Serviceability Connector Overview
You can ease the collection of logs with the Webex Serviceability service. The service automates the tasks of finding, retrieving, and storing diagnostic logs and information.
This capability uses the Serviceability Connector deployed on your premises. Serviceability Connector runs on a dedicated host in your network ('connector host'). You can install the connector on either of these components:
-
Enterprise Compute Platform (ECP)—Recommended
ECP uses Docker containers to isolate, secure, and manage its services. The host and the Serviceability Connector application install from the cloud. You don’t need to manually upgrade them to stay current and secure.

Important
We recommend use of ECP. Our future development will focus on this platform. Some new features won't be available if you install the Serviceability Connector on an Expressway.
-
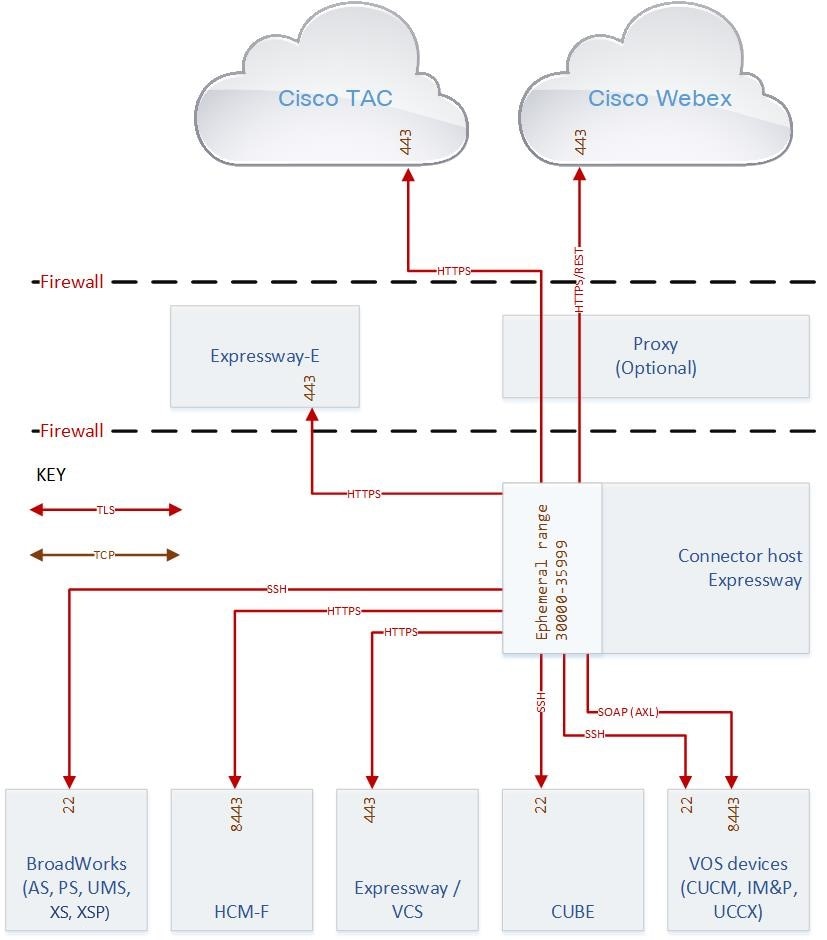
Cisco Expressway
You can use the Servicability Connector for these purposes:
-
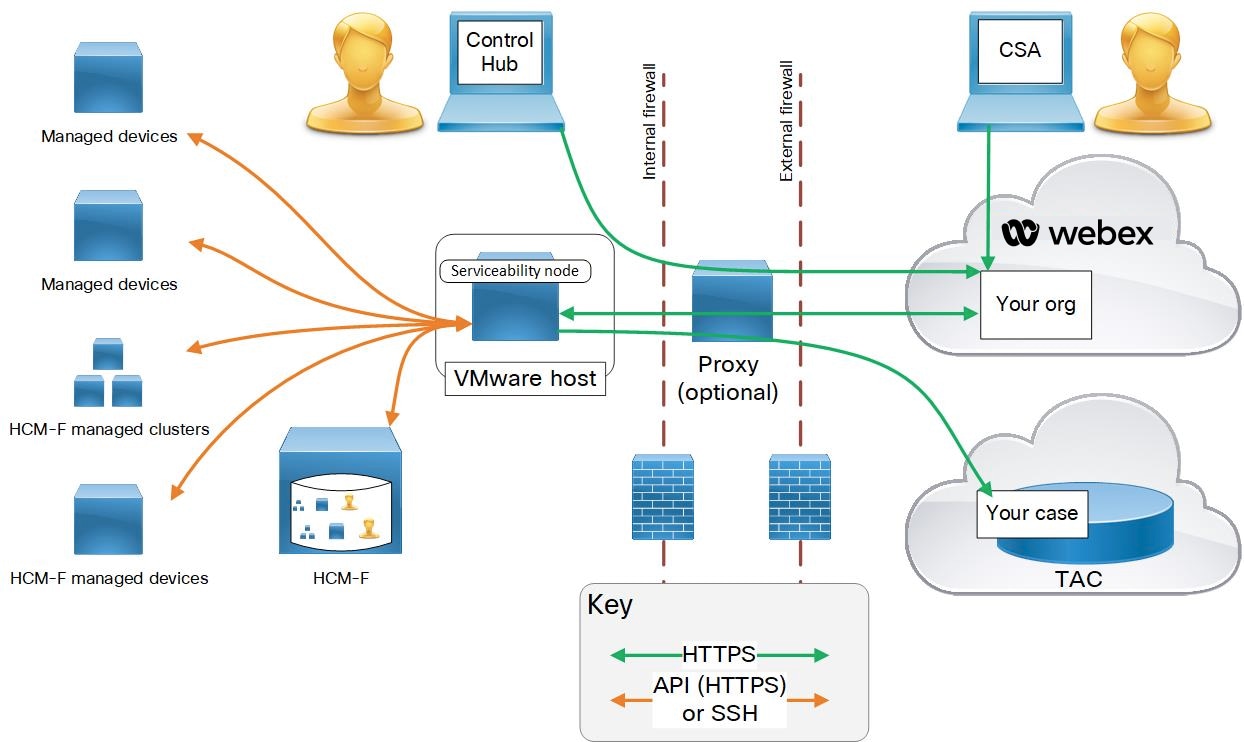
Automated log and system information retrieval for service requests
-
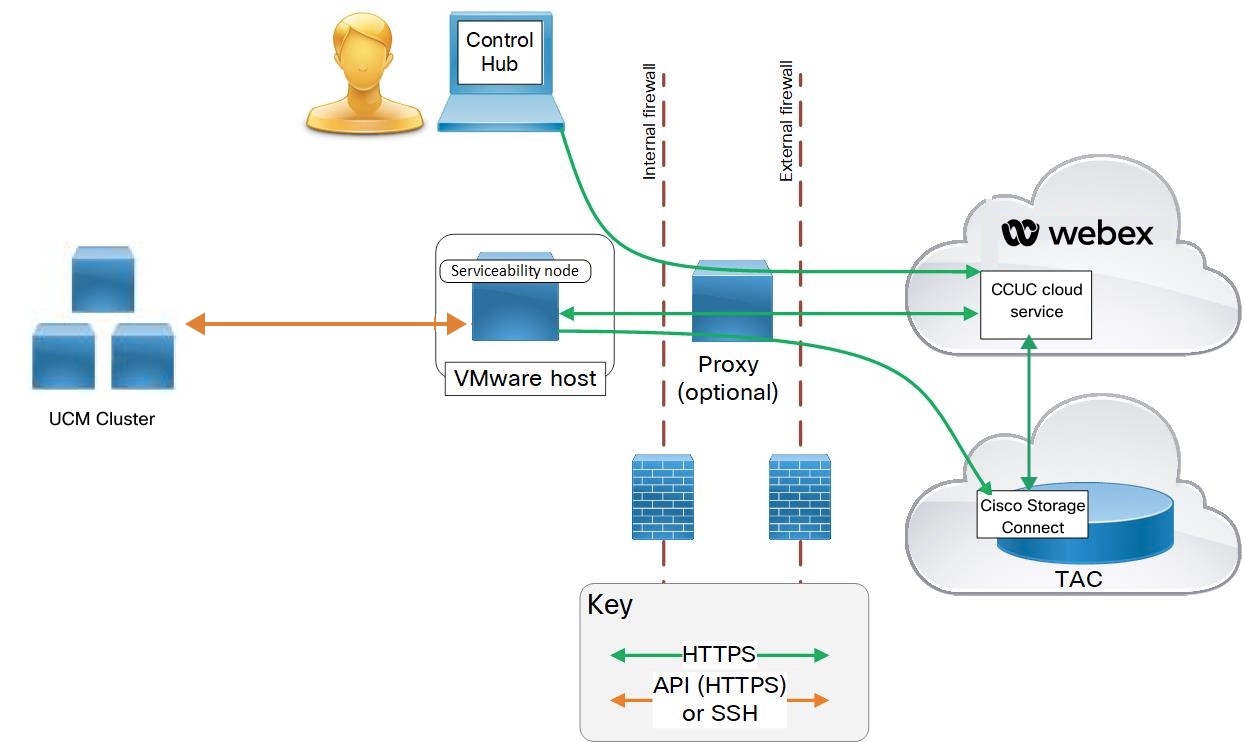
Log collection of your Unified CM clusters in a Cloud-Connected UC deployment
You can use the same Serviceability Connector for both use cases.


 Feedback
Feedback