Domain Filtering Overview
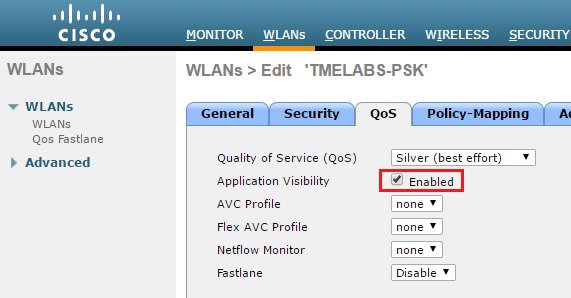
Domain Filtering is a new enhancement that is being introduced as part of the 8.3 release. This enhancement complements the Application Visibility Control (AVC) filtering currently available on the WLC. AVC filtering only supports the protocols and applications that are defined in the Protocol Pack for a given AirOS release allowing specific applications to be dropped, marked or rate-limited.
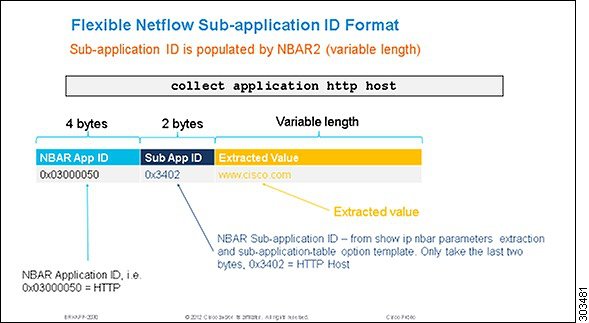
Domain Filtering is based on the NBAR2 engines filtering capabilities using field extraction. The latest NBAR2 engine supports 120 custom applications. URLs can be defined as a custom application and be classified by the engine:
-
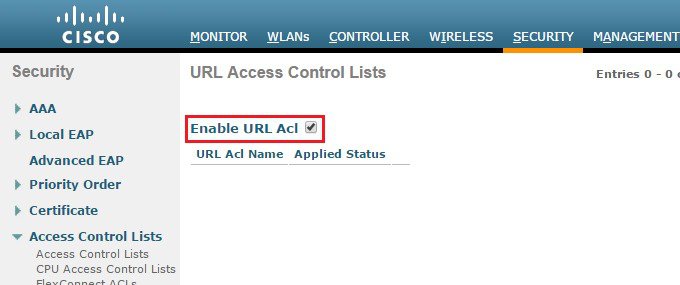
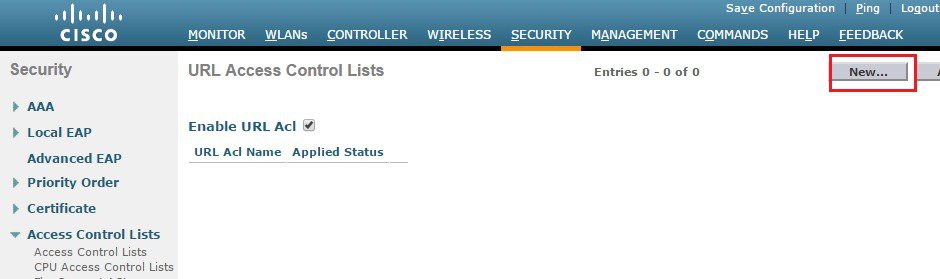
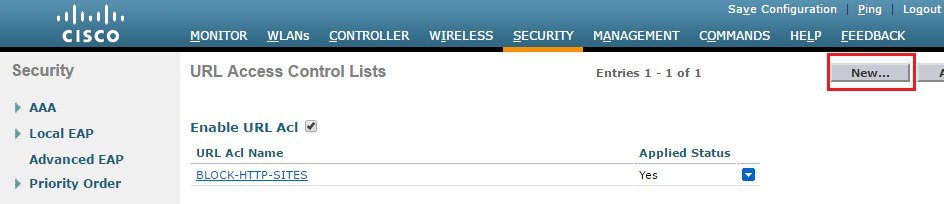
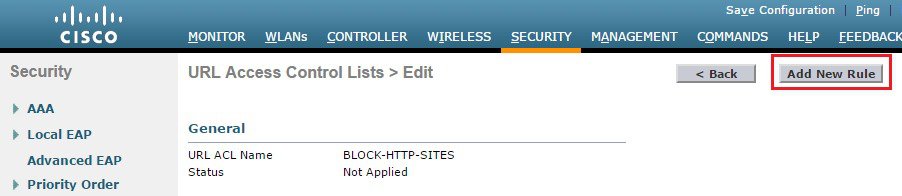
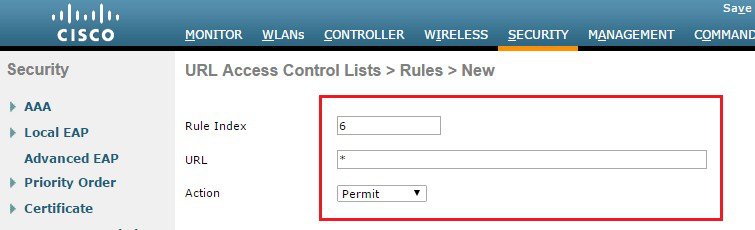
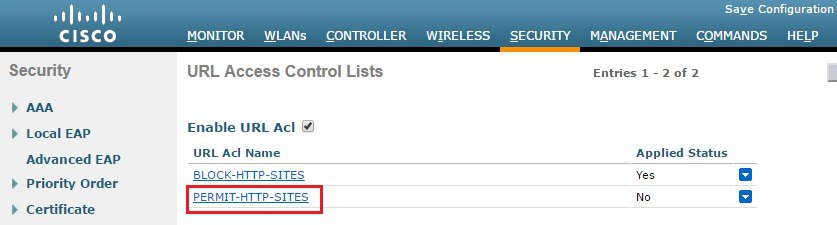
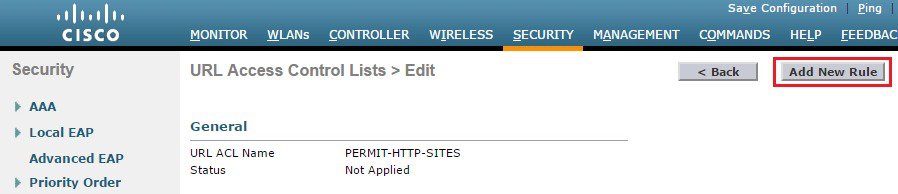
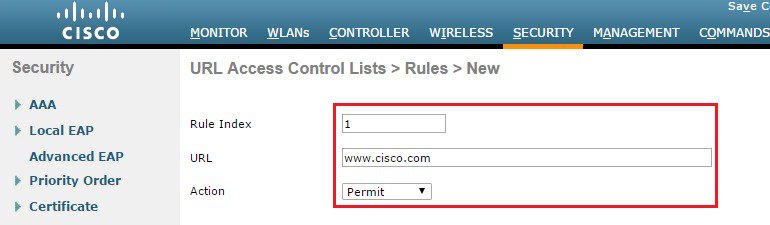
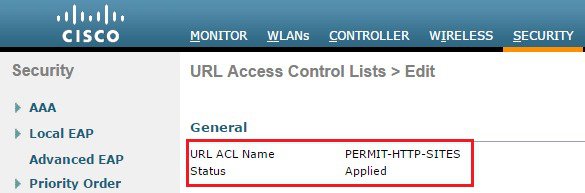
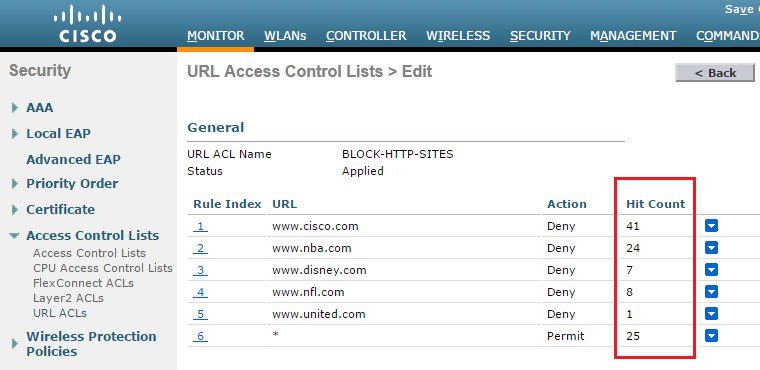
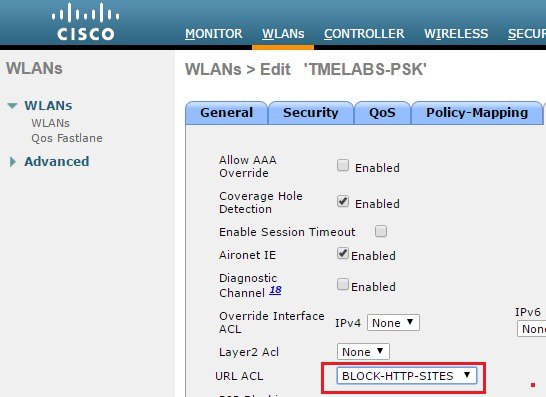
URLs are classified using ACLs defined on the WLC. Each ACL has rules defined that determine the URLs to be matched.
-
The NBAR2 engine is configured to extract the URL field (if present) in the packets passed to it. Field extraction is performed per flow to optimize performance.
-
The WLC passes HTTP packets to the NBAR2 engine to extract the URL. If present, the NBAR2 engine returns the host-name (for example www.cisco.com) as the URL to the WLC.
-
The WLC implements filtering logic for the extracted URLs and takes the appropriate forwarding action (i.e. permit or denies the flow).
Considerations
-
This release supports a maximum of 100 x URL ACLs:
-
Each ACL supports a maximum of 64 rules.
-
Each rule has either a permit or deny action. At least one permit rule must be defined per URL ACL for traffic to be permitted.
-
Each ACL has an implicit “deny all rule” as the last rule. If a URL does not match any of the rules, it is dropped by the WLC.
-
Each rule is inspected in order of precedence (lowest to highest). The first rule in the ACL that is matched is applied to the flow.
-
Each rule supports a maximum length 32 characters.
-
Each rule must match the exact subdomain, domain and top level domain you wish to match (example www.cisco.com, tools.cisco.com or partners.cisco.com).
-
Partial matches using wildcards or regular expressions are not supported in this release (example. www.c*.com or *.cisco.com).
-
No support for folders, file-names or extensions is provided in this release (example www.cisco.com/resources/index.html). A rule matching www.cisco.com will be applied to www.cisco.com/c/en/us/support.index.html as well as http://www.cisco.com/c/en/us/buy.html.
-
One wildcard (*) rule with a permit or deny action is supported per ACL. The wildcard matches all URLs.
-
-
-
No support for AVC Profiles for matched URLs is provided in this release. URL ACLs and rules are defined separately then applied to WLANs, Interfaces or Local Policies.
-
No support for IPv6 in this release (IPv4 support only).
-
No support for PI is provided in this release.
 Note |
This release supports HTTP URLs only. HTTPS URL support will be introduced in a later release. |








 Feedback
Feedback