Restrictions for IPv6 ACLs
With IPv4, you can configure standard and extended numbered IP ACLs, named IP ACLs, and MAC ACLs. IPv6 supports only named ACLs.
The switch supports most Cisco IOS-supported IPv6 ACLs with some exceptions:
-
The switch does not support matching on these keywords: routing header, and undetermined-transport.
-
The switch does not support reflexive ACLs (the reflect keyword).
-
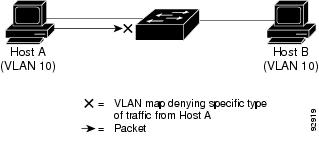
This release supports port ACLs, router ACLs and VLAN ACLs (VLAN maps) for IPv6.
-
The switch does not apply MAC-based ACLs on IPv6 frames.
-
When configuring an ACL, there is no restriction on keywords entered in the ACL, regardless of whether or not they are supported on the platform. When you apply the ACL to an interface that requires hardware forwarding (physical ports or SVIs), the switch checks to determine whether or not the ACL can be supported on the interface. If not, attaching the ACL is rejected.
-
If an ACL is applied to an interface and you attempt to add an access control entry (ACE) with an unsupported keyword, the switch does not allow the ACE to be added to the ACL that is currently attached to the interface.
IPv6 ACLs on the switch have these characteristics:
-
Fragmented frames (the fragments keyword as in IPv4) are supported
-
The same statistics supported in IPv4 are supported for IPv6 ACLs.
-
If the switch runs out of hardware space, the packets associated with the ACL are dropped on the interface.
-
Logging is supported for router ACLs, but not for port ACLs.
-
The switch supports IPv6 address-matching for a full range of prefix-lengths.
-
If a downloadable ACL contains any type of duplicate entries, the entries are not auto merged. As a result, the 802.1X session authorization fails. Ensure that the downloadable ACL is optimized without any duplicate entries, for example port-based and name-based entries for the same port.

 Feedback
Feedback