Connect and Disconnect to a VPN
AnyConnect VPN Connectivity Options
The AnyConnect client provides many options for automatically connecting, reconnecting, or disconnecting VPN sessions. These options provide a convenient way for your users to connect to your VPN, and they also support your network security requirements.
Starting and Restarting AnyConnect Connections
Configure VPN Connection Servers to provide the names and addresses of the secure gateways your users will manually connect to.
Choose from the following AnyConnect capabilities to provide convenient, automatic VPN connectivity:
Also, consider using the following Automatic VPN Policy options to enforce greater network security or restrict network access to the VPN only:
Renegotiating and Maintaining the AnyConnect Connection
You can limit how long the ASA keeps an AnyConnect VPN connection available to the user even with no activity. If a VPN session goes idle, you can terminate the connection or re-negotiate the connection.
-
Keepalive—The ASA sends keepalive messages at regular intervals. These messages are ignored by the ASA, but are useful in maintaining connections with devices between the client and the ASA.
For instructions to configure Keepalive with the ASDM or CLI, see the Enable Keepalive section in the Cisco ASA Series VPN Configuration Guide.
-
Dead Peer Detection—The ASA and AnyConnect client send "R-U-There" messages. These messages are sent less frequently than IPsec's keepalive messages. You can enable both the ASA (gateway) and the AnyConnect client to send DPD messages, and configure a timeout interval.
-
If the client does not respond to the ASA’s DPD messages, the ASA tries once more before putting the session into "Waiting to Resume" mode. This mode allows the user to roam networks, or enter sleep mode and later recover the connection. If the user does not reconnect before the idle timeout occurs, the ASA will terminate the tunnel. The recommended gateway DPD interval is 300 seconds.
-
If the ASA does not respond to the client's DPD messages, the client tries again before terminating the tunnel. The recommended client DPD interval is 30 seconds.
For instructions to configure DPD within the ASDM, refer to Configure Dead Peer Detection in the appropriate release of the Cisco ASA Series VPN Configuration Guide.
-
-
Best Practices:
-
Set Client DPD to 30 seconds (Group Policy > Advanced > AnyConnect Client > Dead Peer Detection).
-
Set Server DPD to 300 seconds (Group Policy > Advanced > AnyConnect Client > Dead Peer Detection).
-
Set Rekey, for both SSL and IPsec to 1 hour (Group Policy > Advanced > AnyConnect Client > Key Regeneration).
-
Terminating an AnyConnect Connection
Terminating an AnyConnect connection requires the user to re-authenticate their endpoint to the secure gateway and create a new VPN connection.
The following connection parameters terminate the VPN session based on timeouts:
-
Maximum Connect Time—Sets the maximum user connection time in minutes. At the end of this time, the system terminates the connection. You can also allow unlimited connection time(default).
-
VPN Idle Timeout—Terminates any user’s session when the session is inactive for the specified time. If the VPN idle timeout is not configured, then the default idle timeout is used.
-
Default Idle Timeout—Terminates any user’s session when the session is inactive for the specified time. The default value is 30 minutes. The default is 1800 second.
See the Specify a VPN Session Idle Timeout for a Group Policy section in the appropriate release of the Cisco ASA Series VPN Configuration Guide to set these parameters.
Configure VPN Connection Servers
The AnyConnect VPN server list consists of host name and host address pairs identifying the secure gateways that your VPN users will connect to. The host name can be an alias, an FQDN, or an IP address.
The hosts added to the server list display in the Connect to drop-down list in the AnyConnect GUI. The user can then select from the drop-down list to initiate a VPN connection. The host at the top of the list is the default server, and appears first in the GUI drop-down list. If the user selects an alternate server from the list, the selected server becomes the new default server.
Once you add a server to the server list, you can view its details and edit or delete the server entry. To add a server to the server list, follow this procedure.
Procedure
| Step 1 |
Open the VPN Profile Editor and choose Server List from the navigation pane. |
||
| Step 2 |
Click Add. |
||
| Step 3 |
Configure the server’s host name and address: |
||
| Step 4 |
Enter the server to fall back to as the backup server in the Backup Server List. Do not use "&" or "<" characters in the name.
|
||
| Step 5 |
(Optional) Add load balancing servers to the Load Balancing Server List. Do not use "&" or "<" characters in the name. If the host for this server list entry specifies a load balancing cluster of security appliances, and the Always-On feature is enabled, add the load balancing devices in the cluster to this list. If you do not, Always-On blocks access to the devices in the load balancing cluster. |
||
| Step 6 |
Specify the Primary Protocol for the client to use for this ASA: |
||
| Step 7 |
(Optional) Configure SCEP for this server:
|
||
| Step 8 |
Click OK. |
Automatically Start Windows VPN Connections Before Logon
About Start Before Logon
This feature called Start Before Logon (SBL) allows users to establish their VPN connection to the enterprise infrastructure before logging onto Windows.
 Note |
When using Start Before Logon (SBL) and HostScan, you must install the AnyConnect/HostScan posture predeploy module on the endpoints to achieve full HostScan functionality, since SBL is pre-login. |
After SBL is installed and enabled, the Network Connection button launches the AnyConnect VPN and Network Access Manager UI.
SBL also includes the Network Access Manager tile and allows connections using user configured home network profiles. Network profiles allowed in SBL mode include all media types employing non-802.1X authentication modes, such as open WEP, WPA/WPA2 Personal, and static key (WEP) networks.
-
On Windows, the Pre-Login Access Provider (PLAP) is used to implement AnyConnect SBL.
With PLAP, the Ctrl+Alt+Del key combination opens a window where the user can choose either to log in to the system or activate Network Connections (PLAP components) using the Network Connect button in the lower-right corner of the window.
PLAP supports 32-bit and 64-bit versions of the Windows.
-
The user’s computer is joined to an Active Directory infrastructure.
-
A user has network-mapped drives that require authentication with the Microsoft Active Directory infrastructure.
-
The user cannot have cached credentials on the computer (the group policy disallows cached credentials). In this scenario, users must be able to communicate with a domain controller on the corporate network for their credentials to be validated before gaining access to the computer.
-
The user must run logon scripts that execute from a network resource or need access to a network resource. With SBL enabled, the user has access to the local infrastructure and logon scripts that would normally run when a user is in the office. This includes domain logon scripts, group policy objects and other Active Directory functionality that normally occurs when users log on to their system.
-
Networking components (such as MS NAP/CS NAC) exist that might require connection to the infrastructure.
Limitations on Start Before Logon
-
AnyConnect is not compatible with fast user switching.
-
AnyConnect cannot be started by third-party Start Before Logon applications.
-
Because SBL is pre-login and will not have access to the user store, you cannot do multiple certificate authentication (MCA) with it. MCA requires a machine certificate and a user certificate, or two user certificates.
Configure Start Before Logon
Procedure
| Step 1 | |
| Step 2 |
Install the AnyConnect Start Before Logon Module
The AnyConnect installer detects the underlying operating system and places the appropriate AnyConnect DLL from the AnyConnect SBL module in the system directory. On Windows 7, or the Windows 2008 server, the installer determines whether the 32-bit or 64-bit version of the operating system is in use and installs the appropriate PLAP component, vpnplap.dll or vpnplap64.dll.
 Note |
If you uninstall AnyConnect while leaving the VPNGINA or PLAP component installed, the VPNGINA or PLAP component is disabled and not visible to the remote user. |
You can predeploy the SBL module or configure the ASA to download it. When predeploying AnyConnect, the Start Before Logon module requires that the core client software is installed first. If you are predeploying AnyConnect Core and the Start Before Logon components using MSI files, you must get the order right.
Procedure
| Step 1 |
In ASDM go to . |
| Step 2 |
Select a group policy and click Edit or Add a new group policy. |
| Step 3 |
Select in the left navigation pane. |
| Step 4 |
Uncheck Inherit for the Optional Client Module for Download setting. |
| Step 5 |
Select the AnyConnect SBL module in the drop-down list. |
Enable SBL in the AnyConnect Profile
Before you begin
-
SBL requires a network connection to be present at the time it is invoked. In some cases, this might not be possible, because a wireless connection might depend on credentials of the user to connect to the wireless infrastructure. Since SBL mode precedes the credential phase of a logon, a connection would not be available in this scenario. In this case, the wireless connection needs to be configured to cache the credentials across logon, or another wireless authentication needs to be configured, for SBL to work.
-
If the Network Access Manager is installed, you must deploy device connection to ensure that an appropriate connection is available.
Procedure
| Step 1 |
Open the VPN Profile Editor and choose Preferences (Part 1) from the navigation pane. |
||
| Step 2 |
Select Use Start Before Logon. |
||
| Step 3 |
(Optional) To give the remote user control over SBL, select User Controllable.
|
Troubleshoot Start Before Logon
Procedure
| Step 1 |
Ensure that the AnyConnect profile is loaded on the ASA, ready to be deployed. |
| Step 2 |
Delete prior profiles (search for them on the hard drive to find the location, *.xml). |
| Step 3 |
Using Windows Add/Remove Programs, uninstall the SBL Components. Reboot the computer and retest. |
| Step 4 |
Clear the user’s AnyConnect log in the Event Viewer and retest. |
| Step 5 |
Browse back to the security appliance to install AnyConnect again. |
| Step 6 |
Reboot once. On the next reboot, you should be prompted with the Start Before Logon prompt. |
| Step 7 |
Collect a DART bundle and send it to your AnyConnect Administrator. |
| Step 8 |
If you see the following error, delete the user’s AnyConnect profile: |
| Step 9 |
Go back to the .tmpl file, save a copy as an.xml file, and use that XML file as the default profile. |
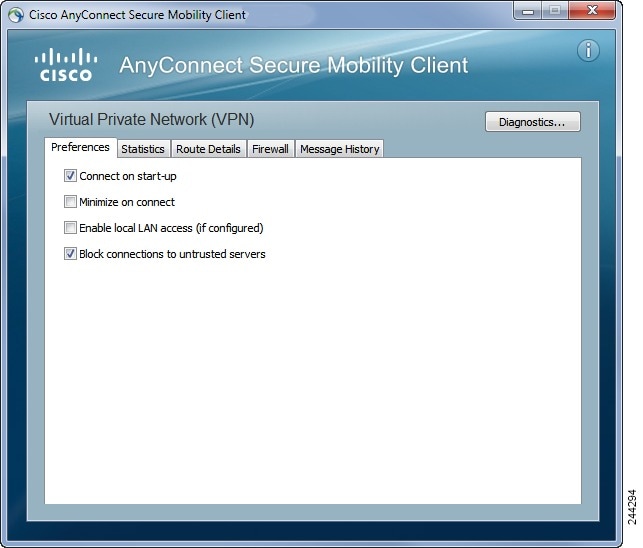
Automatically Start VPN Connections When AnyConnect Starts
This feature called Auto Connect On Start, automatically establishes a VPN connection with the secure gateway specified by the VPN client profile when AnyConnect starts.
Auto Connect On Start is disabled by default, requiring the user to specify or select a secure gateway.
Procedure
| Step 1 |
Open the VPN Profile Editor and choose Preferences (Part 1) from the navigation pane. |
| Step 2 |
Select Auto Connect On Start. |
| Step 3 |
(Optional) To give the user control over Auto Connect on Start, select User Controllable. |



 Feedback
Feedback