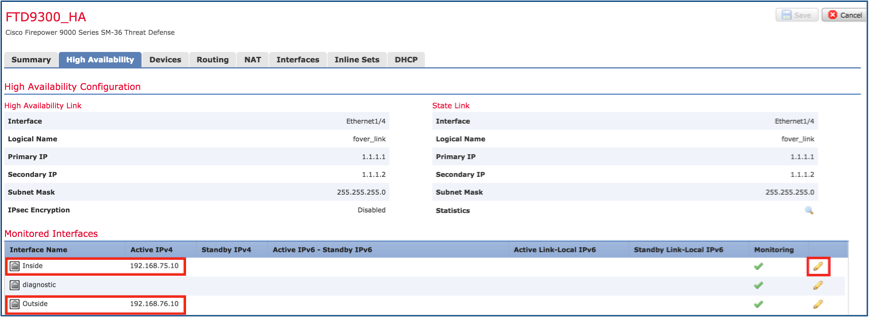
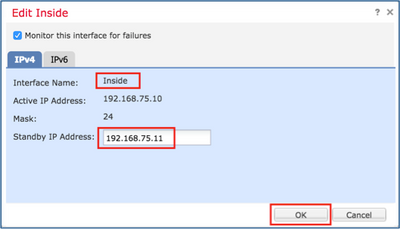
步驟6.導覽至High Availability,然後選擇Interface Name Edit以新增備用IP位址,如下圖所示。
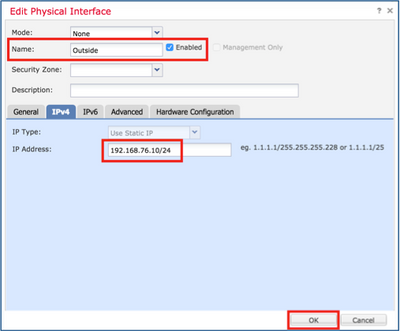
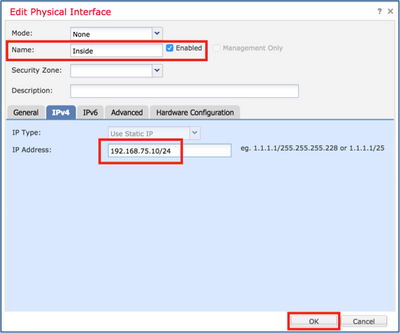
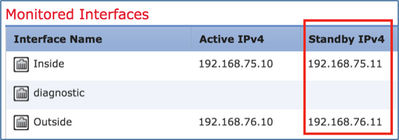
步驟 7. 內部介面如圖所示。
步驟 8. 請對外部介面執行相同的動作。
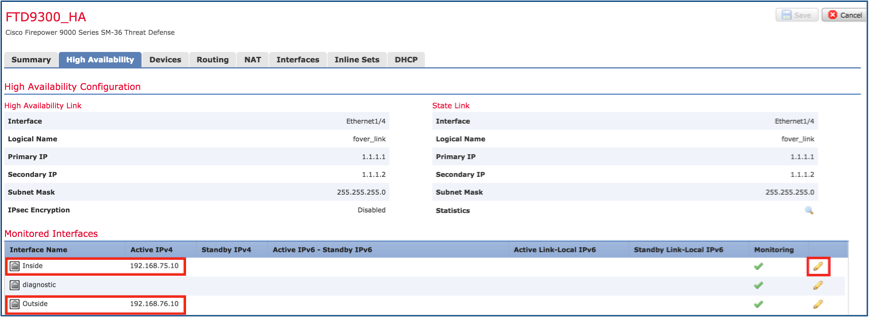
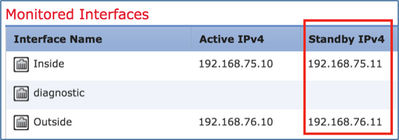
步驟 9. 確認結果,如圖所示。
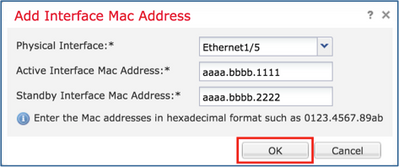
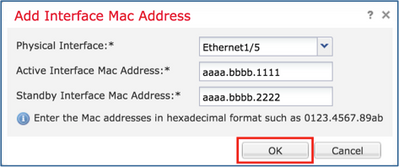
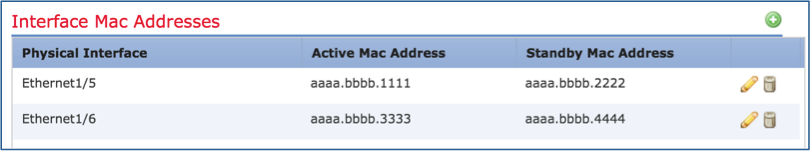
步驟10.停留在高可用性頁籤上,並配置虛擬MAC地址,如下圖所示。
步驟 11. 內部介面如圖所示。

步驟 12. 請對外部介面執行相同的動作。
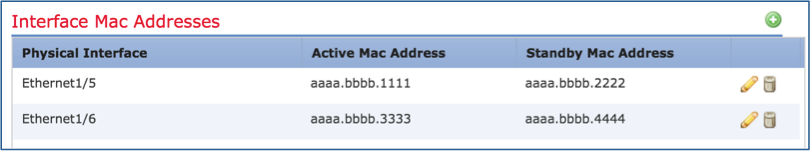
步驟 13. 確認結果,如圖所示。
步驟14.設定變更後,選擇Save和Deploy。
工作 3: 確認 FTD HA 和授權
工作需求:
透過 FMC GUI 和 FTD CLI 確認 FTD HA 設定和已啟用的授權。
解決方案:
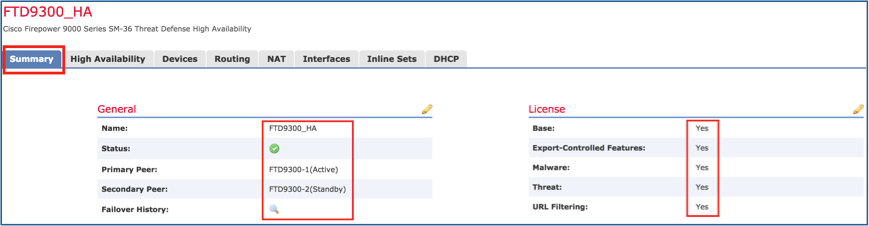
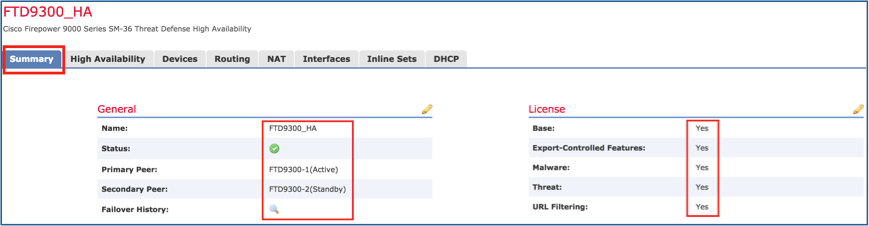
步驟 1. 導覽至「摘要」,然後檢查 HA 設定和已啟用的授權,如圖所示。
步驟2.在FTD CLISH CLI中,執行「show high-availability config」或「show failover」命令:
> show high-availability config
Failover On
Failover unit Primary
Failover LAN Interface: FOVER Port-channel3 (up)
Reconnect timeout 0:00:00
Unit Poll frequency 1 seconds, holdtime 15 seconds
Interface Poll frequency 5 seconds, holdtime 25 seconds
Interface Policy 1
Monitored Interfaces 2 of 1291 maximum
MAC Address Move Notification Interval not set
failover replication http
Version: Ours 9.18(4)210, Mate 9.18(4)210
Serial Number: Ours FLM1949C5RR, Mate FLM2108V9YG
Last Failover at: 08:46:30 UTC Jul 18 2024
This host: Primary - Active
Active time: 1999 (sec)
slot 0: UCSB-B200-M3-U hw/sw rev (0.0/9.18(4)210) status (Up Sys)
Interface diagnostic (0.0.0.0): Normal (Waiting)
Interface Inside (192.168.75.10): Link Down (Shutdown)
Interface Outside (192.168.76.10): Normal (Not-Monitored)
slot 1: snort rev (1.0) status (up)
slot 2: diskstatus rev (1.0) status (up)
Other host: Secondary - Standby Ready
Active time: 1466 (sec)
slot 0: UCSB-B200-M3-U hw/sw rev (0.0/9.18(4)210) status (Up Sys)
Interface diagnostic (0.0.0.0): Normal (Waiting)
Interface Inside (192.168.75.11): Link Down (Shutdown)
Interface Outside (192.168.76.11): Normal (Not-Monitored)
slot 1: snort rev (1.0) status (up)
slot 2: diskstatus rev (1.0) status (up)
Stateful Failover Logical Update Statistics
<output omitted>
步驟 3. 在次要裝置上執行相同的動作。
步驟 4. 在 LINA CLI 中,執行 show failover state 命令:
firepower# show failover state
State Last Failure Reason Date/Time
This host - Primary
Active None
Other host - Secondary
Standby Ready Comm Failure 18:32:56 EEST Jul 21 2016
====Configuration State===
Sync Done
====Communication State===
Mac set
firepower#
步驟 5. 透過主要裝置(LINA CLI)確認組態:
> show running-config failover
failover
failover lan unit primary
failover lan interface FOVER Port-channel3
failover replication http
failover mac address Ethernet1/4 aaaa.bbbb.1111 aaaa.bbbb.2222
failover mac address Port-channel2.202 aaaa.bbbb.3333 aaaa.bbbb.4444
failover link FOVER Port-channel3
failover interface ip FOVER 172.16.51.1 255.255.255.0 standby 172.16.51.2
> show running-config interface
!
interface Port-channel2
no nameif
no security-level
no ip address
!
interface Port-channel2.202
vlan 202
nameif Outside
cts manual
propagate sgt preserve-untag
policy static sgt disabled trusted
security-level 0
ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11
!
interface Port-channel3
description LAN/STATE Failover Interface
!
interface Ethernet1/1
management-only
nameif diagnostic
security-level 0
no ip address
!
interface Ethernet1/4
shutdown
nameif Inside
security-level 0
ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11
>
工作 4: 切換容錯移轉角色
工作需求:
在 FMC 中,將容錯移轉角色從「主要/作用中」、「次要/待命」切換成「主要/待命」、「次要/作用中」
解決方案:
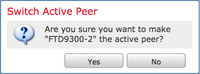
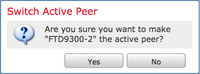
步驟 1. 選取圖示,如圖所示。
步驟2.確認操作。
您可以使用show failover history命令輸出:
| 在新活動專案上 |
在新待機模式中 |
| > show failover history
==========================================================================
從州到州的原因
========================================================================== 世界協調時2024年7月18日09時27分11秒
備用就緒僅啟用其他裝置希望我啟用
(通過config命令設定) 世界協調時2024年7月18日09時27分11秒
僅啟用活動排出其他裝置需要啟用
(通過config命令設定) 世界協調時2024年7月18日09時27分11秒
Active Drain Active Applying Config其他裝置需要啟用
(通過config命令設定) 世界協調時2024年7月18日09時27分11秒
Active Applying Config Active Config Applied Other unit wes me Active
(通過config命令設定) 世界協調時2024年7月18日09時27分11秒
Active Config Applied Active Other unit wes me Active
(通過config命令設定) |
> show failover history
==========================================================================
從州到州的原因
========================================================================== 世界協調時2024年7月18日09時27分11秒
通過config命令設定活動備用就緒
(無活動故障轉移) |
步驟 4. 驗證完畢後,請再次將主要裝置設為「作用中」。
工作 5: 分割 HA 配對
工作需求:
在 FMC 中分割容錯移轉配對。
解決方案:
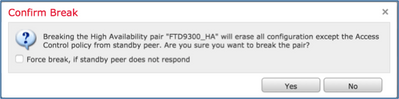
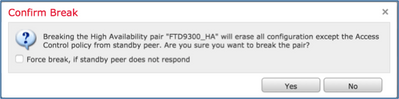
步驟 1. 選取圖示,如圖所示。

步驟 2. 檢查通知,如圖所示。
步驟 3. 注意訊息,如圖所示。

步驟4.從FMC GUI或CLI驗證結果
在執行 HA 分割之前和之後,主要裝置上的 show running-config:
| HA中斷前的主/備用裝置 |
HA中斷後的主裝置 |
| > show running-config
:已儲存 :
:序列號:FLM1949C5RR
:硬體:FPR4K-SM-24,73850 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname firepower
enable password ***** encrypted
strong-cryption-disable
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
no nameif
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
無安全級別
no ip address
!
interface Port-channel2.202
vlan 202
nameif Outside
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11
!
interface Port-channel3
說明LAN/STATE故障切換介面
!
interface Ethernet1/1
僅管理
nameif diagnostic
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
no ip address
!
interface Ethernet1/4
nameif Inside
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11
!
ftp mode passive
ngips conn-match vlan-id
object-group-search訪問控制
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268434433:ACCESS POLICY:acp_simple — 預設
access-list CSM_FW_ACL_ remark rule-id 268434433:L4 RULE:預設操作規則
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434433
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
mtu Outside 1500
mtu diagnostic 1500
mtu Inside 1500
容錯移轉
failover lan unit primary
failover lan interface FOVER Port-channel3
故障切換複製http
故障轉移mac address Ethernet1/4 aaaa.bbb.1111 aaaa.bbb.2222
故障轉移mac address Port-channel2.202 aaaa.bbb.3333 aaaa.bbb.4444
故障切換鏈路FOVER Port-channel3
故障切換介面ip從172.16.51.1 255.255.255.0備用172.16.51.2 <省略部分輸出> |
>資訊:此裝置當前處於備用狀態。通過禁用故障轉移,此裝置將保持備用狀態。 > show running-config
:已儲存 :
:序列號:FLM1949C5RR
:硬體:FPR4K-SM-24,73850 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname firepower
enable password ***** encrypted
strong-cryption-disable
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
關機
no nameif
無安全級別
no ip address
!
interface Port-channel3
關機
no nameif
無安全級別
no ip address
!
interface Ethernet1/1
僅管理
關機
no nameif
無安全級別
no ip address
!
interface Ethernet1/4
關機
no nameif
無安全級別
no ip address
!
ftp mode passive
ngips conn-match vlan-id
object-group-search訪問控制
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268439552:ACCESS POLICY:acp_simple — 必填
access-list CSM_FW_ACL_ remark rule-id 268439552:L7 RULE:rule1
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268439552
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
無故障切換
<省略部分輸出>
|
| HA中斷之前的輔助/主用裝置 |
HA中斷後的輔助裝置 |
| >show running-config
:已儲存 :
:序列號:FLM2108V9YG
:硬體:FPR4K-SM-24,73850 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname firepower
enable password ***** encrypted
strong-cryption-disable
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
no nameif
無安全級別
no ip address
!
interface Port-channel2.202
vlan 202
nameif Outside
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11
!
interface Port-channel3
說明LAN/STATE故障切換介面
!
interface Ethernet1/1
僅管理
nameif diagnostic
安全級別0
no ip address
!
interface Ethernet1/4
nameif Inside
安全級別0
ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11
!
ftp mode passive
ngips conn-match vlan-id
object-group-search訪問控制
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268439552:ACCESS POLICY:acp_simple — 必填
access-list CSM_FW_ACL_ remark rule-id 268439552:L7 RULE:rule1
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268439552
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
mtu Outside 1500
mtu diagnostic 1500
mtu Inside 1500
容錯移轉
故障轉移lan裝置輔助
failover lan interface FOVER Port-channel3
故障切換複製http
故障切換鏈路FOVER Port-channel3
故障切換介面ip從172.16.51.1 255.255.255.0備用172.16.51.2 <省略部分輸出> |
> show running-config
:已儲存 :
:序列號:FLM2108V9YG
:硬體:FPR4K-SM-24,73850 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname firepower
enable password ***** encrypted
strong-cryption-disable
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
no nameif
無安全級別
no ip address
!
interface Port-channel2.202
vlan 202
nameif Outside
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 192.168.76.10 255.255.255.0 standby 192.168.76.11
!
interface Port-channel3
no nameif
無安全級別
no ip address
!
interface Ethernet1/1
僅管理
nameif diagnostic
安全級別0
no ip address
!
interface Ethernet1/4
nameif Inside
安全級別0
ip address 192.168.75.10 255.255.255.0 standby 192.168.75.11
!
ftp mode passive
ngips conn-match vlan-id
object-group-search訪問控制
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268439552:ACCESS POLICY:acp_simple — 必填
access-list CSM_FW_ACL_ remark rule-id 268439552:L7 RULE:rule1
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268439552
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
mtu Outside 1500
mtu diagnostic 1500
mtu Inside 1500
無故障切換
no monitor-interface外部
no monitor-interface service-module <省略部分輸出> |
HA 分割的主要注意事項:
| 主/備用裝置 |
輔助/主用裝置 |
|
|
- 會移除所有容錯移轉組態
- 備用IP將保留,但在下次部署中移除
|
步驟 5. 完成此工作後,請重新建立 HA 配對。
任務6.刪除HA對
此任務基於使用7.2.8軟體的41xx上的HA設定。在這種情況下,裝置最初處於以下狀態:
工作需求:
從FMC中刪除故障轉移對。
解決方案:
步驟1。選擇如下圖所示的圖示:

步驟2.檢查通知並進行確認,如下圖所示:
步驟 3. 刪除 HA 後,兩個裝置均會從 FMC 中取消註冊(移除)。
LINA CLI 傳回的 show running-config 結果,如下表所示:
| 主裝置(備用)
|
輔助裝置(活動)
|
| > show running-config
:已儲存 :
:序列號:FLM1949C5RR
:硬體:FPR4K-SM-24,73853 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname Firepower-module1
enable password ***** encrypted
strong-cryption-disable
no asp inspect-dp ack-passthrough
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
no nameif
無安全級別
no ip address
!
interface Port-channel2.202
vlan 202
nameif NET202
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.202.1 255.255.255.0 standby 172.16.202.2
!
interface Port-channel2.203
vlan 203
nameif NET203
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.203.1 255.255.255.0 standby 172.16.203.2
!
interface Port-channel3
說明LAN/STATE故障切換介面
!
interface Ethernet1/1
僅管理
nameif diagnostic
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
no ip address
!
interface Ethernet1/4
nameif NET204
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.204.1 255.255.255.0 standby 172.16.204.2
!
ftp mode passive
ngips conn-match vlan-id
no object-group-search access-control
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268434433:ACCESS POLICY:acp_simple — 預設
access-list CSM_FW_ACL_ remark rule-id 268434433:L4 RULE:預設操作規則
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434433
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
tcp選項md5 clear
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
mtu NET202 1500
mtu NET203 1500
mtu diagnostic 1500
mtu NET204 1500
容錯移轉
failover lan unit primary
failover lan interface FOVER Port-channel3
故障切換複製http
故障切換鏈路FOVER Port-channel3
故障切換介面ip從172.16.51.1 255.255.255.0備用172.16.51.2
monitor-interface NET202
monitor-interface NET203
icmp無法連線速率限制1 burst-size 1 <省略部分輸出>
> show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0配置
Port-channel2.203 NET203 172.16.203.1 255.255.255.0配置
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.1 255.255.255.0配置
當前IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.2 255.255.255.0配置
Port-channel2.203 NET203 172.16.203.2 255.255.255.0配置
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.2 255.255.255.0配置 > show failover
故障切換開啟
故障切換裝置主裝置
故障轉移LAN介面:FOVER Port-channel3(up)
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面4(共1291個)
未設定MAC地址移動通知間隔
故障切換複製http
版本:9.18(4)210,Mate 9.18(4)210
序列號:我們的FLM1949C5RR,配對FLM2108V9YG
上次故障轉移時間:世界協調時2024年7月16日13時56分37秒
此主機:主要 — 備用就緒
活動時間:0(秒)
插槽0:UCSB-B200-M3-U硬體/軟體版本(0.0/9.18(4)210)狀態(啟動系統)
Interface NET202(172.16.202.2):正常(受監控)
Interface NET203(172.16.203.2):正常(受監控)
介面診斷(0.0.0.0):正常(等待)
Interface NET204(172.16.204.2):正常(受監控)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up)
其他主機:輔助 — 活動
活動時間:70293(秒)
Interface NET202(172.16.202.1):正常(受監控)
Interface NET203(172.16.203.1):正常(受監控)
介面診斷(0.0.0.0):正常(等待)
Interface NET204(172.16.204.1):正常(受監控)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up) <省略部分輸出> |
> show running-config
:已儲存 :
:序列號:FLM2108V9YG
:硬體:FPR4K-SM-24,73853 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname Firepower-module1
enable password ***** encrypted
strong-cryption-disable
no asp inspect-dp ack-passthrough
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
no nameif
無安全級別
no ip address
!
interface Port-channel2.202
vlan 202
nameif NET202
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.202.1 255.255.255.0 standby 172.16.202.2
!
interface Port-channel2.203
vlan 203
nameif NET203
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.203.1 255.255.255.0 standby 172.16.203.2
!
interface Port-channel3
說明LAN/STATE故障切換介面
!
interface Ethernet1/1
僅管理
nameif diagnostic
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
no ip address
!
interface Ethernet1/4
nameif NET204
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.204.1 255.255.255.0 standby 172.16.204.2
!
ftp mode passive
ngips conn-match vlan-id
no object-group-search access-control
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268434433:ACCESS POLICY:acp_simple — 預設
access-list CSM_FW_ACL_ remark rule-id 268434433:L4 RULE:預設操作規則
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434433
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
tcp選項md5 clear
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
mtu NET202 1500
mtu NET203 1500
mtu diagnostic 1500
mtu NET204 1500
容錯移轉
故障轉移lan裝置輔助
failover lan interface FOVER Port-channel3
故障切換複製http
故障切換鏈路FOVER Port-channel3
故障切換介面ip從172.16.51.1 255.255.255.0備用172.16.51.2
monitor-interface NET202
monitor-interface NET203
icmp無法連線速率限制1 burst-size 1 <省略部分輸出>
>show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0配置
Port-channel2.203 NET203 172.16.203.1 255.255.255.0配置
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.1 255.255.255.0配置
當前IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0配置
Port-channel2.203 NET203 172.16.203.1 255.255.255.0配置
Port-channel3 FOVER 172.16.51.2 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.1 255.255.255.0配置 > show failover
故障切換開啟
故障轉移單元輔助
故障轉移LAN介面:FOVER Port-channel3(up)
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面4(共1291個)
未設定MAC地址移動通知間隔
故障切換複製http
版本:9.18(4)210,Mate 9.18(4)210
序列號:我們的FLM2108V9YG,配對FLM1949C5RR
上次故障轉移時間:世界協調時2024年7月16日13時42分35秒
此主機:輔助 — 活動
活動時間:70312(秒)
插槽0:UCSB-B200-M3-U硬體/軟體版本(0.0/9.18(4)210)狀態(啟動系統)
Interface NET202(172.16.202.1):正常(受監控)
Interface NET203(172.16.203.1):正常(受監控)
介面診斷(0.0.0.0):正常(等待)
Interface NET204(172.16.204.1):正常(受監控)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up)
其他主機:主要 — 備用就緒
活動時間:0(秒)
插槽0:UCSB-B200-M3-U硬體/軟體版本(0.0/9.18(4)210)狀態(啟動系統)
Interface NET202(172.16.202.2):正常(受監控)
Interface NET203(172.16.203.2):正常(受監控)
介面診斷(0.0.0.0):正常(等待)
Interface NET204(172.16.204.2):正常(受監控)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up) <省略部分輸出> |
步驟 4. 兩個 FTD 裝置均會從 FMC 中取消註冊:
> show managers
No managers configured.
FMC 中「停用 HA 」選項的主要注意事項:
| 主裝置 |
輔助裝置
|
| 會從 FMC 中移除裝置。 不會從 FTD 裝置移除任何組態. |
會從 FMC 中移除裝置。 不會從 FTD 裝置移除任何組態. |
案例 1
執行「configure high-availability disable」命令以從作用中FTD裝置移除容錯移轉組態:
> configure high-availability disable ?
Optional parameter to clear interfaces (clear-interfaces) optional parameter to clear interfaces (clear-interfaces) (clear-interfaces)
<cr>
> configure high-availability disable
High-availability will be disabled. Do you really want to continue?
Please enter 'YES' or 'NO': yes
Successfully disabled high-availability.
結果是:
| 主裝置(非待機)
|
輔助裝置(非活動)
|
> INFO: This unit is currently in standby state. By disabling failover, this unit will remain in standby state.
> show failover
Failover Off (pseudo-Standby)
Failover unit Primary
Failover LAN Interface: FOVER Port-channel3 (up)
Reconnect timeout 0:00:00
Unit Poll frequency 1 seconds, holdtime 15 seconds
Interface Poll frequency 5 seconds, holdtime 25 seconds
Interface Policy 1
Monitored Interfaces 0 of 1291 maximum
MAC Address Move Notification Interval not set
failover replication http
> show ip
System IP Addresses:
Interface Name IP address Subnet mask Method
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
Current IP Addresses:
Interface Name IP address Subnet mask Method
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
|
> show failover
Failover Off
Failover unit Secondary
Failover LAN Interface: not Configured
Reconnect timeout 0:00:00
Unit Poll frequency 1 seconds, holdtime 15 seconds
Interface Poll frequency 5 seconds, holdtime 25 seconds
Interface Policy 1
Monitored Interfaces 4 of 1291 maximum
MAC Address Move Notification Interval not set
> show ip
System IP Addresses:
Interface Name IP address Subnet mask Method
Port-channel2.202 NET202 172.16.202.1 255.255.255.0 CONFIG
Port-channel2.203 NET203 172.16.203.1 255.255.255.0 CONFIG
Ethernet1/4 NET204 172.16.204.1 255.255.255.0 CONFIG
Current IP Addresses:
Interface Name IP address Subnet mask Method
Port-channel2.202 NET202 172.16.202.1 255.255.255.0 CONFIG
Port-channel2.203 NET203 172.16.203.1 255.255.255.0 CONFIG
Ethernet1/4 NET204 172.16.204.1 255.255.255.0 CONFIG
|
| 主要(非待機)
|
輔助(非活動)
|
| > show running-config
:已儲存 :
:序列號:FLM1949C5RR
:硬體:FPR4K-SM-24,73853 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname Firepower-module1
enable password ***** encrypted
strong-cryption-disable
no asp inspect-dp ack-passthrough
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
關機
no nameif
無安全級別
no ip address < — 已刪除IP
!
interface Port-channel3
說明LAN/STATE故障切換介面
!
interface Ethernet1/1
僅管理
關機
no nameif
無安全級別
no ip address
!
interface Ethernet1/4
關機
no nameif
無安全級別
no ip address
!
ftp mode passive
ngips conn-match vlan-id
no object-group-search access-control
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268434433:ACCESS POLICY:acp_simple — 預設
access-list CSM_FW_ACL_ remark rule-id 268434433:L4 RULE:預設操作規則
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434433
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
tcp選項md5 clear
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
無故障切換
failover lan unit primary
failover lan interface FOVER Port-channel3
故障切換複製http
故障切換鏈路FOVER Port-channel3
故障切換介面ip從172.16.51.1 255.255.255.0備用172.16.51.2
no monitor-interface service-module <省略部分輸出> |
> show running-config
:已儲存 :
:序列號:FLM2108V9YG
:硬體:FPR4K-SM-24,73853 MB RAM,CPU Xeon E5系列2200 MHz,2個CPU(48個核心)
:
NGFW版本7.2.8
!
hostname Firepower-module1
enable password ***** encrypted
strong-cryption-disable
no asp inspect-dp ack-passthrough
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
姓名
no mac-address auto !
interface Port-channel2
no nameif
無安全級別
no ip address
!
interface Port-channel2.202
vlan 202
nameif NET202
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.202.1 255.255.255.0 standby 172.16.202.2
!
interface Port-channel2.203
vlan 203
nameif NET203
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.203.1 255.255.255.0 standby 172.16.203.2
!
interface Port-channel3
no nameif
無安全級別
no ip address
!
interface Ethernet1/1
僅管理
nameif diagnostic
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
no ip address
!
interface Ethernet1/4
nameif NET204
cts manual(cts手冊)
propagate sgt preserve-untag
策略靜態sgt disabled trusted
安全級別0
ip address 172.16.204.1 255.255.255.0 standby 172.16.204.2
!
ftp mode passive
ngips conn-match vlan-id
no object-group-search access-control
access-group CSM_FW_ACL_ global
access-list CSM_FW_ACL_ remark rule-id 9998:預過濾器策略:預設通道和優先順序原則
access-list CSM_FW_ACL_ remark rule-id 9998:RULE:預設隧道操作規則
access-list CSM_FW_ACL_ advanced permit ipinip any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any eq 3544 any range 1025 65535 rule-id 9998
access-list CSM_FW_ACL_ advanced permit udp any range 1025 65535 any eq 3544 rule-id 9998
access-list CSM_FW_ACL_ advanced permit 41 any any rule-id 9998
access-list CSM_FW_ACL_ advanced permit gre any any rule-id 9998
access-list CSM_FW_ACL_ remark rule-id 268434433:ACCESS POLICY:acp_simple — 預設
access-list CSM_FW_ACL_ remark rule-id 268434433:L4 RULE:預設操作規則
access-list CSM_FW_ACL_ advanced permit ip any any rule-id 268434433
!
tcp-map UM_STATIC_TCP_MAP
tcp-options range 6 7 allow
tcp選項範圍9 18 allow
tcp-options range 20 255 allow
tcp選項md5 clear
urgent-flag allow
!
無尋呼機
no logging message 106015
no logging message 313001
no logging message 313008
no logging message 106023
no logging message 710003
no logging message 106100
no logging message 302015
no logging message 302014
no logging message 302013
no logging message 302018
no logging message 302017
no logging message 302016
no logging message 302021
no logging message 302020
mtu NET202 1500
mtu NET203 1500
mtu diagnostic 1500
mtu NET204 1500
無故障切換
monitor-interface NET202
monitor-interface NET203
no monitor-interface service-module |
在作用中FTD CLI上停用HA的注意事項:
| 活動單元
|
備用裝置
|
|
|
- 會移除介面組態.
- 未刪除故障轉移配置,但已禁用故障轉移(偽備用)
|
此時,您也可以在非備用裝置上禁用HA。
案例2(不建議)
警告:此方案會導致主用/主用情況,因此不建議使用。僅顯示用於感知。
執行「configure high-availability disable」命令以從備用FTD裝置移除故障切換配置:
> configure high-availability disable
High-availability will be disabled. Do you really want to continue?
Please enter 'YES' or 'NO': YES
Successfully disabled high-availability.
結果是:
| 主要(非待機) |
輔助(活動)
|
| > show failover
故障切換關閉
故障轉移單元輔助
故障轉移LAN介面:未配置
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面4(共1291個)
未設定MAC地址移動通知間隔
> show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0手冊< — 裝置使用與活動狀態相同的IP!
Port-channel2.203 NET203 172.16.203.1 255.255.255.0手冊
Ethernet1/4 NET204 172.16.204.1 255.255.255.0手冊
當前IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0手冊
Port-channel2.203 NET203 172.16.203.1 255.255.255.0手冊
Ethernet1/4 NET204 172.16.204.1 255.255.255.0手冊
|
> show failover
故障切換開< — 未禁用故障切換
故障轉移單元輔助
故障轉移LAN介面:FOVER Port-channel3(up)
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面4(共1291個)
未設定MAC地址移動通知間隔
故障切換複製http
版本:9.18(4)210,Mate 9.18(4)210
序列號:我們的FLM2108V9YG,配對FLM1949C5RR
上次故障轉移時間:12:44:06 UTC 2024年7月17日
此主機:輔助 — 活動
活動時間:632(秒)
插槽0:UCSB-B200-M3-U硬體/軟體版本(0.0/9.18(4)210)狀態(啟動系統)
介面診斷(0.0.0.0):正常(等待)
Interface NET204(172.16.204.1):正常(受監控)
Interface NET203(172.16.203.1):正常(受監控)
Interface NET202(172.16.202.1):正常(受監控)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up)
其他主機:主要 — 已禁用
活動時間:932(秒)
插槽0:UCSB-B200-M3-U硬體/軟體版本(0.0/9.18(4)210)狀態(啟動系統)
介面診斷(0.0.0.0):未知(正在等待)
Interface NET204(172.16.204.2):未知(被監視)
Interface NET203(172.16.203.2):未知(被監視)
Interface NET202(172.16.202.2):未知(被監視)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up) > show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0手動< — 裝置使用與ex-Standby相同的IP!
Port-channel2.203 NET203 172.16.203.1 255.255.255.0手冊
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.1 255.255.255.0手冊
當前IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0手冊
Port-channel2.203 NET203 172.16.203.1 255.255.255.0手冊
Port-channel3 FOVER 172.16.51.2 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.1 255.255.255.0手冊 |
在作用中FTD CLI上停用HA的注意事項:
| 活動單元
|
備用裝置
|
- 故障切換配置未刪除,仍保持啟用狀態
- 裝置使用的IP與ex-Standby裝置相同
|
|
案例 3
執行「configure high-availability disable clear-interfaces」命令以從作用中FTD裝置移除故障切換配置:
> configure high-availability disable clear-interfaces
High-availability will be disabled. Do you really want to continue?
Please enter 'YES' or 'NO': yes
Successfully disabled high-availability.
>
結果是:
| 主要(非待機) |
輔助(非活動)
|
| > show failover
關閉故障轉移(偽備用)
故障切換裝置主裝置
故障轉移LAN介面:FOVER Port-channel3(up)
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面0(共1291個)
未設定MAC地址移動通知間隔
故障切換複製http
> show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
當前IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
>
|
> show failover
故障切換關閉
故障轉移單元輔助
故障轉移LAN介面:未配置
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面0(共1291個)
未設定MAC地址移動通知間隔
> show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
當前IP地址:
介面名稱IP位址子網路遮罩方法
>
|
從作用中FTD CLI停用HA以及「clear-interfaces」需注意的要點:
| 活動單元
|
備用裝置
|
|
|
- 未刪除故障轉移配置,但已禁用故障轉移(偽備用)
- IP將被刪除
|
案例 4
執行「configure high-availability disable clear-interfaces」命令以從備用FTD裝置移除故障切換配置:
> configure high-availability disable clear-interfaces
High-availability will be disabled. Do you really want to continue?
Please enter 'YES' or 'NO': YES
Successfully disabled high-availability.
>
結果是:
| 主要(非待機) |
輔助(活動)
|
| > show failover
故障切換關閉
故障轉移單元輔助
故障轉移LAN介面:未配置
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面0(共1291個)
未設定MAC地址移動通知間隔
> show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
當前IP地址:
介面名稱IP位址子網路遮罩方法
>
|
> show failover
故障切換開啟
故障轉移單元輔助
故障轉移LAN介面:FOVER Port-channel3(up)
重新連線超時0:00:00
裝置輪詢頻率1秒,保持時間15秒
介面輪詢頻率5秒,保持時間25秒
介面策略1
受監控介面4(共1291個)
未設定MAC地址移動通知間隔
故障切換複製http
版本:9.18(4)210,Mate 9.18(4)210
序列號:我們的FLM2108V9YG,配對FLM1949C5RR
上次故障轉移時間:世界協調時2024年7月18日07時6分56秒
此主機:輔助 — 活動
活動時間:1194(秒)
插槽0:UCSB-B200-M3-U硬體/軟體版本(0.0/9.18(4)210)狀態(啟動系統)
介面診斷(0.0.0.0):正常(等待)
Interface NET204(172.16.204.1):正常(受監控)
Interface NET202(172.16.202.1):正常(受監控)
Interface NET203(172.16.203.1):正常(受監控)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up)
其他主機:主要 — 已禁用
活動時間:846(秒)
插槽0:UCSB-B200-M3-U硬體/軟體版本(0.0/9.18(4)210)狀態(啟動系統)
介面診斷(0.0.0.0):未知(正在等待)
Interface NET204(172.16.204.2):未知(被監視)
Interface NET202(172.16.202.2):未知(被監視)
Interface NET203(172.16.203.2):未知(被監視)
插槽1:snort rev(1.0)狀態(up)
插槽2:diskstatus rev(1.0)status(up) > show ip
系統IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0手冊
Port-channel2.203 NET203 172.16.203.1 255.255.255.0手冊
Port-channel3 FOVER 172.16.51.1 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.1 255.255.255.0手冊
當前IP地址:
介面名稱IP位址子網路遮罩方法
Port-channel2.202 NET202 172.16.202.1 255.255.255.0手冊
Port-channel2.203 NET203 172.16.203.1 255.255.255.0手冊
Port-channel3 FOVER 172.16.51.2 255.255.255.0 unset
Ethernet1/4 NET204 172.16.204.1 255.255.255.0手冊 |
從作用中FTD CLI停用HA以及「clear-interfaces」需注意的要點:
步驟 6. 完成工作後,請將裝置重新註冊至 FMC 並啟用 HA 配對。
工作 7: 暫停 HA
工作需求:
透過 FTD CLISH CLI 暫停 HA
解決方案:
步驟 1. 在主要 FTD 上,執行下列命令並確認(輸入 YES)。
> configure high-availability suspend
Please ensure that no deployment operation is in progress before suspending high-availability.
Please enter 'YES' to continue if there is no deployment operation in progress and 'NO' if you wish to abort: YES
Successfully suspended high-availability.
步驟 2. 確認主要裝置上的變更:
> show high-availability config
Failover Off
Failover unit Primary
Failover LAN Interface: fover_link Ethernet1/4 (up)
Reconnect timeout 0:00:00
Unit Poll frequency 1 seconds, holdtime 15 seconds
Interface Poll frequency 5 seconds, holdtime 25 seconds
Interface Policy 1
Monitored Interfaces 1 of 1041 maximum
MAC Address Move Notification Interval not set
failover replication http
步驟 3. 次要裝置上的結果:
> show high-availability config
Failover Off (pseudo-Standby)
Failover unit Secondary
Failover LAN Interface: fover_link Ethernet1/4 (up)
Reconnect timeout 0:00:00
Unit Poll frequency 1 seconds, holdtime 15 seconds
Interface Poll frequency 5 seconds, holdtime 25 seconds
Interface Policy 1
Monitored Interfaces 1 of 1041 maximum
MAC Address Move Notification Interval not set
failover replication http
步驟 4. 恢復主要裝置上的 HA:
> configure high-availability resume
Successfully resumed high-availablity.
> .
No Active mate detected
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Beginning configuration replication: Sending to mate.
End Configuration Replication to mate
>
> show high-availability config
Failover On
Failover unit Primary
Failover LAN Interface: fover_link Ethernet1/4 (up)
Reconnect timeout 0:00:00
Unit Poll frequency 1 seconds, holdtime 15 seconds
Interface Poll frequency 5 seconds, holdtime 25 seconds
Interface Policy 1
Monitored Interfaces 1 of 1041 maximum
MAC Address Move Notification Interval not set
failover replication http
步驟 5. 恢復 HA 後,次要裝置上的結果:
> ..
Detected an Active mate
Beginning configuration replication from mate.
WARNING: Failover is enabled but standby IP address is not configured for this interface.
WARNING: Failover is enabled but standby IP address is not configured for this interface.
End configuration replication from mate.
>
> show high-availability config
Failover On
Failover unit Secondary
Failover LAN Interface: fover_link Ethernet1/4 (up)
Reconnect timeout 0:00:00
Unit Poll frequency 1 seconds, holdtime 15 seconds
Interface Poll frequency 5 seconds, holdtime 25 seconds
Interface Policy 1
Monitored Interfaces 1 of 1041 maximum
MAC Address Move Notification Interval not set
failover replication http
>
常見問題 (FAQ)
複製配置後,是立即(逐行)儲存還是複製結束時儲存?
在複寫結束時。 證據就是在 debug fover sync 命令輸出的結尾,會顯示組態/命令複寫:
cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1506 remark rule-id 268442578: L7 RULE: ACP_Rule_500
cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1507 advanced permit tcp object-group group_10 eq 48894 object-group group_10 eq 23470 vlan eq 1392 rule-id 268442578
cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1508 remark rule-id 268442078: ACCESS POLICY: mzafeiro_500 - Default
cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ line 1509 remark rule-id 268442078: L4 RULE: DEFAULT ACTION RULE
...
cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ advanced permit tcp object-group group_2 eq 32881 object-group group_433 eq 39084 vlan eq 1693 rule-id 268442076
cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268442077: ACCESS POLICY: mzafeiro_ACP1500 - Mandatory
cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268442077: L7 RULE: ACP_Rule_1500
cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ advanced permit tcp object-group group_6 eq 8988 object-group group_311 eq 32433 vlan eq 619 rule-id 268442077
cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268440577: ACCESS POLICY: mzafeiro_ACP1500 - Default
cli_xml_server: frep_write_cmd: Cmd: no access-list CSM_FW_ACL_ line 1510 remark rule-id 268440577: L4 RULE: DEFAULT ACTION RULE
cli_xml_server: frep_write_cmd: Cmd: access-list CSM_FW_ACL_ advanced deny ip any any rule-id 268442078 event-log flow-start
cli_xml_server: frep_write_cmd: Cmd: crypto isakmp nat-traversal
cli_xml_server: frep_write_cmd: Cmd: no object-group network group_311
cli_xml_server: frep_write_cmd: Cmd: no object-group network group_433
cli_xml_server: frep_write_cmd: Cmd: no object-group network group_6
cli_xml_server: frep_write_cmd: Cmd: no object-group network group_2
cli_xml_server: frep_write_cmd: Cmd: write memory <--
如果裝置處於偽備用狀態(禁用故障轉移),然後您重新載入該裝置,而另一裝置已啟用故障轉移,並且處於活動狀態,將會發生什麼情況?
您最終會處於主用/主用情形(儘管從技術上講,這是主用/故障切換關閉)。 具體地說,就是裝置啟動後,容錯移轉便會停用,但裝置會使用與作用中裝置相同的 IP。因此,您實際上會有:
- 裝置-1:Active(作用中)
- 裝置-2:容錯移轉已關閉。裝置使用與Unit-1相同的資料IP,但使用不同的MAC地址。
如果手動禁用故障切換(配置高可用性掛起),然後重新載入裝置,故障切換配置會發生什麼情況?
禁用故障切換時,它不是永久更改(除非您決定顯式執行此操作,否則不會儲存在startup-config中)。 您可以用兩種不同的方法重新啟動/重新載入裝置,但第二種方法必須小心:
案例 1. 透過 CLISH 重新啟動
透過 CLISH 重新啟動不會要求確認。 因此,組態變更不會儲存在啟動組態中:
> configure high-availability suspend
Please ensure that no deployment operation is in progress before suspending high-availability.
Please enter 'YES' to continue if there is no deployment operation in progress and 'NO' if you wish to abort: YES
Successfully suspended high-availability.
running-config已禁用故障轉移。在這種情況下,裝置處於「待機」狀態,並按照預期進入偽待機狀態,以避免出現「主用/主用」情況:
firepower# show failover | include Failover
Failover Off (pseudo-Standby)
Failover unit Secondary
Failover LAN Interface: FOVER Ethernet1/1 (up)
startup-config仍然啟用故障轉移:
firepower# show startup | include failover
failover
failover lan unit secondary
failover lan interface FOVER Ethernet1/1
failover replication http
failover link FOVER Ethernet1/1
failover interface ip FOVER 192.0.2.1 255.255.255.0 standby 192.0.2.2
failover ipsec pre-shared-key *****
透過 CLISH 重新啟動裝置(reboot 命令):
> reboot
This command will reboot the system. Continue?
Please enter 'YES' or 'NO': YES
Broadcast message from root@
Threat Defense System: CMD=-stop, CSP-ID=cisco-ftd.6.2.2.81__ftd_001_JMX2119L05CYRIBVX1, FLAG=''
Cisco FTD stopping ...
裝置啟動後,容錯移轉便會啟用,因此裝置會進入容錯移轉交涉階段並嘗試偵測遠端對等:
User enable_1 logged in to firepower
Logins over the last 1 days: 1.
Failed logins since the last login: 0.
Type help or '?' for a list of available commands.
firepower> .
Detected an Active mate
案例 2. 透過 LINA CLI 重新啟動
透過 LINA 重新啟動(reload 命令)會要求確認。因此,如果您選擇Y(是),配置更改將儲存到startup-config:
firepower# reload
System config has been modified. Save? [Y]es/[N]o: Y <-- Be careful. This disables the failover in the startup-config
Cryptochecksum: 31857237 8658f618 3234be7c 854d583a
8781 bytes copied in 0.940 secs
Proceed with reload? [confirm]
firepower# show startup | include failover
no failover
failover lan unit secondary
failover lan interface FOVER Ethernet1/1
failover replication http
failover link FOVER Ethernet1/1
failover interface ip FOVER 192.0.2.1 255.255.255.0 standby 192.0.2.2
failover ipsec pre-shared-key *****
裝置啟動後,容錯移轉便會停用:
firepower# show failover | include Fail
Failover Off
Failover unit Secondary
Failover LAN Interface: FOVER Ethernet1/1 (up)
附註:要避免這種情況,請確保系統提示您時,不要將更改儲存到startup-config。
相關資訊
- 您可以在下列位置找到所有 Cisco Firepower Management Center 版本的組態設定指南:
導航思科安全防火牆威脅防禦文檔
- 您可以在下列位置找到所有 FXOS 機箱管理員版本和 CLI 的組態設定指南:
導航Cisco Firepower 4100/9300 FXOS文檔
- 思科全球技術協助中心(TAC)強烈建議使用以下視覺指南,以瞭解有關Cisco Firepower下一代安全技術的深入實用知識:
Cisco Firepower威脅防禦(FTD):下一代防火牆(NGFW)、下一代入侵防禦系統(NGIPS)和高級惡意軟體防護(AMP)的配置和故障排除最佳實踐
- 有關Firepower技術的所有配置和故障排除技術說明
思科安全防火牆管理中心








 意見
意見