Information About FlexConnect Groups
To organize and manage your FlexConnect access points, you can create FlexConnect Groups and assign specific access points to them.
All of the FlexConnect access points in a group share the same backup RADIUS server, CCKM, and local authentication configuration information. This feature is helpful if you have multiple FlexConnect access points in a remote office or on the floor of a building and you want to configure them all at once. For example, you can configure a backup RADIUS server for a FlexConnect rather than having to configure the same server on each access point.
FlexConnect Groups and Backup RADIUS Servers
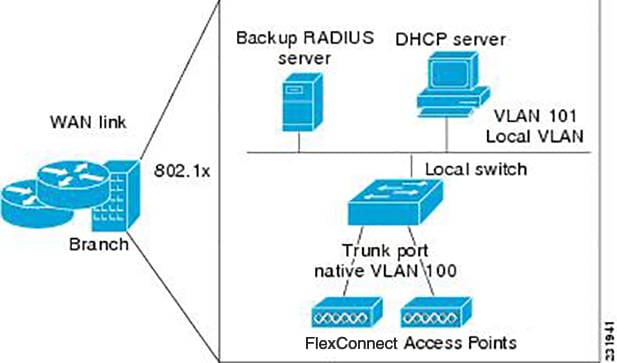
You can configure the controller to allow a FlexConnect access point in standalone mode to perform full 802.1X authentication to a backup RADIUS server. You can configure a primary backup RADIUS server or both a primary and secondary backup RADIUS server. These servers can be used when the FlexConnect access point is in of these two modes: standalone or connected.
FlexConnect Groups and CCKM
FlexConnect Groups are required for CCKM fast roaming to work with FlexConnect access points. CCKM fast roaming is achieved by caching a derivative of the master key from a full EAP authentication so that a simple and secure key exchange can occur when a wireless client roams to a different access point. This feature prevents the need to perform a full RADIUS EAP authentication as the client roams from one access point to another. The FlexConnect access points need to obtain the CCKM cache information for all the clients that might associate so they can process it quickly instead of sending it back to the controller. If, for example, you have a controller with 300 access points and 100 clients that might associate, sending the CCKM cache for all 100 clients is not practical. If you create a FlexConnect that includes a limited number of access points (for example, you create a group for four access points in a remote office), the clients roam only among those four access points, and the CCKM cache is distributed among those four access points only when the clients associate to one of them.
 Note |
CCKM fast roaming among FlexConnect and non-FlexConnect access points is not supported. |
 Note |
FlexConnect Groups is needed for CCKM to work. Flex group needs to be created for CCKM, 11r , and OKC , only then the caching can happen on an AP. The group name must be same between APS for a fast roaming to happen for 11r/CCKM. The group can be different for OKC as final check is done at Cisco WLC. |
FlexConnect Groups and Opportunistic Key Caching
Starting with the Cisco Wireless LAN Controller Release 7.0.116.0, FlexConnect groups accelerate Opportunistic Key Caching (OKC) to enable fast roaming of clients. OKC facilitates fast roaming by using PMK caching in access points that are in the same FlexConnect group.
OKC prevents the need to perform a full authentication as the client roams from one access point to another. FlexConnect groups store the cached key on the APs of the same group, accelerating the process. However, they are not required, as OKC will still happen between access points belonging to different FlexConnect groups and will use the cached key present on the Cisco WLC, provided that Cisco WLC is reachable and APs are in connected mode.
To see the PMK cache entries at the FlexConnect access point, use the show capwap reap pmk command. This feature is supported on Cisco FlexConnect access points only. The PMK cache entries cannot be viewed on Non-FlexConnect access points.
 Note |
The FlexConnect access point must be in connected mode when the PMK is derived during WPA2/802.1x authentication. |
When using FlexConnect groups for OKC or CCKM, the PMK-cache is shared only across the access points that are part of the same FlexConnect group and are associated to the same controller. If the access points are in the same FlexConnect group but are associated to different controllers that are part of the same mobility group, the PMK cache is not updated and CCKM roaming will fail but OKC roaming will still work.
 Note |
Fast roaming works only if the APs are in the same FlexConnect group for APs in FlexConnect mode, 802.11r . |
FlexConnect Groups and Local Authentication
You can configure the controller to allow a FlexConnect access point in standalone mode to perform LEAP, EAP-FAST, PEAP, or EAP-TLS authentication for up to 100 statically configured users. The controller sends the static list of usernames and passwords to each FlexConnect access point when it joins the controller. Each access point in the group authenticates only its own associated clients.
This feature is ideal for customers who are migrating from an autonomous access point network to a lightweight FlexConnect access point network and are not interested in maintaining a large user database or adding another hardware device to replace the RADIUS server functionality available in the autonomous access point.
 Note |
|
You have to provision a certificate to the AP because the AP has to send the certificate to the client. You must download the Vendor Device Certificate and the Vendor Certification Authority Certificate to the controller. The controller then pushes these certificates to the AP. If you do not configure a Vendor Device Certificate and the Vendor CA Certificate on the controller, the APs associating with the FlexConnect group download the self-signed certificate of the controller, which may not be recognized by many wireless clients.
With EAP-TLS, AP does not recognize and accept client certificate if the client root CA is different from the AP root CA. When you use Enterprise public key infrastructures (PKI), you must download a Vendor Device Certificate and Vendor CA Certificate to the controller so that the controller can push the certificates to the AP in the FlexConnect group. Without a common client and AP root CA, EAP-TLS fails on the local AP. The AP cannot check an external CA and relies on its own CA chain for client certificate validation.
The space on the AP for the local certificate and the CA certificate is around 7 Kb, which means that only short chains are adapted. Longer chains or multiple chains are not supported.
 Note |
This feature can be used with the FlexConnect backup RADIUS server feature. If a FlexConnect is configured with both a backup RADIUS server and local authentication, the FlexConnect access point always attempts to authenticate clients using the primary backup RADIUS server first, followed by the secondary backup RADIUS server (if the primary is not reachable), and finally the FlexConnect access point itself (if the primary and secondary are not reachable). |
For information about the number of FlexConnect groups and access point support for a Cisco WLC model, see the data sheet of the respective Cisco WLC model.
FlexConnect Groups and VLAN Support
You can configure VLAN Support and VLAN ID on a per FlexConnect group basis. This allows all APs in a FlexConnect group to inherit the VLAN configuration from the FlexConnect group including VLAN support, Native VLAN, and WLAN-VLAN mappings.
Deployment Considerations
-
When the override flag is set at the FlexConnect Group, modification of VLAN Support, Native VLAN ID, WLAN-VLAN mappings, and Inheritance-Level at the AP is not allowed.
-
An Inheritance-Level configuration is available at the FlexConnect AP. You have to set this to “Make VLAN AP Specific” to configure any AP-Specific VLAN Support, Native VLAN ID and VLAN-WLAN mappings on the AP. Note that you can modify this only when the override flag at the group is disabled.
To achieve this on the WLC GUI, choose , click on the AP name. In the FlexConnect tab, select Make VLAN AP Specific from the drop-down list.
Upgrade and Downgrade Considerations
-
When you upgrade to Release 8.1, if the FlexConnect group has WLAN-VLAN mappings, then after an upgrade, VLAN support is enabled and native VLAN is set to 1. Otherwise, the VLAN support remains disabled on the FlexConnect group. The override flag on the FlexConnect Group is disabled.
-
When you downgrade from Release 8.1, the VLAN Support and Native VLAN ID is on a per AP basis, and the WLAN-VLAN mappings follow the previous inheritance model.
Default FlexGroup
Default FlexGroup is a container where FlexConnect access points (APs), which are not a part of an administrator-configured FlexConnect group, are added automatically when they join the Cisco Wireless Controller. The Default FlexGroup is created and stored when the controller comes up (after upgrading from an earlier release. Note that a reload of the 8.3 will not create the group again. It will only restore the existing Default FlexGroup configuration.) This group cannot be deleted or added manually. Also, you cannot manually add or delete APs to the Default FlexGroup. The APs in the Default FlexGroup inherit the common configuration of the group. Any change in the group configuration is propagated to all the APs in the group.
When a group created by an admin is deleted, all the APs from that group are moved to the Default FlexGroup and inherit the configuration of this group. Similarly, APs that are removed manually from other groups are also added to the Default FlexGroup.
When an AP from the Default FlexGroup is added to a customized group, the existing configuration (from the Default FlexGroup) is deleted and the configuration from the customized group is pushed to the AP. If there is a standby controller, the Default FlexGroup and its configuration are also synchronized to it.
The AP provides FlexConnect group name during the join process. The AP could have received this group name either through cloud provisioning or through Cisco WLC configuration. There are various scenarios involved in deciding the final FlexConnect group, when an AP joins and they are listed in the table below:
|
FlexConnect Group Received from AP |
Status in Cisco WLC |
Final Group Information/Configuration Setn to AP |
Type of Entry (Based on Priority) |
|---|---|---|---|
|
Group1 |
Group1 not present; AP entry not present in any group |
Default FlexGroup |
Admin |
|
Group1 |
Group1 present but maximum entries reached; AP entry not present in any group |
Default FlexGroup |
Admin |
|
Group1 |
Group1 present, but AP entry not present in any group |
Group1 |
Cloud |
|
Group1 |
Group1 present, but AP entry present as part of a different group, Group2 (added by admin) |
Group2 |
Admin |
|
Group1 |
Group1 present, but AP entry exists in a different group, Group2 learnt earlier through cloud |
Group1 |
Cloud |
|
No Group/Default Group |
AP entry exists as part of Group2 (either through admin configuration or learnt via cloud) |
Group2 |
Admin/Cloud |
Whenever the final type of entry is cloud, the AP entry gets added to the corresponding FlexConnect group. Also, when the FlexConnect group received from AP is different from the resultant group, a trap is raised to inform the admin about the conflict. The show flexconnect group detail group-name aps command displays the conflict value.
The following features are not supported:
-
Efficient image upgrade
-
PMK cache distribution
-
Fast Roaming
The following features are supported:
-
VLAN support (native VLAN, WLAN-VLAN mapping)
-
VLAN ACL mapping
-
WebAuth, web policy, local split mapping
-
Local authentication users
-
RADIUS authentication
-
Central DHCP or NAT-PAT
-
Flex AVC
-
VLAN name ID mapping
-
Multicast override
Downgrading to an Earlier Release
The Default FlexGroup configuration is retained after downgrading from 8.3 to an earlier release (8.2 and earlier). It will be treated as a configurable group, where you can add or delete APs. However, the FlexConnect APs will not be able to join this group by default.
Upgrading from a Earlier Release
A FlexConnet AP, which is not part of any FlexConnect group, will join the Default FlexGroup and inherit configuration from the group. If a Default FlexGroup already exists in the system, it will be renamed during the upgrade, and a message is logged with the name of the renamed group.
Restrictions
-
You cannot use the following CLIs to add or delete a Defaut FlexGroup or AP to a group:
-
config flexconnect group default-flexgroup{ add | delete}
-
config flexconnect group default-flexgroup ap{ add | delete}
-
-
The Defaut FlexGroup does not have a default configuration.
-
When you delete an AP from the customized flex group, the VLAN support is also deleted from that AP.
-
In a default FlexGroup scenario, fast roaming is not supported.
 Feedback
Feedback