Capabilities
Cisco Unified Mobile Agent Description
Unified Mobile Agent supports call center agents using phones that your contact center enterprise solution does not directly control. You can deploy a Mobile Agent as follows:
-
Outside the contact center, by using an analog phone or a mobile phone in the home.
-
On an IP phone connection that is not CTI-controlled by Packaged CCE or by an associated Unified Communications Manager.
-
On any voice endpoint of any ACD (including endpoints on other Unified Communication Managers) that the contact center Unified Communication Manager can reach by a SIP trunk.
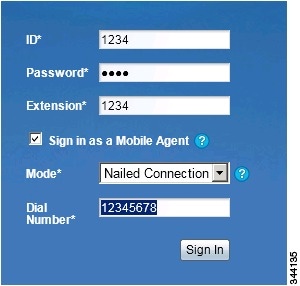
A Mobile Agent can use different phone numbers at different times; the agent enters the phone number at login time. An agent can access the Mobile Agent functionality using any phone number that is included in the Unified Communications Manager dial plan.
Unified Mobile Agent Provides Agent Sign-In Flexibility
Agents can be either local agents or Mobile Agents, depending on how they sign in at various times.
Regardless of whether agents sign in as local or Mobile Agents, their skill groups do not change. Because agents are chosen by existing selection rules and not by how they are connected, the same routing applies regardless of how the agents log in. If you want to control routing depending on whether agents are local or mobile, assign the agents to different skill groups and design your scripts accordingly.
Connection Modes
Cisco Unified Mobile Agent allows system administrators to configure agents to use either call by call dialing or a nailed connection, or the administrator can configure agents to choose a connection mode at login time.
Mobile Agents are defined as agents using phones not directly controlled by Unified CC, irrespective of their physical location. (The term local agent refers to an agent who uses a phone that is under control of Unified CC, irrespective of physical location.)
You can configure Mobile Agents using either of two delivery modes:
-
Call by Call—In this mode, the Mobile Agent's phone is dialed for each incoming call. When the call ends, the Mobile Agent's phone is disconnected before being made ready for the next call.
-
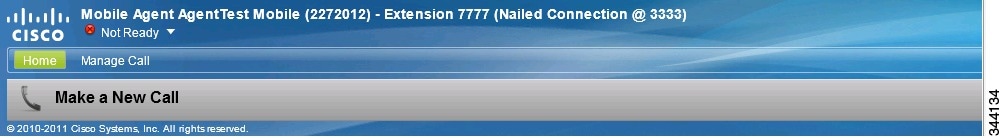
Nailed Connection—In this mode, the agent is called at login time and the line stays connected through multiple customer calls.
 Note |
The administrator can select the Agent chooses option, which allows an agent to select a call delivery mode at login. |
Call by Call
In a call by call delivery mode, the Mobile Agent's phone is dialed for each incoming call. When the call ends, the Mobile Agent's phone disconnects before is it made ready for the next call.
The call by call call flow works as follows:
-
At login, the agent specifies an assigned extension for a CTI port.
-
A customer call arrives in the system and, through normal Unified ICM configuration and scripting, is queued for a skill group or an agent. (This is no different than existing processing for local agents.)
-
The system assigns an agent to the call. If the agent's Desk Setting is Unified Mobile Agent-enabled and configured for either call by call or Agent chooses mode, the router uses the extension of the agent's CTI port as a label.
-
The incoming call rings at the agent's CTI port. The JTAPI Gateway and PIM notice this but do not answer the call.
-
A call to the agent is initiated on another CTI port chosen from a preconfigured pool. If this call fails, Redirect on No Answer processing is initiated.

Note
In call by call mode, the Answer Wait Time is 3 to 15 seconds longer than in a local agent inbound call scenario. Specify a Redirect on No Answer setting large enough to accommodate the extra processing time.
-
When the agent takes the remote phone off-hook to answer the call, the system directs the customer call to the agent's call media address and the agent's call to the customer's call media address.
-
When the call ends, both connections are terminated and the agent is ready to accept another call.
 Note |
To configure Mobile Agent in call by call delivery mode, you must set the wrap-up timer to at least one second using the Agent Desktop Settings List tool in the Configuration Manager. In call by call delivery mode, callers often perceive a longer ring time compared to nailed connection delivery mode. This is because callers hear the ringtone during the call flow; ringing stops only after the agent answers. From the Unified CCE reporting perspective, a Mobile Agent in call by call delivery mode has a longer Answer Wait Time for the same reason. |
Nailed Connections
In nailed connection delivery mode, the agent is called once, at login, and the phone line remains connected through multiple customer calls. See the following figure.
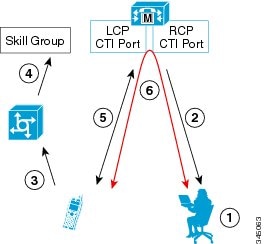
The nailed connection call flow works as follows:
-
At login, the agent enters the directory number of the local CTI port (LCP) and the remote phone number in the Desktop.
The remote phone number can be any phone number reachable by Unified CM.
When the agent clicks the Login button, a call is initiated to the agent's remote CTI port (RCP) and the agent's remote phone rings.
-
When the agent answers the call, the call is then nailed up. This means that the agent will remain on this call until the agent logs out or hangs up.
-
A customer's call arrives in the system and, through normal Packaged CCE configuration and scripting, is queued for a skill group/precision queue. (This is no different than existing processing for local agents.)
-
When the agent clicks the Answer button, the voice path between the agent and the customer phone is established, and the two parties can talk.
-
When the system assigns an agent to the call, the call is routed to the agent's LCP port. The agent then hears the connect tone on the headset.
-
When the call ends, the customer connection is terminated and the agent state returns to Ready.
Connect Tone
The Connect Tone feature in the nailed connection mode enables the system to play a tone to the Mobile Agent through the agent's headset to let the agent know when a new call is connected.
Connect Tone is particularly useful when Auto Answer is enabled or the agent is an Outbound agent. Here are its features:
-
An audible tone (two beeps) is sent to the Mobile Agent headset when the call to the nailed connection Mobile Agent is connected. It is a DTMF tone played by Unified CM and cannot be modified.
-
The Connect Tone plays only when the nailed connection Mobile Agent receives a call, as in the following examples:
-
The agent receives a consultation call.
-
The agent receives an outbound call.
-
-
The Connect Tone does not play when the Mobile Agent initiates a call, as in the following examples:
-
The agent makes a call.
-
The agent makes the consultation call.
-
Outbound direct preview call is made.
-
Supervisor barge-in call is made.
-
Agent Greeting and Whisper Announcement
The Agent Greeting and Whisper Announcement features are available to Unified Mobile Agents. The following sections explain more about how these features apply to Unified Mobile Agents.
Agent Greeting
You can use the Agent Greeting feature to record a message that plays automatically to callers when they connect to you. Your greeting message can welcome the caller, identify you, and include other useful information.
Limitations
The following limitations apply to the Agent Greeting feature for Mobile Agents.
-
A supervisor cannot barge in when an Agent Greeting is playing.
-
If a Peripheral Gateway (PG), JTAPI Gateway (JGW), or PIM failover occurs when an Agent Greeting plays for a Mobile Agent, the call fails.
-
If a Mobile Agent hangs up when an Agent Greeting plays, the customer still hears the complete Agent Greeting before the call ends.

Note
In the Agent Greeting Call Type Report, this call does not appear as a failed agent greeting call.
For more information about Agent Greeting, see Capabilities.
Whisper Announcement
With Whisper Announcement, agents can hear a brief prerecorded message just before they connect with each caller. The announcement plays only to the agent; the caller hears ringing (based on existing ringtone patterns) while the announcement plays. The announcement can contain information about the caller, such as language preference or customer status. This information helps the agent prepare for the call.
Configuration Requirement
For the Whisper Announcement feature for Unified Mobile Agents, you require a Media Termination Point (MTP) resource on an incoming SIP device.
Feature Requirements
Phone Requirements
A Unified Mobile Agent can use an analog, digital, or IP phone to handle calls.
 Note |
When Unified Mobile Agent phones are located on a cluster and a SIP Trunk is used to connect the cluster to another cluster under Packaged CCE control, you must either use SIP phones as Mobile Agent phones or select mtp required on the Packaged CCE cluster to allow Mobile Agent calls to work. |
Conference Requirements
To use Agent Greeting for Mobile Agents, you must configure external conference-bridge (hardware) resources. To estimate the number of required resources, you can use the following formula:
Number of conference bridge resources = Mobile Agent call rate × Average greeting time (in seconds)
For information about configuring external conference-bridge resources, see the dspfarm profile 1 for conference configuration section in the sample configuration gateway, listed in Media Termination Points Configuration.
CTI Port Requirements
You need two CTI ports (local and remote) for every logged-in Mobile Agent.
Unified Mobile Agent uses Unified CM CTI Port as a proxy for the agent's phone. When this proxy is set up, whenever a Mobile Agent is selected to handle a customer call, the following happens:
-
The call is directed to the CTI port extension.
-
Packaged CCE intercepts the call arriving on the CTI Port and directs Unified CM to connect the call to the Mobile Agent.
For Unified Mobile Agent to work properly, you must configure two CTI ports:
-
One port to serve as the agent's virtual extension.
-
The other port to initiate calls to the agent.
You must assign these CTI ports to the Packaged CCE application. The ports are recognized by Packaged CCE when receiving the Unified CM configuration.
For these CTI ports in IPv6 enabled deployments, you have to set IP Addressing Mode to IPv4 Only. You do this by creating a Common Device Configuration and referencing it to these CTI ports.
Important Considerations
Before you proceed, consider the following Unified Mobile Agent limitations and considerations:
Failover
-
During a failover, if an agent in call by call mode answers an alerting call, the call can drop. This occurs because the media cannot be bridged when there is no active PG.
-
During a prolonged Peripheral Gateway (PG) failover, if an agent takes call control action for a Unified Mobile Agent-to-Unified Mobile Agent call, the call can drop. This occurs because the activating PG may not have information for all agents and calls at that point.
-
Unified Communications Manager failover causes a Mobile Agent call to be lost.
-
If a call by call Mobile Agent initiates a call (including a supervisor call) and does not answer the remote leg of the call before PG failover, the call fails. The agent must disconnect the remote agent call leg and reinitiate the call.
Performance
-
For the total number of supported Unified Mobile Agents and more information about Unified Mobile Agent capability, see Solution Design Guide for Cisco Packaged Contact Center Enterprise at https://www.cisco.com/c/en/us/support/customer-collaboration/packaged-contact-center-enterprise/products-technical-reference-list.html.
-
Because Unified Mobile Agent adds processing steps to Unified CCE default functionality, Mobile Agents may experience some delay in screen popup windows.
-
From a caller's perspective, the call by call delivery mode has a longer ring time compared with the nailed connection delivery mode. This is because Unified CCE does not start to dial the Mobile Agent's phone number until after the call information is routed to the agent desktop. In addition, the customer call media stream is not connected to the agent until after the agent answers the phone.
The caller hears a repeated ringtone while Unified CCE makes these connections.
Codec
-
Launch the Peripheral Gateway Setup.
-
In the Peripheral Gateway Component Properties, select the UCM PIM and click Edit.
-
In the CallManager Parameters section, select the appropriate codec from the Mobile Agent Codec drop down list.
Figure 2. Mobile Agent Codec Selection 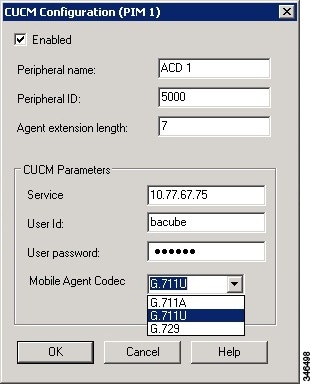
Unsupported Features
The following is a list of unsupported features for Mobile Agent:
-
Web Callback
-
Unified CM-based Silent Monitoring
-
Agent Request
Unified Mobile Agent Reporting
Unified Mobile Agent-specific call data is contained in the following Cisco Unified Intelligence Center reports: Agent Team Historical, Agent Real Time, and Agent Skill Group Historical. These “All Field” reports contain information in multiple fields that show what kind of call the agent is on (nonmobile, call by call, nailed connection) and the Unified Mobile Agent phone number.
 Note |
The service level for Unified Mobile Agent calls might be different than the service level for local agent calls, because it takes longer to connect the call to the agent. For example, a call by call Mobile Agent might have a longer Answer Wait Time Average than a local agent. This is because Packaged CCE does not start to dial the Mobile Agent phone number until after the call information is routed to the agent desktop. In addition, the customer call media stream is not connected to the agent until after the agent answers the phone. |

 Feedback
Feedback